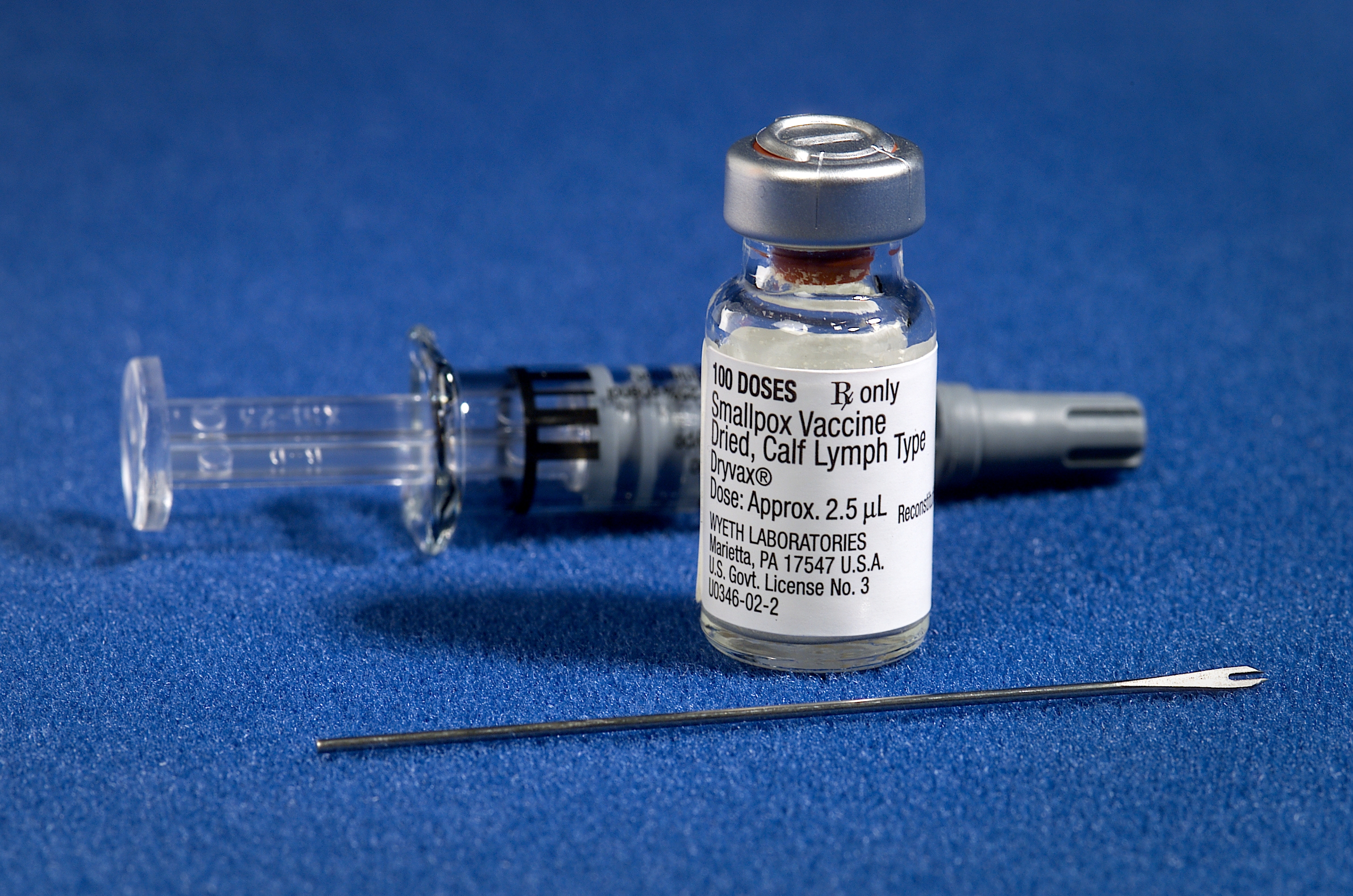
In the relentless march of technological progress, innovation is often celebrated for its breakthroughs – the autonomous vehicles navigating complex environments, the sophisticated AI models understanding human language, or the ubiquitous smart devices connecting our lives. Yet, beneath the gleaming surface of innovation lies a critical, often unsung, struggle: the battle against inherent vulnerabilities, design flaws, and unexpected failures that can cripple even the most promising advancements. Just as a smallpox vaccine provides immunity against a devastating disease, a similar metaphorical “vaccine” is crucial for tech and innovation – a foundational set of principles, components, and practices that inoculate nascent technologies against debilitating “digital maladies.” This article delves into the essential “ingredients” of this technological vaccine, exploring what truly constitutes the core defense mechanisms and enabling factors for resilient, future-proof innovation.
Deconstructing the Digital “Vaccine”: Core Principles for Resilient Tech
The concept of a “vaccine” in technology might seem unconventional, but it offers a powerful framework for understanding how we build robust systems. It’s not about curing existing problems, but proactively instilling immunity against predictable and unpredictable challenges.
The Metaphor of Immunity in Technology Development
Technological immunity is about designing systems that are not just functional but inherently resilient. It’s about anticipating points of failure, safeguarding against external threats, and ensuring longevity in a rapidly evolving landscape. This proactive stance is paramount. Unlike biological vaccines that target specific pathogens, a tech “vaccine” is a multi-faceted defense system. It encompasses architectural integrity, robust algorithms, secure data practices, and ethical considerations, all working in concert to create a dependable technological ecosystem. The goal is to prevent the “smallpox” of design flaws, data breaches, or performance bottlenecks from ever taking hold and spreading.
Identifying “Smallpox” in Modern Tech: Micro-Vulnerabilities
What, then, constitutes “smallpox” in the digital realm? It’s not a singular entity but a constellation of micro-vulnerabilities that, if left unchecked, can escalate into catastrophic failures. These can range from subtle software bugs, insecure data handling protocols, and hardware degradation to more insidious threats like adversarial AI attacks, supply chain compromises, or ethical dilemmas baked into algorithms. For example, a minor flaw in a drone’s flight control software could lead to instability, or a small data leak in a smart home device could compromise user privacy on a grand scale. The “smallpox” of tech often begins as seemingly insignificant issues that, given the right conditions, can propagate and undermine trust, functionality, and even safety. Understanding these potential infection points is the first step toward effective vaccination.
The Genetic Code: Software & AI Architectures as Key Ingredients
At the heart of any modern technological “vaccine” lies its software and AI architecture. These are the genetic blueprints that dictate how a system operates, adapts, and defends itself.
Algorithmic Robustness and Error Correction
The primary ingredient for a strong digital immune system is robust algorithmic design. This involves crafting algorithms that are not only efficient but also resilient to unexpected inputs, edge cases, and environmental fluctuations. Techniques like formal verification, extensive unit and integration testing, and fault-tolerant design patterns are crucial. Error correction codes (ECC) in data transmission and storage, for instance, are a classic example of building immunity at a fundamental level, allowing systems to detect and repair data corruption autonomously. In complex AI systems, this translates to developing models that are robust to adversarial attacks, preventing minor input perturbations from causing major misclassifications or system failures. Predictive maintenance algorithms, for example, analyze vast datasets to anticipate hardware failures before they occur, effectively vaccinating against unexpected downtime.
Artificial Intelligence for Proactive Threat Detection and Self-Healing Systems
AI itself is a powerful “vaccine” component, particularly in its ability to detect anomalies and orchestrate self-healing processes. Machine learning models can be trained to identify emerging cyber threats, unusual system behaviors, or performance degradations in real-time, long before they escalate into critical incidents. Imagine an autonomous drone that, through on-board AI, detects a subtle anomaly in its motor’s vibration signature and proactively adjusts its flight parameters or signals for maintenance. This proactive detection and adaptive response capability is akin to the immune system identifying and neutralizing pathogens. Beyond detection, AI can power self-healing systems that automatically roll back updates, reconfigure networks, or even re-deploy services to mitigate ongoing attacks or failures, minimizing downtime and human intervention.
Open-Source Contributions and Community “Antibodies”
The collaborative nature of open-source development acts as a collective immune response, with a vast community of developers contributing to the strength and security of foundational software. When vulnerabilities are discovered in open-source projects, they are often identified and patched by a global network of experts far more quickly than proprietary software. This collective vigilance and peer review process creates robust “antibodies” that strengthen the entire tech ecosystem. Furthermore, standardized open protocols and interfaces foster interoperability, preventing isolated “organ failures” within a fragmented tech landscape and promoting a healthier, more connected environment.
The Physical Structure: Hardware Resilience and Material Science
While software provides the intelligence, the physical hardware forms the body of the technological immune system. Without a resilient physical structure, even the most sophisticated software vaccine is rendered ineffective.
Miniaturization and Durability: Engineering for Harsh Environments
For many modern innovations, especially in areas like drones, robotics, and IoT, physical resilience is paramount. This involves not just robust casing but also designing internal components to withstand vibrations, temperature extremes, electromagnetic interference, and even radiation. Advanced material science plays a crucial role here, developing lightweight yet incredibly strong alloys, polymers, and composites. Miniaturization, while often driven by performance and size constraints, also contributes to durability by reducing inertia and potential stress points, making devices less susceptible to physical damage in challenging operational environments. Think of micro-drones designed for inspection; their resilience to minor impacts is a fundamental part of their operational vaccine.
Energy Efficiency and Autonomous Power Management
A consistent and reliable power supply is the lifeblood of any autonomous system. “Vaccinating” against power failures involves designing highly energy-efficient components, optimizing power consumption through intelligent algorithms, and integrating redundant power sources. Autonomous power management systems can dynamically switch between batteries, harvest ambient energy, or intelligently throttle performance to extend operational life when power is low. For remote sensors or drones operating in inaccessible locations, this self-sufficiency is a critical protective measure against complete system shutdown, ensuring continuous operation even when external charging is impossible.
Redundancy and Modularity: Building in Layers of Protection
Just as biological systems have redundant organs, robust tech systems incorporate redundancy to prevent single points of failure. This can range from dual processors and backup communication links to modular hardware designs that allow for easy replacement of faulty components. Modularity also simplifies maintenance and upgrades, ensuring that the “vaccine” can be continually updated without needing to replace the entire system. In a drone, for instance, having multiple motors and redundant flight controllers ensures that the failure of one component doesn’t necessarily lead to a catastrophic crash, providing layers of physical immunity.
The Immune Response: Data Security, Privacy, and Ethical Frameworks
Beyond functional resilience, a comprehensive tech vaccine must also address the societal and ethical implications, protecting user data and ensuring responsible innovation. This forms the ethical and security “immune response” of the system.
Encryption and Immutable Ledgers: Safeguarding Digital Assets
In an age where data is the new oil, protecting digital assets is a non-negotiable component of any tech vaccine. Robust encryption protocols, both in transit and at rest, are fundamental. Beyond traditional encryption, technologies like immutable ledgers (e.g., blockchain) are emerging as powerful tools for creating tamper-proof records and ensuring data integrity. For remote sensing drones collecting sensitive environmental data or mapping critical infrastructure, ensuring the data’s authenticity and protection from unauthorized alteration is paramount. This prevents the “digital smallpox” of data corruption or theft, preserving trust and integrity.
Ethical AI and Bias Mitigation: Preventing Algorithmic “Illnesses”
As AI becomes more pervasive, its inherent biases can lead to discriminatory outcomes or unintended consequences, creating an “algorithmic illness” within society. The tech vaccine must include rigorous ethical frameworks and bias mitigation strategies. This involves diverse training datasets, explainable AI (XAI) techniques to understand decision-making, and regular audits of AI systems for fairness and accountability. Building AI that respects privacy, is transparent in its operations, and minimizes unintended harm is crucial for its long-term societal acceptance and health, preventing the spread of distrust and misuse.
Regulatory Compliance and Trust: The “Public Health” of Tech
Just as public health initiatives require regulation, the tech industry benefits from clear compliance standards and responsible governance. Adhering to regulations like GDPR or industry-specific safety standards builds a foundation of trust with users and stakeholders. Transparency in data handling, clear privacy policies, and demonstrable security practices are essential. This creates a regulatory “immune system” that fosters responsible innovation and prevents individual tech “organisms” from becoming toxic to the broader societal “body,” ensuring the public’s confidence in the technology itself.
Continuous Evolution: Adaptive Strategies for Long-Term Tech Health
No vaccine offers permanent immunity against all future threats. A truly robust tech vaccine requires continuous evolution, adapting to new challenges and integrating new insights.
Over-the-Air Updates and Incremental Improvements
The ability to deliver over-the-air (OTA) updates is a critical component of adaptive immunity. This allows manufacturers to patch security vulnerabilities, introduce new features, and improve performance remotely, ensuring that deployed systems remain protected and relevant throughout their lifecycle. Regular, incremental updates prevent the buildup of technical debt and proactively address emerging threats, much like booster shots for a vaccine. This constant refinement ensures that the tech remains agile and responsive to evolving demands and threats.
Predictive Analytics for Maintenance and Lifecycle Management
Leveraging predictive analytics helps in understanding the long-term health of technological systems. By analyzing operational data, performance trends, and usage patterns, organizations can predict potential hardware failures, software degradation, or capacity limitations. This allows for proactive maintenance, parts replacement, or system upgrades, extending the operational lifespan and preventing unexpected breakdowns. This foresight acts as a powerful preventative measure, ensuring the system remains healthy and functional for years to come.
Interoperability and Ecosystem Health: Preventing Isolation “Syndrome”
Finally, a healthy tech ecosystem thrives on interoperability. Systems that can communicate and work seamlessly with others are more robust and offer greater value. Adherence to open standards, common protocols, and API-first design promotes a vibrant, interconnected environment. Conversely, proprietary, closed systems can suffer from “isolation syndrome,” becoming brittle and unable to adapt as the surrounding tech landscape evolves. By fostering a diverse and interconnected ecosystem, the collective resilience against future “digital smallpox” is significantly enhanced, ensuring that innovations contribute positively to a larger, healthier technological world.
In conclusion, the “smallpox vaccine” for tech and innovation is not a single product but a complex interplay of rigorous design principles, intelligent software, resilient hardware, ethical considerations, and a commitment to continuous adaptation. By meticulously crafting these ingredients into every layer of technological development, we can build a future where innovation is not just groundbreaking but also inherently robust, secure, and enduring, truly immunizing our digital world against the vulnerabilities that threaten its progress.
