In the digital age, understanding the intricacies of our interconnected lives has become paramount. While our focus often lies on the seamless flow of information and communication, the mechanisms behind blocked communication present a fascinating, albeit sometimes frustrating, area of exploration. This article delves into the technical underpinnings and user experience of attempting to contact an individual who has initiated a block on your communication channels. We will specifically examine this phenomenon through the lens of drone technology, exploring how similar blocking mechanisms function within the operational parameters of Unmanned Aerial Vehicles (UAVs).

Understanding Digital Blockades
Before we translate this concept to the realm of drones, it’s crucial to establish a foundational understanding of how blocking works in standard telecommunication systems. When an individual blocks your number on their smartphone, they are essentially instructing their device and network provider to reject incoming calls and messages from your specific identifier.
The Technical Infrastructure
At its core, a block is a rule implemented at the device or network level. When your phone attempts to initiate a call to a blocked number, the network or the recipient’s device recognizes your identifier. This recognition triggers a pre-defined action: the connection is terminated before it can be established, or the call is routed to voicemail without the recipient’s device ringing. Similarly, text messages are often silently discarded or never reach the recipient’s inbox. This process is designed to provide users with control over their communication flow and privacy.
User Perception and Experience
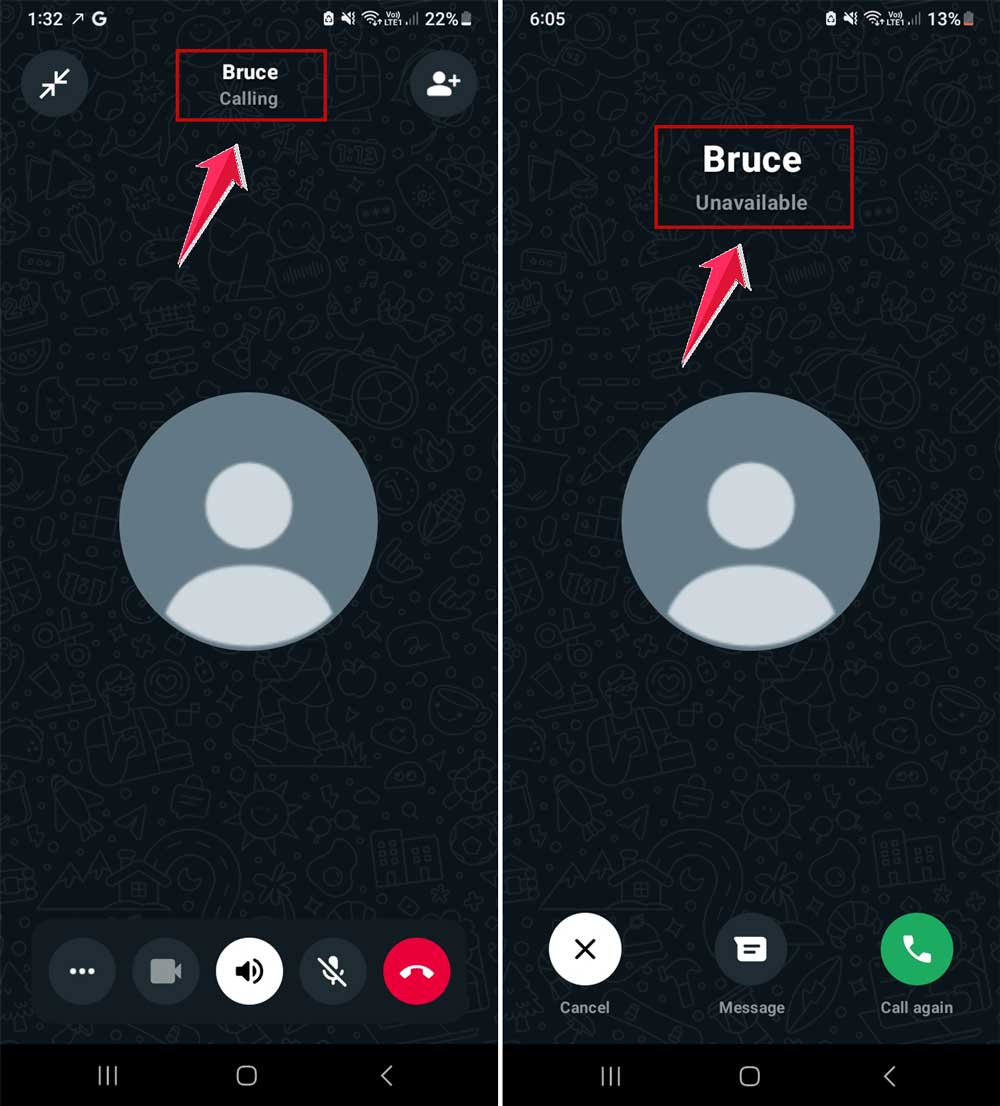
From the caller’s perspective, the experience can vary. A blocked call might immediately go to voicemail, display as “Call Failed,” or ring indefinitely without answer. Text messages may appear to send successfully but never receive a reply. This ambiguity can lead to confusion, frustration, and a desire to understand the underlying cause. The inability to establish contact is the primary manifestation of the block.
Blocking Mechanisms in Drone Operations
Translating the concept of a digital blockade to drone technology requires a shift in perspective from personal communication to operational control and access. In the context of drones, blocking mechanisms are not about silencing individual calls but rather about restricting operational access, geofencing, or preventing unauthorized interaction with a drone or its control systems.
Geofencing and Restricted Airspace
One of the most prominent forms of “blocking” in drone operations is geofencing. This technology utilizes GPS data to create virtual boundaries around specific areas where drone flight is prohibited or restricted. These restricted zones can include airports, military installations, sensitive government buildings, or densely populated areas.
How Geofencing Works
Drone manufacturers and aviation authorities implement geofencing through software embedded within the drone’s flight control system and its accompanying ground control station (GCS) or mobile application. When a drone attempts to fly into a geofenced area, its GPS receiver detects its proximity to the virtual boundary. The flight controller is programmed to react in several ways:
- Prevent Takeoff: In some cases, the drone will refuse to take off if its current location is within a restricted zone.
- Abort Flight: If the drone is already airborne and approaches a geofenced area, the flight controller might automatically abort the mission, hover in place, or even initiate a controlled landing.
- Limited Access: For less sensitive zones, the drone might be allowed to enter but with significant limitations, such as a reduced altitude ceiling or an inability to fly over specific points of interest.
The User Experience of Geofencing
For the drone pilot, encountering a geofence results in a clear inability to operate the drone within the designated area. The GCS or app will typically display a warning message, often accompanied by an audible alert, indicating that the flight path is restricted. Attempts to override the geofence are generally unsuccessful, as the system is designed with safety and regulatory compliance as a priority. This “blocking” prevents the drone from performing its intended function in that specific location.
Network and Control Link Interference
Another scenario that resembles a “block” in drone operations involves interference with the communication link between the drone and its controller, or between the drone and any networked systems it relies upon.
Signal Jamming and Spoofing

While often illegal and unethical, signal jamming involves transmitting radio frequencies that interfere with the drone’s control signals or GPS reception. This effectively “blocks” the pilot’s ability to command the drone or for the drone to receive accurate positional data. Similarly, GPS spoofing involves transmitting false GPS signals, tricking the drone into believing it is in a different location, which can lead to erratic behavior or an inability to maintain a stable flight path.
Network Restrictions
For drones that rely on cellular networks or Wi-Fi for telemetry, command, or data transmission (e.g., beyond visual line of sight – BVLOS operations), network outages or intentional network restrictions can act as a blocking mechanism. If the drone cannot establish or maintain a stable connection to its command and control infrastructure, its operational range and capabilities are severely limited, akin to being unable to call someone due to a dead zone.
Anti-Drone Systems
In more sophisticated and security-conscious environments, specialized anti-drone systems are employed. These systems can actively detect, track, and then neutralize or disable unauthorized drones.
Detection and Identification
Anti-drone systems often utilize a combination of radar, radio frequency scanners, acoustic sensors, and electro-optical/infrared (EO/IR) cameras to identify and track drones. Once a drone is detected, its identity and operational parameters are analyzed.
Countermeasures – The Ultimate Block
The “blocking” effect here is far more direct and decisive. Countermeasures can include:
- Jamming: Similar to what was discussed earlier, but implemented by a dedicated, often authorized, system to disrupt the drone’s control and navigation signals.
- Spoofing: Manipulating the drone’s GPS signals to lead it astray or down.
- Cyberattack: Infiltrating the drone’s software to gain control or disable it.
- Physical Interception: Employing other drones or physical means to capture or disable the target drone.
When an anti-drone system is actively engaged, the unauthorized drone is effectively “blocked” from continuing its mission, rendering it inoperable or forcing it to land. This is the most extreme form of blocking within drone operations, akin to a network severing all connections.
Parallels and Divergences
While the concept of “blocking” in telecommunications and drone operations shares the fundamental outcome of preventing communication or operation, the mechanisms and intentions differ significantly.
Intent and Purpose
In personal communication, blocking is typically an individual’s choice to cease contact with another specific person. It is a tool for personal boundary management and privacy. In drone technology, blocking mechanisms like geofencing are implemented by manufacturers or authorities for safety, security, and regulatory compliance. Anti-drone systems are deployed for defense against unauthorized aerial intrusions. The intent is not personal but rather systemic.
Technical Implementation
The technical implementation also varies. Phone blocking relies on identifiers (phone numbers) and network routing rules. Drone blocking often involves GPS, radio frequency control, and sophisticated software within the flight controller. Geofencing is a virtual boundary, while jamming and anti-drone systems involve active electronic warfare or interception.
User Experience
The user experience of being blocked on a phone can range from a missed call to silent message deletion. The user may not even be aware they are blocked until they try to contact the person. In drone operations, encountering a geofence is usually a clear, immediate, and often visually or audibly communicated restriction. Being targeted by an anti-drone system is a definitive and potentially mission-ending event for the drone pilot.
Conclusion: Control and Containment in the Digital Sky
The notion of “calling someone who blocked you” serves as an accessible analogy for understanding the various forms of restricted access and communication denial within the drone ecosystem. From individual pilots facing geofencing restrictions to the sophisticated countermeasures employed by anti-drone systems, the underlying principle is about control and containment. These “blocks” are not arbitrary; they are engineered to ensure safety, maintain order, and protect airspace. Understanding these mechanisms is crucial for any operator or enthusiast looking to navigate the increasingly complex and regulated world of unmanned aerial vehicles, ensuring their operations remain within the bounds of legality and safety, much like respecting the digital boundaries set by an individual.
