Understanding the Foundation of DNS Data Exchange
The Domain Name System (DNS) is the internet’s fundamental directory, translating human-readable domain names into machine-readable IP addresses. While the end-user experience of browsing the web is seamless, behind the scenes, a complex and robust system ensures this translation happens accurately and efficiently. Central to this intricate network are the concepts of authoritative DNS servers and the mechanisms by which their data is synchronized. A critical operation underpinning this synchronization is the DNS zone transfer, a process that allows for the replication of DNS data from one name server to another. Understanding what a DNS zone transfer is, how it works, and its implications is crucial for anyone involved in network administration, cybersecurity, or even those seeking a deeper appreciation of the internet’s infrastructure.
At its core, a DNS zone transfer, often referred to as AXFR (Authoritative Transfer), is a mechanism by which a secondary (or slave) DNS server obtains a complete copy of a zone file from a primary (or master) DNS server. A “zone file” is a text file containing all the DNS records for a specific domain or a designated portion of the DNS namespace, known as a zone. These records include essential information such as A records (mapping hostnames to IPv4 addresses), AAAA records (mapping hostnames to IPv6 addresses), CNAME records (creating aliases), MX records (specifying mail servers), and NS records (identifying name servers for the zone).
The DNS hierarchy is designed with redundancy and fault tolerance in mind. For any given domain, multiple name servers are typically designated as authoritative. This means they hold the definitive records for that domain. Among these authoritative servers, one is designated as the primary server, responsible for managing and updating the zone file. The others are secondary servers, which maintain a copy of the primary’s zone file. This hierarchical structure is vital; if the primary server experiences an outage, secondary servers can continue to respond to DNS queries, ensuring domain availability. The zone transfer is the mechanism that keeps these secondary servers up-to-date with the primary’s information.
The Mechanics of a DNS Zone Transfer
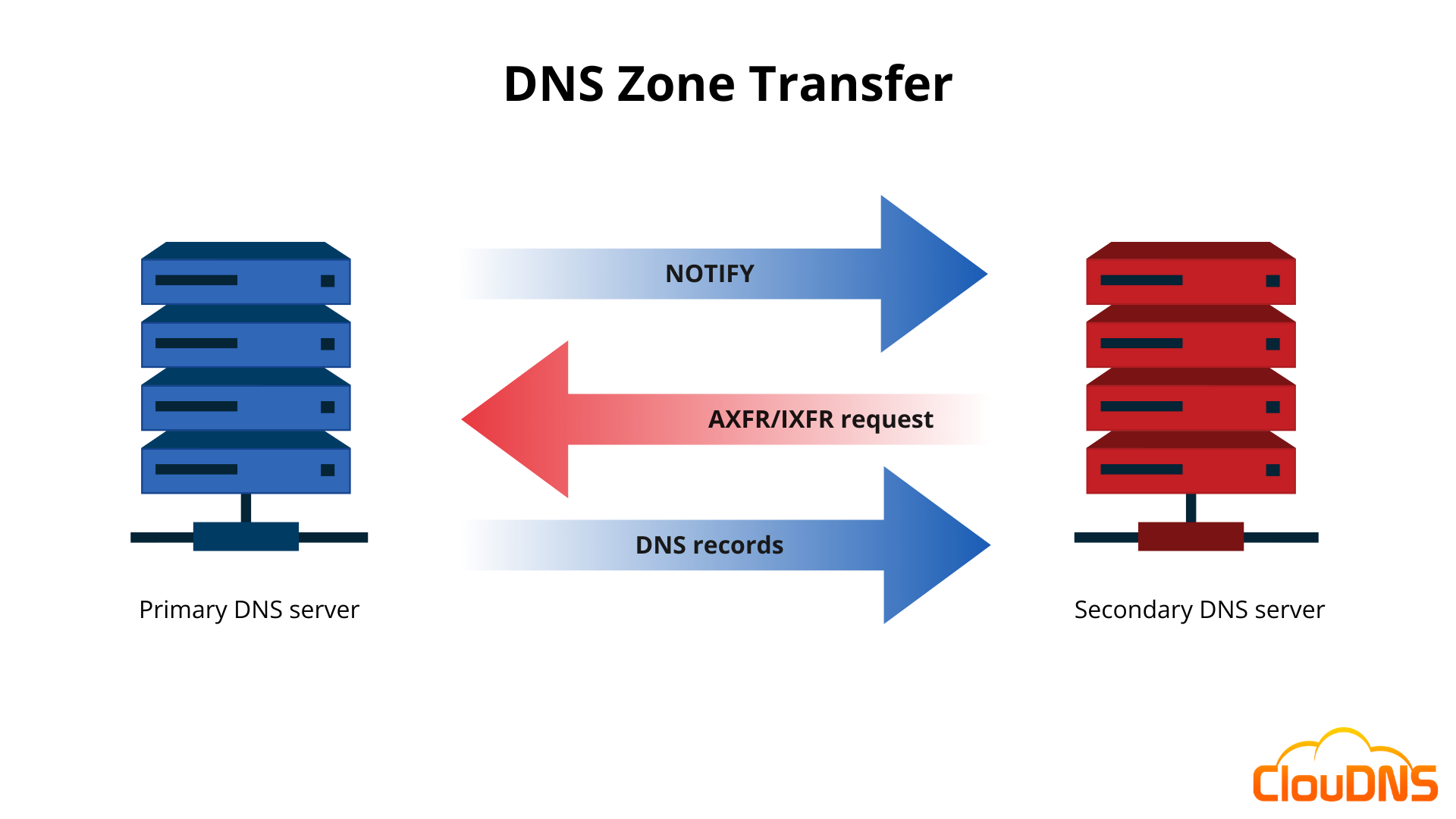
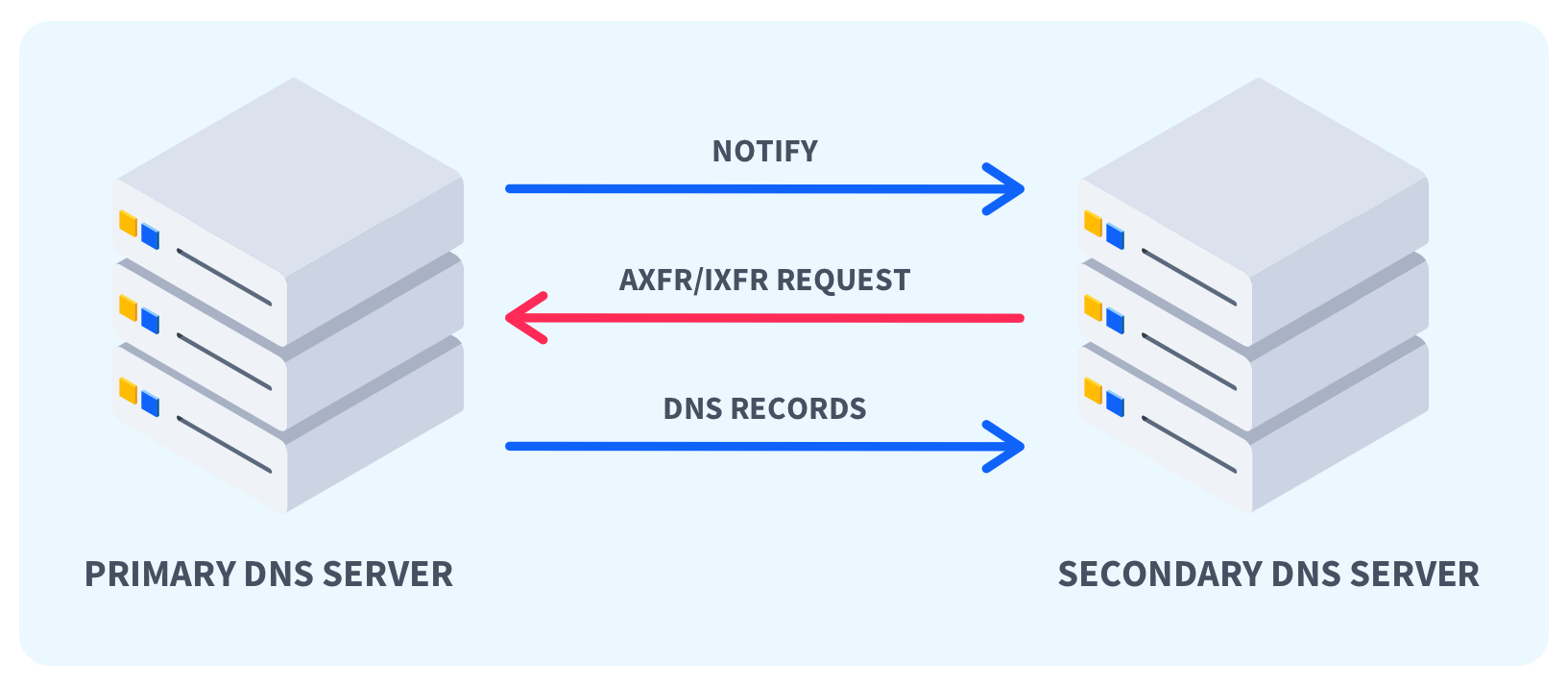
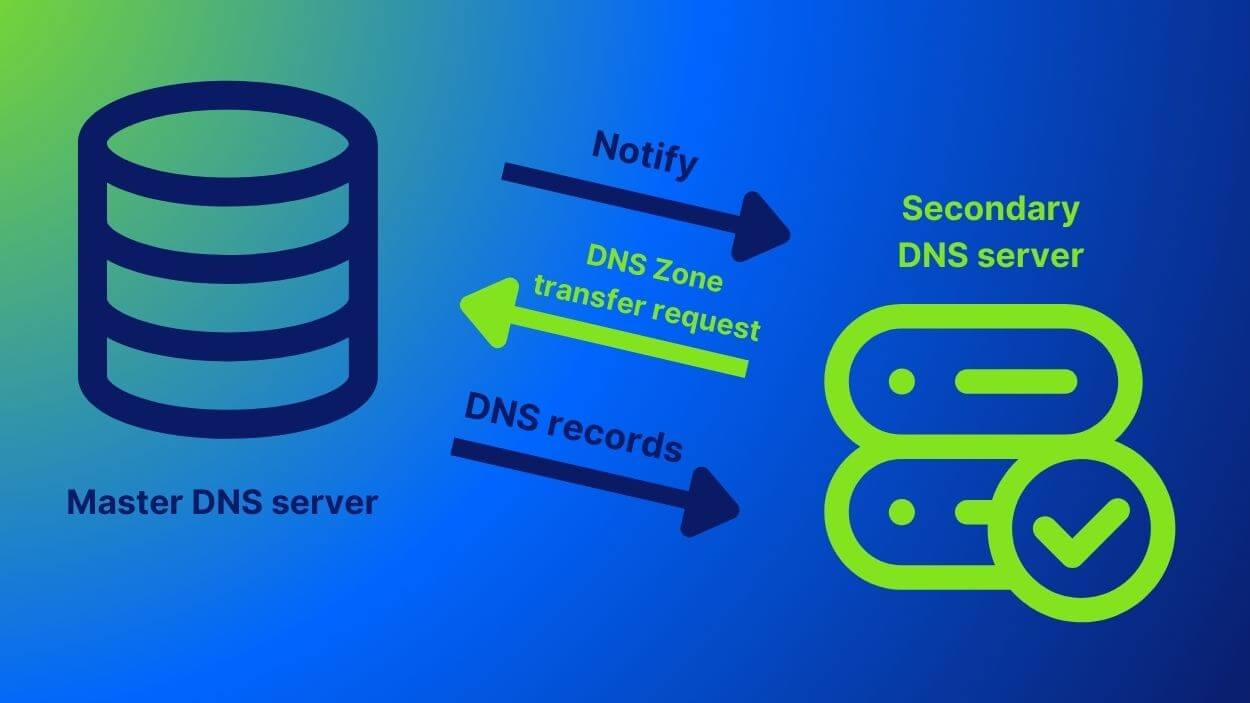
The process of a DNS zone transfer is initiated periodically or in response to specific events. Primarily, secondary name servers poll the primary name server to check for updates. This polling mechanism relies on the serial number within the SOA (Start of Authority) record of the zone file. The SOA record contains critical administrative information about the zone, including its serial number. Every time the primary server’s zone file is updated, the serial number must be incremented. This simple yet effective method allows secondary servers to quickly determine if their copy of the zone file is outdated.
When a secondary server checks with the primary and finds that the serial number on the primary’s SOA record is higher than its own, it knows an update is available. It then requests a full zone transfer. The primary server responds by sending the entire zone file to the secondary server. Once the secondary server receives the complete zone file, it updates its local copy and, in turn, its SOA serial number to match the new version. This ensures that all authoritative name servers for a given domain are synchronized and providing consistent DNS resolution information.
There are two primary types of zone transfers:
Full Zone Transfer (AXFR)
AXFR is the foundational method for transferring an entire zone file. When a secondary server requests an AXFR, the primary server sends all the resource records within that zone. This is a comprehensive transfer, ensuring the secondary server has a complete and accurate replica. While robust, AXFR can be bandwidth-intensive, especially for large zones, as it requires transmitting the entire dataset every time an update is detected. It is typically initiated by the secondary server based on the SOA serial number check.
Incremental Zone Transfer (IXFR)
To address the bandwidth concerns associated with AXFR, Incremental Zone Transfer (IXFR) was developed. IXFR allows a secondary server to request only the changes made to the zone file since its last update. The primary server then sends a list of only the added, deleted, or modified records, rather than the entire zone file. This is significantly more efficient for zones that experience frequent, minor updates. For IXFR to function, both the primary and secondary servers must support it, and the primary server must maintain a log of zone file changes. When a secondary requests an update, the primary checks if it can fulfill the request with an IXFR. If the secondary supports IXFR and the primary can provide the differential data, an IXFR is performed. Otherwise, the primary will fall back to an AXFR.
Security Implications and Best Practices
While DNS zone transfers are essential for the proper functioning and resilience of the DNS infrastructure, they also present significant security implications if not managed correctly. By design, a zone transfer reveals the complete DNS records for a domain. This includes not only publicly accessible hostnames and their IP addresses but potentially internal hostnames, subdomains, and other sensitive information that an attacker could use for reconnaissance.
Reconnaissance and Attack Vectors
Attackers can exploit an unsecured zone transfer to gather a comprehensive map of a network’s infrastructure. By obtaining a full zone file, they can identify:
- All active hosts: This includes servers, workstations, and network devices.
- Subdomains: Discovering subdomains can reveal areas of the network that might be less secured or that host specific applications.
- Internal hostnames: Some internal naming conventions might be exposed, providing clues about the organization’s structure and naming schemes.
- Services: While not directly exposed in standard DNS records, the presence of certain hostnames (e.g.,
mail,ftp,vpn) can indicate the services running on specific IP addresses.
This information can be invaluable for an attacker planning further exploits, such as targeted phishing attacks, identifying vulnerable services, or planning denial-of-service attacks.
Preventing Unauthorized Zone Transfers
Given these risks, it is paramount to implement robust security measures to prevent unauthorized zone transfers. The most common and effective method is to restrict zone transfer requests to only authorized secondary DNS servers.
- ACLs (Access Control Lists): Most DNS server software (like BIND or Microsoft DNS) allows administrators to configure Access Control Lists. These lists specify which IP addresses are permitted to request zone transfers. By default, zone transfers should be restricted to the IP addresses of known and trusted secondary name servers.
- Host-based Firewalls: In addition to DNS server configurations, host-based firewalls on the primary DNS server can be used to block zone transfer requests from any IP address not explicitly allowed.
- Network Segmentation: Properly segmenting networks can further limit the potential reach of an unauthorized zone transfer, even if it occurs.
- Regular Auditing: Regularly audit DNS server configurations and zone transfer logs to identify any suspicious activity.
It is crucial to understand that zone transfers are not intended to be publicly accessible. They are an internal synchronization mechanism. Broadcasting the ability to perform a zone transfer publicly is akin to leaving a detailed blueprint of your network unattended.
The Role of DNS Zone Transfers in Modern DNS Architectures
While the fundamental principles of DNS zone transfers remain consistent, their implementation and importance are viewed within the context of evolving DNS architectures. Modern DNS environments often leverage cloud-based DNS services, distributed DNS infrastructures, and sophisticated load balancing techniques.
Cloud-Based DNS and Managed Services
Many organizations today utilize cloud-based DNS providers (e.g., Amazon Route 53, Google Cloud DNS, Azure DNS). In these managed environments, the concept of a “primary” and “secondary” server is abstracted. The cloud provider handles the replication and synchronization of DNS data across their global network of name servers. While the underlying mechanisms might still involve data transfer protocols similar in principle to AXFR/IXFR, the administration and control are managed through APIs and web consoles. Users typically don’t directly configure zone transfers in the same way they would with self-hosted DNS servers. The provider ensures that the DNS data is consistent and highly available across all their points of presence.
Dynamic DNS (DDNS)
Dynamic DNS is a different, albeit related, mechanism that allows IP addresses to be updated automatically. Unlike traditional DNS zone transfers which replicate static zone files, DDNS is used to update DNS records in real-time when a dynamic IP address changes, often for residential internet connections or mobile devices. This process typically involves a client on the device sending an update request to a DDNS provider, which then updates the specific DNS record. While not a zone transfer in the AXFR/IXFR sense, it highlights the need for mechanisms to keep DNS information current.
DNSSEC and Zone Signing
DNS Security Extensions (DNSSEC) adds another layer of complexity and security to DNS. DNSSEC uses digital signatures to authenticate DNS data. Zone signing involves creating these digital signatures for DNS records within a zone. When zone data is transferred, especially in a hierarchical setup, these signatures must also be propagated and maintained. The process of transferring signed zones requires careful management to ensure the integrity of the signatures. While AXFR and IXFR still serve as the transport mechanisms, they are now carrying cryptographically signed data, adding an extra consideration for security and synchronization.
Conclusion
DNS zone transfers are an indispensable component of the Domain Name System, providing a reliable method for synchronizing DNS data across multiple authoritative name servers. Whether it’s the comprehensive full zone transfer (AXFR) or the more efficient incremental zone transfer (IXFR), these mechanisms are critical for ensuring the availability and accuracy of DNS resolution. However, their power also necessitates a strong understanding of their security implications. By implementing proper access controls and adhering to best practices, administrators can safeguard their DNS infrastructure from unauthorized access and reconnaissance. As DNS architectures continue to evolve, the fundamental need for robust data synchronization mechanisms like zone transfers will persist, albeit often managed through more sophisticated, abstracted platforms. Mastering the intricacies of DNS zone transfers is not just about data replication; it’s about understanding and securing a foundational element of the internet itself.
