Securing your website with an SSL certificate is no longer a mere option; it’s a fundamental necessity in today’s digital landscape. An SSL (Secure Sockets Layer) certificate encrypts the data exchanged between your website and its visitors, ensuring that sensitive information like login credentials, payment details, and personal data remains confidential and protected from prying eyes. Beyond security, SSL certificates play a crucial role in search engine optimization (SEO) and building trust with your audience. Browsers prominently display a padlock icon in the address bar for HTTPS-enabled sites, signaling to users that their connection is secure. Conversely, non-secure sites are often flagged, deterring potential visitors and negatively impacting your brand’s reputation.

This guide will walk you through the essential steps of installing an SSL certificate on your website, covering everything from choosing the right certificate to verifying its successful implementation. While the specific process can vary slightly depending on your hosting provider and the type of SSL certificate you select, the underlying principles remain consistent.
Understanding SSL Certificates and Their Types
Before diving into the installation process, it’s vital to grasp the different types of SSL certificates available and how they function. The primary purpose of any SSL certificate is to enable HTTPS (Hypertext Transfer Protocol Secure) by encrypting data. However, they differ in the level of validation they provide and the number of domains they can secure.
Domain Validated (DV) SSL Certificates
Domain Validated certificates are the most basic and widely used type. They are ideal for small businesses, personal blogs, and websites where the primary concern is encrypting data in transit. The validation process for a DV certificate is automated and involves verifying that the applicant has control over the domain name. This is typically done through an email sent to a pre-defined email address associated with the domain (e.g., admin@yourdomain.com) or by requiring the applicant to place a specific file on their web server. DV certificates provide a basic level of encryption and are quick and inexpensive to obtain.
Organization Validated (OV) SSL Certificates
Organization Validated certificates offer a higher level of trust and security. The validation process for OV certificates is more rigorous, requiring the Certificate Authority (CA) to verify the legal identity and physical address of the organization requesting the certificate. This involves checking official business registration documents and other credentials. Websites that handle sensitive customer information, such as e-commerce sites or financial institutions, often opt for OV certificates. The validation process for OV certificates can take a few days.
Extended Validation (EV) SSL Certificates
Extended Validation certificates represent the highest level of assurance and are the most stringently validated. The EV validation process is the most comprehensive, involving a thorough vetting of the organization’s legal, physical, and operational existence. Once installed, EV certificates typically cause the browser’s address bar to display the organization’s name in a distinct green color, providing a highly visible trust signal to visitors. These are generally recommended for large e-commerce businesses, financial services, and government websites that require the utmost in trust and security. The EV validation process can take several days to a week or more.
Wildcard SSL Certificates
Wildcard SSL certificates secure a primary domain along with an unlimited number of its subdomains. For example, a wildcard certificate for *.yourdomain.com would secure www.yourdomain.com, blog.yourdomain.com, shop.yourdomain.com, and so on. This is a cost-effective solution for organizations that manage multiple subdomains and want to secure them all under a single certificate.
Multi-Domain (SAN) SSL Certificates
Multi-Domain (Subject Alternative Name) or SAN certificates allow you to secure multiple distinct domain names with a single certificate. This is useful if you have several different websites or if you need to secure both www.yourdomain.com and yourdomain.com (the apex domain) along with other entirely different domains. You can add up to 100 SAN entries to a single certificate.
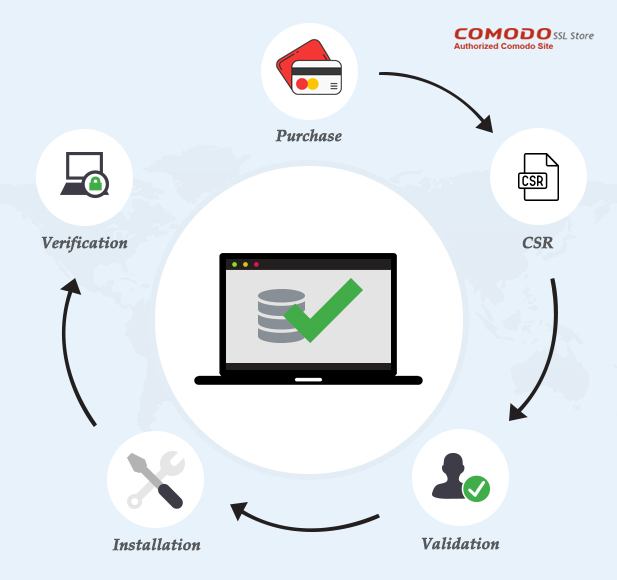
Obtaining and Installing Your SSL Certificate
The process of obtaining and installing an SSL certificate typically involves several key stages. While your hosting provider often simplifies this by offering integrated solutions, understanding the underlying steps is beneficial.
Step 1: Generate a Certificate Signing Request (CSR)
A Certificate Signing Request (CSR) is a block of encoded text that contains information about your organization and your public key. This information is used by the Certificate Authority (CA) to issue your SSL certificate. The CSR generation process is usually performed on your web server. The specific commands or interface to generate a CSR will depend on your server’s operating system and web server software (e.g., Apache, Nginx, IIS).
For Apache Servers:
You can use the openssl command-line tool. Navigate to your server’s command line and execute a command similar to this:
openssl req -new -newkey rsa:2048 -nodes -keyout yourdomain.key -out yourdomain.csr
This command will prompt you for information such as your country name, state, locality, organization name, common name (your website’s domain name, e.g., www.yourdomain.com), and an email address. The yourdomain.key file will contain your private key, which must be kept secure and never shared. The yourdomain.csr file will contain the CSR you’ll submit to the CA.
For Nginx Servers:
The process is similar to Apache, often involving openssl:
openssl req -new -newkey rsa:2048 -nodes -keyout yourdomain.key -out yourdomain.csr
For IIS (Windows Servers):
You’ll typically use the IIS Manager. Navigate to “Server Certificates,” then “Create Certificate Request.” You will be prompted to enter the required distinguished name information.
Step 2: Choose a Certificate Authority (CA) and Purchase Your Certificate
Once you have your CSR, you need to choose a reputable Certificate Authority to issue your SSL certificate. Popular CAs include Let’s Encrypt (which offers free DV certificates), Comodo (now Sectigo), DigiCert, GlobalSign, and Thawte.
When selecting a CA, consider:
- Price: Compare pricing for the type of certificate you need.
- Validation Level: Ensure the CA offers the DV, OV, or EV validation you require.
- Customer Support: Look for a CA with good support resources in case you encounter issues.
- Browser Compatibility: Most reputable CAs ensure their certificates are trusted by all major browsers.
- Warranty: Some certificates come with warranties that can protect your customers in the event of a compromise.
After selecting a CA and a certificate type, you will proceed to purchase the certificate. During the purchase process, you will be prompted to submit the CSR you generated in Step 1.
Step 3: Validate Your Domain and Organization
The validation process by the CA begins after you submit your CSR and complete the purchase. The steps involved will depend on the type of certificate:
- DV Certificates: The CA will send an email to a designated administrative address for your domain (e.g.,
admin@yourdomain.com,webmaster@yourdomain.com). You must click on the link in this email to confirm your ownership. Alternatively, some CAs might require you to upload a specific file to a designated directory on your web server. - OV and EV Certificates: These require more extensive documentation. You’ll need to provide proof of your organization’s identity, such as business registration documents, phone numbers, and physical addresses. The CA will contact you and your organization to verify this information.
Step 4: Install the SSL Certificate on Your Server
Once your certificate has been validated and issued by the CA, you will receive the certificate files. These typically include:
- Your SSL Certificate: The actual certificate file.
- Intermediate Certificates (Chain Certificates): These link your certificate back to the root certificate of the CA, ensuring trust across different browsers.
- Root Certificate: The CA’s root certificate, which is already trusted by most browsers.
The installation process varies significantly based on your hosting environment.
For Shared Hosting:
Many shared hosting providers offer one-click SSL installations or have a control panel (like cPanel or Plesk) that guides you through the process. You might find an “SSL/TLS” section where you can upload your certificate and private key.
For VPS or Dedicated Servers (Manual Installation):
If you manage your own server, you’ll need to configure your web server software.
-
Apache:
You’ll typically edit your Apache configuration file (e.g.,httpd.confor a virtual host file). You’ll need to enable the SSL module and specify the paths to your certificate file, private key file, and intermediate certificate bundle.<VirtualHost *:443> ServerName yourdomain.com SSLEngine on SSLCertificateFile /path/to/your/certificate.crt SSLCertificateKeyFile /path/to/your/private.key SSLCertificateChainFile /path/to/your/intermediate.crt DocumentRoot /var/www/html # ... other configurations </VirtualHost>After making changes, you’ll need to restart Apache:
sudo systemctl restart apache2(on Debian/Ubuntu) orsudo service httpd restart(on CentOS/RHEL). -
Nginx:
Edit your Nginx server block configuration file.server { listen 443 ssl; server_name yourdomain.com;ssl_certificate /path/to/your/certificate.crt; ssl_certificate_key /path/to/your/private.key; ssl_trusted_certificate /path/to/your/intermediate.crt; # Often combined # ... other configurations}
After making changes, reload Nginx:
sudo systemctl reload nginx. -
IIS:
Open IIS Manager, select your website, and go to “SSL Certificates.” Import the certificate (often a.pfxfile containing the certificate and private key) and then bind it to the HTTPS port (443).
Step 5: Redirect HTTP to HTTPS
Once your SSL certificate is installed, you need to ensure that all traffic to your website uses HTTPS. This is achieved by redirecting all HTTP requests to their HTTPS equivalents. This practice is crucial for security and SEO, as it consolidates your site’s ranking signals and ensures all visitors benefit from encryption.
-
Apache:
You can add the following to your.htaccessfile in the document root of your website:RewriteEngine On RewriteCond %{HTTPS} off RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301] -
Nginx:
Modify your HTTP server block to redirect to HTTPS:server { listen 80; server_name yourdomain.com; return 301 https://$host$request_uri; } -
IIS:
You can use the URL Rewrite module to configure this redirection.
Step 6: Test Your Installation
After completing the installation and setting up redirects, it’s essential to test your SSL certificate to ensure it’s working correctly.
- Browser Test: Visit your website using
https://yourdomain.com. Look for the padlock icon in the browser’s address bar. Click on it to view certificate details and confirm it’s valid and issued to your domain. - Online SSL Checkers: Utilize free online tools like SSL Labs’ SSL Server Test (ssllabs.com/ssltest/), Why No Padlock? (whynopadlock.com), or the SSL Checker from your CA. These tools will analyze your SSL configuration, identify any vulnerabilities, and provide a comprehensive report on your certificate’s health and security. They can detect issues like mixed content (HTTP resources on an HTTPS page), expired certificates, or weak cipher suites.
Maintaining Your SSL Certificate
SSL certificate installation isn’t a set-it-and-forget-it task. Regular maintenance is crucial to ensure ongoing security and functionality.
Renewal
SSL certificates have expiration dates, typically ranging from one to three years. Before your certificate expires, you’ll need to renew it with your CA. The renewal process often involves generating a new CSR, although some CAs may allow you to renew with your existing CSR if your domain and organization details haven’t changed. Failing to renew your certificate will result in browser warnings and a loss of trust from your visitors.
Updates and Configuration Checks
Periodically, it’s wise to re-evaluate your SSL configuration. This includes ensuring you’re using strong cipher suites and the latest TLS versions (TLS 1.2 and TLS 1.3 are recommended). Certificate authorities and security experts often update their recommendations based on evolving threats. Running regular checks using online tools can help you identify any outdated configurations.

Monitoring
Implement monitoring for your SSL certificate’s expiration date. Many hosting providers and domain registrars offer notifications for expiring certificates. Proactive monitoring ensures you have ample time to renew and reinstall before it becomes an issue.
By following these steps and maintaining vigilance, you can ensure your website remains secure, trustworthy, and accessible to all your visitors, fostering a positive online experience and strengthening your digital presence.
