Alternate Data Streams (ADS), a feature deeply embedded within the NTFS (New Technology File System) used by Windows operating systems, represent a powerful yet often overlooked method for attaching additional, non-visible data to files. While not directly visible in standard file explorers like Windows Explorer, ADS can store a wealth of information, from metadata and resource forks to entirely separate data payloads. Understanding ADS is crucial for professionals working in cybersecurity, digital forensics, and even for advanced system administrators seeking to leverage its capabilities for specific applications within the realm of tech and innovation.

The Fundamentals of NTFS and ADS
The NTFS file system, introduced with Windows NT, was designed with advanced features beyond the capabilities of its predecessors like FAT. One of these innovations is the concept of the Master File Table (MFT). The MFT is essentially a database that contains an entry for every file and directory on an NTFS volume. Each MFT entry comprises a set of attributes that describe the file, such as its name, size, timestamps, security permissions, and importantly, its data.
Traditionally, a file’s content is stored within its primary data attribute. However, NTFS allows for the creation of multiple data attributes associated with a single file. These additional data attributes are known as Alternate Data Streams. Each ADS is essentially a separate stream of data that is intrinsically linked to the parent file. When you view a file in a standard file explorer, you are only seeing the primary data stream. The existence and content of any ADS are transparent to most users and applications.
The syntax for referencing an ADS typically involves appending a colon and the stream name to the original file’s path. For example, myfile.txt:secretdata.txt would refer to an ADS named secretdata.txt associated with myfile.txt. This syntax is fundamental to interacting with ADS, whether for creating, reading, or deleting them.
The Master File Table (MFT) and File Attributes
At the heart of NTFS’s ability to support ADS lies the Master File Table (MFT). Each file and directory on an NTFS volume has a corresponding record in the MFT. This record is structured as a series of attributes, each identified by a type code. The $DATA attribute is the primary attribute that holds the main content of a file. However, NTFS permits the existence of multiple $DATA attributes, each with its own identifier and content. These are the Alternate Data Streams.
When a file is created, its basic information – filename, size, timestamps, etc. – are stored as attributes in its MFT record. If additional data is associated with this file, it can be written to a new $DATA attribute, forming an ADS. This attribute is then referenced within the MFT entry of the parent file, creating a direct link. The operating system’s file handling mechanisms are designed to recognize and manage these multiple data streams, even though they are not presented as separate files in a typical directory listing.
How ADS are Stored and Referenced
The physical storage of ADS can vary. For smaller ADS, their content might be stored directly within the MFT record of the parent file. This is known as “resident” data. This allows for very quick access to the ADS content without requiring separate disk I/O operations. However, for larger ADS, their content will be stored in separate clusters on the disk, similar to how the primary data stream of a large file is stored. In this “non-resident” scenario, the MFT entry will contain pointers to the disk clusters where the ADS data resides.
The referencing mechanism is critical. When an application or a tool needs to access an ADS, it uses the special colon-separated path format. For example, to write data to an ADS named “MyMetadata” for a file named “report.docx,” a command might look like:
echo "This is hidden metadata." > report.docx:MyMetadata
This command tells the NTFS driver to create or append data to the “MyMetadata” ADS associated with “report.docx”. The operating system then translates this request into an operation that modifies the MFT entry and potentially writes data to disk clusters.
Applications of Alternate Data Streams in Tech & Innovation
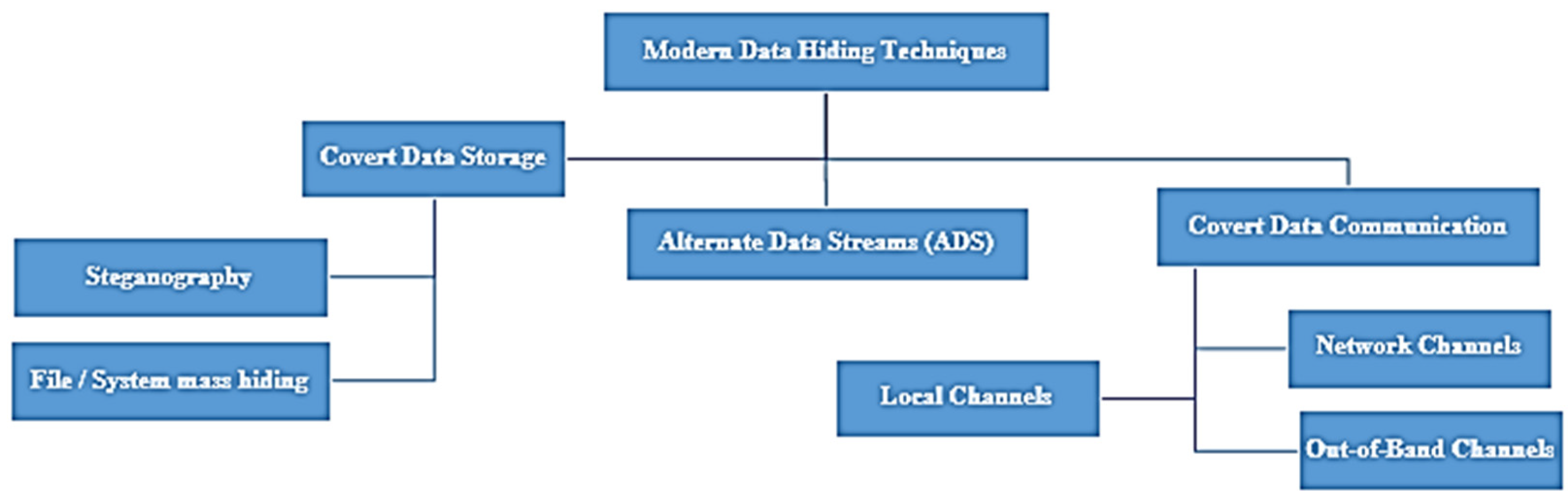
While ADS can be used for benign purposes, their stealthy nature has also made them a popular tool for malicious actors, particularly in the cybersecurity domain. Understanding these applications is vital for developing robust defense mechanisms and for conducting effective digital investigations.
Cybersecurity and Digital Forensics
In the realm of cybersecurity, ADS offer a discreet way to hide malicious code, configuration files, or exploit payloads. Malware authors can attach executables or scripts to seemingly innocuous files, making them difficult to detect by traditional antivirus software that primarily scans the main file content. During a security incident, discovering and analyzing ADS can be a critical step in understanding the attack vector and the tools used by an adversary.
Digital forensics professionals frequently encounter ADS during investigations. They are often used to conceal evidence, such as logs, chat histories, or even complete programs, linked to legitimate files. Tools specifically designed to scan for and extract ADS are indispensable for forensic analysts. The ability to uncover hidden data can provide crucial insights into user activity, system compromise, and the perpetrators of cybercrimes.
Hiding Malware Payloads
One of the classic uses of ADS in malware is to hide the actual executable payload. A seemingly harmless document, image, or even a system file can have a malicious program hidden within an ADS. When the user interacts with the primary file, or when a vulnerability is triggered, the operating system might be tricked into executing the code within the ADS. This bypasses many security measures that are designed to scan the visible content of files.
Storing Command and Control (C2) Information
Malware often needs to communicate with a command and control server. ADS can be used to store the IP addresses, domain names, or other connection parameters for these C2 servers. This information can be updated remotely by the attacker without leaving visible traces within the primary file. This makes it harder for defenders to disrupt the communication channels.
Evidence Concealment by Attackers
Conversely, attackers may use ADS to conceal evidence of their activities. This could include logs of their actions, scripts they used to move laterally within a network, or credentials they exfiltrated. By attaching this data to unrelated files, they aim to make it harder for forensic investigators to find and analyze it.
Data Integrity and Metadata Management
Beyond security applications, ADS can serve legitimate purposes in managing file-related information. They can be used to store extended metadata that is not covered by the standard file system attributes. This can include custom properties, author information, version history, or even application-specific configurations.
For example, a content management system could use ADS to store a thumbnail image or a preview of a document directly alongside the original file, without cluttering the primary file’s data. This keeps related data together and can improve performance by reducing the need for separate lookups. Similarly, software applications might use ADS to store configuration settings, license keys, or cached data associated with the main program file.
Extended File Properties
Many applications store information about a file that doesn’t fit neatly into standard file attributes. This could be anything from authoring details for a creative work, specific settings for a configuration file, or even a brief summary of the file’s content. Using ADS allows this information to be stored directly with the file, ensuring it remains associated even if the file is moved or copied.
Application-Specific Configurations
Software developers can leverage ADS to store application-specific configuration data for their programs. This might include user preferences, temporary cache data, or even small resource files needed by the application. By attaching these to the executable or associated data files, the application can manage its own internal data structures discreetly.
Resource Forks and Compatibility
Historically, systems like classic Mac OS used the concept of “resource forks” and “data forks” for files. The data fork contained the actual content, while the resource fork stored metadata, icons, and other application resources. When files from these systems were moved to Windows, the resource fork data was sometimes lost or mishandled. ADS provided a way to emulate this behavior on NTFS systems, allowing some Windows applications to store their resources in ADS associated with the main file.
Interacting with Alternate Data Streams
Working with ADS requires specialized tools or commands, as standard file operations will not reveal them. Several command-line utilities and graphical tools are available for managing ADS.
Command-Line Utilities
The most fundamental tool for interacting with ADS on Windows is the dir command with specific switches, or dedicated command-line utilities. For instance, the dir /R command can list ADS associated with files.
dir /R
The dir /R command is a built-in Windows utility that can reveal ADS. When executed on a directory, it will list files that have ADS attached to them, along with the names of those streams. For example, a file document.txt with an ADS named metadata.xml might be listed like this:
dir /R
Volume in drive C has no label.
Volume Serial Number is XXXX-XXXX
Directory of C:UsersExampleDocuments
01/01/2023 10:00 AM 123 document.txt
45 document.txt:metadata.xml
1 File(s) 123 bytes
0 Dir(s) 123,456,789,123 bytes free
streams.exe (Sysinternals)
A more powerful and widely used tool for managing ADS is streams.exe from the Microsoft Sysinternals suite. This command-line utility can recursively scan directories for ADS, list them, and also delete them.
To list all ADS in a directory and its subdirectories, you would typically use:
streams -s C:PathToDirectory
To delete all ADS associated with a specific file, you might use:
streams -d C:PathToFile.txt
Caution: Deleting ADS is a permanent operation and should be performed with extreme care, especially in forensic investigations, as it can irrevocably remove evidence.
Graphical Tools
Several third-party graphical tools offer a more user-friendly interface for managing ADS. These tools typically scan a selected drive or directory and present a visual representation of files with attached ADS, allowing users to view, extract, or delete them through a point-and-click interface. These are often favored by users who are less comfortable with the command line but need to interact with ADS.
Challenges and Considerations
Despite their utility, ADS present several challenges and require careful consideration, especially when dealing with cross-platform compatibility, security implications, and data management.
Cross-Platform Compatibility
ADS are a feature specific to the NTFS file system. When files with ADS are copied to or accessed from other file systems (like FAT32, exFAT, or HFS+ used by macOS), the ADS data is typically lost. This can lead to data corruption or the loss of important information if not handled properly. For applications that rely on ADS, it is crucial to ensure that the target file system supports them or to implement alternative methods for data storage and retrieval.
Security Risks and Detection
As discussed, the stealthy nature of ADS makes them a significant security risk. Antivirus software and intrusion detection systems are continuously evolving to better detect and flag suspicious ADS activity. However, sophisticated attackers can often devise new ways to bypass these defenses. Awareness of ADS and the use of specialized detection tools are essential for maintaining a secure computing environment.
Data Management and Organization
While ADS can keep related data together, overuse or improper management can lead to complexity. It can become difficult to track which files have ADS, what their content is, and how they are being used. For organizations, establishing clear policies and procedures for using ADS, and employing tools for inventory and management, is important to avoid a chaotic and unmanageable data landscape.

Conclusion
Alternate Data Streams are a powerful and often hidden feature of the NTFS file system. They offer unique capabilities for attaching additional data to files, with applications ranging from cybersecurity and digital forensics to sophisticated data management and metadata storage. While their stealthy nature can be exploited for malicious purposes, understanding how ADS work, how to interact with them, and their implications is crucial for professionals in the technology sector, particularly in areas focused on advanced system capabilities, security, and data integrity. As technology continues to evolve, the role and detection of Alternate Data Streams will remain a pertinent area of interest and development.
