In the fast-evolving landscape of Tech & Innovation, access to critical platforms is paramount. Whether it’s a dashboard controlling a fleet of autonomous drones, an AI/ML development environment, a remote sensing data analytics portal, or an IoT device management system, these platforms are the nerve centers of modern technological advancements. Losing access, even temporarily, due to a forgotten password can halt progress, jeopardize data integrity, and even compromise operational safety. While the frustration of a forgotten password is universally relatable, its implications within the Tech & Innovation sphere can be far more severe than merely missing out on a social media update. This guide provides a professional, insightful, and engaging approach to recovering access to your essential tech and innovation platforms, emphasizing best practices for both recovery and prevention.

Understanding the Stakes: Why Platform Access is Crucial in Tech & Innovation
The digital backbone of contemporary innovation relies heavily on sophisticated software platforms. These aren’t just applications; they are often integrated ecosystems that manage complex operations, process vast datasets, and enable groundbreaking research. Forgetting a password here isn’t a minor inconvenience; it’s a potential operational roadblock.
The Ecosystem of Modern Tech Platforms
The “Tech & Innovation” category encompasses a broad spectrum of specialized platforms. Consider:
- Autonomous Systems Management: Dashboards for planning, monitoring, and controlling drone fleets, robotic systems, or autonomous vehicles. Losing access here means losing command over physical assets.
- AI/ML Development & Deployment: Cloud-based environments for model training, data annotation, algorithm testing, and deploying AI solutions. Access is critical for continuous iteration and deployment.
- IoT Device Management: Platforms that connect, monitor, and control thousands of internet-connected devices, from smart sensors to industrial machinery. A lapse in access can lead to unmonitored systems or inability to respond to critical alerts.
- Remote Sensing & Data Analytics: Portals for accessing, processing, and analyzing satellite imagery, drone-collected data, or other geospatial intelligence. These are vital for environmental monitoring, urban planning, or disaster response.
- Collaborative Innovation Hubs: Secure platforms where distributed teams co-develop intellectual property, manage research projects, and share sensitive information related to emerging technologies.
Each of these platforms represents a nexus of data, control, and intellectual capital. Unfettered, secure access is the oxygen for innovation.
Impact of Lost Access
The consequences of losing access to these platforms can range from frustrating delays to catastrophic failures:
- Operational Paralysis: If a drone fleet manager cannot log in, flight operations cease. If an IoT technician cannot access the control panel, critical alerts might be missed, or system parameters cannot be adjusted.
- Data Vulnerability & Loss: Extended periods of being locked out can create windows of vulnerability if accounts aren’t properly secured. Furthermore, inability to access and backup data could lead to data loss or corruption if not managed promptly.
- Project Delays & Missed Deadlines: In fast-paced R&D environments, every hour counts. Lost access can cause significant setbacks, impacting project timelines, client commitments, and competitive advantage.
- Financial Implications: Downtime translates directly to financial losses, whether through unutilized assets, delayed product launches, or contractual penalties.
- Security Risks: A forgotten password might tempt users to create weak, easily guessable replacements, or lead to desperate attempts that bypass proper security protocols, opening doors for malicious actors.
Proactive Security Measures
Before delving into recovery, it’s crucial to acknowledge that prevention is always superior. Implement robust password policies, enforce multi-factor authentication (MFA), and regularly educate your team on cybersecurity best practices. These steps significantly reduce the likelihood and impact of a forgotten password incident.
The Standard Recovery Protocol: Step-by-Step Guide
When you find yourself locked out of an essential Tech & Innovation platform, a systematic approach is key. Resist the urge to panic or try easily guessable passwords repeatedly, which might trigger lockout mechanisms.
Initiating the Password Reset Process
The first and most common step is to utilize the platform’s built-in password recovery mechanism.
- Navigate to the Login Page: Go directly to the official login page of the platform. Avoid clicking suspicious links from emails, even if they appear legitimate.
- Locate “Forgot Password” or “Reset Password”: This link is typically found near the username/password fields. Clicking it initiates the recovery workflow.
- Enter Your Account Identifier: You will usually be prompted to enter the email address or username associated with your account. Ensure accuracy, as a typo will prevent the process from moving forward.
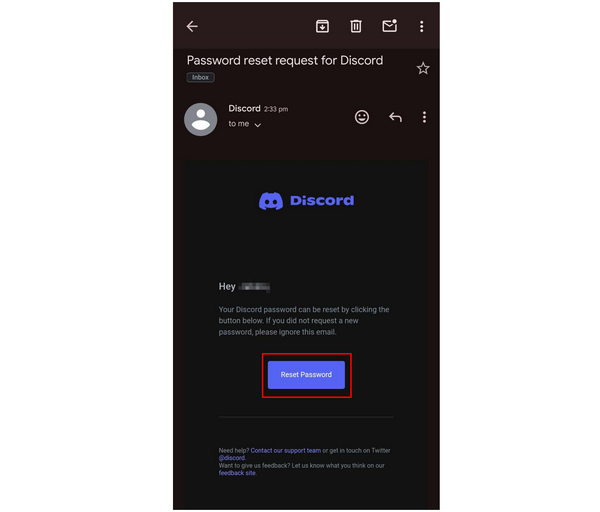
- Check Your Registered Email/Phone: The system will typically send a password reset link or a verification code to your registered email address or phone number. Check your inbox (including spam/junk folders) or SMS messages.
Verifying Your Identity
This is a critical security step designed to ensure only the legitimate account owner can regain access.
- Email/SMS Verification Code: Enter the unique code sent to your registered contact method into the platform’s verification field. This is the most common and straightforward method.
- Security Questions: Some platforms might ask you to answer pre-set security questions (e.g., “What was the name of your first pet?”, “What is your mother’s maiden name?”). Ensure you remember the exact answers you set up.
- Backup Codes: If you had previously set up two-factor authentication (2FA) with backup codes, now is the time to retrieve one. Each code is typically single-use.
- Secondary Email/Phone: Some platforms allow you to register a secondary recovery email or phone number, providing an alternative if your primary method is inaccessible.
Creating a New, Robust Password
Once your identity is verified, you’ll be prompted to create a new password. This is an opportunity to strengthen your account’s security significantly.
- Length and Complexity: Aim for at least 12-16 characters. Combine uppercase and lowercase letters, numbers, and symbols.
- Uniqueness: Never reuse passwords across different platforms, especially for critical Tech & Innovation accounts. A breach on one platform shouldn’t compromise others.
- Avoid Personal Information: Do not use easily guessable information like birthdays, names, or common words.
- Memorable but Complex: Consider using a passphrase (e.g., “ThisAutonomousDroneFliesHigherThanEver!2024”) which is long and complex but easier for you to remember.
Advanced Recovery Scenarios & Best Practices
Sometimes, the standard recovery methods aren’t enough. In the complex world of Tech & Innovation, more robust solutions and proactive strategies are essential.
When Standard Methods Fail
What if you’ve lost access to your primary recovery email, or your phone?
- Contact Platform Support: This should be your next step. Prepare to provide extensive proof of identity. This might include:
- Account Details: Past billing information, subscription dates, last known login details, IP addresses.
- Associated Data: Specific project names, unique identifiers for autonomous systems you manage, recent data upload timestamps, specific configurations.
- Government-Issued ID: In highly sensitive cases, some platforms may require a copy of a government ID to verify your identity.
- Employer Verification: If it’s a corporate account, your employer’s IT department or a designated administrator might need to verify your identity.
- Team Administrator Access: For organizational accounts, if one individual loses access, a designated team administrator or IT personnel often has the authority to reset passwords or create new user accounts. Ensure your organization has a clear protocol for this.
Implementing Two-Factor Authentication (2FA) Post-Recovery
Immediately after regaining access, the absolute priority should be to set up or re-enable 2FA. This adds a crucial layer of security, requiring a second form of verification beyond just your password.
- Authenticator Apps: Apps like Google Authenticator, Authy, or Microsoft Authenticator generate time-sensitive codes, providing strong protection even if your password is stolen.
- Hardware Security Keys: Devices like YubiKey offer the highest level of security, requiring a physical key to be present and authenticated. Ideal for highly sensitive platforms.
- SMS/Email 2FA: While less secure than authenticator apps due to SIM-swapping and email phishing risks, it’s still better than no 2FA at all.
Leveraging Password Managers
To prevent future incidents, integrate a reliable password manager into your workflow.
- Secure Storage: Password managers (e.g., LastPass, 1Password, Bitwarden) securely store all your complex, unique passwords in an encrypted vault, accessible with a single master password.
- Auto-Fill & Generation: They can auto-fill login credentials and generate strong, unique passwords for new accounts, drastically improving your security posture.
- Sync Across Devices: Access your passwords securely from all your devices, reducing the frustration of “forgetting” across different workstations.
- Team Management: Many password managers offer team functionalities, allowing secure sharing of credentials among authorized personnel, critical for collaborative Tech & Innovation projects.
Strategic Security for Tech & Innovation Environments
Beyond individual recovery, organizations operating in Tech & Innovation must adopt a holistic, strategic approach to access management and security.
Regular Security Audits and Access Reviews
Periodically review who has access to which platforms and what level of permissions they hold.
- Least Privilege Principle: Ensure users only have the minimum access necessary to perform their job functions.
- Account Hygiene: Disable accounts for employees who have left the organization promptly.
- Audit Logs: Regularly review platform audit logs for unusual login attempts or suspicious activity.
Disaster Recovery Planning for Access Loss
In a critical Tech & Innovation environment, anticipating access loss is part of comprehensive disaster recovery.
- Designated Recovery Personnel: Appoint specific individuals or teams with elevated privileges who can assist with account recovery for others.
- Offline Backup Procedures: Implement procedures for offline backups of critical data, independent of specific platform access, where feasible and secure.
- Communication Protocols: Establish clear internal communication channels for reporting and resolving access issues, minimizing downtime.
Continuous User Education
The human element remains the weakest link in cybersecurity. Regular, mandatory training for all personnel is crucial.
- Password Best Practices: Reinforce the importance of strong, unique passwords and the dangers of reusing them.
- Phishing Awareness: Train users to identify and report phishing attempts, which are often used to compromise credentials.
- 2FA Usage: Educate on the benefits and proper use of multi-factor authentication.
- Platform-Specific Security: Provide training on the unique security features and recovery processes of critical Tech & Innovation platforms used within the organization.
Forgetting a password is an inevitable part of navigating the digital world. However, in the realm of Tech & Innovation, where operations, data, and intellectual property are constantly at stake, the impact can be profound. By understanding the gravity of lost access, diligently following robust recovery protocols, and proactively implementing advanced security measures like 2FA and password managers, individuals and organizations can significantly mitigate risks. Ultimately, fostering a culture of robust digital hygiene and strategic foresight ensures that innovation can continue uninterrupted, even in the face of minor digital setbacks.

