The digital landscape is constantly evolving, with new technologies emerging to enhance security, streamline communication, and facilitate remote access. Among these, SSH (Secure Shell) plays a pivotal role, offering a secure way to connect to remote servers. However, SSH’s capabilities extend beyond simple command-line access; one of its most powerful features is the ability to create SSH tunnels, also known as SSH port forwarding. This sophisticated technique allows for the secure transmission of data for applications that were not originally designed with encryption in mind, effectively extending the security of an SSH connection to other network traffic. Understanding SSH tunneling is crucial for anyone looking to bolster their network security, access resources remotely with confidence, or manage complex network configurations.
The Fundamentals of SSH Tunneling
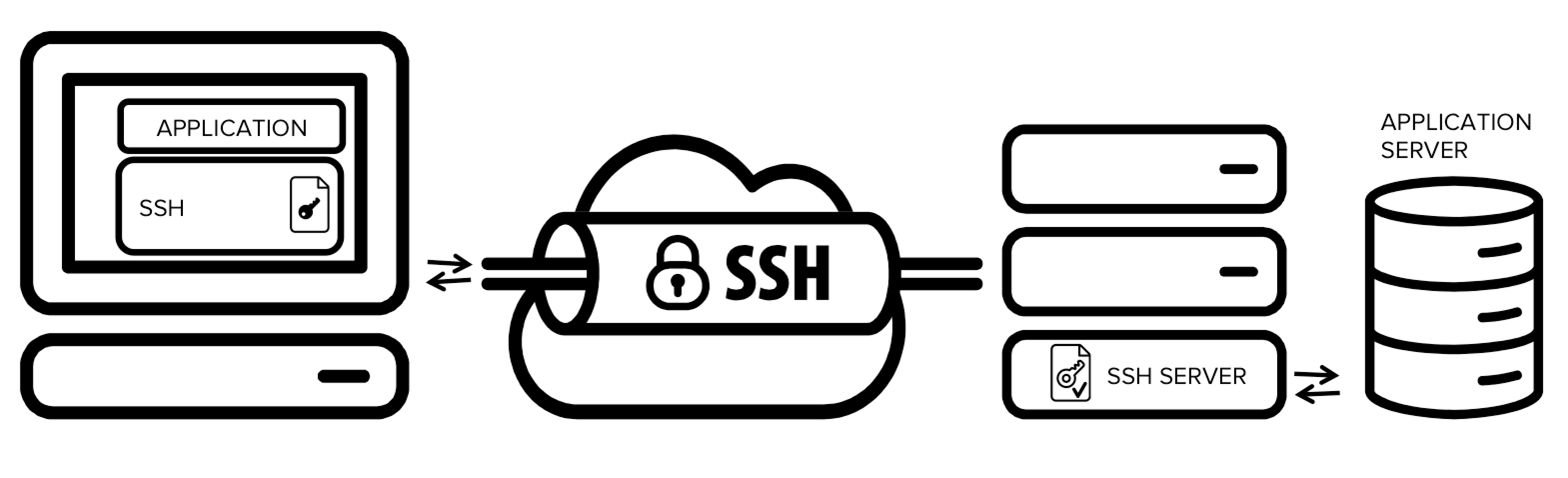
At its core, an SSH tunnel leverages the secure, encrypted connection established by SSH to create a secure pathway for other network protocols. Imagine an encrypted tunnel through an otherwise public or potentially insecure network. Data entering this tunnel at one end emerges at the other end, decrypted and ready for its intended destination, all while being shielded from prying eyes during transit. This is precisely what an SSH tunnel achieves.
There are three primary types of SSH tunnels, each serving a distinct purpose:
Local Port Forwarding
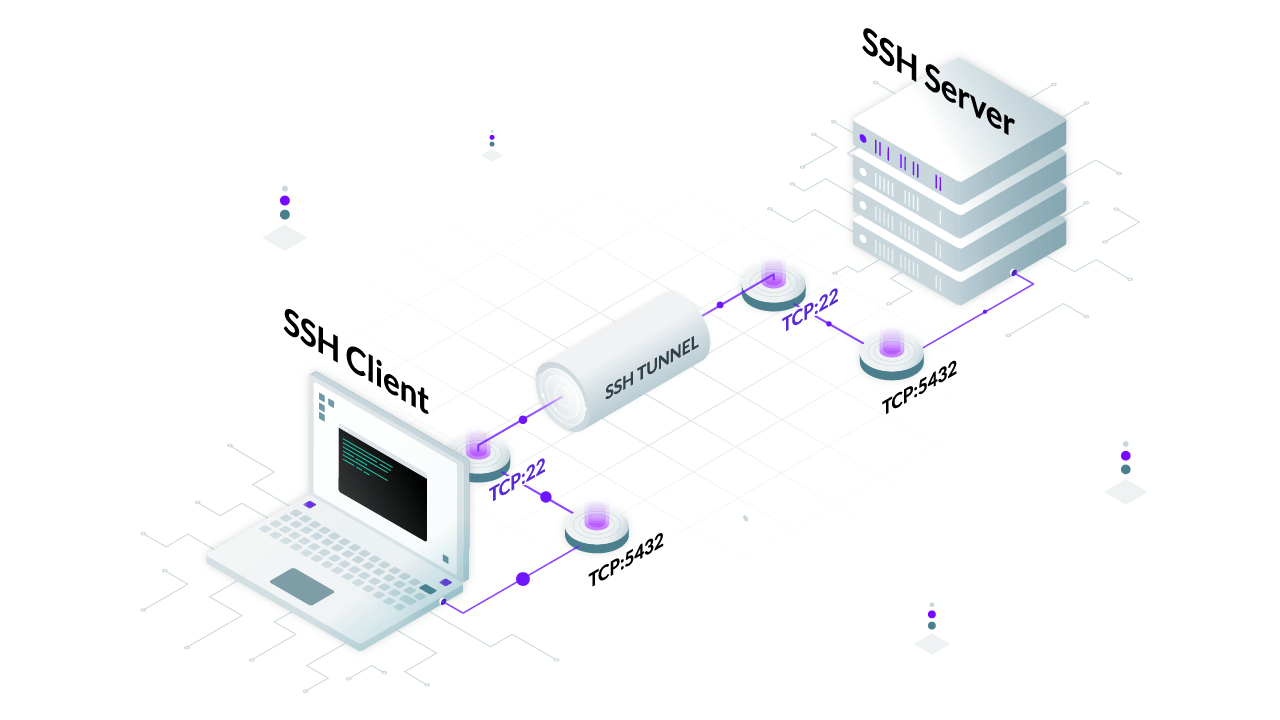
Local port forwarding is arguably the most common and intuitive type of SSH tunnel. It’s used to forward traffic from a port on your local machine to a port on a remote server, or even to a different machine accessible from that remote server.
How it Works:
- Establish an SSH Connection: You initiate an SSH connection to a remote server.
- Define the Local Port: You specify a local port on your machine that will act as the entry point for the data you want to tunnel. This port will listen for incoming connections.
- Specify the Destination: You define the actual destination host and port that the traffic should ultimately reach. This could be a service running on the SSH server itself, or another server accessible from the SSH server.
- The Tunnel: When an application on your local machine connects to the specified local port, the SSH client encrypts this traffic, sends it through the SSH connection to the remote server.
- Decryption and Forwarding: The SSH server on the remote end receives the encrypted data, decrypts it, and then forwards it to the specified destination host and port.
- Return Traffic: Any response from the destination is sent back to the SSH server, encrypted, sent back to your local SSH client, decrypted, and then delivered to the originating application.
Use Cases for Local Port Forwarding:
- Accessing Internal Web Services: If a web server is running on a private network behind a firewall, and you have SSH access to a machine on that internal network, you can use local port forwarding to access the web server as if it were running on your local machine. For instance, if a database admin interface is only accessible from the database server itself, and that server is on a private network, you can tunnel to it through an SSH-accessible jump host.
- Securing Insecure Protocols: Applications that use unencrypted protocols (like older versions of VNC or certain database connections) can be secured by tunneling their traffic through an SSH tunnel. This adds a layer of encryption, protecting sensitive data from eavesdropping.
- Bypassing Firewalls: If direct access to a service is blocked by a firewall, but SSH access to a server behind that firewall is permitted, you can use local port forwarding to create a secure pathway to the blocked service.
Example Command (Local Port Forwarding):
ssh -L 8080:localhost:80 user@remote_server
In this command:
-L 8080:localhost:80instructs the SSH client to forward connections from local port 8080 to port 80 on thelocalhostas seen from theremote_server.user@remote_serverspecifies the username and the remote server to connect to.
After running this command, any application on your local machine connecting to localhost:8080 will have its traffic securely sent through the SSH connection and appear on the remote_server as a connection to localhost:80.
Remote Port Forwarding
Remote port forwarding achieves the opposite of local port forwarding. It allows a port on the remote server to forward traffic back to your local machine, or to a service accessible from your local machine.
How it Works:
- Establish an SSH Connection: You initiate an SSH connection from your local machine to a remote server.
- Define the Remote Port: You specify a port on the remote server that will listen for incoming connections.
- Specify the Destination: You define the actual destination host and port that the traffic should ultimately reach on your local network.
- The Tunnel: When an application on the remote server (or another machine that can reach the remote server) connects to the specified remote port, the SSH server on the remote end forwards this connection request through the established SSH tunnel back to your local SSH client.
- Local Forwarding: Your local SSH client receives the encrypted request, decrypts it, and then forwards it to the specified destination host and port on your local network.
Use Cases for Remote Port Forwarding:
- Exposing Local Services to the Internet Securely: If you have a web server or an API running on your local machine that you need to make temporarily accessible to someone on the internet, but you cannot directly expose your local machine due to NAT or firewall restrictions, remote port forwarding is your solution. You can tunnel a port from a publicly accessible server back to your local service.
- Callback Mechanisms: In scenarios where a remote system needs to initiate a connection back to a system behind a firewall, remote port forwarding enables this by opening a listening port on the remote server that directs traffic to the local client.
- Remote Development and Debugging: Developers can use remote port forwarding to allow remote debugging tools or IDEs to connect to applications running on their local development machine from a remote server.
Example Command (Remote Port Forwarding):
ssh -R 9090:localhost:8000 user@remote_server
In this command:
-R 9090:localhost:8000instructs the SSH client to set up a listener on theremote_server‘s port 9090. Connections to this port on theremote_serverwill be forwarded back tolocalhost:8000on your local machine.user@remote_serverspecifies the username and the remote server to connect to.
After executing this, any connection made to remote_server:9090 will be routed to localhost:8000 on your local machine.
Dynamic Port Forwarding (SOCKS Proxy)
Dynamic port forwarding is the most versatile type of SSH tunnel. Instead of forwarding traffic from a specific local port to a specific remote destination, it turns your SSH client into a SOCKS proxy server. This allows any application configured to use the SOCKS proxy to route its traffic through the SSH tunnel.
How it Works:
- Establish an SSH Connection: You initiate an SSH connection to a remote server.
- Define a Local Listening Port: You specify a local port on your machine that will act as the SOCKS proxy server.
- The Tunnel: When an application is configured to use your local SSH client as a SOCKS proxy and sends a request to this proxy, the SSH client receives the request.
- Dynamic Destination Resolution: The SSH client then determines the final destination based on the application’s request and forwards the traffic through the encrypted SSH connection to the remote SSH server.
- Destination Access: The remote SSH server then makes the connection to the actual destination on behalf of your application. All subsequent traffic for that connection is tunneled back and forth.
Use Cases for Dynamic Port Forwarding:
- Secure Browsing: You can configure your web browser to use the SOCKS proxy provided by the SSH tunnel. This encrypts all your web traffic and routes it through the remote server, effectively masking your IP address and securing your browsing activity on public Wi-Fi networks.
- Accessing Geo-Restricted Content: By connecting to an SSH server in a different geographical location, you can access content or services that are restricted to that region.
- Unified Proxy for Multiple Applications: Unlike local port forwarding which is typically one-to-one, dynamic forwarding allows multiple applications to use the same SOCKS proxy, simplifying the management of proxied traffic.
Example Command (Dynamic Port Forwarding):
ssh -D 1080 user@remote_server
In this command:
-D 1080instructs the SSH client to create a SOCKS proxy server listening on local port 1080.user@remote_serverspecifies the username and the remote server to connect to.
After running this, you would configure your applications (like a web browser) to use localhost as the SOCKS host and 1080 as the SOCKS port.
Advanced SSH Tunneling Concepts and Best Practices
While the basic mechanics of SSH tunneling are straightforward, advanced usage and careful configuration can unlock even greater power and security.
Chaining SSH Tunnels
It’s possible to chain SSH tunnels, meaning you can establish an SSH tunnel through another SSH tunnel. This is useful in highly restrictive network environments where you might need to traverse multiple SSH servers to reach your final destination. For example, you might have access to a bastion host, and from that bastion host, you can SSH to another internal server. You can chain tunnels to route traffic through both.
SSH Tunneling with Specific Applications
Many applications support direct configuration for SOCKS proxies or can be easily configured to use a local port forwarded service. Beyond web browsers, tools like curl, wget, and even some email clients can be set up to leverage SSH tunnels for secure and private data transfer.
Security Considerations
- Key-Based Authentication: Always use SSH keys instead of passwords for authentication when setting up tunnels, especially for automated processes or long-running tunnels. This significantly enhances security.
- Restricting Remote Forwarding: Be cautious with remote port forwarding. If not configured properly, it can inadvertently expose local services to the internet. Use
GatewayPorts noon the SSH server configuration (sshd_config) to prevent remote forwarded ports from being accessible from outside the remote server’s localhost interface, unless explicitly required. - Dedicated SSH Users: For tunnels that are used for specific purposes or by specific applications, consider creating dedicated SSH user accounts with limited privileges on the remote server.
- Firewall Rules: Ensure that the necessary ports for SSH (typically port 22) are open on the firewalls between your client and the SSH server.
Performance and Reliability
- SSH KeepAlive Options: For long-running tunnels, configure
ServerAliveIntervalandServerAliveCountMaxon the client-side (ssh_config) or use the-ooption in the command line. This helps maintain the connection by sending periodic “keep-alive” messages, preventing idle connections from being terminated by network devices. - Backgrounding SSH Tunnels: Use the
-fflag with SSH to put the client into the background after authentication, keeping the tunnel active without tying up your terminal. Combined with-N(do not execute a remote command), this is ideal for setting up persistent tunnels. For example:ssh -f -N -D 1080 user@remote_server.

Conclusion
SSH tunneling is a powerful and versatile tool for securing network traffic, enabling remote access, and navigating complex network infrastructures. By understanding the principles of local, remote, and dynamic port forwarding, users can significantly enhance their security posture and unlock new possibilities for remote connectivity. Whether you are a system administrator managing distributed systems, a developer working with remote resources, or an individual seeking to enhance your online privacy, mastering SSH tunneling is an invaluable skill in today’s interconnected world. It transforms the humble SSH connection into a secure conduit for virtually any network application, providing a robust and flexible solution for a wide array of technical challenges.
