In the intricate landscape of modern technology and innovation, where data integrity, security, and efficiency are paramount, hash algorithms stand as silent, yet indispensable, pillars. Far from being a niche concept, hashing underpins a vast array of digital operations, from safeguarding personal information to ensuring the reliability of autonomous systems and the veracity of remote sensing data. To truly grasp the future trajectories of AI, autonomous flight, sophisticated mapping, and advanced remote sensing, one must first understand the fundamental mechanics and profound implications of hash algorithms.
The Core Mechanics of Hashing
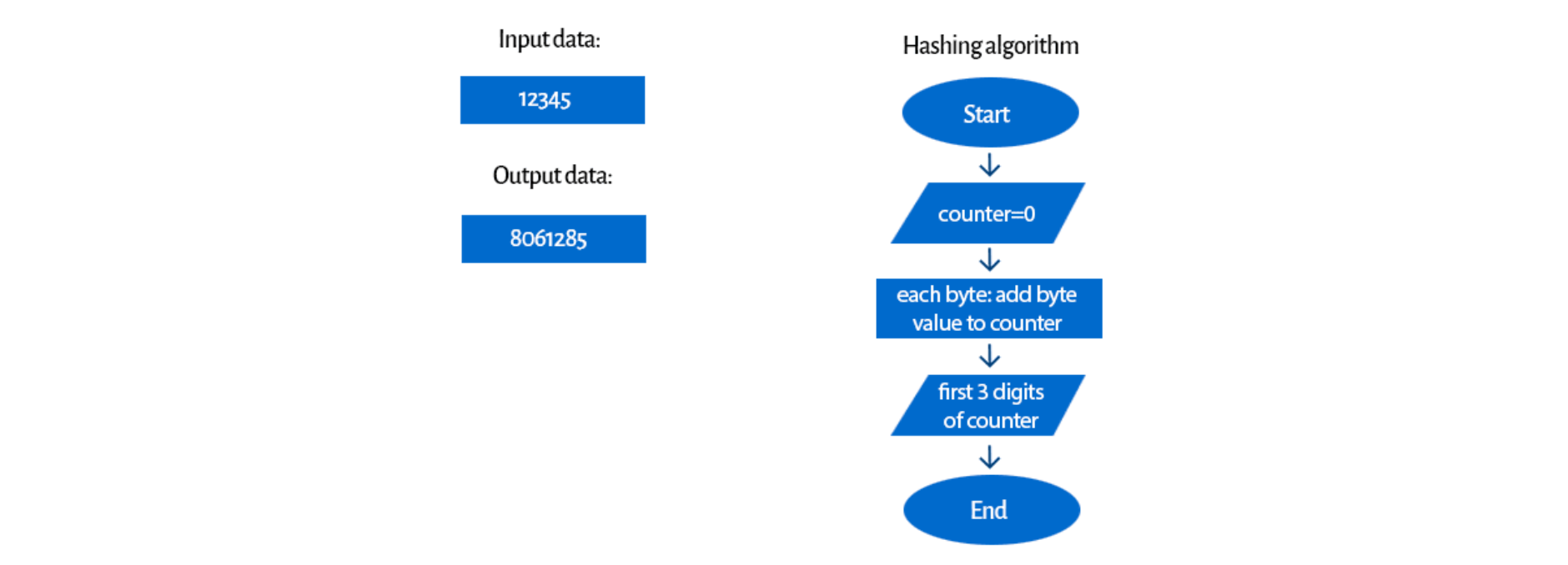
At its essence, a hash algorithm is a mathematical function that takes an input (or ‘message’) of arbitrary length and transforms it into a fixed-size string of characters, typically a sequence of numbers and letters, known as a ‘hash value’ or ‘digest.’ Think of it as a unique digital fingerprint for any given piece of data. Regardless of whether the input is a single character, an entire video file, or a complex dataset from an autonomous drone, the output hash will always be of a predetermined length.
The process is deterministic, meaning that the same input will always produce the exact same hash output. This deterministic property is crucial for verification purposes. If even a single bit in the input data is altered, the resulting hash value will change dramatically, a characteristic known as the “avalanche effect.” This sensitivity makes hash algorithms exceptionally powerful tools for detecting tampering or corruption.
Several key characteristics define robust hash algorithms:
- Determinism: Identical input always yields identical output.
- Fixed-Size Output: Regardless of input size, the hash value has a consistent length.
- One-Way Function: It is computationally infeasible to reverse the process; that is, to derive the original input data from its hash value alone. This ‘one-way’ nature is vital for security.
- Collision Resistance: It should be exceedingly difficult to find two different inputs that produce the same hash output (a ‘collision’). While theoretically possible due to the infinite number of possible inputs mapping to a finite number of outputs, strong hash functions make finding collisions practically impossible.
- Fast Computation: Generating a hash should be computationally efficient, allowing for rapid processing of large amounts of data.
These properties make hash algorithms fundamental building blocks for many sophisticated tech innovations.
Hash Algorithms as Cornerstones of Tech & Innovation
The utility of hash algorithms extends deeply into critical areas like AI follow mode, autonomous flight, advanced mapping, and remote sensing – all core components of the Tech & Innovation category. Their primary contributions revolve around data integrity, security, and efficient data management.
Data Integrity and Verification
In a world increasingly reliant on sensor data and automated decisions, ensuring the integrity of information is non-negotiable. Consider a drone conducting a remote sensing mission, collecting terabytes of environmental data. Before this data is used for critical analysis—such as identifying crop health, monitoring infrastructure, or detecting environmental changes—its integrity must be verified. A hash of the collected data can be generated at the point of capture. Upon transfer to a processing station, a new hash can be computed and compared with the original. Any discrepancy indicates potential corruption during transmission or storage, alerting operators to potential issues before erroneous decisions are made. This mechanism is vital for maintaining the trustworthiness of data streams powering mapping applications and complex environmental models.
For autonomous systems, the integrity of navigation data, sensor readings (e.g., lidar, radar, vision systems), and command signals is paramount. An AI follow mode drone needs to verify that the target’s GPS coordinates or visual markers haven’t been corrupted. Autonomous flight systems rely on verified altitude, velocity, and positional data to execute flight plans safely. Hash algorithms provide a quick and reliable method to ensure that the data being acted upon is exactly what was intended, free from accidental alteration or malicious interference.
Security and Authentication
Beyond data integrity, hash algorithms are pivotal for security. Their one-way nature makes them ideal for storing passwords securely. Instead of storing actual passwords, systems store their hash values. When a user attempts to log in, the entered password is hashed, and this new hash is compared against the stored hash. If they match, authentication is granted. This prevents attackers who gain access to a database from directly obtaining user passwords.
In the realm of autonomous systems, this extends to secure firmware updates, critical for maintaining the operational integrity and security of drones. Before a drone installs new firmware, it can calculate the hash of the downloaded file and compare it against a known, trusted hash provided by the manufacturer. If the hashes don’t match, it signifies a tampered or corrupted update, preventing the installation of potentially malicious software. This is crucial for safeguarding against supply chain attacks and ensuring that autonomous vehicles operate with verified, legitimate software. Similarly, secure communication between a ground control station and an autonomous drone often involves hashing to authenticate messages and ensure their confidentiality.
Efficiency in Data Management
Hashing also plays a significant role in improving data management efficiency. In large-scale mapping projects, where vast areas are scanned and billions of data points are collected, hash tables can be used for rapid data retrieval and indexing. By hashing keys associated with data records, systems can quickly locate specific information without exhaustively searching through entire datasets. This accelerates everything from processing geographical information systems (GIS) data to indexing objects detected during remote sensing missions.
Furthermore, hashing is used in data deduplication. In scenarios where multiple drones might capture slightly overlapping imagery or redundant sensor data, hashing can identify identical blocks of data. Storing only one copy of each unique block, along with references to it, dramatically reduces storage requirements and improves data transfer efficiency—a significant advantage for resource-intensive applications like 3D mapping and large-area surveillance.
Hash Algorithms in Action: Advanced Applications
The abstract concept of hashing manifests in tangible, impactful ways across various advanced technological domains.
Ensuring Authenticity of Firmware and Software Updates
For autonomous drones and advanced robotics, software and firmware updates are common and critical. A compromised update could lead to loss of control, security breaches, or complete system failure. Manufacturers sign their firmware updates digitally using cryptographic techniques that rely heavily on hash functions. The update file is hashed, and this hash is then encrypted with the manufacturer’s private key. The drone uses the manufacturer’s public key to decrypt the hash and then independently hashes the downloaded file. Only if both hashes match and the decryption is successful will the update proceed, guaranteeing that the software is authentic and untampered. This mechanism is a bedrock of trust for ensuring the safety and reliability of autonomous flight.
Verifying Telemetry and Sensor Data Integrity
Every piece of telemetry—from battery voltage to GPS coordinates, IMU data to camera feeds—is vital for an autonomous system. Corrupted data can lead to erroneous decisions, such as incorrect path planning in AI follow mode or unsafe maneuvers during autonomous flight. By periodically hashing telemetry streams or individual sensor packets and comparing them against expected values or previously transmitted hashes, systems can detect data corruption in real-time. This can trigger error correction protocols or fail-safes, preventing potentially catastrophic outcomes. For remote sensing, ensuring the integrity of spectral data or thermal imagery prevents false positives or negatives in crucial analyses.
Securing Communication Channels for Autonomous Flight
Communication between ground control stations, command centers, and autonomous drones often traverses potentially insecure wireless channels. Hash algorithms, often combined with symmetric or asymmetric encryption, form the backbone of secure communication protocols. They are used to create Message Authentication Codes (MACs) or digital signatures, ensuring that commands and data exchanged are both authentic (from a trusted source) and have not been tampered with in transit. This prevents unauthorized actors from injecting malicious commands or altering critical flight parameters, a fundamental requirement for the secure operation of any autonomous vehicle.
Data Deduplication and Indexing in Mapping and Remote Sensing
When mapping vast terrains or conducting long-duration remote sensing missions, the sheer volume of data generated can be overwhelming. Hash functions are employed to identify duplicate data blocks, allowing storage systems to save only unique instances. This is particularly valuable for incremental backups or for managing evolving datasets where only changes need to be stored. In large GIS databases, hashes can accelerate spatial queries and indexing of geographical features, enabling faster processing of complex mapping algorithms and real-time visualization of remote sensing data.
Blockchain and Distributed Ledger Technologies
Though a broader topic, blockchain technology relies almost entirely on cryptographic hashing. Each ‘block’ in a blockchain contains a hash of the previous block, creating an immutable chain. If any data in a previous block is altered, its hash would change, invalidating all subsequent blocks and immediately revealing the tampering. This makes blockchain incredibly secure for recording transactions and creating an auditable, decentralized ledger. While not directly embedded in every drone, distributed ledger technologies are finding applications in drone logistics, supply chain management for parts, and ensuring the provenance of data collected by drones in sensitive remote sensing operations, providing an unalterable record of data origin and processing steps.

The Evolution and Challenges of Hashing
The landscape of hash algorithms is not static. Early algorithms like MD5 and SHA-1, while historically significant, have been found to have vulnerabilities where collisions can be generated more easily than intended. This has led to their deprecation in favor of more robust algorithms like the SHA-2 family (e.g., SHA-256, SHA-512) and the even newer SHA-3 standard. The development of these algorithms is a continuous race against increasing computational power and sophisticated attack techniques.
The primary challenge lies in maintaining collision resistance. As computing power grows, the theoretical possibility of finding collisions becomes a more practical concern. Furthermore, the advent of quantum computing poses a significant long-term threat to current cryptographic standards, including some hash functions, leading to research into quantum-resistant cryptographic algorithms. For the foreseeable future, however, well-designed and implemented hash algorithms remain an indispensable tool for ensuring data integrity, security, and efficiency across the spectrum of cutting-edge tech and innovation, from the smallest micro-drone’s firmware to the vast datasets of global remote sensing initiatives.
In essence, understanding hash algorithms is not merely an academic exercise; it is a prerequisite for anyone navigating or contributing to the future of secure, reliable, and intelligent autonomous systems and data-driven technologies. They are the silent guardians, ensuring that the innovations of tomorrow stand on a foundation of verifiable truth.
