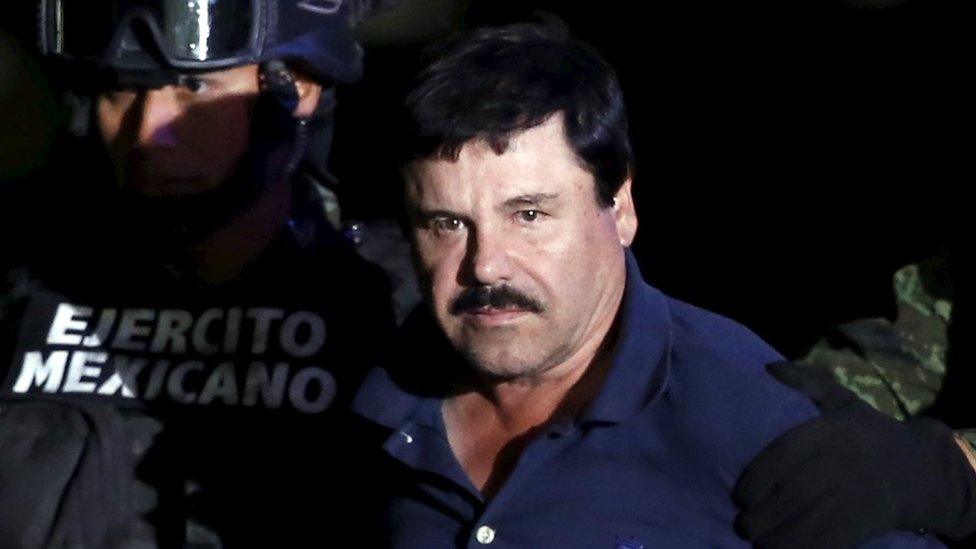
The Elusive Kingpin and the Technologies That Pursued Him
The name Joaquín “El Chapo” Guzmán is synonymous with the apex of international drug trafficking. For decades, he orchestrated a vast criminal empire, building a legend around his ability to evade capture. While the story of his rise and eventual downfall is complex and involves myriad human and geopolitical factors, the relentless pursuit by law enforcement agencies worldwide also highlights a fascinating interplay with evolving technologies. From cutting-edge surveillance to sophisticated communication intercepts, the tools and techniques employed to track, locate, and ultimately apprehend El Chapo offer a compelling case study in the technological arms race between criminals and those seeking to bring them to justice. This exploration delves into the technological dimensions of El Chapo’s saga, focusing on the surveillance and communication technologies that played a crucial role in his eventual capture and conviction.
The Digital Shadows: Surveillance and Intelligence Gathering
The sheer scale of El Chapo’s operations necessitated a level of sophistication in surveillance that often pushed the boundaries of what was technologically feasible at the time. Law enforcement agencies, particularly in the United States and Mexico, invested heavily in intelligence gathering, employing a multi-pronged approach that leveraged both traditional and advanced methods.
Signal Intelligence and Electronic Eavesdropping
A cornerstone of any modern manhunt, especially for a figure as influential as El Chapo, is signal intelligence (SIGINT). This involves the interception of communications, including phone calls, text messages, and emails. As El Chapo and his associates operated globally, the challenge was not just in intercepting signals but in decrypting them and pinpointing their origin.
- Cellular Intercept Technologies: Law enforcement agencies employ sophisticated equipment capable of intercepting cellular communications within a specific geographic area. Devices known as “Stingrays” or cell-site simulators can mimic legitimate cell towers, forcing nearby mobile phones to connect to them. This allows authorities to gather information about the devices in the vicinity, including their unique identifiers (IMSI and IMEI) and, in some cases, even capture call logs and text messages. The challenge with such technologies lies in their potential to sweep up data from innocent bystanders, raising privacy concerns. However, for high-value targets like Guzmán, the legal frameworks and justifications for their use become paramount.
- Advanced Cryptography and Decryption: While El Chapo’s organization likely employed encrypted communication methods to safeguard their dealings, intelligence agencies possess advanced capabilities for decryption. This can involve brute-force attacks, leveraging massive computing power to decipher complex algorithms, or exploiting vulnerabilities in specific encryption software. The ongoing battle between encryption development and decryption capabilities is a constant theme in cybersecurity and law enforcement.
- Social Media and Open-Source Intelligence (OSINT): In the digital age, even those operating outside the law leave a digital footprint. El Chapo’s associates, and sometimes even Guzmán himself through intermediaries, inadvertently revealed information through social media posts, public records, and other publicly available data. OSINT professionals meticulously sift through this vast amount of information to identify patterns, connections, and potential locations, triangulating intelligence that might otherwise be missed. This often involves analyzing location tags, photographs, and social connections that can reveal the whereabouts and activities of key players.
Satellite and Aerial Surveillance
Beyond ground-based intelligence, aerial and satellite surveillance provided critical overwatch and tracking capabilities. The vastness of the territories El Chapo operated within, particularly the remote mountainous regions of Mexico, demanded advanced imaging and tracking solutions.
- High-Resolution Satellite Imagery: Commercial and governmental satellites equipped with high-resolution cameras can provide detailed imagery of terrain, infrastructure, and even significant movements of vehicles or personnel. While not typically real-time in the same way as aerial surveillance, satellite imagery is invaluable for long-term monitoring, identifying remote compounds, or detecting changes in terrain that might indicate clandestine activity, such as the construction of tunnels.
- Reconnaissance Aircraft and Drones: Unmanned Aerial Vehicles (UAVs) and manned reconnaissance aircraft equipped with advanced sensor suites have become indispensable tools. These platforms can provide persistent surveillance over specific areas, equipped with:
- Electro-Optical/Infrared (EO/IR) Cameras: These cameras allow for visual observation during the day and thermal imaging at night or through atmospheric obscurants like fog and smoke. This is crucial for detecting heat signatures from vehicles, buildings, or even individuals.
- Synthetic Aperture Radar (SAR): SAR systems can penetrate cloud cover and darkness to create detailed images of the ground, useful for mapping clandestine routes or identifying structures hidden beneath vegetation.
- Communications Intelligence (COMINT) Payloads: Some advanced aerial platforms can be equipped to intercept radio communications in their vicinity, augmenting SIGINT efforts. The ability of drones to loiter for extended periods over target areas at relatively low cost compared to manned aircraft made them particularly attractive for sustained surveillance operations.

The Hunt for the Ghost: Tracking and Apprehension Technologies
The pursuit of El Chapo was not a static operation; it involved a dynamic and often cat-and-mouse game, utilizing technologies to track his movements and anticipate his next steps.
Tracking and Identification Technologies
As El Chapo moved frequently, often employing elaborate disguises and seemingly vanishing into thin air, law enforcement relied on a combination of technological and human intelligence to keep pace.
- Facial Recognition Technology: While not always perfect, facial recognition algorithms have advanced significantly. Law enforcement agencies utilize databases of known individuals and employ these systems to scan surveillance footage from public cameras, airports, and border crossings to identify potential sightings of Guzmán or his associates. The accuracy and speed of these systems have improved, making them a powerful tool in identifying known fugitives in crowded environments.
- Biometric Data Analysis: Beyond facial recognition, other biometric data, such as fingerprints and DNA, play a critical role in confirming identities. While these are often collected post-apprehension, the proactive analysis of any obtained biometric data can help law enforcement build profiles and understand the networks involved.
- Electronic Surveillance of Vehicles and Property: Authorities have the capability to track vehicles associated with El Chapo’s organization. This can involve deploying GPS trackers on suspect vehicles, although this requires close proximity and a high degree of certainty about which vehicle to target. More broadly, monitoring traffic camera feeds and license plate recognition (LPR) systems can help piece together movements and identify patterns. Investigations also extended to monitoring known properties and residences, looking for signs of activity or occupants.
Communication and Information Management
The sheer volume of intelligence gathered during the protracted hunt for El Chapo would be unmanageable without sophisticated systems for collecting, analyzing, and disseminating information.
- Secure Communication Networks: Law enforcement agencies rely on encrypted and secure communication networks to share intelligence amongst different units and international partners. This ensures that sensitive information is protected from interception by the targets or other malicious actors. The ability to share real-time intelligence is paramount in coordinating complex operations involving multiple agencies and jurisdictions.
- Data Analytics and Artificial Intelligence: Modern intelligence gathering is increasingly reliant on advanced data analytics and artificial intelligence (AI). These technologies can process vast datasets to identify anomalies, predict behavior, and uncover hidden connections that human analysts might miss. AI algorithms can analyze communication patterns, financial transactions, and travel records to flag suspicious activity or identify potential hiding places. This is particularly useful in sifting through the immense amount of data generated by surveillance operations, allowing investigators to focus on the most promising leads.
- Geospatial Intelligence (GEOINT) Platforms: GIS and GEOINT platforms allow for the integration and visualization of various data sources, including satellite imagery, GPS coordinates, and intelligence reports. This enables analysts to create detailed maps and 3D models of operational areas, identify potential escape routes, and plan tactical operations more effectively. The ability to overlay different types of information—such as known cartel routes, potential safe houses, and surveillance data—provides a comprehensive operational picture.

The Tunnels and the Trail: Technological Limitations and Innovations
El Chapo’s ability to evade capture for so long was not solely due to the ingenuity of law enforcement, but also due to his own elaborate schemes, which often included sophisticated infrastructure and evasion tactics. The infamous tunnels used to escape capture highlight a specific area where technology played a dual role: both as a tool for evasion and for detection.
- Tunnel Detection Technologies: The construction of elaborate tunnels presented a significant challenge for detection. While traditional ground-penetrating radar (GPR) can detect subsurface anomalies, the scale and complexity of El Chapo’s tunnel network often made it difficult to identify every entry and exit point. Advances in seismic sensors, advanced GPR techniques, and even acoustic monitoring systems are continuously being developed to improve the detection of subterranean structures. The ability to differentiate between natural geological formations and man-made tunnels remains a key area of research and development.
- Counter-Surveillance and Evasion Techniques: While the article focuses on law enforcement technologies, it is important to acknowledge that criminal organizations also employ counter-surveillance measures. This can range from simple tactics like driving in convoy to mask individual movements, to more sophisticated electronic countermeasures. However, the technological advantage typically lies with the state-sponsored agencies, who can deploy resources and expertise that are largely inaccessible to criminal enterprises.
The story of El Chapo’s pursuit is a testament to the evolving technological landscape and its impact on crime and law enforcement. As technology continues to advance, so too will the methods employed by both sides of this perpetual conflict. The sophisticated blend of surveillance, intelligence gathering, and analytical tools used to track and apprehend figures like El Chapo demonstrates the critical role of technology in modern criminal justice and the ongoing battle against transnational organized crime.
