In an age defined by digital interaction, the phrase “what to do if you forgot your Facebook password” resonates with nearly everyone. It’s a trivial yet universal problem, a moment of minor panic when a gateway to our online identity seems to vanish. However, beneath this seemingly simple query lies a profound metaphor for one of the most critical challenges in the rapidly evolving landscape of Tech & Innovation: the imperative of secure access, robust control, and resilient recovery within complex technological systems.
When we consider the cutting edge of innovation—autonomous AI systems, sophisticated IoT networks, quantum computing infrastructure, or critical national digital grids—the notion of “forgetting a password” transcends a mere inconvenience. It can translate into a catastrophic loss of control, a critical data breach, or even the complete paralysis of essential operations. This article delves into how the core principles of digital access, security, and recovery, exemplified by the everyday problem of a forgotten password, are being addressed and innovated upon within the broader realm of modern technology. We explore the advanced strategies and groundbreaking developments that ensure resilience, continuity, and secure stewardship in an increasingly interconnected and automated world, transforming how we understand and manage access to the digital future.

The Metaphorical Password: Access and Control in Advanced Systems
The concept of a “password” isn’t merely a string of characters; it represents a key, a token of authority that grants access and control. In advanced technological domains, this key takes on manifold forms, and its loss or compromise can have far-reaching consequences. Understanding how we manage and safeguard these metaphorical passwords is central to the progress of innovation.
Autonomous Systems and Control Overrides
Consider the burgeoning field of autonomous systems – from self-driving vehicles and sophisticated industrial robots to advanced drone fleets and AI-driven logistical networks. What happens when these systems, designed for independent operation, encounter unforeseen circumstances, malfunction, or, in a worst-case scenario, deviate from their intended parameters? This is the high-stakes equivalent of “forgetting the password” to an active, powerful system.
The innovation here lies in designing robust emergency protocols and manual override capabilities. These are the “recovery mechanisms” for autonomous control. Systems incorporate multi-layered failsafes, often involving both digital and physical circuit breakers, secure communication channels for remote intervention, and geographical containment protocols. The development of human-in-the-loop (HITL) systems, where AI handles routine tasks but human operators retain ultimate oversight and the ability to intervene, represents a sophisticated approach to ensuring that control can always be “recovered” even if automated processes falter. The “password” in this context isn’t just about initial access but about maintaining a secure, verifiable pathway to reassume command when necessary, preventing autonomous entities from becoming truly uncontrollable.
AI Ethics and Explainability (XAI)
Another critical dimension of the metaphorical password emerges in the realm of artificial intelligence. As AI models grow in complexity, particularly with deep learning architectures, they often become “black boxes”—systems that produce accurate results but whose internal decision-making processes are opaque even to their creators. In this scenario, “forgetting the password” translates to losing understanding or control over why an AI makes certain decisions. This lack of transparency poses significant ethical, legal, and operational challenges, particularly in high-stakes applications like medical diagnostics, financial trading, or judicial sentencing.
The innovation of Explainable AI (XAI) seeks to “recover” this lost insight. XAI techniques aim to make AI models more transparent and interpretable, providing explanations for their outputs. This involves developing methods to visualize internal states, identify influential features, and generate human-understandable justifications for decisions. By recovering explainability, we effectively regain a “password” to understanding the AI’s internal logic, enabling developers to debug, audit, and ethically govern AI systems. It allows for critical oversight, ensuring that AI operates within acceptable boundaries and that its reasoning can be scrutinized, much like reviewing a login history after a security incident.
Fortifying Digital Gates: Innovative Security & Authentication
The foundation of preventing “forgotten password” scenarios, or mitigating their impact, lies in robust security and authentication. While the literal password remains a staple, Tech & Innovation is rapidly moving beyond its limitations, developing far more sophisticated mechanisms to safeguard access to sensitive systems and data.
Beyond Passwords: Multi-Factor Authentication (MFA) Evolution
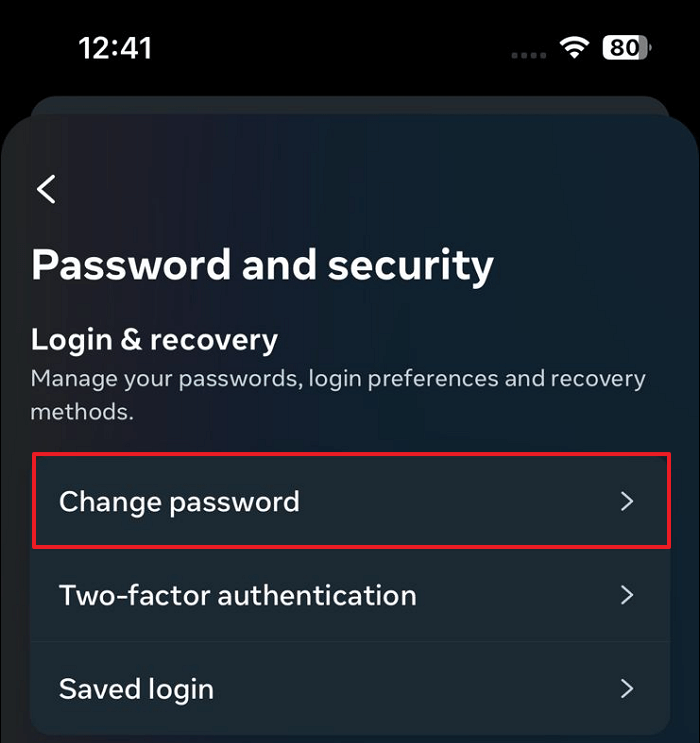
The traditional password, prone to being forgotten, guessed, or stolen, is increasingly recognized as an insufficient primary defense. The evolution of Multi-Factor Authentication (MFA) is a cornerstone of modern digital security, adding layers of verification to ensure that even if one “password” is compromised, access remains secure. For critical tech infrastructure, MFA has evolved far beyond SMS codes.
Advanced MFA implementations now include sophisticated biometrics (fingerprint, facial recognition, iris scans, voice biometrics), hardware security keys (FIDO U2F/WebAuthn standards), and behavioral analytics (analyzing typing patterns, mouse movements, or typical device usage to confirm identity). These innovations provide a much stronger “proof of identity” than a simple password. For instance, accessing a secure industrial control system might require a hardware token combined with a biometric scan and geo-fencing verification, making it virtually impossible for an unauthorized party to “guess the password” or exploit a single point of failure. The emphasis is on proving who you are through multiple, distinct attributes, making “forgetting” one element less critical as other factors can still grant access.
Blockchain for Immutable Access Logs and Identity Management
Blockchain technology, initially known for cryptocurrencies, is emerging as a powerful tool for secure identity management and immutable access control. Its decentralized, distributed ledger architecture offers a novel approach to safeguarding digital “passwords” and access records.
In a blockchain-based identity system, users can own and control their digital identities and credentials, rather than relying on centralized authorities (like a social media company or a government database). This concept of “Self-Sovereign Identity” (SSI) means that proof of access rights or identity attributes can be stored securely on a blockchain, verifiable by anyone but controlled only by the user. If an individual needs to “log in” or prove access rights to a critical system, they can present cryptographically signed credentials from their SSI wallet. This not only enhances security by removing a central honeypot for attackers but also provides an immutable audit trail of all access events. The “forgotten password” scenario becomes less about recovering a secret string and more about recovering control over one’s secure digital identity on a decentralized network, where cryptographic keys act as the ultimate password, often protected by secure hardware modules.
Recovery and Resilience: Strategies for System Continuity
Even with the most advanced security, the possibility of unforeseen access issues—whether a literal forgotten password, a system malfunction, or a security breach—remains. Tech & Innovation is therefore heavily focused on building systems that are not only secure but also resilient, with inherent capabilities for recovery and continuity.
Redundancy and Distributed Systems
A fundamental principle of modern tech resilience is redundancy. Just as a single forgotten password can lock you out, a single point of failure can cripple an entire system. Innovative architectures mitigate this by distributing components and data across multiple locations and servers, ensuring that if one “key” is lost or one “door” becomes inaccessible, others remain functional.
Cloud computing, with its distributed infrastructure and automated failover mechanisms, is a prime example. Data and applications are replicated across numerous data centers, making them highly available. If a server goes down or a data segment is corrupted (metaphorically, “forgotten”), redundant copies immediately take over, ensuring seamless service. Edge computing extends this resilience closer to the data source, processing information locally to reduce latency and dependence on centralized servers. Similarly, distributed ledgers and mesh networks are designed with no central authority, meaning a loss of access or compromise of any single node does not bring down the entire system, offering inherent resilience against single points of failure.

Intelligent Anomaly Detection and Self-Healing Systems
The evolution of AI and machine learning has given rise to intelligent systems capable of detecting anomalies and even initiating self-healing processes. These innovations act as advanced “password recovery” mechanisms for the entire system, going beyond human intervention.
AI-powered monitoring systems continuously analyze network traffic, system logs, and user behavior patterns. They can detect unusual access attempts, system malfunctions, or performance degradations that might indicate a problem, even if no one has explicitly “forgotten a password.” Upon detecting an anomaly, these systems can automatically trigger alerts, isolate compromised components, roll back to a previous stable state, or even deploy patches. Predictive maintenance uses AI to anticipate potential failures before they occur, scheduling proactive interventions. This ability for systems to autonomously “remember” their correct state and “recover” from errors significantly enhances operational continuity, reducing downtime and protecting against disruptions caused by various forms of “lost access.”
The Human Element: Training, Policy, and Future-Proofing
Despite technological advancements, the human element remains a crucial factor in both creating vulnerabilities and enabling solutions. Effective access management and recovery strategies in Tech & Innovation require a strong emphasis on human practices and overarching policies.
User Education and Best Practices
No matter how sophisticated the security measures, human error remains a leading cause of security incidents. Just as a strong password is useless if written on a sticky note, advanced tech systems are vulnerable if operators do not follow best practices. User education is critical for managing access to complex technologies.
This involves comprehensive training on secure credential management, understanding social engineering tactics, recognizing phishing attempts, and knowing proper protocols for using multi-factor authentication and secure hardware. For engineers and developers, it extends to secure coding practices, understanding supply chain risks, and implementing security-by-design principles. Continuous education ensures that as technology evolves, so does the human understanding of how to securely interact with it, preventing the “forgetting” of essential security practices.
Policy Frameworks for Digital Access and Disaster Recovery
Beyond individual actions, robust policy frameworks are essential to govern digital access, data handling, and disaster recovery in technological environments. These policies provide the structural “remembering” for an organization, dictating how to react when access is lost or compromised.
Policies define clear roles and responsibilities, establish protocols for incident response, mandate regular security audits, and outline procedures for data backup and recovery. They also address regulatory compliance, such as GDPR or HIPAA, ensuring that sensitive data access is managed lawfully and ethically. For critical infrastructure, these frameworks often include highly detailed business continuity plans, which are essentially pre-written instructions for “what to do if you forgot your password” for an entire operational system, including defined recovery time objectives (RTOs) and recovery point objectives (RPOs). These frameworks are continuously reviewed and updated to adapt to new threats and technological advancements, future-proofing organizations against evolving access challenges.
Conclusion
The seemingly mundane query “what to do if u forgot your facebook password” opens a window into the complex and critical world of access, security, and recovery within Tech & Innovation. From safeguarding control in autonomous systems and ensuring transparency in AI to developing multi-factor authentication and leveraging blockchain for identity management, the principles of maintaining secure access and enabling robust recovery are paramount.
The solutions extend beyond simple passwords, embracing redundant system architectures, intelligent self-healing mechanisms, and comprehensive human-centric strategies like continuous education and well-defined policy frameworks. As technology continues its relentless march forward, creating increasingly intricate and powerful systems, the challenge of managing access and ensuring resilience will only intensify. The ongoing innovation in these areas is not just about convenience; it’s about preserving control, securing data, and ensuring the continuous, reliable operation of the digital fabric that underpins our modern world, ensuring that even if a “password” is metaphorically forgotten, the gateway to progress remains open and secure.
