In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), innovation is driven not just by aerodynamic design or sensor sophistication, but increasingly by the underlying software and communication infrastructure that enables complex operations. Among the foundational technologies empowering advanced drone applications is the Secure Shell (SSH) protocol. Far from being a niche IT tool, SSH is an indispensable component for secure remote access, data transfer, and system management, underpinning many of the breakthroughs in autonomous flight, AI integration, mapping, and remote sensing. Understanding SSH is crucial for anyone delving into the sophisticated technical architecture of modern drone platforms.
The Foundation of Secure Remote Access: Understanding SSH
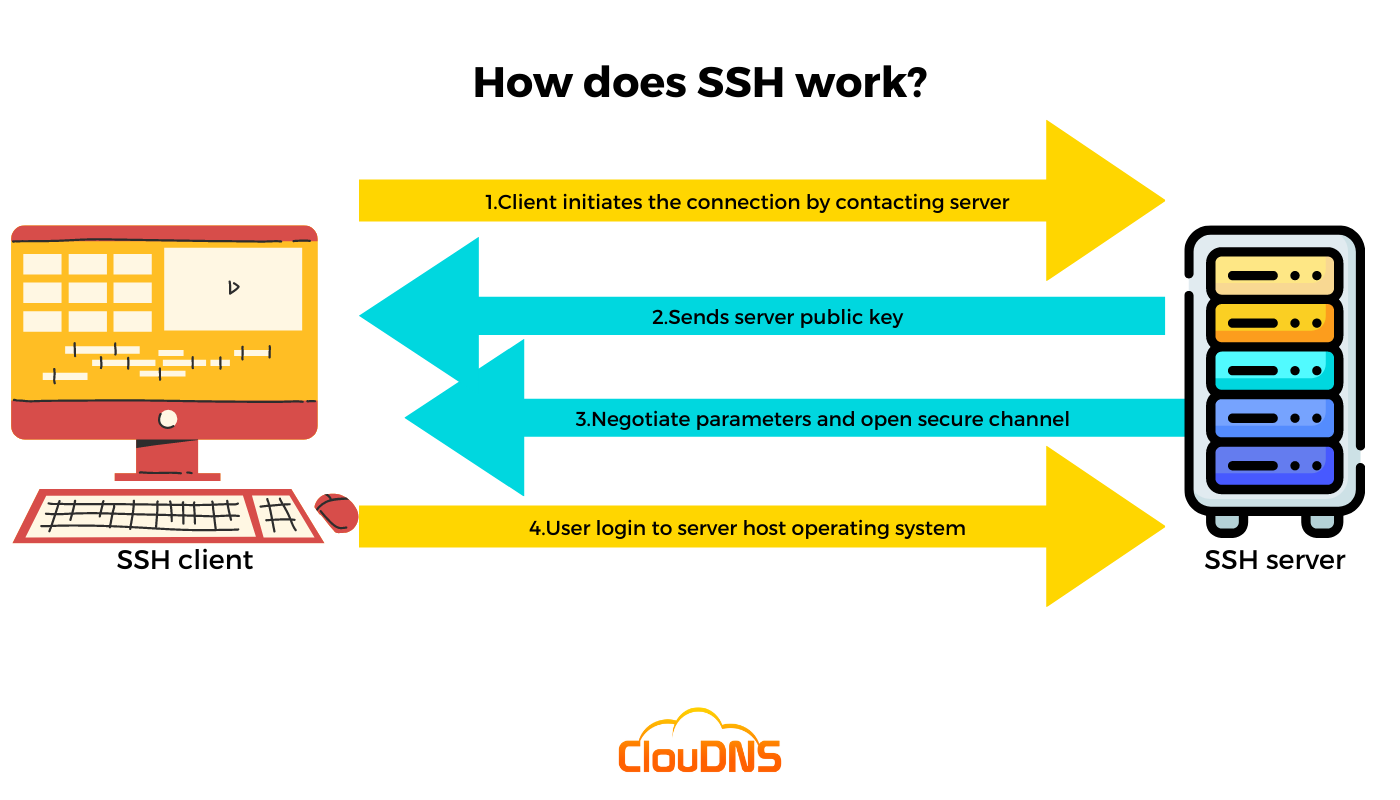
At its core, SSH is a cryptographic network protocol for operating network services securely over an unsecured network. It provides a secure channel over an untrusted network by using a client-server architecture, connecting an SSH client application with an SSH server. SSH encrypts all traffic, including usernames, passwords, commands, and data transfers, effectively preventing eavesdropping, connection hijacking, and other network-level attacks. This robust security makes it a cornerstone for managing systems remotely, a necessity for drones operating in diverse and often challenging environments.
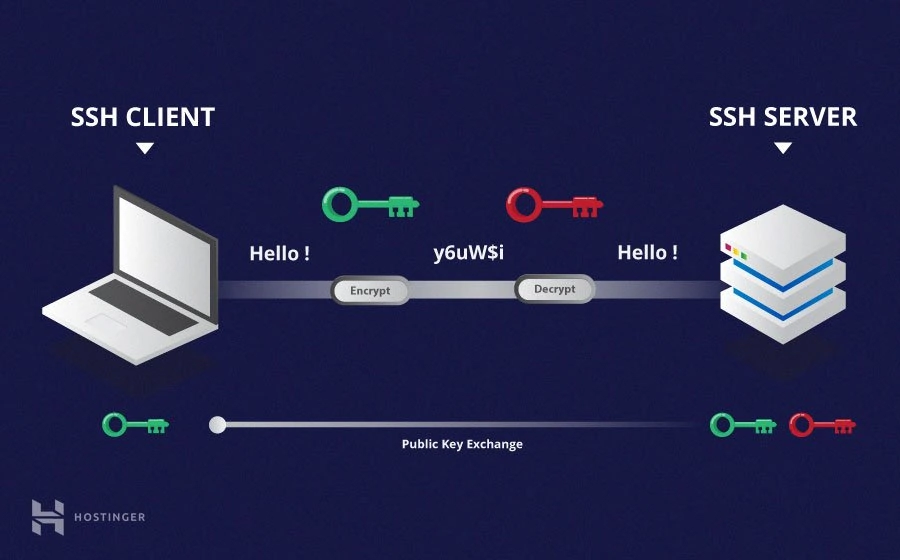
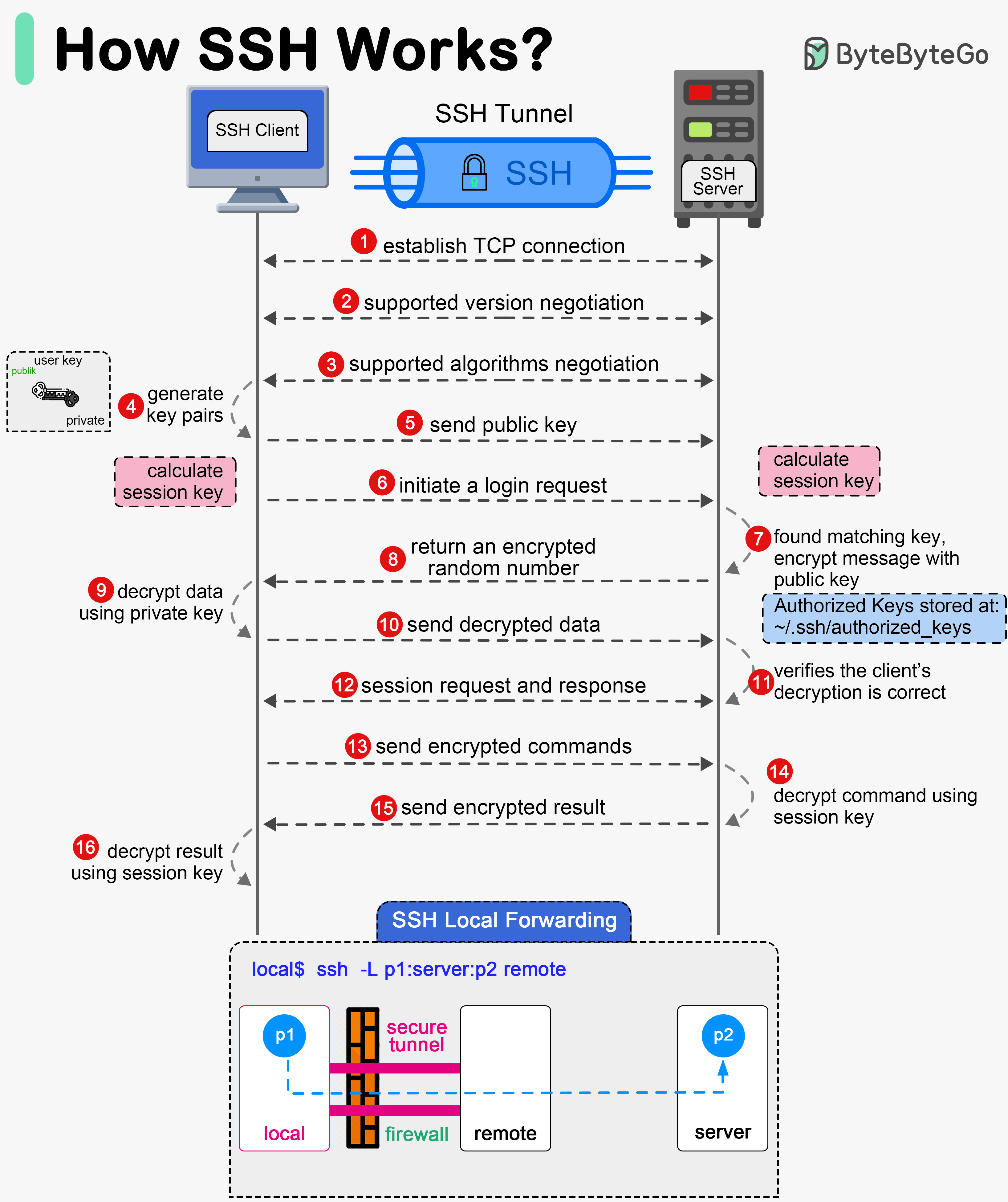
The protocol functions by establishing a secure, encrypted tunnel. When an SSH client attempts to connect to an SSH server, a handshaking process occurs. This involves exchanging cryptographic keys to establish a shared secret, which is then used to encrypt and decrypt subsequent communication. This initial key exchange often uses public-key cryptography, where the server presents its public key to the client for authentication. For user authentication, SSH commonly employs either password-based authentication (less secure for automated systems) or public-key authentication, where the client uses a private key that corresponds to a public key stored on the server. The latter is significantly more secure and suitable for automated scripts and headless systems typical in drone operations.
Beyond basic terminal access, SSH offers several capabilities critical for advanced drone applications:
- Secure Remote Command Execution: Running commands on a remote system as if you were locally present.
- Secure File Transfer (SFTP/SCP): Encrypted transfer of files between local and remote systems.
- Port Forwarding (Tunneling): Creating secure tunnels for other network services, allowing encrypted access to services that might otherwise be insecure.
These features collectively provide the backbone for secure and reliable interaction with the complex computational systems found onboard modern drones and their associated ground infrastructure.
SSH for Onboard Intelligence: Managing Drone Companion Computers
The cutting edge of drone technology often involves powerful companion computers mounted directly on the UAV. These small, high-performance computing units, such as NVIDIA Jetson modules, Raspberry Pis, or custom embedded Linux systems, are responsible for processing vast amounts of data in real-time. They enable advanced functionalities like AI follow mode, real-time object detection, simultaneous localization and mapping (SLAM), complex mission planning, and sophisticated sensor fusion. SSH is the primary conduit for interacting with these onboard intelligence hubs.
For developers and operators, SSH provides unparalleled access to these embedded systems. Imagine a drone configured for autonomous navigation and object recognition. The AI models and navigation algorithms reside on the companion computer. Through an SSH connection, a developer can securely:
- Deploy New AI Models: Upload updated neural networks or refined machine learning models to enhance the drone’s perception capabilities. This is vital for adapting to new environments or improving accuracy for specific tasks like agricultural analysis or infrastructure inspection.
- Update Flight Control Software: Push new firmware or software patches for autonomous flight algorithms without physically connecting to the drone. This can include updates to PID controllers, path planning algorithms, or safety protocols.
- Monitor System Performance: Access logs, check CPU/GPU utilization, memory consumption, and sensor data streams in real-time to diagnose issues or optimize performance during test flights or actual missions. This is crucial for ensuring the reliability of autonomous systems.
- Debug Code On-the-Fly: Connect to a running process, attach a debugger, or modify configuration files to troubleshoot complex issues, reducing downtime and accelerating development cycles.
- Configure Network Settings: Adjust Wi-Fi, cellular, or satellite communication parameters for reliable data transmission and command & control.
Without SSH, managing these complex onboard systems would necessitate physical access to the drone for every update or diagnostic check, making remote operations and rapid iteration prohibitively cumbersome. SSH liberates drone development and deployment from geographical constraints, enabling true innovation at the edge.
Secure Data Transfer and Remote Sensing Applications
Modern drones, especially those used for mapping, surveying, and remote sensing, collect an enormous volume of sensitive data. High-resolution imagery, LiDAR scans, multispectral data, and thermal readings are crucial for applications ranging from precision agriculture and environmental monitoring to construction site progress tracking and urban planning. The secure and efficient transfer of this data is paramount, and SSH-based protocols like SFTP (SSH File Transfer Protocol) and SCP (Secure Copy Protocol) play a critical role.
After a drone completes a mapping mission, gigabytes or even terabytes of data might reside on its onboard storage. Rather than physically retrieving storage cards, which can be impractical in remote locations or for large-scale operations, SSH allows for secure, encrypted transfer of this data to a ground station, a central server, or cloud storage. This ensures data integrity and confidentiality from the point of collection to its final processing destination.
Consider a drone conducting a remote sensing mission over a vast agricultural field. It collects multispectral data to assess crop health. Using SFTP, this data can be securely downloaded to a local processing unit where AI algorithms analyze plant vigor, identify disease outbreaks, or detect irrigation issues. Similarly, for applications like 3D mapping and photogrammetry, thousands of high-resolution images are captured. SCP can be used to transfer these image sets to powerful workstations for stitching, point cloud generation, and model creation.
The security provided by SSH is non-negotiable for sensitive applications, protecting intellectual property, proprietary data, and privacy concerns associated with aerial surveillance or data collection. Furthermore, SSH tunneling can be used to secure other data streams or protocols that are not inherently encrypted, providing an additional layer of protection for real-time sensor feeds or command and control channels.
Enabling Autonomous Flight and Swarm Intelligence
Autonomous flight, the holy grail of drone innovation, relies heavily on robust communication and secure system interactions. SSH contributes significantly to this domain by enabling secure management of the software and data that drive autonomous behaviors. From initial mission planning to in-flight adjustments and post-mission analysis, SSH provides the secure backbone.
For fully autonomous drones or fleets of drones operating in a swarm, SSH can facilitate:
- Secure Mission Uploads: Uploading encrypted flight plans, waypoints, and operational parameters to individual drones or an entire swarm. This ensures that critical mission data cannot be tampered with or intercepted.
- Distributed Computing and Swarm Management: In a swarm intelligence scenario, drones might coordinate tasks or share processed information. While direct inter-drone communication might use other protocols, SSH could be used for secure initial setup, configuration, or for secure communication with a central orchestrator. For example, a ground station could SSH into individual drones to deploy new coordination algorithms or query their status securely.
- Over-the-Air (OTA) Updates: As autonomous capabilities evolve, software updates are frequent. SSH allows for secure OTA updates of onboard navigation systems, obstacle avoidance algorithms, and AI inference engines, ensuring drones always operate with the latest and safest software versions.
- Edge Computing Integration: As more processing moves to the edge on the drone itself, SSH becomes essential for managing these distributed computing nodes. It allows for secure deployment of microservices, containerized applications, and real-time data processing modules directly on the drone hardware.
The ability to securely and reliably interact with these complex systems remotely is a cornerstone of developing and deploying advanced autonomous drone capabilities, pushing the boundaries of what UAVs can achieve without human intervention.
Implementing SSH for Secure Drone Operations: Best Practices
While SSH offers robust security, its effectiveness depends on proper implementation and adherence to best practices, especially in the context of high-stakes drone operations.
- Public-Key Authentication (Preferred): Always use SSH key pairs instead of passwords for authentication. Generate strong, unique key pairs for each system or user. Public keys are placed on the drone’s companion computer, and the private key is kept secure on the ground station or user’s machine. Passphrases for private keys add an extra layer of security.
- Disable Password Authentication (if possible): Once key-based authentication is set up, disable password authentication on the SSH server configuration (
sshd_config) to eliminate a common attack vector. - Change Default SSH Port: While not a security silver bullet, changing the default SSH port (22) to a non-standard port can reduce automated scanning attempts and noise in logs.
- Restrict User Access: Configure SSH to allow access only for specific, necessary user accounts. Avoid using root login directly. Use
sudofor administrative tasks after logging in as a regular user. - Firewall Rules: Implement strict firewall rules (
ufw,iptables) on the drone’s companion computer to only allow SSH connections from known IP addresses or networks. - Regular Updates: Keep SSH server and client software updated to patch known vulnerabilities.
- Monitor SSH Logs: Regularly review SSH server logs for suspicious login attempts or activities.
- Use Strong Cryptographic Algorithms: Ensure that the SSH configuration prefers strong encryption and hashing algorithms. Modern SSH clients and servers typically handle this by default.
By meticulously following these best practices, operators and developers can harness the full power of SSH to manage, secure, and innovate with their drone fleets, ensuring that the sophisticated technologies onboard are protected from unauthorized access and data breaches. As drones become more integrated into critical infrastructure and commercial operations, the importance of foundational security protocols like SSH will only grow.
