OWASP ZAP, which stands for Zed Attack Proxy, is a widely-used, open-source web application security scanner. Developed and maintained by the Open Web Application Security Project (OWASP), ZAP is designed to help developers and security professionals find vulnerabilities in their web applications during the development and testing phases. It acts as an intercepting proxy, allowing users to inspect, modify, and replay HTTP messages between their browser and the target application. This capability is fundamental to understanding how web applications function and, more importantly, how they can be exploited.
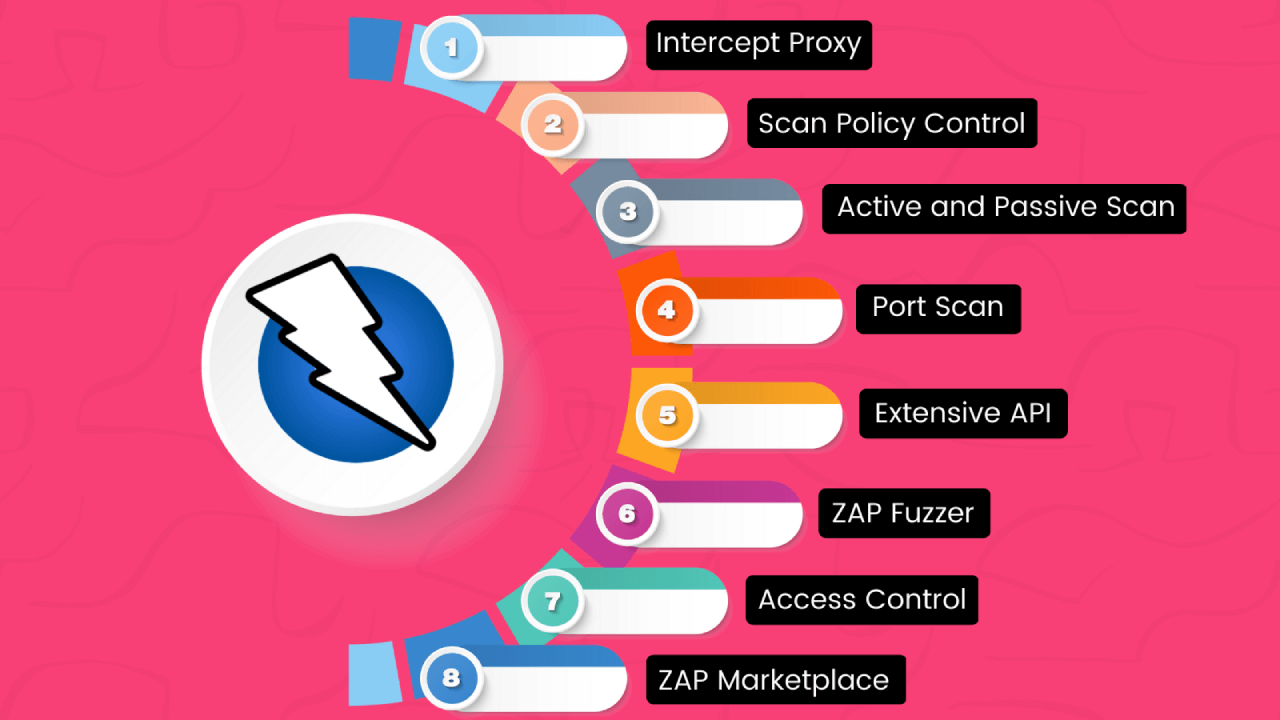
ZAP is more than just a vulnerability scanner; it’s a comprehensive platform for web application security testing. Its flexibility, extensibility, and active community support make it a powerful tool for both beginners and experienced security testers. Whether you are looking to perform automated scans to quickly identify common vulnerabilities or engage in detailed manual penetration testing, ZAP provides the necessary features and flexibility.

Core Functionality and Architecture
At its heart, OWASP ZAP operates as an intercepting proxy. This means it sits between your web browser (or any other client making HTTP requests) and the web application you are testing. All traffic passing between the client and the server is routed through ZAP. This interception is the key to its effectiveness, enabling several critical functionalities:
Intercepting Proxy
The primary function of ZAP is its intercepting proxy. When enabled, ZAP captures every HTTP request and response. This allows testers to:
- Inspect Traffic: View the raw HTTP requests and responses, including headers, cookies, and body content. This granular view is essential for understanding the communication flow and identifying potential weaknesses.
- Modify Traffic: Alter requests before they are sent to the server or modify responses before they reach the client. This is crucial for techniques like fuzzing or injecting malicious payloads to test for vulnerabilities such as Cross-Site Scripting (XSS) or SQL Injection.
- Replay Requests: Send modified or original requests to the server multiple times. This is useful for testing how an application handles different inputs or for repeating an attack.
Active and Passive Scanning
ZAP employs two primary scanning methodologies to identify vulnerabilities:
- Passive Scanning: This method analyzes HTTP requests and responses without actively sending malicious payloads. ZAP inspects the content of requests and responses for patterns that indicate known vulnerabilities. Examples include identifying outdated software versions, revealing sensitive information in error messages, or detecting insecure configurations. Passive scanning is non-intrusive and can be performed continuously as you browse the application.
- Active Scanning: This is a more aggressive approach where ZAP sends a variety of carefully crafted requests to the target application to probe for specific vulnerabilities. These requests are designed to trigger error conditions or exploit known weaknesses. Active scanning can detect a wider range of vulnerabilities, including SQL Injection, XSS, Command Injection, and more. However, it is more resource-intensive and can potentially impact the performance or stability of the target application, especially in a production environment.
Spidering and Crawling
Before actively scanning an application, ZAP needs to understand its structure. This is achieved through its spidering capabilities:
- Web Spider: The spider automates the process of discovering links and resources within a web application. It starts from a given URL and follows all discovered links, effectively mapping out the application’s attack surface. This includes HTML links, JavaScript-generated links, and forms.
- Authenticated Sessions: ZAP can be configured to authenticate with web applications, allowing the spider to explore protected areas and discover resources that require user login. This ensures that a comprehensive scan covers all accessible parts of the application.
Extensibility and Add-ons
One of ZAP’s greatest strengths is its extensibility. The platform supports a rich ecosystem of add-ons, which can be installed to enhance its functionality. These add-ons provide:
- New Scanners: Additional vulnerability detectors for specific technologies or attack vectors.
- Authentication Scripts: Support for various authentication mechanisms.
- Reporting Tools: Enhanced or customized reporting formats.
- Integrations: Connections with other security tools and CI/CD pipelines.
- Custom Rules: The ability to define and implement custom detection rules.
This modular design allows users to tailor ZAP to their specific needs and integrate it into their existing security workflows.
Key Features for Web Application Security Testing
OWASP ZAP offers a wide array of features that cater to different aspects of web application security testing, from automated scans to in-depth manual analysis.
Automated Vulnerability Scanning
ZAP’s automated scanning capabilities are a cornerstone of its utility. It can perform quick scans to identify common vulnerabilities, making it an ideal tool for continuous integration and continuous delivery (CI/CD) pipelines.
- Quick Scans: These are designed to be fast and efficient, providing a baseline assessment of the application’s security posture. They typically focus on the most prevalent and easily detectable vulnerabilities.
- Full Scans: These are more comprehensive and time-consuming, performing a deeper analysis of the application. They involve extensive probing and may cover a broader range of vulnerability types.
- API Scanning: ZAP includes specialized capabilities for scanning REST and SOAP APIs, ensuring that these critical components of modern web applications are also tested for security flaws.
Manual Exploration and Attack Tools
While automated scans are valuable, manual testing remains crucial for uncovering complex or context-specific vulnerabilities. ZAP provides a suite of tools for manual testing:
- Fuzzer: The fuzzer allows testers to send a large number of modified requests to the application, often by substituting parts of a legitimate request with a wide range of predefined or custom data. This is highly effective for finding injection vulnerabilities like SQL Injection, XSS, and command injection.
- Break and Modify Requests: As mentioned earlier, the intercepting proxy allows testers to manually break requests in progress, examine their contents, and then modify them before they are sent to the server. This provides fine-grained control over the testing process.
- Forced Browse: This feature helps discover hidden or unlinked directories and files on the web server by systematically trying common file and directory names.
- Database (DB) Explorer: This tool allows testers to interact with databases accessible through the web application, facilitating the discovery and exploitation of database-related vulnerabilities.
Authentication and Session Management Testing
Secure authentication and session management are critical aspects of web application security. ZAP provides robust features to test these areas:
- Scripting Support: ZAP supports various scripting languages (e.g., JavaScript, Python, Ruby) which can be used to automate complex authentication sequences, custom session handling, and other dynamic testing scenarios. This is invaluable for applications with multi-factor authentication or intricate login processes.
- Handle Various Authentication Methods: ZAP can be configured to handle different authentication mechanisms, including form-based authentication, HTTP basic/digest authentication, and token-based authentication.
- Session Management Analysis: It helps in understanding how the application manages user sessions, identifying potential vulnerabilities like session fixation or predictable session IDs.
Reporting and Alerting
Effective reporting is essential for communicating findings to stakeholders and developers. ZAP provides comprehensive reporting capabilities:
- Alerts Panel: ZAP presents identified vulnerabilities in a clear and organized manner in its Alerts panel. Each alert includes details about the vulnerability, its risk level, a description, and often recommendations for remediation.
- Customizable Reports: ZAP can generate reports in various formats, including HTML, XML, and JSON. These reports can be customized to include specific information and tailored to different audiences, such as technical teams or management.
- Integration with CI/CD: ZAP can be run in daemon mode or through its API, allowing for seamless integration into CI/CD pipelines. This enables automated security testing as part of the development lifecycle, shifting security left.
Getting Started with OWASP ZAP
OWASP ZAP is designed to be accessible to users of varying technical backgrounds, though a fundamental understanding of web technologies and security concepts is beneficial.
Installation and Initial Setup
ZAP can be downloaded from the official OWASP ZAP website. It is available for Windows, macOS, and Linux. The installation process is generally straightforward, involving downloading an installer and following the on-screen prompts.
Upon launching ZAP for the first time, users will typically be presented with options regarding the session management. It’s recommended to start with a “quick start” or “default” session, which will create a workspace for your testing.
Basic Workflow: Proxying and Exploring
The most fundamental way to use ZAP is as an intercepting proxy. The typical workflow involves:
- Configure Browser Proxy: Manually configure your web browser’s proxy settings to point to the address and port ZAP is listening on (by default, it’s
localhost:8080). - Start ZAP Proxy: Ensure ZAP’s proxy is enabled.
- Browse the Target Application: Navigate through your target web application using your configured browser. As you click links, submit forms, and interact with the application, ZAP will capture all the HTTP traffic.
- Inspect Traffic in ZAP: The captured requests and responses will appear in ZAP’s “History” tab, allowing you to inspect them in detail.
- Initiate a Scan: Once you have explored parts of the application, you can right-click on specific requests or the entire site in the “Sites” tree within ZAP and choose to “Attack” or “Scan” them. This will trigger ZAP’s automated scanners.
Understanding the User Interface
ZAP’s user interface is divided into several key sections:
- Sites Tree: This panel displays the structure of the web applications you are exploring, organized by domain and sub-domains.
- History Tab: Shows a chronological list of all HTTP requests and responses that have passed through ZAP.
- Alerts Tab: Lists all the vulnerabilities that ZAP has detected, categorized by risk level.
- Request/Response Viewers: These panes, typically at the bottom of the window, display the details of the selected request or response, allowing for inspection and modification.
- Add-ons Tab: Where you can manage and install new functionalities.
Best Practices and Advanced Usage
- Use in a Test Environment: Always perform security testing on applications in a controlled test or staging environment, not on live production systems, unless explicit permission and protocols are in place.
- Understand Vulnerability Types: Familiarize yourself with common web application vulnerabilities (e.g., OWASP Top 10) to better interpret ZAP’s findings.
- Leverage Scripting: For complex applications, explore ZAP’s scripting capabilities to automate repetitive tasks or handle intricate authentication flows.
- Integrate into CI/CD: Utilize ZAP’s API or command-line options to integrate automated security scans into your development pipeline.
- Explore Add-ons: Regularly check the ZAP Marketplace for new and useful add-ons that can enhance your testing capabilities.
- Community Support: The OWASP ZAP community is very active. If you encounter issues or have questions, the forums and mailing lists are excellent resources.
OWASP ZAP in the Development Lifecycle
OWASP ZAP plays a crucial role in ensuring the security of web applications throughout their entire lifecycle, from initial development to deployment and maintenance. Its integration into the development process, often referred to as “shifting security left,” helps in identifying and rectifying vulnerabilities early, which is significantly more cost-effective and efficient than fixing them after deployment.
Security in Development and Testing
During the development phase, developers can use ZAP to:
- Validate Security Controls: Test the security of authentication mechanisms, access controls, and input validation routines as they are being built.
- Identify Common Flaws: Quickly run automated scans to catch basic vulnerabilities like XSS or insecure direct object references before code is committed to the main repository.
- Understand Vulnerabilities: By examining how ZAP identifies vulnerabilities, developers gain a deeper understanding of secure coding practices.
In the testing phase, ZAP is an indispensable tool for quality assurance (QA) and security testing teams:
- Automated Regression Testing: Incorporate ZAP scans into automated test suites to ensure that new code changes do not introduce new security vulnerabilities.
- Penetration Testing: ZAP provides the foundational tools and reconnaissance capabilities necessary for manual penetration testers to conduct thorough security assessments.
- API Security Testing: With the increasing prevalence of APIs, ZAP’s API scanning features are vital for securing these critical communication channels.
CI/CD Integration and DevSecOps
The rise of DevSecOps emphasizes the integration of security practices into every stage of the software development lifecycle. OWASP ZAP is a key enabler of this paradigm:
- Automated Scans in Build Pipelines: ZAP can be configured to run automatically as part of the build process in CI/CD platforms like Jenkins, GitLab CI, GitHub Actions, or Azure DevOps. This means that every code commit or build can be automatically scanned for security issues.
- Fail Builds on Critical Vulnerabilities: Configure the CI/CD pipeline to fail the build if ZAP detects vulnerabilities above a certain severity threshold. This prevents insecure code from progressing further in the deployment pipeline.
- Continuous Monitoring: Even after deployment, ZAP can be used for periodic security scans of the live application to detect any new vulnerabilities that may have emerged due to configuration changes or new threats.
- Reporting for Compliance: The detailed reports generated by ZAP can be used to demonstrate compliance with security standards and regulations.

Collaboration Between Development and Security Teams
ZAP fosters better collaboration between development and security teams by providing a common platform and language for discussing security issues:
- Clear Vulnerability Reporting: ZAP’s detailed alerts and reports provide developers with actionable information on how to fix identified vulnerabilities, including references to best practices and remediation steps.
- Shared Understanding: By working with ZAP, developers become more security-aware, and security professionals gain a better understanding of the development process.
- Iterative Improvement: The feedback loop provided by ZAP scans allows for continuous improvement of the application’s security posture over time.
In conclusion, OWASP ZAP is a powerful, versatile, and free tool that is essential for anyone involved in web application security. Its ability to intercept, inspect, and attack web traffic, combined with its extensive scanning capabilities and extensibility, makes it a cornerstone of modern web security testing and a vital component of DevSecOps practices.
