In the rapidly evolving landscape of technology, particularly within the realms of drones, flight technology, and the burgeoning fields of aerial imaging and remote sensing, understanding fundamental internet protocols is paramount. While the direct application of HTTP (Hypertext Transfer Protocol) and HTTPS (Hypertext Transfer Protocol Secure) to a drone’s flight path or its camera sensor might seem tangential, their role in the broader ecosystem of data transmission, control, and user interaction is undeniable. From receiving firmware updates for a sophisticated UAV to securely transmitting sensitive aerial mapping data, the distinction between these two protocols directly impacts the integrity and confidentiality of information exchange. This article delves into the core differences between HTTP and HTTPS, highlighting why understanding this security layer is crucial for anyone operating within or interacting with advanced technological systems.
The Foundation: Understanding HTTP
At its heart, HTTP is the foundational protocol of data communication on the World Wide Web. Developed in the early days of the internet, it defines how messages are formatted and transmitted, and what actions web servers and browsers should take in response to various commands. Think of it as the language that computers use to talk to each other when requesting and sending web pages, images, or any other resource from a web server.
How HTTP Works: The Request-Response Cycle
The fundamental interaction model of HTTP is a stateless request-response cycle. A client, typically a web browser (or in our context, a control application, a ground station software, or even a drone’s onboard management system communicating with a server), sends an HTTP request to a server. This request contains information such as the desired resource (e.g., a specific file or page), the method of the request (e.g., GET to retrieve data, POST to send data), and headers that provide additional context.
The server then processes this request and sends back an HTTP response. This response includes a status code (e.g., 200 OK for success, 404 Not Found if the resource doesn’t exist), headers that describe the response, and the actual body of the response, which could be the HTML content of a web page, an image file, or any other data.
Statelessness and its Implications
A key characteristic of HTTP is its stateless nature. This means that each request from a client to a server is treated as an independent transaction. The server does not retain any information about previous requests from the same client. While this simplifies server design and allows for efficient handling of many simultaneous connections, it also means that maintaining user sessions or tracking sequences of actions requires additional mechanisms, such as cookies. For applications managing drone fleets or real-time telemetry, this statelessness necessitates careful design to ensure continuity and context are preserved.
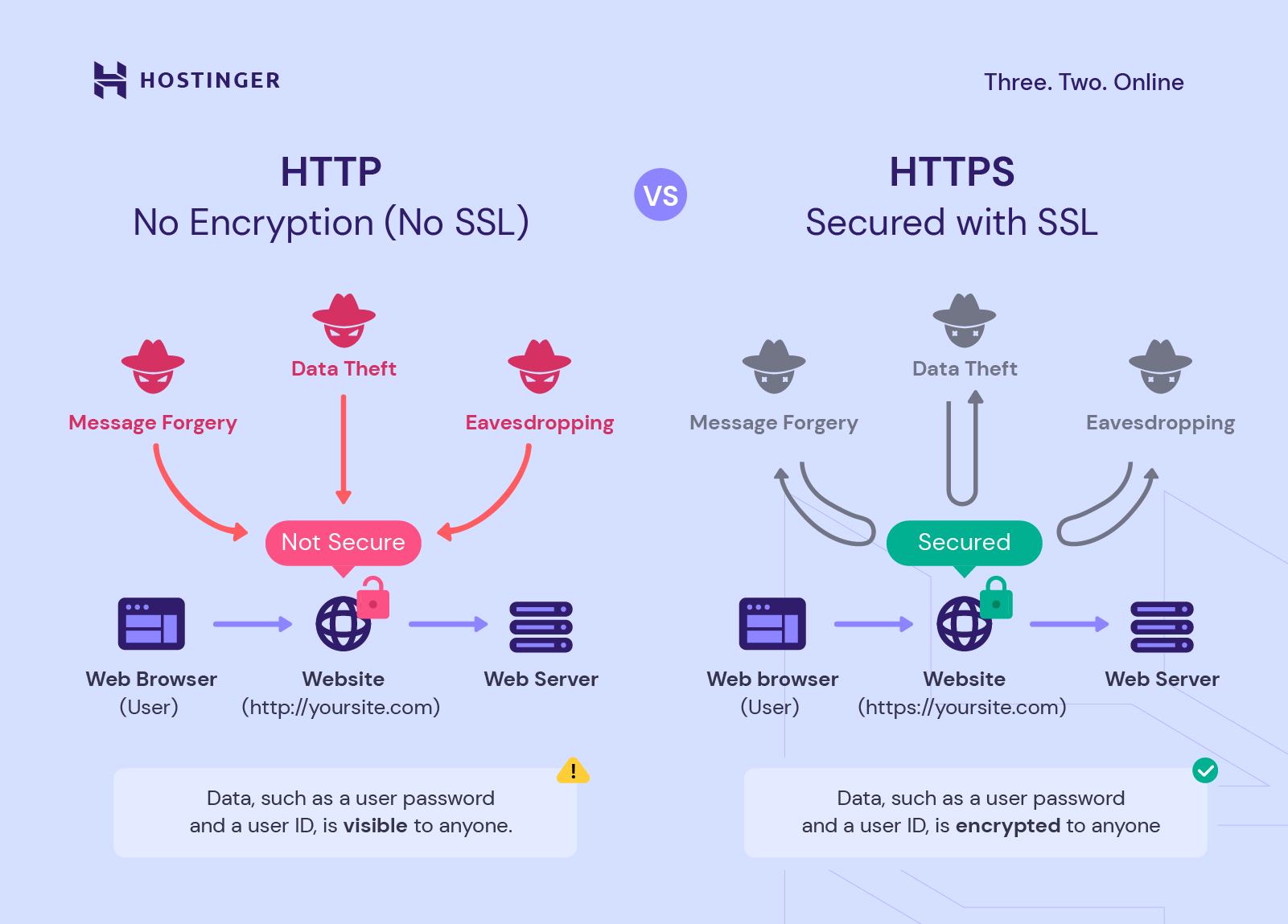
Vulnerabilities of HTTP
The primary drawback of HTTP is its inherent lack of security. All data transmitted over HTTP is sent in plain text. This means that any information exchanged between a client and server – including login credentials, sensitive flight plan data, or proprietary imaging information – can be intercepted and read by a third party with the right tools. This vulnerability is often referred to as a “man-in-the-middle” attack, where an attacker can eavesdrop on the communication or even alter the data being transmitted without either party being aware. In scenarios involving remote drone operation or sensitive data collection, this is a critical concern.
The Evolution to Security: Understanding HTTPS
Recognizing the significant security limitations of HTTP, HTTPS was developed. HTTPS is not a separate protocol in itself, but rather an extension of HTTP that adds a crucial layer of security. It achieves this by utilizing an encryption protocol, most commonly Transport Layer Security (TLS), formerly known as Secure Sockets Layer (SSL), to encrypt the communication between the client and the server.
The Role of TLS/SSL Encryption
When a client connects to a server using HTTPS, a TLS/SSL handshake takes place before any actual data is exchanged. This handshake is a complex process where the client and server negotiate the encryption algorithms and keys that will be used for the session. The server presents its digital certificate, which is issued by a trusted Certificate Authority (CA), to prove its identity to the client. Once the handshake is successfully completed, all subsequent data exchanged between the client and server is encrypted.
Benefits of Encryption
The encryption provided by TLS/SSL ensures two primary security benefits:
-
Confidentiality: The transmitted data is scrambled, making it unreadable to anyone who might intercept it. This is vital for protecting sensitive information, such as control commands for a drone, user authentication details for a flight management platform, or the raw data collected by aerial sensors.
-
Integrity: TLS/SSL also provides mechanisms to ensure that the data has not been tampered with during transmission. Any alteration to the data by an attacker would be detected, and the connection would likely be terminated or flagged. This guarantees that the commands sent to a drone or the data received from it are exactly as intended.
Authentication and Trust
Beyond encryption, HTTPS also provides authentication. The TLS/SSL certificate used by the server verifies its identity. When your browser (or drone control software) connects to an HTTPS-enabled server, it checks the validity of this certificate. If the certificate is valid and issued by a trusted CA, you can be reasonably assured that you are communicating with the legitimate server and not an imposter. This trust is fundamental when dealing with critical infrastructure like drone control systems, where a compromised communication channel could have severe consequences.
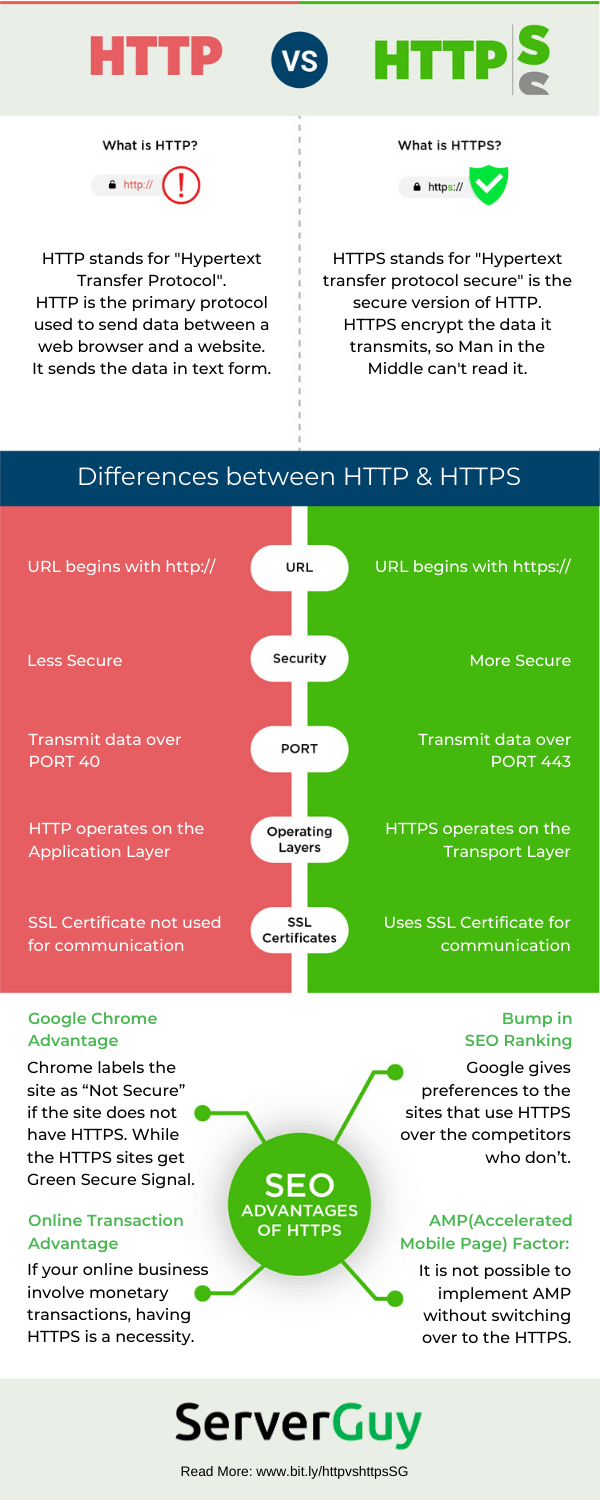
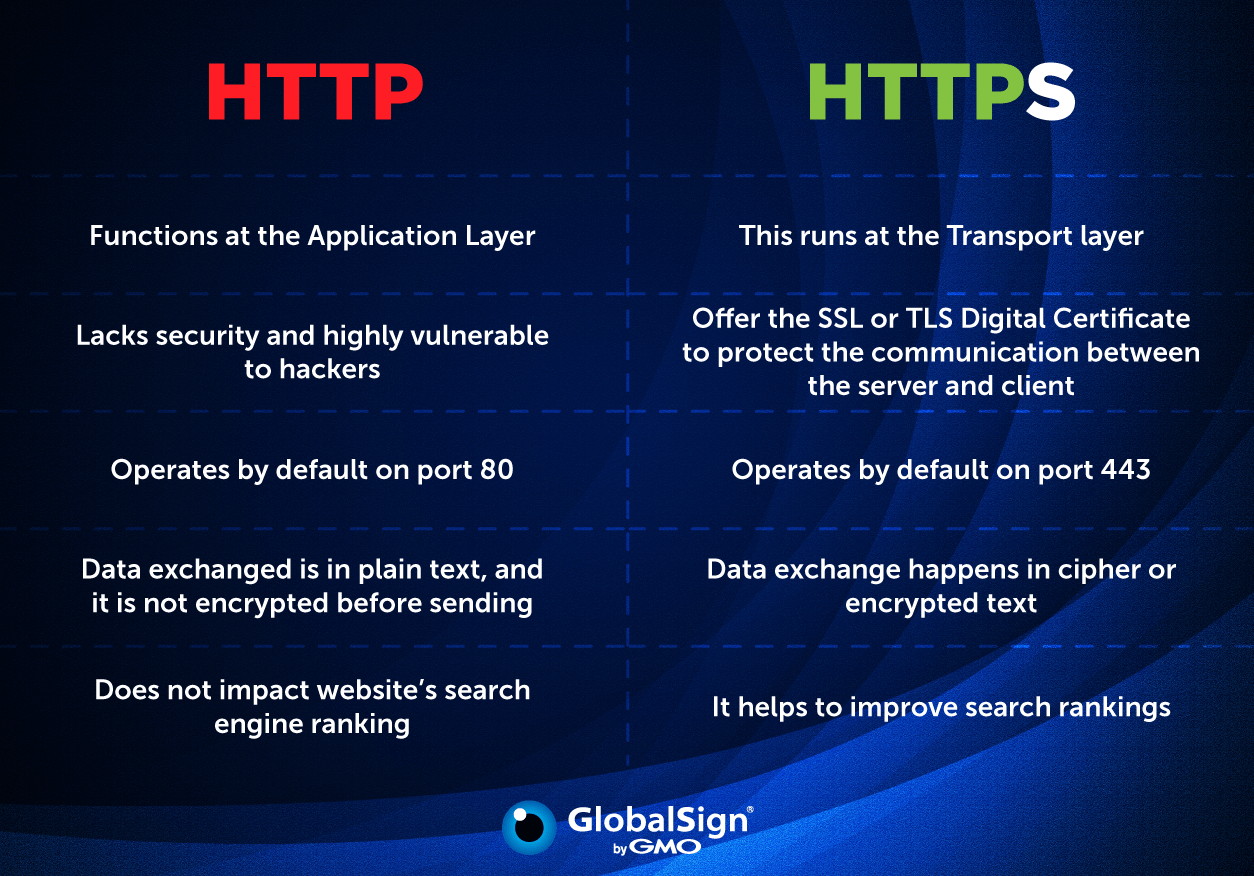
Key Differences Summarized
The core distinction between HTTP and HTTPS boils down to security. While both protocols facilitate the transfer of data, HTTPS adds the essential layers of encryption and authentication that are absent in HTTP.
| Feature | HTTP (Hypertext Transfer Protocol) | HTTPS (Hypertext Transfer Protocol Secure) |
|---|---|---|
| Security | None. Data is transmitted in plain text. | Uses TLS/SSL to encrypt data, ensuring confidentiality and integrity. |
| Port | Typically uses port 80. | Typically uses port 443. |
| URL Prefix | http:// |
https:// |
| Certificate | No digital certificate required. | Requires a valid SSL/TLS certificate issued by a Certificate Authority (CA). |
| Trust | Lower trust due to lack of encryption and authentication. | Higher trust due to verified identity and encrypted communication. |
| Vulnerability | Susceptible to eavesdropping and man-in-the-middle attacks. | Significantly more resistant to eavesdropping and data tampering. |
| Use Cases | Simple, non-sensitive data exchange (rarely used for critical functions). | Secure websites, online transactions, sensitive data transmission, API communication. |
The Impact on Data Transmission
For applications involving drone operations, the choice between HTTP and HTTPS has direct implications:
- Control and Telemetry: When a ground station or cloud platform sends commands to a drone or receives telemetry data (like GPS coordinates, battery status, or sensor readings), using HTTPS ensures that these communications are protected from interception or manipulation. This is critical for maintaining flight safety and operational integrity.
- Data Uploads and Downloads: If a drone is collecting sensitive aerial imagery, mapping data, or environmental readings, transmitting this data over HTTPS to a storage server or processing platform ensures its confidentiality and integrity. This is particularly important in sectors like public safety, defense, or commercial surveying where data privacy is paramount.
- Firmware Updates and Software Communication: When drones receive firmware updates or communicate with cloud-based AI systems for autonomous flight or object recognition, using HTTPS guarantees that the data being transferred is authentic and has not been corrupted or replaced by malicious code.
Why HTTPS is Now the Standard
In today’s interconnected world, the reliance on secure communication channels is no longer optional; it’s a fundamental requirement. Search engines like Google prioritize HTTPS-enabled websites in their search rankings, and web browsers actively warn users when they are about to visit an HTTP site, flagging it as “Not Secure.”
This trend extends beyond traditional web browsing. For any application that involves the transmission of data over a network, especially when that data is sensitive or controls critical systems, HTTPS is the de facto standard. This includes:
- Drone Fleet Management Platforms: Securely managing multiple drones, their operational parameters, and their collected data necessitates robust encryption.
- API Endpoints for Drone Services: When developers build applications that interact with drone hardware or cloud services, the APIs they use must be secured with HTTPS.
- Onboard Drone Communication: While not always direct HTTPS, many onboard systems use similar secure communication protocols for internal data exchange, mirroring the principles of TLS/SSL.
- User Interfaces and Mobile Apps: Any mobile application or web interface used to control or monitor drones must communicate with backend servers using HTTPS to protect user credentials and operational data.
The adoption of HTTPS is a clear indicator of the increasing importance of data security and privacy in all technological domains, including the advanced and often sensitive operations involving unmanned aerial vehicles and sophisticated imaging systems. Understanding this difference is a vital step in ensuring the safe, reliable, and secure use of these powerful technologies.
