In the rapidly evolving landscape of drone technology, where innovation drives capabilities like AI follow mode, autonomous flight, advanced mapping, and sophisticated remote sensing, the inherent cyber security risks are escalating proportionally. As these technologies become more complex and integrated into critical applications, understanding and mitigating potential threats becomes paramount. This is where threat modeling, a foundational practice in cyber security, emerges as an indispensable tool for developers, manufacturers, and operators in the drone industry. Threat modeling is not merely a reactive measure; it is a proactive, structured approach to identify, understand, and mitigate potential security threats to a system before they can be exploited.

At its core, threat modeling involves analyzing a system or application to identify potential security vulnerabilities and determine how an attacker might exploit them. For drone technology, this means scrutinizing everything from the embedded flight controllers and communication protocols to the cloud-based data processing platforms and user interfaces. The goal is to build a comprehensive understanding of the system’s security posture, anticipate attack vectors, and implement robust defenses, ensuring the integrity, availability, and confidentiality of drone operations and the sensitive data they handle.
The Imperative of Threat Modeling in Drone Technology
The unique characteristics of drones—their mobility, connectivity, computational power, and potential for both physical and digital impact—introduce a complex array of security challenges. Unlike traditional IT systems confined to a network, drones operate in dynamic environments, often transmitting sensitive data over wireless channels and interacting with various external systems. This expanded attack surface necessitates a systematic approach to security planning and implementation, which threat modeling provides.
Proactive Security for Autonomous Systems
Autonomous flight capabilities, powered by advanced AI algorithms, represent a pinnacle of drone innovation. However, this autonomy also presents significant security concerns. A compromised autonomous system could lead to loss of control, diversion of the drone for malicious purposes, or even physical harm. Threat modeling allows engineers to dissect these complex systems, identify critical control points, data flows, and decision-making logic that an attacker might target. By predicting potential exploits—such as GPS spoofing, sensor jamming, or manipulation of AI models—developers can bake security measures into the design phase, rather than attempting to patch vulnerabilities post-deployment. This proactive stance is vital for maintaining public trust and ensuring the safe operation of increasingly autonomous drone fleets.
Safeguarding Data in Remote Sensing and Mapping
Drones are invaluable tools for remote sensing and mapping, collecting vast amounts of data ranging from high-resolution imagery and topographical information to thermal signatures and environmental readings. This data often includes proprietary information, critical infrastructure details, or personally identifiable information, making it a prime target for cyber adversaries. Threat modeling helps identify where this data resides, how it is transmitted, stored, and processed, and who has access to it. It scrutinizes the entire data lifecycle, from collection on the drone’s sensors to its transmission to ground stations, cloud storage, and eventual analysis. By understanding the vulnerabilities at each stage—from unsecured Wi-Fi links on the drone to insecure APIs for data access—organizations can implement encryption, access controls, and data integrity checks that protect against unauthorized access, tampering, or exfiltration, ensuring the reliability and trustworthiness of drone-collected insights.
Core Principles of Threat Modeling for Drone Innovation
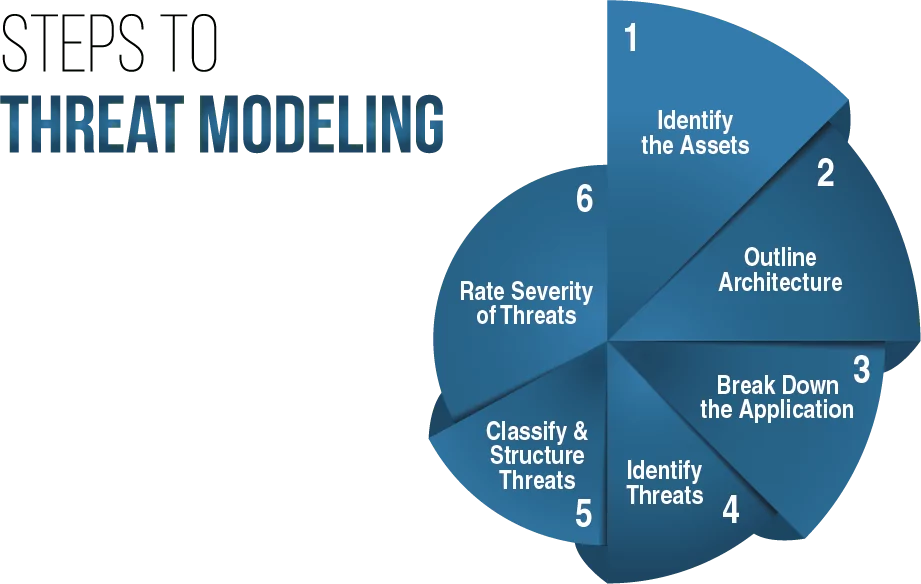
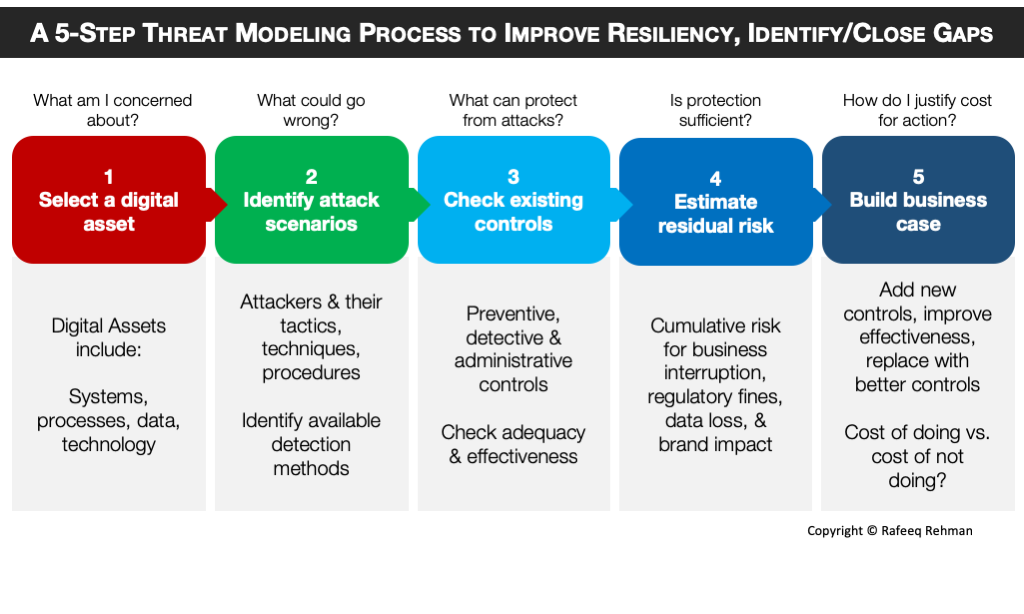
Implementing threat modeling effectively requires a structured methodology that can be adapted to the specific nuances of drone technology. While several methodologies exist (e.g., STRIDE, DREAD, PASTA, VAST), they generally share common core principles focused on understanding the system, identifying threats, and developing countermeasures.
Identifying Assets and Adversaries
The first step in threat modeling involves clearly defining the system’s assets and identifying potential adversaries. For drones, assets extend beyond the physical hardware to include the software stack, firmware, data collected (e.g., mapping data, video feeds), intellectual property embedded in algorithms (e.g., AI follow mode logic), communication links, and the reputation of the operating entity. Adversaries can range from individual hobbyists looking to exploit vulnerabilities for fun, to organized criminal groups seeking valuable data, state-sponsored actors aiming for espionage or sabotage, or even competitors attempting intellectual property theft. Defining these assets and adversaries helps in understanding what needs protection and from whom. This stage demands a deep understanding of the drone’s purpose, its operational environment, and the value of its components and data.
Analyzing Threats and Vulnerabilities
Once assets and adversaries are identified, the next phase involves analyzing potential threats and vulnerabilities. Threats represent potential attacks, while vulnerabilities are weaknesses in the system that an attacker could exploit. For drone systems, this involves considering various attack vectors:
- Physical Attacks: Tampering with drone hardware, sensors, or navigation systems.
- Network Attacks: Intercepting or jamming communication links (e.g., C2 links, data uplinks), denial-of-service attacks, man-in-the-middle attacks.
- Software/Firmware Attacks: Exploiting vulnerabilities in the operating system, flight control software, AI algorithms, or payload applications (e.g., injecting malicious code, buffer overflows).
- Data Attacks: Unauthorized access, modification, or deletion of collected data, or data in transit/at rest.
- Social Engineering: Targeting ground crew or operators to gain unauthorized access or manipulate drone operations.
- Supply Chain Attacks: Introducing malicious components or software during manufacturing or maintenance.
Techniques like STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) can be particularly useful here, mapping potential threats to specific drone components or data flows. For instance, GPS spoofing directly addresses a ‘Spoofing’ threat to the drone’s navigation system. Analyzing these helps prioritize risks based on their potential impact and likelihood.
Mitigating Risks and Verifying Defenses
The final stage of threat modeling focuses on developing and implementing mitigation strategies for identified threats and then verifying their effectiveness. For each high-priority threat, specific security controls are designed. These could include:
- Encryption: For all data in transit (e.g., between drone and ground station) and at rest (e.g., onboard storage, cloud archives).
- Authentication & Authorization: Strong mutual authentication for drone-ground station communication, role-based access control for operational personnel and data access.
- Secure Boot & Firmware Updates: Ensuring the drone’s firmware is genuine and untampered, and updates are securely delivered.
- Anomaly Detection: Monitoring flight patterns, sensor readings, and network traffic for unusual behavior indicative of an attack.
- Physical Security: Protecting drone hardware from unauthorized access or tampering.
- Redundancy & Fail-safes: Implementing backup systems and failsafe protocols for critical components and autonomous functions.
- Secure Development Practices: Incorporating security from the ground up in the development of AI algorithms, flight software, and associated applications.
Crucially, threat modeling is an iterative process. Once mitigations are implemented, they must be tested and verified to ensure they effectively address the identified threats without introducing new vulnerabilities. This ongoing verification ensures that the security posture of drone technology remains robust against evolving threats.
Applying Threat Modeling to Advanced Drone Capabilities
The real power of threat modeling lies in its adaptability to specific, cutting-edge drone innovations, allowing for targeted security enhancements where they are most needed.
Threat Modeling for AI-Powered Flight Modes
AI follow mode, object recognition, and intelligent navigation rely heavily on complex algorithms and sensor data. Threat modeling for these systems involves scrutinizing the AI model itself. Potential threats include:
- Adversarial AI Attacks: Manipulating input data (e.g., slightly altering visual cues) to cause the AI to misclassify objects or misinterpret commands, leading to incorrect flight paths or target identification.
- Model Poisoning: Introducing malicious data into the training set to corrupt the AI model’s behavior, potentially leading to bias or vulnerabilities.
- Model Theft/Reverse Engineering: Extracting or understanding the proprietary AI model to replicate or exploit its weaknesses.
- Data Integrity Attacks: Tampering with sensor inputs that feed the AI, causing it to make flawed decisions.
Mitigations would include robust input validation, secure training data pipelines, explainable AI techniques to understand decision-making, and strong intellectual property protection for AI models.
Securing Autonomous Navigation and Control
Autonomous flight systems, which enable drones to operate without continuous human intervention, are highly susceptible to navigation and control threats. These include:
- GPS Spoofing: Broadcasting false GPS signals to trick the drone into believing it is in a different location, potentially leading it off course or into restricted airspace.
- Jamming: Disrupting radio frequency communication, leading to loss of control, loss of telemetry, or failure of mission.
- Inertial Measurement Unit (IMU) Exploits: Manipulating or overwhelming the drone’s IMU to cause instability or incorrect positional awareness.
- Flight Control System Exploitation: Directly injecting commands or exploiting vulnerabilities in the flight control software to hijack the drone.
Countermeasures might involve multi-sensor fusion for navigation (combining GPS with visual odometry, lidar, and IMU data for redundancy), advanced anti-jamming and anti-spoofing technologies, cryptographic signing of flight commands, and secure, redundant communication links.
Protecting Data in Drone Mapping and Remote Sensing Workflows
The vast quantities of sensitive data generated by drone mapping and remote sensing workflows are a prime target. Threats here include:
- Data Interception: Capturing sensitive imagery or sensor data during wireless transmission from the drone to the ground station or cloud.
- Data Tampering: Modifying mapping data to introduce inaccuracies or malicious information, compromising the integrity of analysis.
- Unauthorized Access to Stored Data: Exploiting weak authentication or access controls to gain unauthorized entry to cloud storage or local servers holding drone data.
- Supply Chain Attacks on Data Processing: Introducing malware into the software used for processing and analyzing drone data.
Effective mitigations include end-to-end encryption for all data at rest and in transit, robust access control policies based on the principle of least privilege, secure APIs for data access and integration, regular security audits of cloud storage configurations, and stringent vendor security requirements for data processing software.
Integrating Threat Modeling into the Drone Development Lifecycle
Threat modeling is most effective when it is not treated as a one-off audit but rather integrated seamlessly into the entire development lifecycle of drone technology, from initial concept to ongoing operations and maintenance.
Early-Stage Design and Architecture Review
Integrating threat modeling at the design phase is crucial. By analyzing architectural diagrams and functional specifications, potential security flaws can be identified and addressed before any code is written. This “shift-left” approach significantly reduces the cost and effort of fixing vulnerabilities later. During this stage, teams can model various use cases for new features like AI-driven autonomous decisions or advanced remote sensing payloads, identifying potential abuse cases and designing security controls directly into the system’s architecture. This proactive embedding of security from the outset is far more efficient than retrofitting defenses into an already built system.
Continuous Threat Assessment
The threat landscape is constantly evolving, with new vulnerabilities discovered and attack techniques emerging regularly. Therefore, threat modeling should be an ongoing activity, not a static report. As new features are added (e.g., updated AI models, new sensor integrations), existing drone systems are modified, or new threats emerge, the threat model should be revisited and updated. Regular security assessments, penetration testing, and vulnerability scanning complement the threat modeling process, providing real-world validation of the assumed security posture and identifying new risks. This continuous assessment ensures that the security of drone technology keeps pace with its innovation and the sophistication of potential adversaries.
Incident Response Preparedness
While threat modeling aims to prevent security incidents, comprehensive preparedness also includes planning for how to respond if a breach occurs. The insights gained from threat modeling—understanding potential attack vectors, critical assets, and anticipated impacts—are invaluable for developing effective incident response plans. Knowing what an adversary might target and how they might breach a drone system allows organizations to pre-plan detection mechanisms, containment strategies, and recovery procedures. This ensures that in the event of a cyber attack on drone operations, the response is swift, coordinated, and minimizes damage, further reinforcing the overall security posture derived from robust threat modeling.
