Network shares, often referred to as shared folders or network drives, are a cornerstone of modern collaborative computing environments. At their core, they represent a mechanism by which files and folders on one computer can be made accessible to other computers on the same network. This seemingly simple concept unlocks a vast array of functionalities, from streamlined document collaboration to efficient data storage and distribution. Understanding network shares is crucial for anyone navigating the complexities of shared digital resources, whether in a home network or a large enterprise.
The fundamental principle behind a network share is the act of “sharing” a resource. When a user or administrator designates a folder on a computer as a network share, they are essentially making it visible and accessible to other authorized users on the network. This accessibility is typically managed through a network protocol, most commonly Server Message Block (SMB) for Windows and Apple Filing Protocol (AFP) for macOS, though Network File System (NFS) is also prevalent in Unix-like environments. These protocols define the rules and commands for how computers communicate to request and transfer files across the network.

The primary benefit of network shares lies in their ability to facilitate centralized access to data. Instead of having individual copies of the same document spread across multiple workstations, a single, definitive version can be stored on a server and accessed by all relevant users via a network share. This not only reduces storage redundancy but also significantly simplifies version control and ensures that everyone is working with the most up-to-date information. For teams working on projects, this centralized access is invaluable, allowing for real-time collaboration and minimizing the confusion that arises from disparate file versions.
How Network Shares Function
The operation of a network share involves a client-server model, though in some configurations, peer-to-peer sharing is also possible. In a typical scenario, one computer, often designated as a server (though any computer can technically host a share), makes a folder available. Other computers on the network, acting as clients, can then connect to this shared folder to read, write, or modify files within it, depending on the permissions set by the administrator.
The Role of Protocols
Network sharing relies heavily on specific communication protocols that govern how data is exchanged between devices.
Server Message Block (SMB)
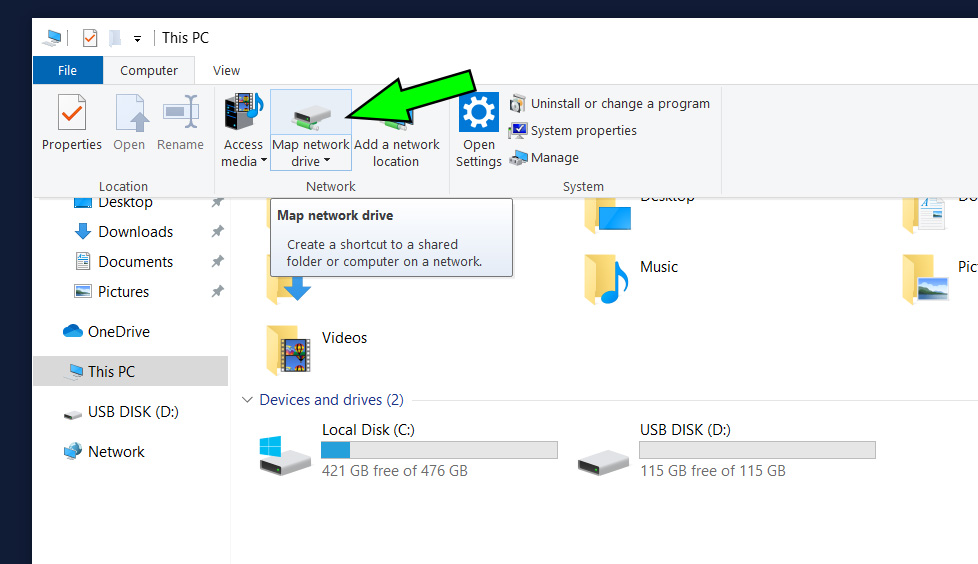
SMB is the de facto standard for file sharing in Windows networks. It allows clients to request access to files and directories on a server, perform operations like opening, reading, writing, and closing files, and manage network resources. SMB has evolved over time, with newer versions offering enhanced security features and performance improvements. When you map a network drive in Windows or browse for shared folders, you are interacting with the SMB protocol.
Apple Filing Protocol (AFP)
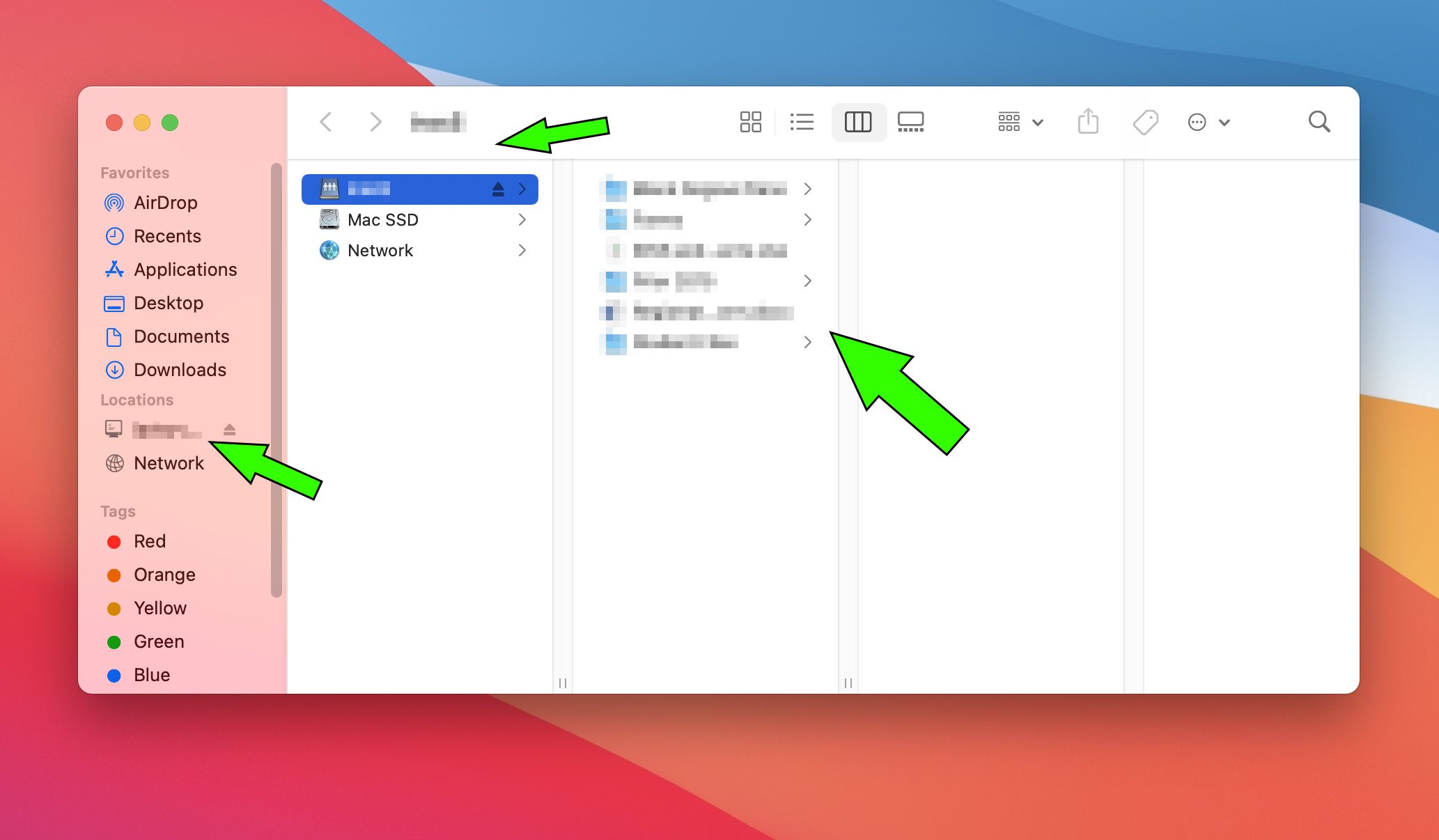
For macOS users, AFP has historically been the primary protocol for network file sharing. It provides similar functionalities to SMB, enabling Macs to connect to shared resources on other Macs or on servers. While macOS has increasingly adopted SMB for compatibility with Windows environments, AFP remains a robust option for Mac-centric networks.
Network File System (NFS)
NFS is a distributed file system protocol commonly used in Unix and Linux environments. It allows a client computer to mount a directory on a remote server and access it as if it were a local directory. NFS is known for its performance and scalability, making it a popular choice in enterprise Linux deployments and for sharing data between servers.
Permissions and Access Control
A critical aspect of network shares is the implementation of permissions and access control. Without proper security measures, sensitive data could be exposed to unauthorized users. Administrators define who can access a shared folder and what actions they can perform (e.g., read-only, read/write, full control). These permissions can be applied at the user level or group level, providing granular control over data access.
User-Level Permissions
This involves granting specific access rights to individual user accounts. For example, User A might have read-only access to a project folder, while User B, a project manager, might have full read/write access.
Group-Level Permissions
For easier management, users can be organized into groups, and permissions can be assigned to these groups. This simplifies the process of managing access for multiple users with similar roles. For instance, a “Marketing Team” group could be granted read/write access to the marketing department’s shared folder, and all members of that group would automatically inherit those permissions.
Types and Implementations of Network Shares
Network shares can be implemented in various ways, ranging from simple peer-to-peer sharing on home networks to sophisticated enterprise-level solutions. The underlying technology and management complexity vary significantly between these implementations.
Peer-to-Peer Sharing
In a peer-to-peer network, any computer can act as both a client and a server. Users can directly share folders from their personal computers with other computers on the same local network. This is a common setup in small home or office environments where a dedicated server is not practical. While convenient for quick sharing, it relies on the availability and power of individual workstations and can pose security risks if not managed carefully.
Server-Based Sharing
This is the more robust and scalable approach, typically found in businesses and larger organizations. A dedicated server (or multiple servers) is used to host network shares. This offers several advantages:
Centralized Storage and Management
All shared data resides on the server, making it easier to manage, back up, and secure. The server’s resources (processing power, storage capacity, network bandwidth) are dedicated to serving files.
Enhanced Security
Servers can be configured with advanced security features, including firewalls, intrusion detection systems, and robust access control lists, to protect sensitive data.
Reliability and Uptime
Dedicated servers are typically built for continuous operation, ensuring that network shares are available when needed. They often have redundant power supplies, RAID configurations for disk fault tolerance, and regular maintenance schedules.
Network Attached Storage (NAS) Devices
NAS devices are specialized hardware appliances designed specifically for network file storage and sharing. They act as dedicated file servers, offering a user-friendly interface for setting up and managing shares. NAS devices are a popular choice for both home users and small to medium-sized businesses looking for a cost-effective and easy-to-manage solution for centralized storage and backups. They often come with built-in RAID capabilities for data redundancy and can support various network protocols, including SMB, AFP, and NFS.
Practical Applications of Network Shares
The utility of network shares extends to numerous practical applications that enhance productivity and streamline workflows across diverse environments.
Collaborative Document Editing
As mentioned earlier, network shares are indispensable for collaborative environments. Teams can work on shared documents stored in a central location, allowing multiple users to access and edit files simultaneously (depending on the application’s capabilities). This is particularly useful for projects requiring input from various team members, fostering a more integrated and efficient workflow.
Centralized Data Backups
Network shares provide an excellent platform for centralizing backups. Instead of backing up individual workstations, administrators can configure backup solutions to target specific network shares, ensuring that critical data is regularly backed up to a secure, accessible location. This simplifies the backup process and makes data recovery more efficient in the event of hardware failure or data loss.
Software Deployment and Updates
In larger organizations, network shares are often used to store software installation files and updates. IT administrators can deploy software to multiple workstations by mapping a network drive containing the installation packages, saving significant time and effort compared to manual installation on each machine. Similarly, software updates can be distributed efficiently.
Media Streaming and File Distribution
Network shares can serve as a central repository for media files, such as music, videos, or presentations, which can then be streamed or accessed by multiple users on the network. This is common in home entertainment setups or in educational institutions for distributing learning materials.
Accessing Shared Printers and Other Peripherals
While not strictly file sharing, the concept of network sharing extends to other network resources, including printers. When a printer is connected to a computer that is part of a network, it can be shared, allowing other computers on the network to send print jobs to it. This eliminates the need for individual printers for each workstation.
Benefits and Considerations
The widespread adoption of network shares is a testament to their significant benefits. However, like any technology, there are considerations that users and administrators must keep in mind to ensure optimal performance and security.
Key Advantages
- Enhanced Collaboration: Facilitates seamless teamwork by providing a single source of truth for project files.
- Centralized Data Management: Simplifies data organization, storage, and retrieval.
- Reduced Data Redundancy: Minimizes the number of duplicate files, saving storage space.
- Improved Efficiency: Streamlines workflows related to file access, sharing, and distribution.
- Simplified Backups and Recovery: Centralized data makes backup and recovery processes more manageable.
- Scalability: Can be scaled to accommodate growing data storage needs.
Important Considerations
- Security: Proper configuration of permissions is paramount to prevent unauthorized access and data breaches. Regular audits of access logs are recommended.
- Network Performance: The speed and reliability of the network significantly impact the performance of network shares. Bottlenecks in network bandwidth or slow server response times can lead to user frustration.
- Data Integrity: While network shares enable collaboration, they do not inherently guarantee data integrity. The use of robust file systems, regular backups, and careful management practices are essential to prevent data corruption.
- Server Maintenance: For server-based shares, regular maintenance, updates, and monitoring of the server hardware and software are crucial for ensuring uptime and performance.
- User Training: Educating users on how to properly access and utilize network shares, as well as the importance of security protocols, is vital for effective implementation.
In conclusion, network shares are a fundamental technology that empowers individuals and organizations to share and manage digital resources effectively. From enabling collaborative projects to ensuring secure data access, their impact on modern computing is profound. By understanding the underlying principles, protocols, and best practices, users can leverage network shares to their full potential, fostering greater productivity and a more connected digital experience.
