The acronym “WPA” is frequently encountered in discussions related to wireless networking, particularly in the context of securing Wi-Fi connections. While often used interchangeably with “Wi-Fi security” in general, WPA specifically refers to a set of security protocols designed to protect wireless computer networks. Understanding what WPA stands for is crucial for anyone aiming to secure their home or business network against unauthorized access and data interception.
Understanding the Evolution of Wireless Security
Before delving into what WPA stands for, it’s important to recognize its lineage and the security challenges it was designed to address. The initial standard for wireless networking, 802.11, did not include robust security measures. This led to the development of Wired Equivalent Privacy (WEP), the first attempt at securing Wi-Fi.
Wired Equivalent Privacy (WEP) – The Precursor to WPA
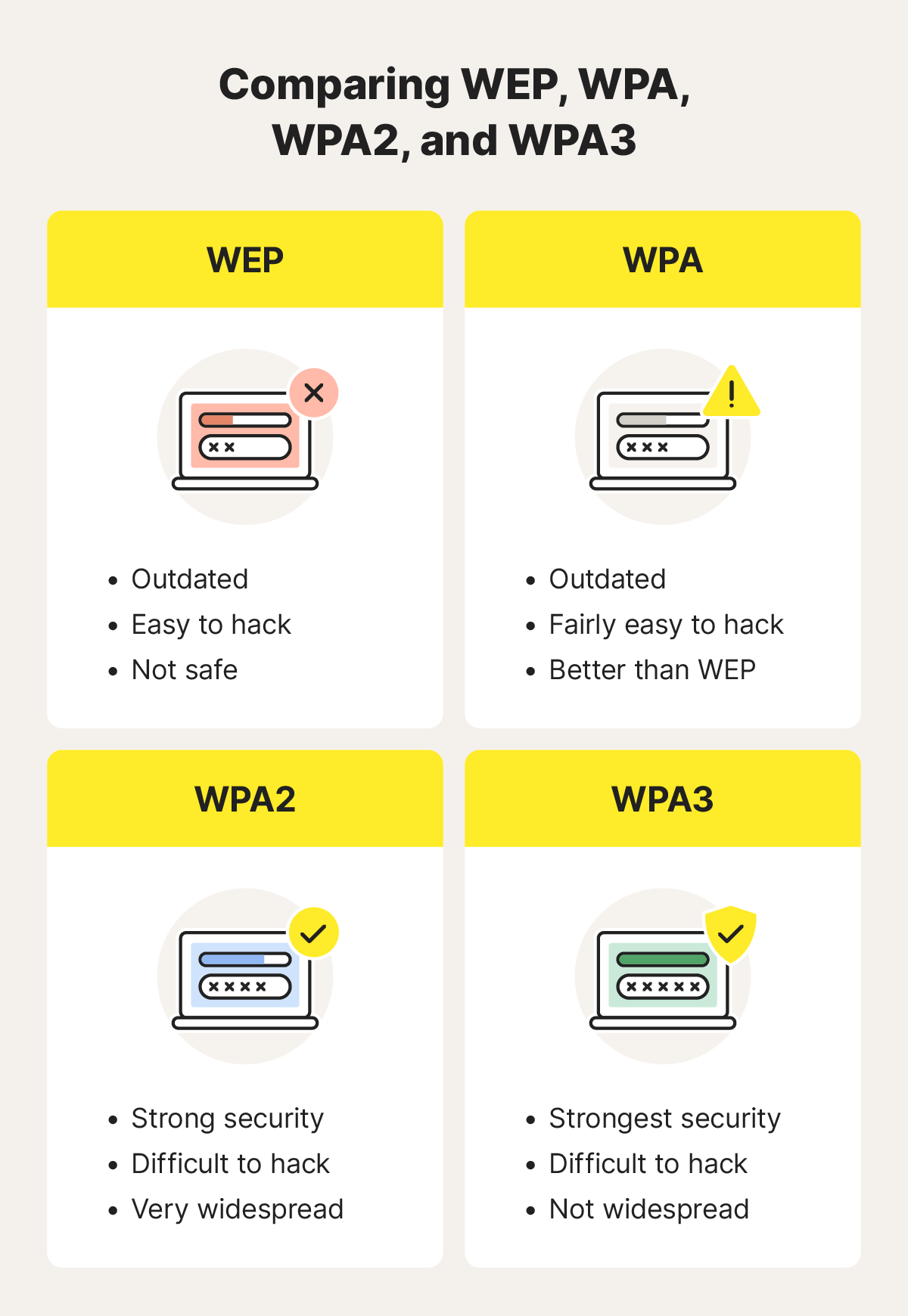
WEP was introduced in 1999 with the goal of providing a level of security comparable to that of a wired network. It used a static, shared key for both encryption and decryption. While seemingly a step forward, WEP had significant cryptographic flaws that made it vulnerable to decryption by even moderately skilled attackers within minutes. Its weaknesses were widely publicized, leading to its deprecation. The vulnerabilities of WEP highlighted the urgent need for more advanced security protocols, paving the way for WPA.
The Genesis of WPA: Addressing WEP’s Deficiencies
The shortcomings of WEP prompted the Wi-Fi Alliance to develop a more secure interim standard known as Wi-Fi Protected Access (WPA). WPA was designed to be a significant improvement over WEP while being compatible with existing hardware, a crucial factor for widespread adoption. It addressed WEP’s fundamental cryptographic weaknesses and introduced enhanced security features.
Wi-Fi Protected Access (WPA): The Foundation
WPA stands for Wi-Fi Protected Access. It was developed by the Wi-Fi Alliance as a security protocol to safeguard wireless computer networks. WPA was released in 2003 as a response to the critical security vulnerabilities found in WEP. Its primary objective was to provide a stronger encryption method and more secure authentication mechanisms.
Core Components of WPA
WPA implemented two key improvements over WEP:
Temporal Key Integrity Protocol (TKIP)
TKIP was the encryption protocol introduced with WPA. It was designed to be a drop-in replacement for WEP’s encryption algorithm, RC4, while addressing its weaknesses. TKIP dynamically changed encryption keys for each packet, making it significantly harder for attackers to crack the network. It also implemented a message integrity check (MIC) to ensure data authenticity and prevent tampering. While a substantial improvement over WEP, TKIP was later found to have some underlying cryptographic weaknesses that could be exploited with sufficient effort.
Message Integrity Check (MIC)
A crucial addition to WPA was the Message Integrity Check (MIC). This feature, often implemented as a Byte Flipping Attack Detection (BFAD) or a Michael mechanism, ensured that data packets had not been altered in transit. If a packet was modified, the MIC would detect it, and the packet would be discarded. This prevented attackers from injecting malicious data or altering existing transmissions.
Authentication Methods
WPA offered two primary authentication modes:
-
WPA-Personal (WPA-PSK): This mode uses a Pre-Shared Key (PSK), which is essentially a password. All devices connecting to the network use the same password to authenticate. This is the most common setup for home and small office networks. While simpler to set up, the security of the network heavily relies on the strength of the PSK. A weak password can still make the network vulnerable.
-
WPA-Enterprise: This mode uses the IEEE 802.1X standard for authentication, which is more robust and scalable for larger networks. It requires a RADIUS (Remote Authentication Dial-In User Service) server to authenticate users. Instead of a shared password, each user or device is assigned unique credentials, providing much stronger security and better management capabilities for enterprise environments.
Wi-Fi Protected Access II (WPA2): The Next Generation
While WPA represented a significant leap in wireless security, its underlying TKIP protocol was eventually found to have exploitable weaknesses. This led to the development of a more secure and robust standard: WPA2.
WPA2 stands for Wi-Fi Protected Access II. It was released in 2004 and became the industry standard for Wi-Fi security for many years. WPA2 is based on the IEEE 802.11i amendment, which provided a more comprehensive and secure framework for wireless network protection.
Key Advancements in WPA2
WPA2 introduced several critical improvements over WPA:
Advanced Encryption Standard (AES)
The most significant advancement in WPA2 was the adoption of the Advanced Encryption Standard (AES), specifically in its Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP). AES is a much stronger and more modern encryption algorithm than the RC4 used in WEP and TKIP. CCMP provides both strong encryption and robust data integrity, making it highly resistant to cryptographic attacks. This was a monumental improvement in securing wireless communications.
Enhanced Authentication
Similar to WPA, WPA2 also supports two authentication modes:
-
WPA2-Personal (WPA2-PSK): This mode continues to use a Pre-Shared Key for authentication. While the encryption is significantly stronger with AES, the security of the network still depends on the strength of the PSK. Users are strongly advised to use long, complex, and unique passwords for WPA2-PSK networks.
-
WPA2-Enterprise: This mode also utilizes IEEE 802.1X authentication with a RADIUS server. This offers the highest level of security and manageability, making it the preferred choice for businesses and organizations. It ensures individual user authentication and provides centralized control over network access.
The Importance of WPA2
WPA2 became the de facto standard for Wi-Fi security due to its strong encryption and improved authentication. For a considerable period, it was considered the best available option for protecting wireless networks from eavesdropping and unauthorized access. However, even strong security protocols can have vulnerabilities discovered over time, and the landscape of cybersecurity is constantly evolving.
Wi-Fi Protected Access 3 (WPA3): The Latest Standard
As cyber threats continued to evolve, even WPA2 began to show areas where it could be further enhanced. In response, the Wi-Fi Alliance introduced WPA3.
WPA3 stands for Wi-Fi Protected Access 3. Announced in 2018, it represents the latest generation of Wi-Fi security protocols, aiming to address some of the remaining vulnerabilities in WPA2 and introduce new security features for both consumer and enterprise networks.
Key Innovations in WPA3
WPA3 introduces several significant upgrades to wireless security:
Simultaneous Authentication of Equals (SAE)
One of the most notable improvements in WPA3-Personal is the introduction of Simultaneous Authentication of Equals (SAE). SAE is a more secure method of authentication that replaces the PSK system used in WPA and WPA2-Personal. SAE is an enhanced version of the Dragonfly handshake protocol, offering stronger protection against brute-force attacks. Even if an attacker knows the network name (SSID), SAE makes it significantly more difficult to guess the password, protecting against dictionary attacks and offline password cracking attempts.
Enhanced Open Security
For open Wi-Fi networks (those that don’t require a password, often found in public places), WPA3 introduces Wi-Fi Enhanced Open. This technology provides individualized data encryption between the user and the network access point, even without a pre-shared password. This is a crucial step in protecting users from eavesdropping on public Wi-Fi. Previously, open networks offered no encryption, leaving all data vulnerable.
Stronger Encryption for Enterprise Networks
WPA3-Enterprise further enhances security for business networks. It mandates the use of 192-bit cryptographic strength in its security protocols, providing an even higher level of protection against sophisticated attacks. This is particularly important for organizations dealing with sensitive data.
Forward Secrecy
WPA3 also emphasizes forward secrecy. This means that even if a long-term secret key is compromised, past communications remain secure because each session uses a unique, ephemeral key. This ensures that a breach of one session’s key does not compromise the security of other sessions.
Choosing the Right WPA Standard for Your Network
Understanding what WPA stands for and its evolution is critical for making informed decisions about your wireless network security.
Recommendations for Home Networks
For most home users, WPA2-Personal is still considered the minimum acceptable standard. However, if your router and devices support it, WPA3-Personal is the superior choice. Always use a strong, unique password for your Wi-Fi network, regardless of the WPA standard. Avoid using “admin,” “password,” or common phrases.
Recommendations for Business Networks
For businesses, WPA2-Enterprise has been the recommended standard for years. With the advent of WPA3, WPA3-Enterprise is now the most secure option available, offering the highest level of protection and advanced features like 192-bit encryption. Ensure your network infrastructure, including routers and access points, supports these advanced security protocols.
Recognizing and Upgrading
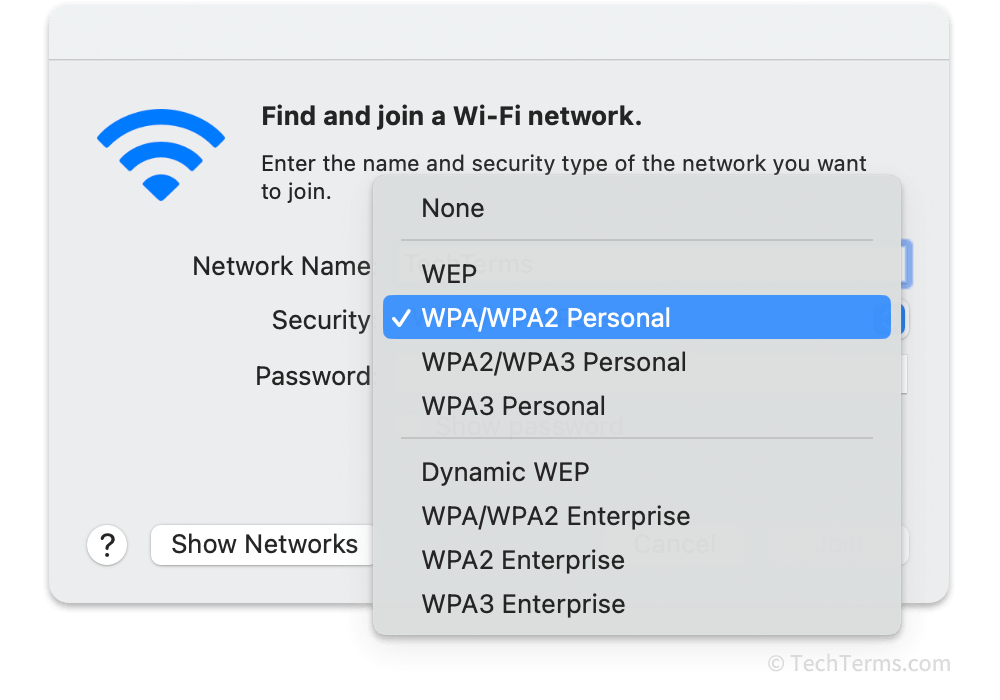
When configuring your Wi-Fi router, you will typically see options for WPA, WPA2, WPA3, and various combinations like WPA2/WPA3-Personal. It’s advisable to select the most secure option your devices support. Older devices may only support WPA or WPA2. If you have many older devices, you might need to use a mixed mode (e.g., WPA2/WPA3) temporarily, but aim to upgrade older devices to support WPA3 for optimal security.
In conclusion, WPA stands for Wi-Fi Protected Access, a suite of security protocols designed to secure wireless networks. From its origins as a necessary upgrade from the insecure WEP to the robust WPA2 and the cutting-edge WPA3, each iteration has brought significant advancements in protecting wireless communications. Staying informed about these standards and implementing the most secure options available is paramount in today’s interconnected world.
