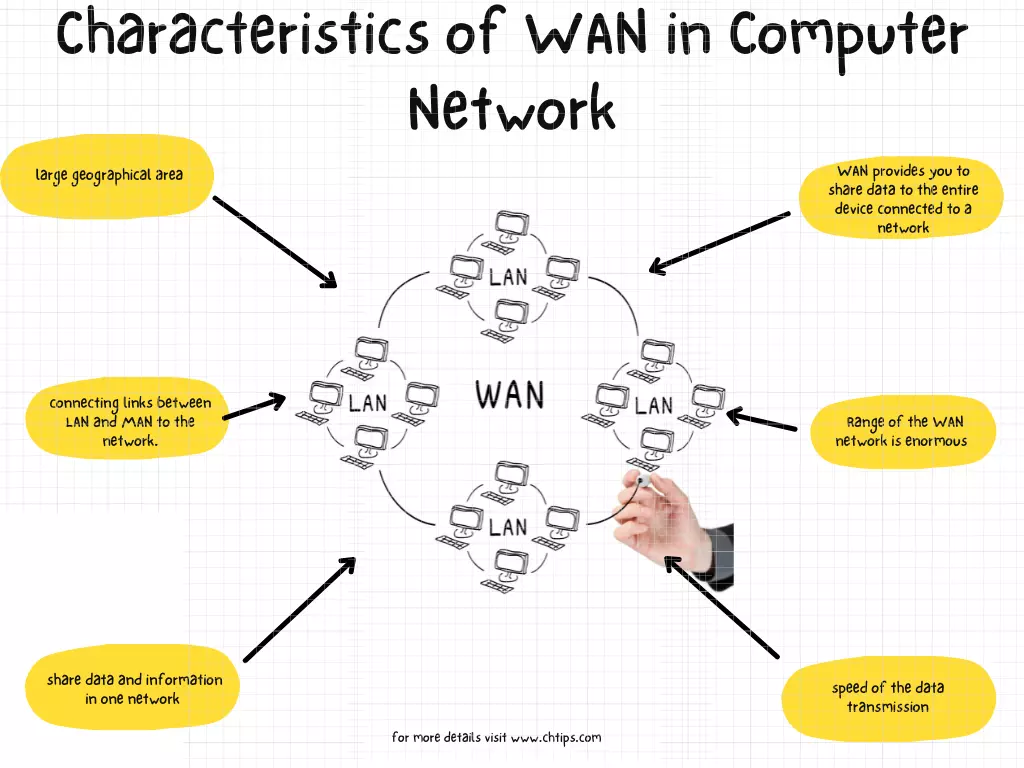
A Wide Area Network (WAN) is a crucial component of modern technology infrastructure, particularly in the realm of interconnected systems. While the term “WAN” might evoke images of vast geographical distances and complex network topologies, its fundamental characteristics are what define its utility and differentiate it from other network types, such as Local Area Networks (LANs). Understanding these characteristics is paramount for anyone involved in designing, managing, or utilizing networked systems, especially within the context of advanced technological applications.
Geographic Scope
The most defining characteristic of a WAN is its extensive geographic scope. Unlike LANs, which are typically confined to a single building, campus, or small cluster of buildings, WANs span large geographical areas. This can range from connecting different offices of a single corporation across a city or state to linking multinational enterprises across continents. The sheer scale of a WAN necessitates a different approach to network design, management, and security compared to the localized nature of a LAN.
Interconnecting Distant Locations
The primary purpose of this broad geographic scope is to enable communication and resource sharing between geographically dispersed locations. This could involve:
- Branch Office Connectivity: Businesses with multiple physical locations rely on WANs to connect their branches to a central headquarters or to each other. This allows for seamless data exchange, shared access to company resources, and unified communication channels.
- Global Access to Services: Many cloud-based services and online platforms operate on a global scale, accessed by users from diverse locations. The underlying infrastructure that facilitates this widespread access often involves WAN technologies.
- Distributed Computing and Research: In scientific and research environments, WANs are essential for connecting supercomputing facilities, data repositories, and research teams spread across the globe, enabling collaborative projects and the sharing of massive datasets.
Scalability and Reach
The ability of a WAN to scale and reach virtually any point on the globe is a testament to its design and the underlying technologies it employs. This scalability is not merely about increasing the number of connected devices but also about extending the network’s reach to accommodate new locations as an organization grows or its operational needs evolve. This broad reach is what enables global commerce, international collaboration, and the accessibility of information on an unprecedented scale.
Network Infrastructure and Technologies
The extensive geographic scope of a WAN is made possible by a complex interplay of various network infrastructure and technologies. Unlike LANs that often rely on privately owned cabling, WANs typically leverage a combination of public and private telecommunications infrastructure.
Leased Lines and Circuits
Historically, leased lines and dedicated circuits have been fundamental to WAN connectivity. These are private communication paths purchased from telecommunications providers, offering guaranteed bandwidth and performance between specific locations. While offering high reliability, they can also be expensive and less flexible for rapidly changing network demands.
Public Switched Telephone Network (PSTN) and Dial-up
In the early days of WANs, dial-up modems over the PSTN provided a cost-effective, albeit slow, method for connecting remote locations. While largely superseded by faster technologies, dial-up still finds niche applications in disaster recovery scenarios or for very low-bandwidth requirements.
Digital Subscriber Line (DSL) and Cable Modems
As broadband technologies emerged, DSL and cable modems offered higher speeds over existing copper and coaxial cable infrastructure, respectively. These technologies became popular for small to medium-sized businesses and for home users requiring more robust internet connectivity, often forming the backbone for smaller WAN segments.
Fiber Optic Networks
The most significant advancements in WAN infrastructure have come with the widespread deployment of fiber optic cables. Offering vastly superior bandwidth, lower latency, and greater reliability compared to copper-based technologies, fiber optics form the backbone of modern high-speed WANs. This includes:
- Fiber-to-the-Home (FTTH) and Fiber-to-the-Business (FTTB): Bringing high-speed fiber connections directly to end-users, enabling faster access to WAN resources.
- Dense Wavelength Division Multiplexing (DWDM): A technology that allows multiple data streams to be transmitted simultaneously over a single fiber optic cable by using different wavelengths of light, dramatically increasing the capacity of long-haul WAN links.
Wireless Technologies
Wireless technologies also play a vital role in WAN connectivity, especially in areas where wired infrastructure is impractical or unavailable.
- Satellite Communications: For extremely remote locations or mobile platforms, satellite links provide WAN connectivity, albeit often with higher latency.
- Cellular Networks (3G, 4G, 5G): Mobile broadband technologies provide increasingly capable WAN access, allowing devices and small offices to connect to the internet and private networks on the go or in underserved areas.
- Fixed Wireless Access (FWA): This technology uses point-to-point or point-to-multipoint radio links to provide broadband internet access, serving as a viable alternative to wired connections in certain geographic contexts.
Multiprotocol Label Switching (MPLS)
MPLS is a routing technique that directs data from one network node to the next based on short path labels rather than long network addresses. It is commonly used in enterprise WANs to provide traffic engineering, quality of service (QoS), and predictable performance for different types of traffic. MPLS allows organizations to prioritize critical applications like voice and video conferencing over less time-sensitive data.
Software-Defined Wide Area Networking (SD-WAN)
SD-WAN represents a paradigm shift in WAN architecture. It utilizes software to intelligently manage and route traffic across various transport links (e.g., MPLS, broadband internet, LTE), optimizing performance and reducing costs. SD-WAN solutions offer enhanced agility, centralized control, and simplified management for complex WAN deployments.
Data Transmission and Speed
Another critical characteristic of a WAN is its approach to data transmission and speed. The speed and efficiency of data transfer over a WAN are influenced by a multitude of factors, including the underlying technologies, the distances involved, and the network’s architecture.
Bandwidth and Latency Considerations
The bandwidth of a WAN connection refers to the maximum rate at which data can be transferred. This is typically measured in bits per second (bps), kilobits per second (Kbps), megabits per second (Mbps), or gigabits per second (Gbps). WANs often exhibit lower bandwidth compared to LANs, especially for connections that traverse public infrastructure or rely on older technologies.
Latency, on the other hand, refers to the time it takes for a data packet to travel from its source to its destination. This is often measured in milliseconds (ms). Latency is a critical factor for real-time applications such as voice over IP (VoIP) and video conferencing. WANs, especially those spanning long distances, inherently have higher latency due to the physical distance data must travel and the number of network devices it must traverse.
Impact on Applications
The combination of bandwidth and latency significantly impacts the performance of applications running over a WAN.
- High-Bandwidth, Low-Latency Applications: Applications that require rapid transfer of large data volumes with minimal delay, such as high-definition video streaming, large file transfers, and real-time collaboration tools, are best served by high-performance WAN connections.
- Latency-Sensitive Applications: Applications like online gaming, VoIP, and remote desktop control are highly sensitive to latency. Even with high bandwidth, excessive latency can render these applications unusable or severely degraded.
- Bandwidth-Constrained Applications: For applications that are less sensitive to latency but require consistent data flow, such as email or basic web browsing, lower bandwidth connections might suffice, though performance will be noticeably slower.
Traffic Management and Optimization
To mitigate the challenges of bandwidth limitations and latency, WANs employ various traffic management and optimization techniques:
- Quality of Service (QoS): QoS mechanisms prioritize certain types of network traffic over others. For example, voice traffic can be given higher priority than file transfers to ensure clear and uninterrupted conversations.
- Traffic Shaping and Policing: These techniques control the rate at which traffic is sent onto the network, preventing congestion and ensuring fair access for all users.
- Data Compression: Compressing data before transmission can reduce the amount of data that needs to be sent, effectively increasing available bandwidth and reducing transfer times.
- Caching: Storing frequently accessed data closer to the end-users can reduce the need to retrieve it from distant servers, thereby improving response times.
Security and Management
The distributed nature and vast scope of WANs introduce unique challenges related to security and management. Ensuring the integrity, confidentiality, and availability of data across geographically dispersed locations requires robust security protocols and centralized management strategies.
Network Security Measures
- Firewalls: Essential for controlling and monitoring incoming and outgoing network traffic, firewalls act as the first line of defense against unauthorized access and malicious attacks. In WAN environments, firewalls are often deployed at network perimeters and between different network segments.
- Virtual Private Networks (VPNs): VPNs create encrypted tunnels over public networks, such as the internet, to securely connect remote users or branch offices to a private network. This ensures that data transmitted over the WAN remains confidential and protected from eavesdropping.
- Intrusion Detection and Prevention Systems (IDPS): These systems monitor network traffic for suspicious activity and can either alert administrators to potential threats or actively block malicious traffic.
- Access Control Lists (ACLs): ACLs are sets of rules that define which users or devices are allowed to access specific network resources. They are crucial for enforcing granular security policies across a distributed network.
- Encryption: End-to-end encryption is vital for protecting sensitive data as it travels across the WAN. This can be applied at various layers, from the application layer to the network layer.
Centralized Management and Monitoring
Managing a dispersed WAN infrastructure can be complex. Centralized management tools and strategies are therefore critical.
- Network Management Systems (NMS): NMS software allows administrators to monitor the performance of network devices, identify and diagnose problems, and manage configurations from a single console.
- Configuration Management: Ensuring consistent configurations across all WAN devices is essential for stability and security. Automated configuration management tools can streamline this process.
- Performance Monitoring: Continuous monitoring of network performance metrics (bandwidth utilization, latency, packet loss) helps identify bottlenecks and potential issues before they impact users.
- Remote Access and Control: Secure remote access capabilities enable IT staff to manage and troubleshoot WAN devices from anywhere, reducing the need for on-site visits.
Addressing the Extended Attack Surface
The broad reach of a WAN inherently creates a larger attack surface. Every connected endpoint, every link, and every device within the WAN represents a potential vulnerability. Therefore, a comprehensive security strategy that addresses all these points is crucial. This includes regular security audits, vulnerability assessments, and prompt patching of software and firmware on all network devices. The layered security approach, combined with proactive monitoring and incident response plans, is fundamental to maintaining a secure and reliable WAN.

Conclusion
In summary, a Wide Area Network is characterized by its expansive geographic scope, the diverse infrastructure and technologies it employs, its specific considerations for data transmission speed and management, and the paramount importance of robust security and centralized management. These characteristics collectively define how WANs enable global connectivity, facilitate complex business operations, and underpin many of the digital services we rely on daily. Understanding these defining attributes is key to appreciating the intricate and vital role WANs play in the modern technological landscape.
