The enigmatic title “Cheese Escape” immediately sparks curiosity, particularly within circles that appreciate intricate puzzles and the thrill of intellectual pursuit. While the phrase might evoke images of a playful scenario, its true meaning often lies hidden within a coded message, a challenge designed to test observation, deduction, and an understanding of digital or analog systems. In the context of technology and innovation, “Cheese Escape” likely refers to a metaphorical or literal challenge involving the deciphering of a system, a process, or a piece of data that is “trapped” or inaccessible, much like cheese might be perceived as being confined within its rind or packaging. This article delves into the potential interpretations of “Cheese Escape” within the realm of Tech & Innovation, exploring the types of codes and systems it might represent, and the innovative approaches used to “escape” or decode them.
Unpacking the Metaphor: Cheese as Data and Systems
The “cheese” in “Cheese Escape” serves as a potent metaphor for information, data, or even functional systems that are not readily accessible or understandable. Just as cheese can range from simple, easily consumed varieties to complex, aged forms with intricate internal structures and external rinds, digital data and technological systems can possess layers of complexity. The “escape” then signifies the process of breaking through these layers, whether it’s decrypting encrypted files, bypassing security protocols, reverse-engineering proprietary software, or even understanding the emergent behaviors of complex AI models.
Layers of Obfuscation and Access Control
In the technological landscape, information and functionality are frequently protected by various forms of obfuscation and access control mechanisms. These are the “rinds” and “casings” that the “cheese” is protected by.
Encryption and Data Security
At its core, encryption is the art of scrambling data to make it unintelligible to unauthorized parties. When we speak of “escaping” encrypted data, we are referring to the process of decryption. This can involve brute-force attacks, exploiting algorithmic weaknesses, or leveraging stolen cryptographic keys. The complexity of modern encryption algorithms means that “escaping” this form of cheese often requires significant computational power and sophisticated decryption techniques. The ongoing arms race between encryption and decryption methods is a fundamental aspect of cybersecurity and a constant driver of innovation in cryptography.
Proprietary Software and Hardware
Many technological products and services are built upon proprietary code and hardware designs. “Escaping” these systems might involve reverse-engineering the software to understand its inner workings, identify vulnerabilities, or even replicate its functionality. This can range from analyzing compiled binaries to dissecting circuit boards. Such efforts are crucial for interoperability, security auditing, and fostering open-source alternatives, pushing the boundaries of what is publicly understood and achievable.
Access Control Mechanisms
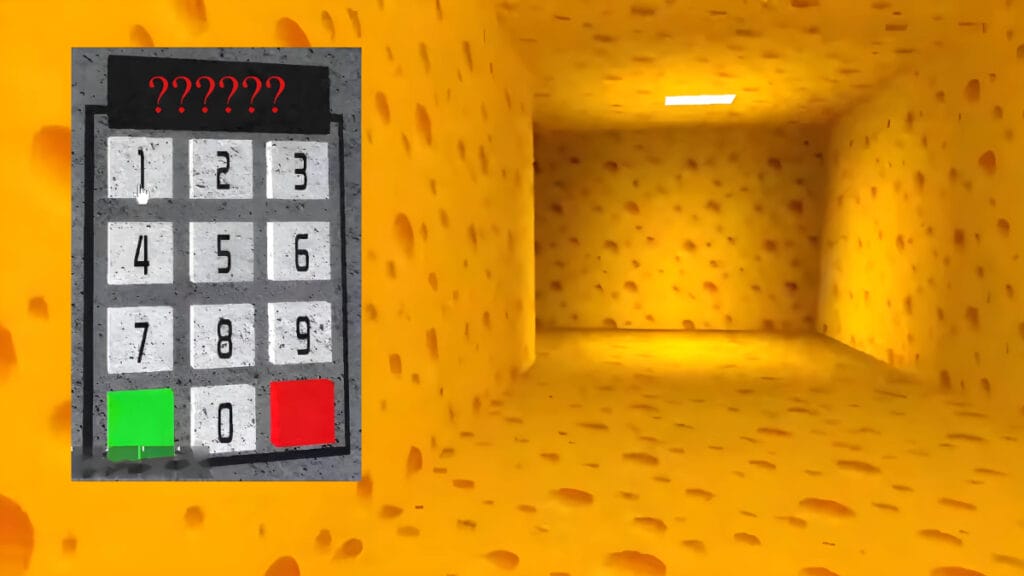
Beyond encryption, systems employ a myriad of access control measures, from passwords and multi-factor authentication to complex authorization frameworks. “Escaping” these often involves social engineering, exploiting authentication loopholes, or finding ways to elevate privileges. These methods highlight the human element in security and the constant need for vigilance and robust system design.
The “Code” in “Cheese Escape”: From Algorithms to Anomalies
The “code” within “Cheese Escape” is not necessarily a singular programming language or a simple substitution cipher. Instead, it represents the underlying logic, the rules, the patterns, and the vulnerabilities that define the system and its limitations. Understanding this code is paramount to achieving the “escape.”
Algorithmic Puzzles and Cryptography
At the heart of many technological challenges lies the domain of algorithms and cryptography. “Cheese Escape” could represent a puzzle where the solution is hidden within the steps of a specific algorithm, or where the data itself is a complex cipher.
Cryptographic Challenges
Many cybersecurity competitions and training platforms feature cryptographic challenges that mirror the “Cheese Escape” concept. Participants are presented with encrypted messages or encoded data and must apply their knowledge of cryptographic techniques, such as DES, AES, RSA, or even custom ciphers, to decipher the information. Success requires not only understanding the algorithms but also recognizing subtle patterns and potential weaknesses.
Algorithmic Reverse Engineering
In software development and security, reverse engineering algorithms is a critical skill. This involves taking a piece of software or a system’s behavior and reconstructing the underlying logic and data flow. This is akin to understanding how the “cheese” was made and how its structure was formed, allowing for its deconstruction.
Anomaly Detection and Behavioral Analysis
Sometimes, the “code” to escaping a system isn’t about direct decryption but about identifying deviations from expected behavior. This is particularly relevant in fields like AI and machine learning.
Identifying AI “Glitches”
In the context of advanced AI systems, “Cheese Escape” might refer to identifying and exploiting unexpected or emergent behaviors that were not explicitly programmed. This could involve finding situations where an AI makes illogical decisions, exhibits unintended biases, or behaves in a way that allows for manipulation or bypass. The “code” here is the anomaly itself, a deviation from the intended operational parameters.
Network Intrusion Detection
In cybersecurity, detecting intrusions often relies on identifying anomalous network traffic patterns. A sudden surge in unusual requests, unexpected data flows, or suspicious connection attempts can be the “code” that signals an unauthorized presence, prompting an “escape” response to secure the system.
Innovative Approaches to “Escaping” Complex Systems
The pursuit of “escaping” these complex “cheese” systems drives a remarkable amount of innovation across various technological domains. The methods employed are as diverse as the challenges themselves.
Leveraging Machine Learning for Decryption and Analysis
Machine learning (ML) is increasingly being employed to tackle complex “Cheese Escape” scenarios. ML models can be trained to identify patterns in encrypted data, predict algorithmic behaviors, and even generate novel attack vectors.
ML-Powered Cryptanalysis
Researchers are exploring the use of deep learning models to break sophisticated encryption algorithms. These models can learn subtle statistical properties of ciphertext that are difficult for traditional cryptanalysis methods to detect.
AI for Vulnerability Discovery
ML algorithms can also be trained to scan codebases and system configurations for potential vulnerabilities, acting as an automated “escape artist” by identifying weaknesses before they can be exploited maliciously.
Quantum Computing and the Future of Cryptography
The advent of quantum computing poses a significant threat to current encryption standards. If successfully developed, quantum computers could render many widely used encryption algorithms obsolete, forcing a complete paradigm shift in data security.
Post-Quantum Cryptography
The race is on to develop “post-quantum cryptography”—new encryption algorithms that are resistant to attacks from both classical and quantum computers. This is a proactive “escape” from a future threat, ensuring the continued security of digital information.
Quantum Cryptanalysis
Conversely, quantum computers could also be used to accelerate cryptanalysis, making the “escape” from certain forms of encryption more feasible. This creates a dual-use scenario where quantum technology can both secure and potentially compromise data.
Human Ingenuity and Collaborative Problem Solving
Despite the advancements in automated tools, human ingenuity and collaborative problem-solving remain indispensable in tackling the most challenging “Cheese Escape” scenarios.
Capture the Flag (CTF) Competitions
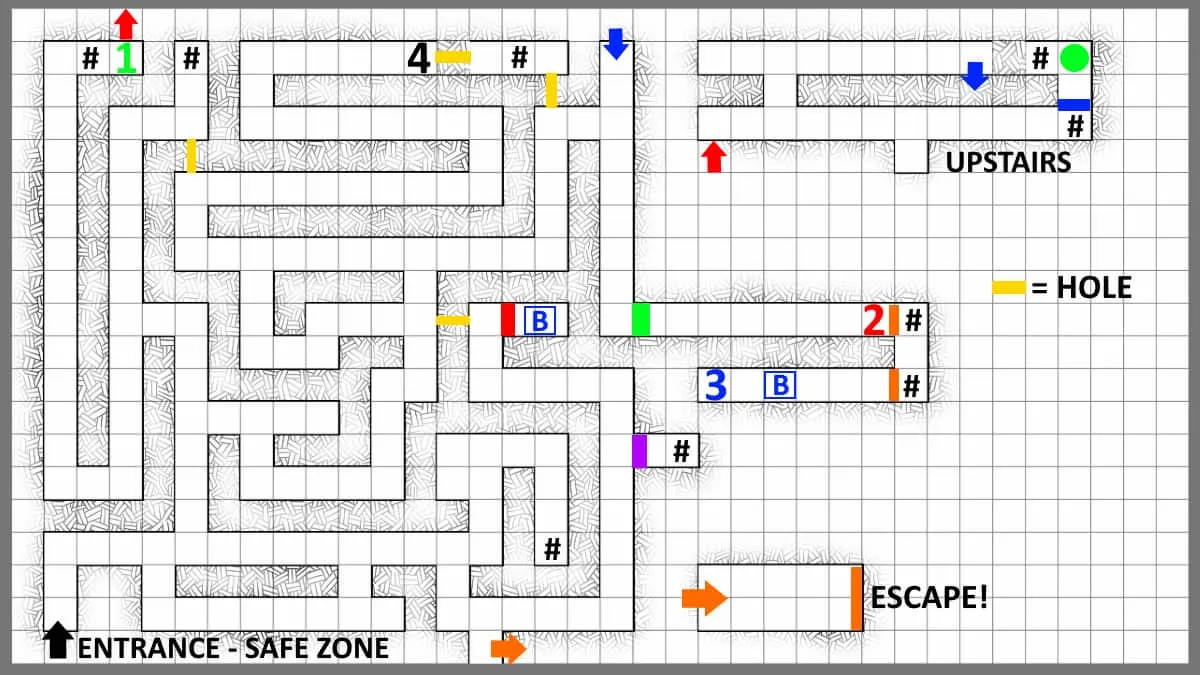
Cybersecurity “Capture the Flag” (CTF) events are prime examples of “Cheese Escape” challenges in action. Teams of individuals collaborate, applying a wide range of technical skills to solve puzzles, exploit vulnerabilities, and decrypt hidden information, all within a competitive and engaging framework. These events foster innovation and skill development in a practical, hands-on manner.
Open Source Intelligence (OSINT) and Crowdsourcing
The power of the collective can also be harnessed. Open Source Intelligence (OSINT) techniques, which involve gathering information from publicly available sources, can be crucial in understanding the context and potential weaknesses of a system. Crowdsourcing solutions to complex problems, including security challenges, allows for a broader range of perspectives and expertise to be applied, accelerating the “escape.”

Conclusion: The Enduring Quest for Access and Understanding
The concept of “Cheese Escape,” whether literal or metaphorical, underscores a fundamental human drive: the desire to understand, to access, and to overcome barriers. In the realm of Tech & Innovation, this drive is a constant catalyst for progress. From cracking complex codes and decrypting sensitive data to reverse-engineering intricate systems and understanding emergent AI behaviors, the challenges are numerous and ever-evolving. The innovative tools and techniques developed to “escape” these complex “cheeses”—from machine learning and quantum computing to collaborative problem-solving—are not merely about bypassing security or gaining access. They are about pushing the boundaries of our knowledge, fostering greater security, and ultimately, unlocking new possibilities for how we interact with and understand the technological world around us. The “code” within “Cheese Escape” is, in essence, the challenge itself, and the “escape” is the innovative solution that emerges from our persistent quest for understanding.
