A proxy web browser, at its core, is a tool that allows you to browse the internet through an intermediary server. Instead of your computer directly connecting to a website, your request is first routed to a proxy server. This server then forwards the request to the website on your behalf, receives the website’s response, and sends it back to your computer. This fundamental mechanism of routing traffic through an external server opens up a range of functionalities and benefits, particularly in the realm of online privacy, security, and accessibility. Understanding how these browsers function is crucial for anyone looking to enhance their online experience, whether for personal use, research, or business operations.

The concept of a proxy server itself is not new; it has been a staple in network administration and cybersecurity for decades. However, the integration of this technology into user-friendly web browsing applications has democratized its use. Proxy web browsers abstract away the complexities of setting up and managing individual proxy connections, offering a seamless experience for the end-user. This accessibility has made proxy browsing a popular choice for individuals and organizations seeking to circumvent geographical restrictions, mask their IP addresses, and enhance their overall online anonymity.
The Mechanics of Proxy Web Browsing
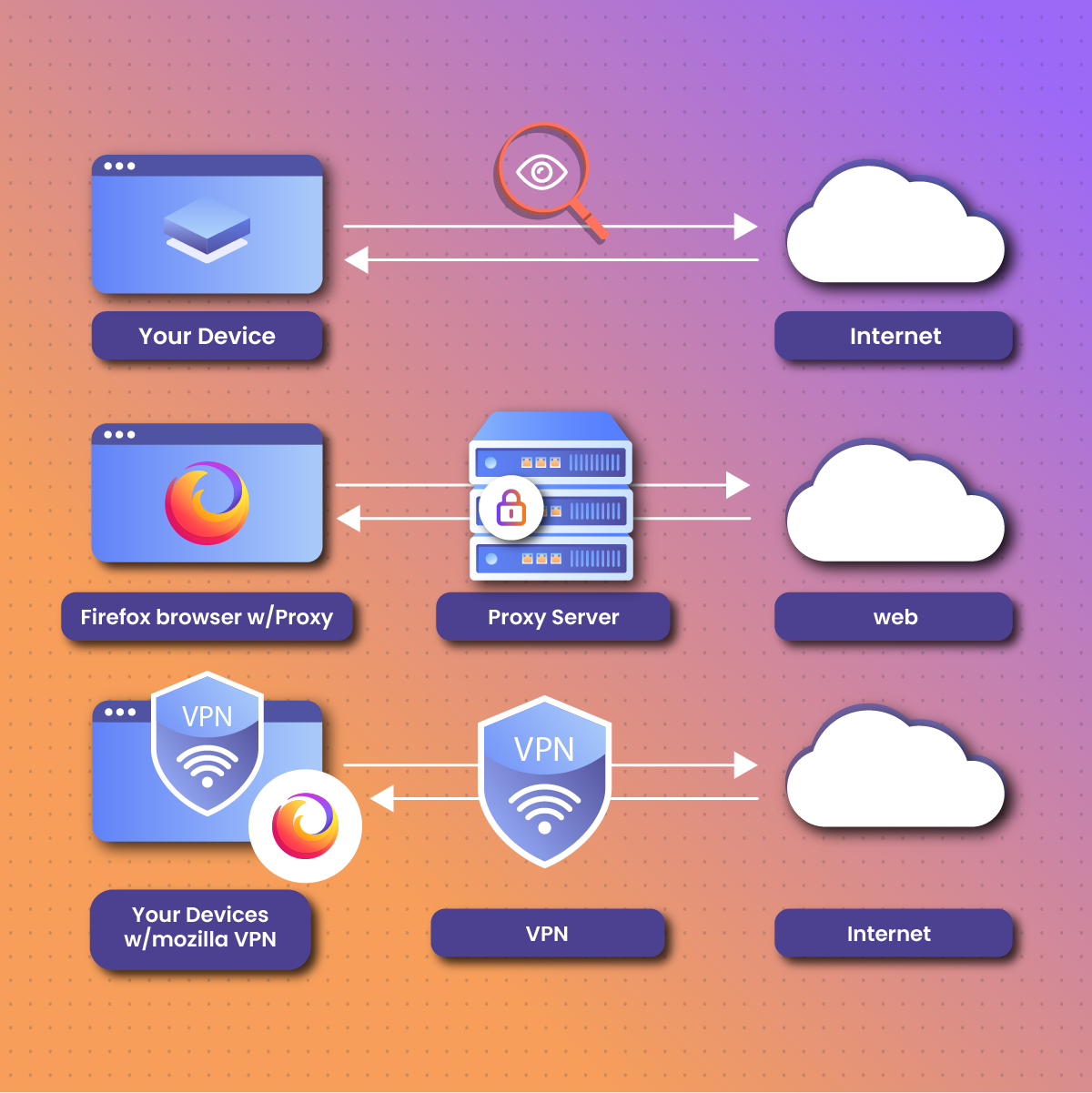
At its most basic, a proxy web browser operates by acting as a gateway between your device and the internet. When you type a URL into the address bar of a proxy browser, your request doesn’t go directly to the target website’s server. Instead, it’s first sent to the proxy server. The proxy server then makes the request to the website using its own IP address. The website’s server, unaware of your actual IP address, sends the data back to the proxy server. Finally, the proxy server transmits this data back to your browser.
Types of Proxy Servers and Their Implications
The effectiveness and functionality of a proxy web browser are heavily dependent on the type of proxy server it utilizes. Different proxy types offer varying levels of anonymity, performance, and features.
Forward Proxies
A forward proxy is the most common type encountered in proxy web browsers. It serves clients (your device) by forwarding requests from those clients to other servers on the internet. In essence, it acts on behalf of a group of clients. For a proxy web browser, this means the browser is configured to send all its outgoing traffic through a specific forward proxy server. This is the mechanism that allows you to appear as if you are browsing from the proxy server’s location, masking your true IP address and location.
Reverse Proxies
While less common for direct user browsing applications, reverse proxies are also a significant component of proxy technology. A reverse proxy sits in front of one or more web servers, intercepting requests from clients. Instead of acting on behalf of the client, it acts on behalf of the server. Websites use reverse proxies for load balancing, security, and caching. Understanding reverse proxies helps in appreciating the broader landscape of how proxy servers manage and protect internet traffic.
Anonymous Proxies
Anonymous proxies are designed to hide your IP address and make it difficult for websites to track your online activity. They come in different flavors:
-
High Anonymity Proxies (Elite Proxies): These proxies are the most effective at masking your identity. They not only hide your IP address but also do not identify themselves as proxies to the destination server. This makes it exceptionally difficult for websites to detect that you are using a proxy.
-
Anonymous Proxies: These proxies hide your IP address but may still identify themselves as proxies to the destination server. While they offer a good level of anonymity, sophisticated detection methods might still be able to identify their use.
-
Transparent Proxies: These proxies do not hide your IP address. They are often used by organizations for content filtering or caching purposes, without attempting to provide anonymity to the end-user. Proxy web browsers typically do not utilize transparent proxies if anonymity is a primary goal.
Residential Proxies
Residential proxies are IP addresses assigned to real residential internet service providers. When you use a proxy web browser that routes through a residential proxy, your traffic appears to originate from a genuine home internet connection. This makes them highly effective for tasks that require a legitimate online presence, such as web scraping or accessing geo-restricted content without triggering detection mechanisms.
Datacenter Proxies
Datacenter proxies use IP addresses owned by data centers. They are generally faster and cheaper than residential proxies but are also more easily detectable as proxies by websites. For general browsing and privacy, datacenter proxies can be sufficient, but for more sensitive tasks, residential proxies might be preferred.
The Role of the Proxy Server in Traffic Management
The proxy server is the central node in the proxy web browsing process. It performs several critical functions:
-
IP Masking: As previously discussed, the primary function is to replace your IP address with its own. This is fundamental for online anonymity and bypassing geo-restrictions.
-
Caching: Proxy servers can cache frequently accessed web pages. When multiple users request the same page, the proxy server can deliver the cached version instead of fetching it from the original server again. This can significantly speed up browsing and reduce bandwidth consumption.
-
Filtering and Security: Organizations often use proxy servers to filter out unwanted content or block access to malicious websites. They can also provide a layer of security by inspecting incoming and outgoing traffic for threats.
-
Content Modification: In some cases, proxy servers can modify web content, such as compressing images or translating languages, to improve performance or user experience.
Applications and Benefits of Proxy Web Browsers
The unique operational model of proxy web browsers lends itself to a variety of practical applications and offers several significant benefits to users. These range from enhanced privacy and security to the ability to access information without limitations.
Enhancing Online Privacy and Anonymity
One of the most compelling reasons to use a proxy web browser is to bolster online privacy. By routing your internet traffic through an intermediary server, your real IP address is concealed from the websites you visit. This makes it considerably harder for websites, advertisers, and even your Internet Service Provider (ISP) to track your online activities, build profiles based on your browsing habits, or identify your geographical location. For individuals concerned about digital footprints and pervasive tracking, a proxy browser offers a crucial layer of obfuscation.
Bypassing Geo-Restrictions and Censorship
Many online services and content providers restrict access based on a user’s geographical location. This can range from streaming services showing different content libraries in different countries to websites entirely blocking access from certain regions. A proxy web browser allows you to connect to a proxy server located in a region where the content is accessible. Your traffic then appears to originate from that location, enabling you to bypass these geo-restrictions and access a wider range of online information and entertainment. Similarly, in regions with strict internet censorship, proxy browsers can help users circumvent government-imposed blocks on websites and services.

Improving Security and Mitigating Risks
Proxy servers can act as a buffer between your device and the internet, offering a degree of security against certain online threats. By filtering requests and acting as an intermediary, they can help block access to malicious websites, prevent phishing attempts, and shield your network from direct exposure to potential attacks. Some proxy configurations can also scan incoming data for malware, providing an additional layer of protection. For organizations, this can be particularly important for protecting sensitive data and ensuring compliance with security policies.
Facilitating Web Scraping and Data Collection
For researchers, marketers, and developers, web scraping is a powerful technique for collecting data from websites. However, many websites have measures in place to detect and block automated scraping activities, often by monitoring IP addresses for suspicious patterns of requests. Using a proxy web browser with a pool of rotating IP addresses (like residential proxies) can make it appear as if the requests are coming from a diverse range of legitimate users, significantly reducing the likelihood of being blocked. This allows for more efficient and comprehensive data collection.
Testing and Development
Web developers and testers can utilize proxy web browsers for various purposes. They can simulate user traffic from different geographical locations to test geo-specific content delivery or regional performance. They can also inspect and modify network requests and responses to debug applications or analyze how websites function.
Considerations and Limitations
While proxy web browsers offer numerous advantages, it’s essential to be aware of their inherent limitations and potential drawbacks. Understanding these aspects will help users make informed decisions about their use and select the most appropriate proxy solutions for their needs.
Performance Degradation
The intermediary nature of proxy servers inevitably introduces an additional step in the data transfer process. This can lead to slower browsing speeds and increased latency compared to a direct connection. The extent of this performance degradation depends heavily on the quality and proximity of the proxy server, as well as the user’s own internet connection. High-traffic proxy servers or geographically distant servers can exacerbate these issues, making the browsing experience less fluid.
Security Risks with Untrusted Proxies
Not all proxy servers are created equal. Free proxy services, while appealing, often come with significant risks. These providers may log your browsing activity, inject ads into web pages, or even use your connection for malicious purposes. Furthermore, unencrypted proxy connections can expose your data to interception by the proxy provider or others on the network. It is paramount to use reputable proxy services that offer strong encryption (like HTTPS) and have clear privacy policies.
Incompatibility with Certain Applications and Services
Some online services, particularly those that rely heavily on real-time data or robust security protocols (like online banking or certain streaming platforms), may detect and block traffic originating from known proxy servers. This is a security measure to prevent fraudulent activity and unauthorized access. Consequently, users might find themselves unable to access certain content or functionalities when using a proxy web browser.
Potential for Logging and Data Collection
While the goal of using a proxy is often to enhance privacy, the proxy server itself has the potential to log your activity. If you are using a proxy for anonymity, it is crucial to choose a provider that explicitly states a “no-logs” policy and has a track record of upholding it. The trust you place in the proxy provider is as important as the technology itself.
Legal and Ethical Implications
The use of proxy web browsers to bypass geo-restrictions or access copyrighted material can have legal and ethical implications depending on the jurisdiction and the specific content being accessed. While bypassing geo-restrictions is often a grey area, downloading or distributing copyrighted material without authorization is illegal in most countries. Users should be aware of and adhere to the laws in their respective regions.
Choosing the Right Proxy Web Browser
Selecting the appropriate proxy web browser hinges on individual needs and priorities. The market offers a spectrum of solutions, from dedicated browser applications to browser extensions that integrate proxy functionality. Understanding the distinctions and features of various options is key to making an informed choice.
Dedicated Proxy Browsers
Some applications are built from the ground up as proxy browsers. These often provide a more integrated and streamlined experience, with built-in proxy settings and management tools. They might offer features such as automatic proxy switching, advanced security options, and specialized modes for different browsing scenarios. Examples range from privacy-focused browsers that have proxy capabilities to specialized tools for web scraping.
Browser Extensions and Plugins
Another common approach is to use browser extensions or plugins that enable proxy functionality. These are typically easier to install and manage, often allowing users to toggle proxy settings on and off with a single click. Popular extensions can connect to user-provided proxy servers or offer access to a network of proxy servers managed by the extension provider. While convenient, the scope of their proxy integration might be limited compared to dedicated browsers, sometimes only proxying traffic from within the browser itself.
Factors to Consider When Selecting a Proxy Solution
When evaluating proxy web browser options, several critical factors should guide your decision:
-
Privacy Policy and Logging: Thoroughly review the provider’s privacy policy. Look for explicit statements about data logging, data retention, and how your information is used. A strict no-logs policy is ideal for privacy-conscious users.
-
Security Features: Ensure the proxy solution offers robust security, including HTTPS encryption for all traffic. Some providers may offer additional security features like ad-blocking or malware protection.
-
Performance and Reliability: Consider the speed and stability of the proxy servers. User reviews and independent testing can provide insights into the reliability and performance of different services.
-
Server Locations: If bypassing geo-restrictions is a primary goal, ensure the provider offers proxy servers in the geographical locations you need access to. A wide distribution of servers can also improve performance by allowing you to connect to a server closer to your actual location.
-
Cost: Proxy services range from free to paid subscriptions. Free proxies often come with compromises in terms of speed, reliability, and privacy. Paid services generally offer better performance, security, and a wider selection of servers.
-
Ease of Use: The interface and user experience of the proxy browser or extension should be intuitive and easy to navigate, especially for users who are not technically inclined.
By carefully considering these aspects, users can select a proxy web browser that effectively meets their needs for privacy, security, access, and overall browsing experience.
