In an increasingly interconnected world, where every device from our smartwatches to our drone controllers operates as a miniature computer, the concept of a “virus” has expanded far beyond the desktop PCs of yesteryear. The question, “what is a phone virus,” transcends simple curiosity; it delves into the fundamental vulnerabilities of our digital ecosystem, particularly as these mobile devices become integral components in controlling complex systems like modern drones. To truly understand a phone virus in this advanced technological landscape, we must first appreciate its nature, its evolution, and its profound implications for the world of aerial robotics and remote sensing.
At its core, a phone virus is a type of malicious software, or “malware,” designed to infiltrate a smartphone or tablet without the user’s consent. Once entrenched, it can perform a variety of harmful actions: stealing personal data, corrupting files, monitoring communications, sending premium-rate messages, or even taking control of the device’s functions. Unlike earlier computer viruses that often aimed simply to replicate and spread, modern phone viruses are frequently sophisticated tools for espionage, financial gain, or disruption. Their existence poses a significant threat not only to individual privacy but also to the operational security of critical technologies, especially those relying on mobile interfaces, such as drones.
The Evolving Landscape of Digital Threats
The digital world is a constant battleground between innovators and exploiters. As technology advances, so do the methods of attack, necessitating a deep understanding of the risks.
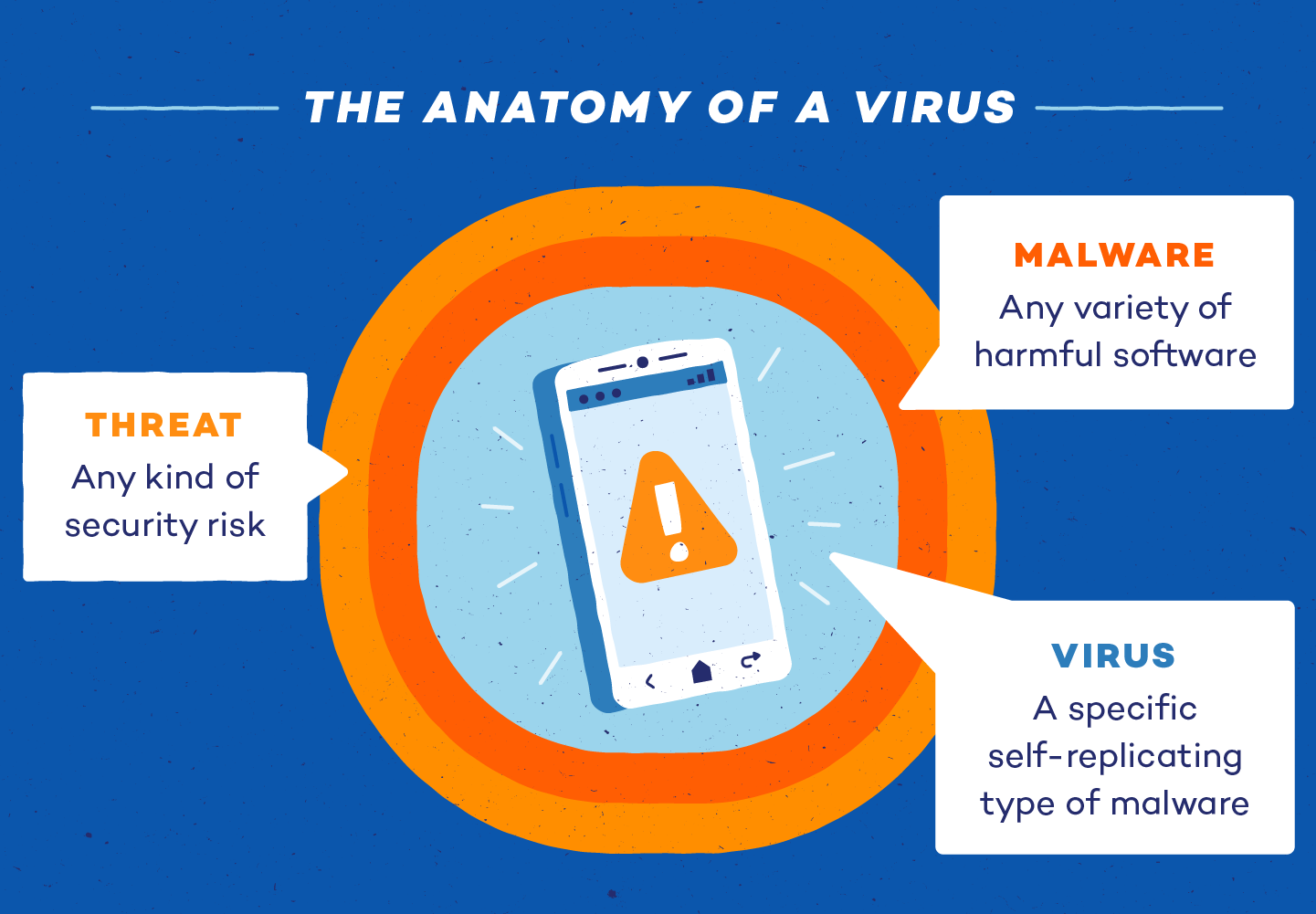
Defining Malware and Viruses in a Connected World
The term “virus” is often used generically to describe any malicious software, but it’s more accurate to consider it a specific type of malware. A true virus requires a host program to spread, inserting its own code into legitimate applications. When the host program is executed, the virus code runs too, often replicating itself. However, the ecosystem of phone malware is much broader, encompassing various threats:
- Worms: Standalone malicious programs that can self-replicate and spread across networks without human intervention.
- Trojans: Disguise themselves as legitimate software to trick users into installing them, then perform malicious activities in the background. They do not self-replicate.
- Spyware: Secretly monitors user activity, capturing sensitive information like passwords, credit card numbers, or GPS locations.
- Adware: Bombards users with unwanted advertisements, often compromising privacy in the process.
- Ransomware: Encrypts a device’s data and demands a ransom, typically in cryptocurrency, for its release.
- Rootkits: A collection of software tools that enable administrator-level access to a computer or network without being detected.
In the mobile context, these distinctions blur, as phone malware often combines elements of several types. The rapid proliferation of apps, often with extensive permissions, creates fertile ground for these digital parasites.

Beyond Traditional PCs: Smartphones as Attack Vectors
Smartphones have become ubiquitous, serving as our primary communication tools, personal assistants, and increasingly, controllers for other smart devices. This centrality makes them prime targets for malicious actors. Unlike traditional PCs, smartphones possess unique characteristics that make them particularly vulnerable and attractive as attack vectors:
- Constant Connectivity: Always online, always accessible, facilitating easier remote access for attackers.
- Rich Sensor Data: GPS, accelerometers, cameras, microphones—all can be exploited to gather extensive personal or environmental data.
- App Ecosystems: While app stores provide some vetting, malicious apps can still slip through, or legitimate apps can be compromised.
- Integrated Payment Systems: Mobile payment options and stored financial information make phones lucrative targets for theft.
- Control over IoT Devices: Many smart home devices, wearables, and crucially, drones, are controlled via smartphone apps, expanding the potential for cascading security breaches.
The evolution of phone viruses reflects a move from simple mischief to sophisticated cybercrime, with attackers leveraging device features and user habits to achieve their objectives. This brings us to a critical juncture when considering advanced technologies like drones.

The Intersection of Mobile Security and Drone Operations
Drones, representing a pinnacle of modern robotics and autonomous flight technology, are often controlled via sophisticated mobile applications running on smartphones or tablets. This critical link creates a significant cyber-physical security challenge.
Smartphones as Drone Controllers: A Critical Link
The convenience and processing power of modern smartphones make them ideal platforms for drone control. Apps provide intuitive interfaces for flight planning, real-time telemetry, camera control, and even advanced features like AI follow mode or autonomous flight path generation. However, this convenience introduces a significant attack surface. If the controlling smartphone or tablet is compromised by a virus, the integrity and safety of the drone operation can be severely jeopardized. An attacker could potentially:
- Intercept Control Signals: Gain unauthorized access to the drone’s command and control channels.
- Manipulate Flight Parameters: Alter predefined flight paths, altitude limits, or no-fly zones, leading to unsafe operations or even loss of the drone.
- Exfiltrate Data: Steal sensitive data collected by the drone, such as high-resolution imagery, thermal scans, or mapping data.
- Disable Safety Features: Compromise critical safety mechanisms, increasing the risk of accidents or deliberate misuse.
This direct dependency means that the security posture of the mobile device directly correlates with the security posture of the entire drone mission.
How a “Phone Virus” Can Impact Drone Missions
The consequences of a compromised control device extend far beyond personal data theft. For drone operators, especially those involved in commercial, industrial, or public safety applications, a phone virus can have severe operational and financial ramifications:
- Mission Failure: A virus could crash the control app, disconnect the drone, or send erroneous commands, leading to incomplete or failed missions.
- Loss of Drone: If an attacker gains control, they could fly the drone out of range, crash it, or even steal it, representing a substantial asset loss.
- Compromised Data Integrity: Data collected for mapping, remote sensing, or inspection could be altered, deleted, or leaked, rendering it useless or causing significant damage to reputation or regulatory compliance.
- Security Breaches: Drones used for sensitive applications (e.g., surveillance, infrastructure inspection) could have their feeds intercepted or their operational locations revealed, compromising security protocols.
- Public Safety Risks: In worst-case scenarios, a hijacked drone could be used maliciously, causing harm to people or property.
The sophisticated nature of modern phone viruses, capable of persistent access and covert operations, makes them a stealthy and dangerous adversary in the drone ecosystem.
Data Integrity and Privacy Concerns
Drones are powerful data collection platforms. From 4K video for cinematic aerial filmmaking to precise geospatial data for agricultural mapping and infrastructure inspection, the integrity and privacy of this data are paramount. A phone virus, particularly spyware or a Trojan, can compromise this data at various stages:
- During Transmission: Intercepting data as it streams from the drone to the controller.
- At Rest on the Device: Accessing stored flight logs, photos, videos, or mission plans on the phone.
- Before Upload: Stealing data before it is encrypted and uploaded to cloud services.
For businesses and government agencies utilizing drones, data breaches are not just an inconvenience; they can lead to competitive disadvantages, regulatory fines, and a complete loss of trust. Therefore, securing the mobile controller is an essential first step in ensuring the overall cybersecurity of drone operations.
Emerging Cyber Threats to Drone Technology Itself
Beyond the control device, drones themselves are complex technological systems with embedded computers, sensors, and communication links, making them direct targets for sophisticated cyber threats. The “Tech & Innovation” landscape of drones means these threats are constantly evolving.
Firmware Vulnerabilities and Exploits
Drones run on proprietary firmware—the low-level software that controls their hardware functions. Like any software, firmware can contain bugs or vulnerabilities that can be exploited by attackers. A successful firmware exploit could allow an attacker to:
- Gain Root Access: Achieve full control over the drone’s operating system.
- Install Malicious Code: Introduce persistent malware that can alter flight behavior, disable safety features, or transmit data to unauthorized parties.
- Brick the Drone: Render the drone inoperable.
- Bypass Geofencing/No-Fly Zones: Allow the drone to operate in restricted airspace, posing security and safety risks.
Regular firmware updates from manufacturers are crucial, but relying solely on these isn’t enough; operators must ensure their update processes are secure and verified.
GPS Spoofing and Jamming: Hijacking Autonomy
One of the most critical flight technologies in drones is GPS, essential for navigation, stabilization, and autonomous flight. This reliance makes GPS a prime target for specific cyberattacks:
- GPS Spoofing: An attacker broadcasts fake GPS signals that mimic legitimate ones, tricking the drone into believing it’s in a different location. This can cause the drone to deviate from its flight path, fly into restricted areas, or land prematurely. For drones relying on precise mapping and remote sensing for tasks like surveying, spoofing can entirely invalidate collected data.
- GPS Jamming: Attackers overwhelm legitimate GPS signals with noise, effectively blinding the drone’s navigation system. While some drones have contingencies (e.g., visual positioning systems), jamming can force a drone to return home, land abruptly, or become uncontrollable.
These attacks can compromise autonomous flight capabilities, disrupting missions and potentially leading to drone loss or accidental damage.
Network-Based Attacks on Drone Communication
Drones communicate with their controllers and often with other network services via various wireless protocols (Wi-Fi, radio, cellular). These communication channels are susceptible to network-based attacks:
- Eavesdropping: Intercepting unencrypted command and control signals or data streams (e.g., FPV video feeds).
- Man-in-the-Middle Attacks: An attacker secretly relays and possibly alters the communication between the drone and its controller, making it appear as if they are directly communicating.
- Denial-of-Service (DoS) Attacks: Flooding the drone’s communication channels with traffic to prevent it from receiving legitimate commands or transmitting data.
- Exploiting Protocol Vulnerabilities: Weaknesses in wireless communication protocols (e.g., WPA2 flaws) can be exploited to gain unauthorized access.
Such attacks can lead to loss of control, data exfiltration, or complete operational disruption, highlighting the importance of robust encryption and secure communication protocols in drone design and operation.
Safeguarding Your Drone Ecosystem from Digital Intruders
The evolving nature of “phone viruses” and broader cyber threats demands a multi-layered security approach for drone operators and manufacturers. Proactive measures are essential to mitigate risks and ensure the safety, reliability, and security of drone technology.
Best Practices for Mobile Device Security
Since the smartphone or tablet often serves as the nexus of drone control, securing this device is paramount:
- Keep Software Updated: Regularly update the operating system and all apps (especially the drone control app) to patch known vulnerabilities.
- Install Antivirus/Anti-Malware: Use reputable mobile security software to detect and remove malicious threats.
- Download Apps from Official Sources: Stick to official app stores (Google Play, Apple App Store) and scrutinize app permissions. Avoid side-loading apps from unknown sources.
- Use Strong, Unique Passwords/Biometrics: Secure your device with strong passcodes, fingerprints, or facial recognition.
- Enable Two-Factor Authentication (2FA): Where available, use 2FA for drone manufacturer accounts and any cloud services tied to your drone operations.
- Be Wary of Phishing: Exercise caution with suspicious emails, messages, or links that could lead to malware installation.
- Encrypt Your Device: Ensure your mobile device’s storage is encrypted to protect data at rest.
- Limit Permissions: Grant apps only the necessary permissions and review them regularly.
Secure Drone Operation Protocols
Beyond the mobile device, established operational protocols can significantly enhance overall security:
- Pre-Flight Security Checks: Verify firmware versions, check for unauthorized modifications, and ensure all communication links are secure.
- Secure Launch and Recovery Zones: Operate in controlled environments to minimize the risk of physical access to the drone.
- Data Encryption: Utilize drones that support encrypted data transmission for live feeds and recorded data.
- Regular Data Backups: Securely back up flight logs, mission plans, and collected data to separate, protected storage.
- Awareness and Training: Train operators on cybersecurity best practices, threat identification, and incident response procedures.
- Network Segmentation: If operating multiple drones or complex systems, segment networks to limit the spread of potential breaches.
The Future of Drone Cybersecurity: Proactive Measures
As drone technology continues to evolve with advancements in AI follow mode, autonomous flight, and sophisticated remote sensing capabilities, so too will the complexity of cyber threats. The future of drone cybersecurity demands a proactive, integrated approach:
- Hardware-Based Security: Integrating secure boot processes, hardware security modules (HSMs), and tamper-detection mechanisms directly into drone hardware.
- AI-Driven Threat Detection: Leveraging AI and machine learning to detect anomalous behavior in drone flight patterns or communication signals, identifying potential attacks in real-time.
- Blockchain for Data Integrity: Exploring distributed ledger technologies to ensure the immutability and authenticity of drone-collected data, especially for critical applications like legal evidence or supply chain verification.
- Enhanced Regulatory Frameworks: Developing and enforcing robust cybersecurity standards and certifications for drone manufacturers and operators.
- Continuous Vulnerability Assessments: Regular penetration testing and security audits for drone systems, firmware, and associated mobile applications.
In conclusion, “what is a phone virus” is a question that opens the door to a much broader discussion on cybersecurity in the age of connected devices and autonomous systems. For the rapidly expanding world of drone technology, securing the mobile controllers, the drones themselves, and the entire operational ecosystem from these digital threats is not merely an option but an absolute necessity for ensuring safety, integrity, and continued innovation.
