A security policy, in the realm of Tech & Innovation, particularly concerning advanced drone technologies, is a comprehensive set of rules, procedures, and guidelines designed to protect information, systems, and assets from unauthorized access, use, disclosure, disruption, modification, or destruction. Within the context of AI-driven autonomous flight, sophisticated mapping, and remote sensing applications, a robust security policy is not merely a bureaucratic overhead but a fundamental pillar ensuring operational integrity, data privacy, regulatory compliance, and ethical deployment. It serves as a strategic framework to mitigate risks inherent in complex, interconnected drone systems, which are increasingly critical infrastructure and data gathering tools.
The Imperative of Security Policy in Drone Tech & Innovation
The rapid advancements in drone technology, especially in areas like autonomous flight, AI-powered object recognition, and high-precision remote sensing, introduce unprecedented capabilities alongside significant security challenges. These innovations move drones beyond simple remote-controlled devices into intelligent, networked systems capable of processing vast amounts of sensitive data and executing complex missions with minimal human intervention. Without a meticulously crafted security policy, the potential for exploitation, data breaches, and operational failures escalates dramatically, undermining trust and hindering widespread adoption.
Safeguarding Autonomous Systems
Autonomous flight systems, relying heavily on AI and machine learning algorithms, are susceptible to various threats. A security policy addresses vulnerabilities ranging from malicious software injection that could alter flight paths or mission parameters, to GPS spoofing that misleads navigation systems. It mandates protocols for secure software development life cycles (SDLC), including rigorous testing for backdoors and vulnerabilities, cryptographic protections for command and control links, and robust authentication mechanisms for accessing drone control interfaces. The policy extends to the integrity of AI models themselves, ensuring they are not tampered with, poisoned with misleading data, or leveraged for unintended purposes, which could lead to critical failures or privacy invasions. For instance, an AI follow mode system needs policies to define who can initiate tracking, what data is collected during tracking, and how that data is stored and used, preventing misuse or surveillance without consent.
Protecting Remote Sensing and Mapping Data
Drones equipped with advanced sensors (e.g., LiDAR, hyperspectral cameras, thermal imagers) generate immense volumes of data for mapping, infrastructure inspection, environmental monitoring, and surveillance. This data can be highly sensitive, containing proprietary information, personal identifiable information (PII), or critical infrastructure details. A security policy is crucial for governing the entire data lifecycle: from collection and transmission to storage, processing, and disposal. It specifies encryption standards for data in transit and at rest, access controls based on roles and responsibilities, data retention policies, and breach notification procedures. Furthermore, it addresses the integrity of mapping data, preventing falsification or alteration that could lead to misinformed decisions or critical errors in applications like precision agriculture or urban planning. Ethical considerations regarding data collection from private property or sensitive areas are also embedded within these policies, outlining permissible data types and necessary consents.
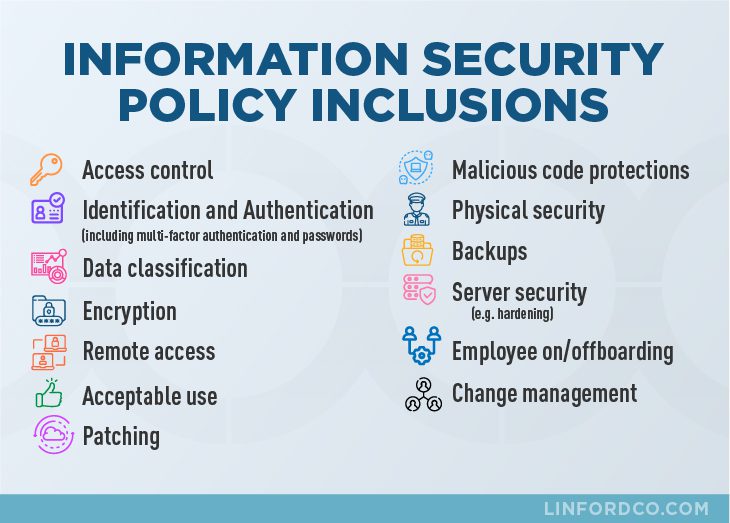
Core Components of a Drone Security Policy
A comprehensive security policy for innovative drone technologies must cover several critical areas, tailored to the unique risks presented by AI, autonomous operations, and data-intensive applications.
Data Governance and Privacy
This section outlines how all data collected, processed, and stored by drones and associated systems is managed throughout its lifecycle. It specifies:
- Data Classification: Categorizing data based on sensitivity (e.g., public, confidential, secret) to apply appropriate protection levels.
- Encryption Standards: Mandating minimum encryption protocols for data at rest (e.g., on-board storage, cloud servers) and in transit (e.g., telemetry, sensor feeds).
- Access Controls: Implementing granular role-based access control (RBAC) to ensure only authorized personnel can access specific data sets or drone controls.
- Privacy by Design: Integrating privacy considerations from the outset of system development, ensuring compliance with regulations like GDPR, CCPA, or specific national privacy laws related to aerial data collection. This includes anonymization or pseudonymization techniques where feasible.
- Data Retention and Disposal: Defining clear policies on how long different types of data are kept and secure methods for their irreversible deletion.
Operational Protocols and Access Control
This addresses the secure operation of the drone systems themselves, extending beyond data to the physical and logical security of the platforms and their control mechanisms. Key aspects include:
- Authentication and Authorization: Strong multi-factor authentication (MFA) for ground control stations, remote access portals, and drone registration systems. Policies for granting and revoking access privileges.
- Firmware and Software Security: Requirements for secure coding practices, regular vulnerability scanning, timely patching of firmware and software, and protection against unauthorized modifications.
- Physical Security: Guidelines for securing drone storage facilities, ground control stations, and critical infrastructure related to drone operations to prevent physical tampering or theft.
- Incident Response Plan: A detailed framework for identifying, containing, eradicating, and recovering from security incidents, including communication protocols and post-incident analysis.
- Supply Chain Security: Policies to vet hardware and software suppliers, ensuring components are free from known vulnerabilities or malicious inclusions, especially relevant for highly specialized sensors or AI processors.

Regulatory Compliance and Ethical AI
As drone technology advances, so too does the regulatory landscape, often playing catch-up. A robust security policy must anticipate and incorporate these evolving legal and ethical frameworks.
- Legal Compliance: Ensuring adherence to aviation regulations (e.g., FAA, EASA), data protection laws, and specific governmental restrictions on drone operations (e.g., no-fly zones, beyond visual line of sight – BVLOS operations).
- Ethical AI Guidelines: Establishing principles for the responsible use of AI in drones, addressing issues like algorithmic bias, transparency in decision-making, accountability for autonomous actions, and the prevention of discriminatory or invasive applications. This includes policies against using AI for unauthorized surveillance or targeting.
- Transparency and Accountability: Defining how stakeholders are informed about data collection practices and how accountability is assigned for system failures or policy breaches.
Implementing and Evolving Security Policies
The effectiveness of a security policy lies not just in its creation but in its dynamic implementation and continuous adaptation. The innovative nature of drone technology means threats and vulnerabilities are constantly evolving.
Risk Assessment and Threat Modeling
Before policy creation, thorough risk assessments must be conducted to identify potential threats to drone systems and data, evaluate their likelihood and impact, and prioritize mitigation strategies. Threat modeling, specific to autonomous flight systems and AI models, helps pinpoint vulnerabilities in algorithms, data flows, and communication channels. This proactive approach ensures policies are built on a solid understanding of the specific risks faced by the organization’s drone operations. Regular reassessments are vital to address new technologies, emerging threats, and changes in operational scope.
Continuous Monitoring and Adaptation
Security policies are living documents. Their efficacy depends on continuous monitoring of compliance, system performance, and the threat landscape. This involves:
- Security Audits: Regular internal and external audits to ensure adherence to policy guidelines and identify any gaps or weaknesses.
- Threat Intelligence: Staying abreast of the latest cybersecurity threats, vulnerabilities, and attack vectors relevant to drone technology and AI systems.
- Policy Review and Updates: Periodically reviewing and updating the policy to reflect technological advancements, new regulatory requirements, lessons learned from incidents, and changes in organizational operations. This ensures the policy remains relevant and effective.
- Employee Training: Ensuring all personnel involved in drone operations, data handling, and system development are thoroughly trained on the security policy and their respective roles in upholding it.
The Future Landscape: Policy Meets Progress
As drone technology integrates further with other advanced innovations like 5G, edge computing, and quantum computing, security policies will need to become even more sophisticated and adaptive.
AI and Machine Learning in Policy Enforcement
AI and machine learning are not just targets of security policies but also powerful tools for their enforcement. AI can be used for real-time anomaly detection in drone telemetry data, identifying unusual flight patterns or unauthorized access attempts. Machine learning algorithms can analyze vast security logs to pinpoint subtle indicators of compromise that human analysts might miss. Furthermore, AI can automate compliance checks, ensuring that drone operations adhere to predefined safety and security parameters without constant manual oversight.
Blockchain and Decentralized Security
Emerging technologies like blockchain hold promise for enhancing the security and integrity of drone operations and data. Blockchain can provide an immutable ledger for drone flight logs, maintenance records, and sensor data, making it tamper-proof and auditable. This decentralized approach can strengthen trust in data provenance for remote sensing applications and ensure the integrity of autonomous flight decisions by providing transparent, verifiable records of every action and data point. Integrating such innovations into future security policies will be key to building a resilient and trustworthy drone ecosystem.
In conclusion, a security policy is an indispensable framework for any entity leveraging advanced drone technologies within the Tech & Innovation landscape. It orchestrates the protection of complex autonomous systems, safeguards sensitive data from remote sensing and mapping, ensures regulatory adherence, and upholds ethical standards. As drones become more intelligent, interconnected, and integral to various sectors, the continuous development, rigorous implementation, and proactive evolution of robust security policies will be paramount to unlocking their full potential securely and responsibly.
