In an increasingly interconnected world, where everything from smart homes to autonomous drones relies on digital communication, understanding the foundational elements of network security is paramount. One such concept, critical to both the operation and vulnerability of these systems, is IP address spoofing. At its core, IP address spoofing is the act of creating Internet Protocol (IP) packets with a forged source IP address, with the intent of disguising the sender’s identity or impersonating another computing system. This deceptive practice is a cornerstone for various cyberattacks, threatening the integrity and reliability of data exchange across all forms of modern technology.
Understanding the Fundamentals of IP Addresses
Before delving into the specifics of spoofing, it’s essential to grasp what an IP address is and its role in network communication. An IP address is a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. Much like a postal address directs mail to your home, an IP address directs data packets to their intended destination on a network.
How IP Addresses Work
There are two primary versions of IP addresses in use today: IPv4 and IPv6. IPv4 addresses are 32-bit numbers, typically displayed as four octets (e.g., 192.168.1.1), while IPv6 addresses are 128-bit numbers, offering a significantly larger address space (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334). Each device, whether it’s a server, a laptop, a smartphone, or an IoT sensor in a drone, has at least one IP address that identifies it on the network.
When you send data over the internet, your device breaks the data into smaller packets. Each packet contains not only a portion of the data but also a header with crucial information, including the source IP address (your device’s IP) and the destination IP address (the recipient’s IP). Routers along the network pathway read these IP addresses to determine the optimal route for the packets to reach their final destination. This entire process relies on the assumption that the source IP address specified in the packet header is genuine.
The Role of IP in Network Communication
IP addresses enable global connectivity. They facilitate the routing of information across vast networks, allowing devices worldwide to communicate seamlessly. In the context of innovative technologies like AI-driven autonomous systems, remote sensing platforms, and complex IoT ecosystems, the accuracy and authenticity of IP addresses are fundamental. They ensure that commands reach the correct drone, that sensor data originates from a verified source, and that responses are sent back to the legitimate requesting system. Any compromise of this underlying trust mechanism can have far-reaching consequences, affecting everything from operational security to data integrity in sophisticated technological deployments.
The Mechanics of IP Spoofing
IP spoofing exploits the fundamental trust model built into the Internet Protocol itself. Because the original IP standard did not inherently include mechanisms to verify the authenticity of a packet’s source address, an attacker can manipulate this information.
Source IP Address Manipulation
The core of IP spoofing involves an attacker crafting an IP packet where they replace their actual source IP address with a different, forged address. This forged address could belong to another legitimate device on the network, a non-existent address, or an address designed to mislead. When the target machine receives this spoofed packet, it interprets it as coming from the forged source address, not the actual sender.
This manipulation is typically performed at the network layer, often using raw socket programming tools that allow direct control over packet headers. Attackers can create custom packets with any source IP address they choose, bypassing the normal network stack that would automatically insert the correct source IP. The response to such a spoofed packet, however, would be sent back to the forged IP address, not the attacker’s actual location. This characteristic is often leveraged in specific attack types.
Types of Spoofing Attacks
IP spoofing is not an end in itself but rather a means to facilitate other, more complex cyberattacks. Several common attack types utilize IP spoofing:
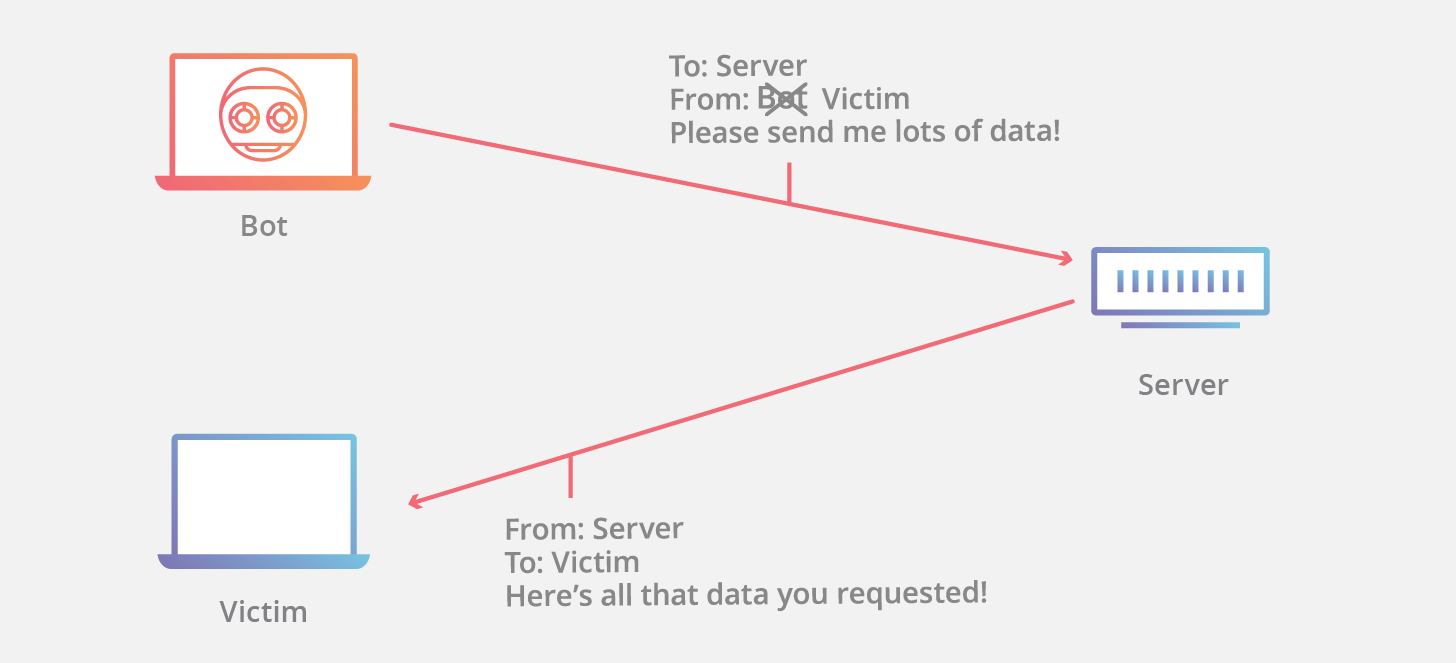
- Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks: In these attacks, a target server is flooded with an overwhelming volume of traffic, rendering it unavailable to legitimate users. Attackers often spoof source IP addresses in DoS/DDoS attacks to hide their identities, making it difficult to trace the origin of the attack. Furthermore, in reflection attacks, spoofed requests are sent to multiple third-party servers, which then reply to the spoofed address (the victim), magnifying the attack’s impact while concealing the attacker.
- Man-in-the-Middle (MITM) Attacks: While traditional MITM attacks often involve ARP spoofing to intercept local network traffic, IP spoofing can be used in broader contexts to masquerade as a legitimate endpoint, diverting or monitoring communications. This is particularly relevant in situations where secure session establishment is weak or where an attacker can inject spoofed packets into a data stream.
- Evading Network Access Controls: Some older network systems or firewalls rely solely on IP addresses for access control, granting or denying access based on the source IP. By spoofing a trusted IP address, an attacker can bypass these controls and gain unauthorized access to resources.
- Trust Exploitation: In environments where systems implicitly trust communication from certain IP addresses (e.g., within internal networks or specific subnets), spoofing a trusted IP can allow an attacker to send malicious commands or data that appear to originate from a legitimate, internal source. This can be devastating for autonomous systems or critical infrastructure.
Why Attackers Use IP Spoofing
The motivations behind employing IP spoofing are diverse, but they generally revolve around anonymity, evasion, and the desire to amplify or facilitate other forms of exploitation.
Evading Detection and Obscuring Identity
One of the primary reasons attackers spoof IP addresses is to remain anonymous and avoid being traced. By presenting a false source IP, the attacker obfuscates their true identity and location, making it significantly harder for network defenders and law enforcement to pinpoint the origin of a malicious act. This is crucial for sustained attack campaigns or for actors operating from jurisdictions where they might face legal repercussions. In scenarios involving sophisticated remote sensing operations or critical infrastructure, the ability to trace the origin of a command or data injection is vital. Spoofing directly undermines this traceability, posing a significant challenge to security incident response.
Facilitating Other Cyber Attacks (DoS/DDoS, Man-in-the-Middle)
As previously mentioned, IP spoofing often serves as an enabler for more impactful attacks. For instance, in DoS/DDoS attacks, spoofing ensures that the flood of traffic appears to originate from countless different, often legitimate, sources, making it difficult to block effectively and obscuring the actual attack infrastructure. In reflection and amplification attacks, spoofing the victim’s IP address allows the attacker to leverage legitimate services (like DNS servers or NTP servers) to bombard the victim with amplified response traffic. The ability to inject packets that appear to come from a legitimate system can also be a crucial step in advanced Man-in-the-Middle attacks or session hijacking, where an attacker seeks to insert themselves into an ongoing communication session.
Detecting and Mitigating IP Spoofing
Despite the inherent challenges, various strategies and technologies have evolved to detect and mitigate IP spoofing, bolstering the security posture of modern networks and innovative technological deployments.
Network Ingress/Egress Filtering
One of the most effective and widely adopted mitigation techniques is network filtering, particularly ingress and egress filtering.
- Ingress Filtering: Implemented at the network’s perimeter (e.g., by an Internet Service Provider or at an organizational gateway), ingress filtering examines incoming packets to ensure their source IP address belongs to a valid range for that network segment or is not a private IP address if originating from the public internet. If a packet claims to originate from an internal IP address but is entering the network from an external interface, it is dropped. This prevents external attackers from spoofing internal IP addresses.
- Egress Filtering: Applied to outgoing traffic, egress filtering ensures that packets leaving an organization’s network have a legitimate source IP address that belongs to that organization’s assigned IP range. This prevents internal compromised systems or malicious insiders from launching spoofed attacks against external targets.
The “BCP 38” (Best Current Practice 38) document from the Internet Engineering Task Force (IETF) provides guidelines for implementing ingress filtering, highlighting its importance in preventing source address spoofing.
Packet Inspection and Traffic Analysis
Advanced network monitoring tools and intrusion detection/prevention systems (IDS/IPS) can perform deep packet inspection and traffic analysis to identify anomalies indicative of spoofing. By analyzing packet headers, communication patterns, and routing information, these systems can flag packets with suspicious or impossible source IP addresses. For example, if a packet arrives from a specific physical port that is known to only host devices from a particular subnet, and the packet’s source IP address claims to be from a different, external subnet, it can be identified as potentially spoofed. Behavioral analytics, which baseline normal network traffic patterns, can also detect deviations caused by spoofed traffic floods or attempts to establish unauthorized connections.
Authentication and Encryption Protocols
While IP spoofing manipulates the source address at the network layer, higher-layer security protocols can provide protection against the consequences of spoofing. Protocols like IPsec (IP Security) implement cryptographic authentication and encryption at the IP layer, verifying the authenticity of the sender and ensuring the integrity of the data. Similarly, Transport Layer Security (TLS) and Secure Shell (SSH) protect data integrity and authenticate endpoints at the transport and application layers, respectively. Even if an attacker manages to spoof an IP address, they cannot forge the cryptographic keys or certificates required to establish a secure, authenticated connection, making their spoofed packets useless for meaningful communication beyond basic flooding. For innovative technologies relying on secure data exchange, such as remote drone command and control or confidential mapping data transmission, these protocols are indispensable.
The Broader Implications for Tech & Innovation
In the landscape of cutting-edge technology, where innovation drives the development of increasingly complex and interconnected systems, the threats posed by IP address spoofing carry significant weight. Its ability to undermine trust and integrity has profound implications for various fields.
Impact on Trust in Autonomous Systems and Data Integrity
Autonomous systems, whether self-driving vehicles, industrial robots, or advanced drones, rely heavily on reliable, authentic data for decision-making. Imagine an autonomous drone performing critical infrastructure inspection or delivering vital supplies. If its communication channels are vulnerable to IP spoofing, an attacker could potentially inject spoofed command packets, making the drone believe instructions are coming from a legitimate ground control station. This could lead to mission failure, deviation from flight paths, data corruption, or even physical damage.
The integrity of data, from remote sensing measurements to AI model updates, is paramount. Spoofing compromises the assurance of data origin. If sensor data appears to come from a valid remote sensing platform but has been manipulated by a spoofed source, the subsequent analysis or AI-driven decisions could be catastrophically flawed. Ensuring data integrity requires robust authentication mechanisms that go beyond mere IP address verification, integrating cryptographic signatures and secure protocols to confirm the true origin of every piece of information.

Evolving Security Paradigms for IoT and Connected Devices
The proliferation of IoT devices, from smart city sensors to networked drone components, presents an expanding attack surface. Many IoT devices have limited processing power and memory, making it challenging to implement complex security protocols. This can make them particularly susceptible to IP spoofing attacks, especially in DoS/DDoS amplification scenarios where they can be unwitting participants.
As “Tech & Innovation” continues to push boundaries with vast networks of interconnected devices for mapping, remote sensing, and autonomous operations, the security paradigms must evolve. This involves:
- Zero-Trust Architectures: Moving away from implicit trust based on network location or IP address, and instead requiring rigorous verification for every access attempt, regardless of whether it originates inside or outside the network.
- Hardware-Based Security: Integrating secure elements and trusted platform modules (TPMs) into devices to securely store cryptographic keys and perform hardware-backed authentication.
- Micro-segmentation: Dividing networks into small, isolated segments to limit the lateral movement of attackers, even if they manage to compromise one device through spoofing or other means.
- Blockchain for Data Provenance: Exploring decentralized ledger technologies to provide an immutable record of data origin and integrity, potentially offering a robust solution for verifying sensor data in remote sensing and mapping applications.
IP address spoofing remains a fundamental threat, but a layered and proactive approach to security, leveraging authentication, encryption, and advanced network defenses, is crucial for fostering a trustworthy and resilient environment for the next generation of technological innovation.
