The burgeoning field of uncrewed aerial vehicles (UAVs), or drones, stands as a testament to relentless technological innovation. From sophisticated autonomous navigation to high-definition aerial imaging and complex data acquisition, drones are reshaping industries and unlocking unprecedented capabilities. At the heart of this revolution lies robust and reliable connectivity. Just as home networks require seamless device integration, advanced drone operations necessitate intuitive yet secure methods for pairing drones with ground control stations, peripheral sensors, and overarching enterprise networks. This article delves into the critical aspects of simplified and secure network pairing for drones, drawing inspiration from established networking paradigms like Wi-Fi Protected Setup (WPS) to envision future-proof connectivity solutions within the realm of drone Tech & Innovation.
The Imperative for Seamless Drone Connectivity in Tech & Innovation
In the rapidly evolving drone ecosystem, the ability to quickly and securely establish communication links is not merely a convenience but an operational necessity. As drones move beyond recreational use into mission-critical applications—such as infrastructure inspection, search and rescue, precision agriculture, and logistics—the complexity of their deployments grows exponentially. Managing fleets, processing vast amounts of data, and ensuring real-time command and control all hinge on superior network integration.
Bridging the Gap: The Need for Intuitive Drone Networking
Traditional network setup can be cumbersome, requiring manual configuration of IP addresses, subnets, and security protocols. For drone operators, especially those deploying multiple units or managing dynamic flight environments, such complexities introduce delays, increase the potential for human error, and detract from mission focus. The ideal scenario involves a streamlined process that allows drones to “just connect,” enabling immediate operational readiness. This demand drives innovation towards systems that simplify network onboarding without compromising performance or security. We are seeing a push for intuitive interfaces, automated discovery protocols, and plug-and-play solutions that minimize manual intervention, allowing operators to concentrate on flight execution and data acquisition.
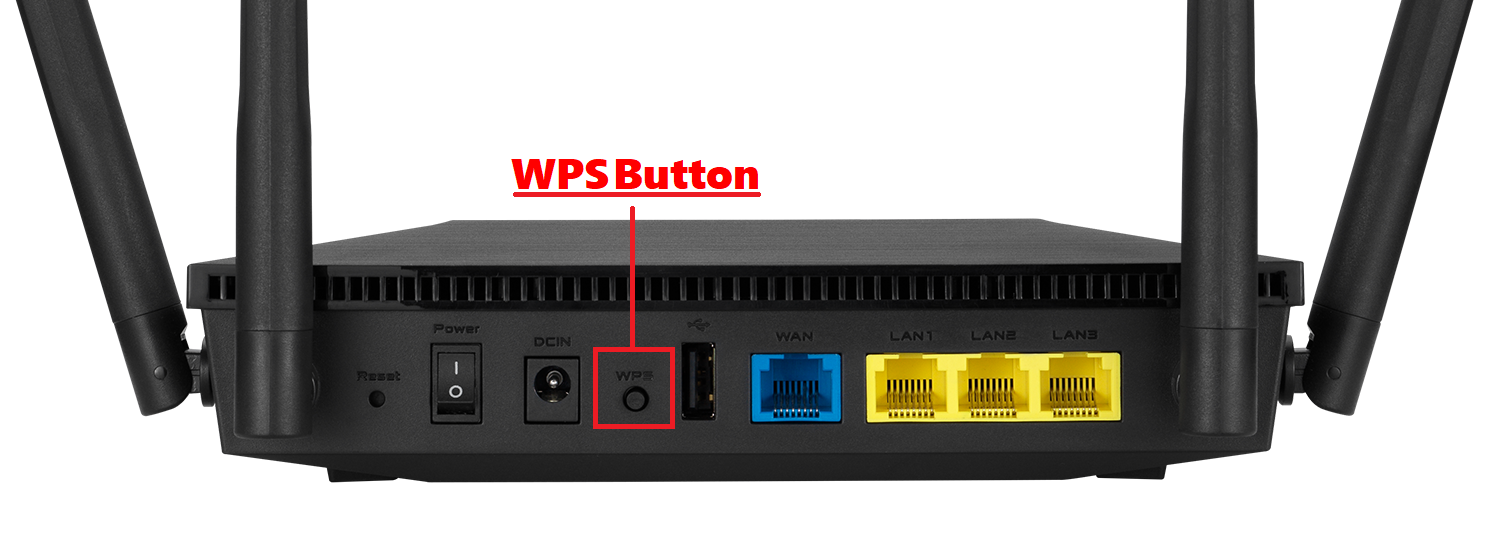
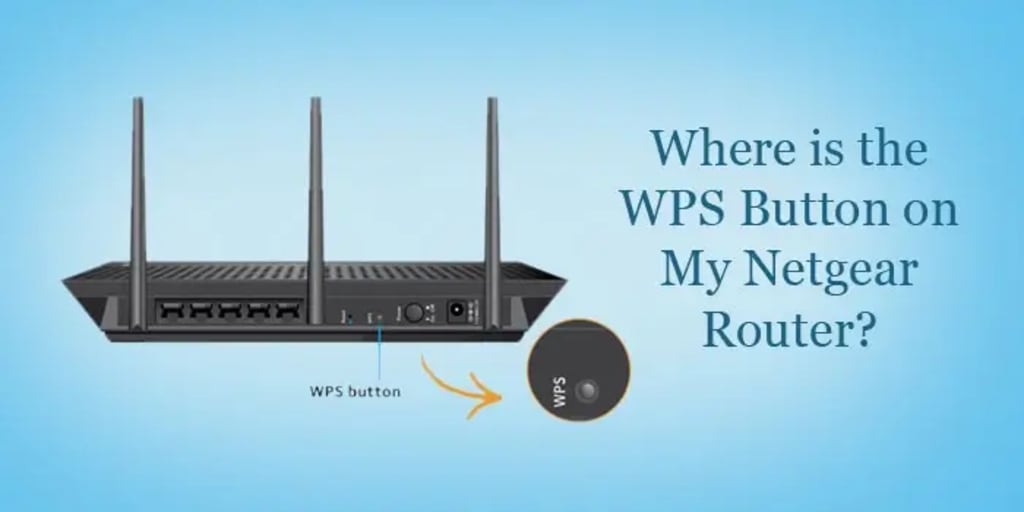
Drawing Parallels: Understanding “Protected Setup” in a Drone Context
To understand the future of drone networking, it’s useful to examine concepts like Wi-Fi Protected Setup (WPS). WPS was designed to simplify the process of connecting devices to a Wi-Fi network, primarily for consumer routers. It offered methods like a “push-button connect” (PBC) or a PIN-based entry to bypass manual password input. While WPS itself has well-documented security vulnerabilities in a general networking context, its core intent—facilitating easy, protected setup—serves as a valuable analogy for desired functionality in drone systems. In the context of drone Tech & Innovation, a “Protected Setup” equivalent would signify a mechanism that allows drones, their controllers, or ground stations to establish secure communication links with minimal user effort, whether for initial pairing, joining a local area network for data offload, or integrating into a wider enterprise infrastructure. The goal is to distill the convenience of WPS while rigorously addressing its security shortcomings in a high-stakes drone environment.
Unpacking Simplified Drone Pairing Mechanisms
Translating the concept of a “protected setup” into the drone sphere involves exploring analogous mechanisms for establishing connectivity. These mechanisms aim to reduce complexity, accelerate deployment, and ensure operational efficiency in diverse drone applications.
One-Touch Pairing: A New Paradigm for Ground Station and Fleet Connectivity
Inspired by the WPS push-button connect (PBC) method, one-touch pairing for drones would revolutionize initial setup and rapid deployment. Imagine a scenario where an operator presses a physical or virtual button on their ground control station (GCS) and simultaneously initiates a pairing sequence on a drone (or a fleet of drones). This action would trigger an automated, secure handshake process, quickly establishing a dedicated communication link for command, control, and data transmission. This approach is particularly advantageous for emergency response scenarios, rapid asset deployment, or in environments where time is of the essence. Innovations in this area leverage short-range radio frequencies, NFC, or secure Bluetooth Low Energy (BLE) channels for initial secure key exchange, followed by establishing a robust Wi-Fi or cellular link. Such systems prioritize simplicity and speed while embedding strong encryption from the outset, moving beyond the inherent vulnerabilities of traditional WPS.

PIN-Based Authentication: Exploring its Application and Risks for Drone Systems
The WPS PIN method, requiring a numerical code to join a network, also has a conceptual counterpart in drone systems. This could manifest as a short, unique code displayed on a drone’s status screen or etched onto its casing, which an operator enters into their GCS or an authorized network portal. For specific enterprise drone applications, such as integrating a new drone into a secure corporate network, a PIN-based authentication offers an additional layer of verification beyond mere physical proximity. However, lessons from WPS are paramount: a short, static PIN is highly susceptible to brute-force attacks. Therefore, any PIN-based system for drones must incorporate dynamic, time-limited PINs, multi-factor authentication, or cryptographic challenge-response mechanisms to prevent unauthorized access. The emphasis must shift from simple PINs to secure and ephemeral authentication codes that strengthen, rather than weaken, the drone’s security posture.
Beyond Direct Connection: Integrating Drones into Enterprise Networks
Modern drone operations often require more than just a direct link between a drone and its controller. Enterprise-grade deployments demand seamless integration into existing IT infrastructure for data management, software updates, compliance, and fleet oversight. This includes connecting drones to local area networks (LANs) for high-speed data offloading post-mission, enabling over-the-air (OTA) firmware updates, or even providing network access for specialized payloads. A “drone protected setup” concept here would facilitate secure, automated provisioning of drones onto a corporate Wi-Fi or wired network, leveraging enterprise-grade authentication standards like 802.1X, pre-shared keys (PSK) with strong encryption (WPA3), or certificate-based authentication. This moves beyond consumer-grade simplicity to robust, scalable, and IT-compliant network integration.
Advantages of Streamlined Drone Network Integration
The drive towards simplified and secure drone network pairing is fueled by tangible benefits that significantly enhance operational efficiency, data utility, and the overall scalability of drone programs.
Operational Efficiency and Rapid Deployment
The most immediate benefit of streamlined connectivity is the drastic reduction in setup time. For emergency services, rapid deployment of surveillance or assessment drones can be critical. For industrial inspections, minimizing setup means more time in the air gathering valuable data, translating directly to cost savings and increased productivity. Imagine a scenario where a fleet of drones can be unboxed, powered on, and automatically connected to a pre-configured ground station or cloud service within minutes, ready for mission assignment. This ‘zero-touch’ provisioning is a cornerstone of future drone operations.
Enhanced Data Offloading and Real-time Telemetry
Drones generate immense volumes of data—4K video, lidar scans, multispectral imagery, and telemetry logs. Efficiently offloading this data is crucial. Simplified network pairing mechanisms facilitate quick connection to high-bandwidth networks (e.g., enterprise Wi-Fi 6 networks) for rapid data transfer, reducing post-mission processing times. Furthermore, secure, low-latency links enable real-time telemetry, allowing operators to monitor drone health, sensor readings, and flight parameters instantaneously, which is vital for safe and effective operations, particularly in Beyond Visual Line of Sight (BVLOS) scenarios.
Facilitating Autonomous Fleet Management
The vision of autonomous drone fleets operating cooperatively requires sophisticated network management. Simplified pairing and robust network integration are essential for:
- Centralized Command: A central ground station or cloud platform can manage mission planning, task assignment, and real-time adjustments for multiple drones.
- Inter-Drone Communication: Enabling drones to communicate directly with each other (mesh networking) for collaborative tasks like swarm intelligence or coordinated mapping.
- Dynamic Load Balancing: Optimizing network resources across a fleet to ensure critical data is prioritized and transmitted effectively.
- Automated Updates and Diagnostics: Pushing firmware updates and running diagnostics remotely, ensuring all drones in a fleet are running optimal, secure software.
Navigating the Security Landscape: Risks and Best Practices
While simplified network pairing offers undeniable advantages, it inherently carries security implications that must be meticulously addressed. The convenience of easy connections must never come at the expense of robust security, especially in sensitive drone applications.
The Vulnerabilities of Overly Simplified Pairing
The original WPS design, particularly its PIN method, demonstrated how convenience could introduce severe security flaws. A short, numeric PIN is easily brute-forced, compromising the entire network. In a drone context, similar overly simplified pairing mechanisms could lead to:
- Unauthorized Access: Malicious actors gaining control of a drone, diverting it, or accessing sensitive data.
- Data Interception: Eavesdropping on command and control links or data streams.
- Denial of Service: Jamming communication, preventing legitimate control, or forcing a drone to land.
- Spoofing: Impersonating a legitimate ground station or drone to inject false commands or data.
Any drone “protected setup” must learn from these lessons, avoiding static, short, and easily guessable authentication factors.
Mitigating Threats: Robust Encryption and Authentication Protocols
To counter these threats, next-generation drone pairing systems must integrate enterprise-grade security protocols from their inception. Key mitigation strategies include:
- Strong Encryption: Utilizing advanced encryption standards like AES-256 for all data in transit, including command and control signals and telemetry.
- Mutual Authentication: Ensuring both the drone and the ground station (or network) mutually verify each other’s identity using digital certificates or secure key exchange protocols. This prevents spoofing.
- Dynamic Authentication Tokens: Employing one-time passwords (OTP), challenge-response mechanisms, or dynamic, time-limited keys instead of static PINs.
- Multi-Factor Authentication (MFA): Requiring more than one form of verification (e.g., something you know and something you have) for critical pairing or access events.
- Secure Boot and Firmware Integrity: Ensuring that only authenticated and untampered firmware can run on the drone, preventing malicious code injection during or after pairing.
Best Practices for Secure Drone Network Operations
Beyond technical protocols, operational best practices are crucial for maintaining a secure drone ecosystem:
- Network Segmentation: Isolating drone networks from general corporate networks to limit the blast radius of any potential breach.
- Regular Audits and Penetration Testing: Proactively identifying and patching vulnerabilities in drone hardware, software, and communication protocols.
- Least Privilege Principle: Ensuring drones and ground stations only have the necessary permissions to perform their designated tasks.
- Secure Key Management: Implementing robust systems for generating, storing, distributing, and revoking cryptographic keys.
- Employee Training: Educating operators on security risks, secure handling of drones and data, and reporting suspicious activities.
- Geofencing and Flight Restrictions: Implementing software-based boundaries to prevent drones from entering restricted airspace or unauthorized zones.
Evolving Alternatives and Future Directions in Drone Connectivity
The quest for a balance between ease of use and uncompromising security continues to drive innovation in drone connectivity. As technology advances, new alternatives and future directions promise even more robust and adaptable solutions.
Advanced Pairing Technologies: QR Codes, NFC, and Beyond
Moving past traditional PINs and buttons, advanced pairing mechanisms are emerging:
- QR Code Pairing: A drone or ground station displays a unique, cryptographically signed QR code, which another device scans to initiate a secure pairing. This leverages visual verification and simplifies key exchange.
- NFC (Near Field Communication): Tapping two devices together for an instantaneous, secure setup of a primary communication link, ideal for close-proximity provisioning.
- Ultra-Wideband (UWB): Offering highly secure, precise, short-range communication that can facilitate secure key exchange for pairing with extreme accuracy and resistance to jamming.
These methods leverage the unique strengths of various short-range wireless technologies to create intuitive yet highly secure initial connections, which can then be escalated to longer-range, high-bandwidth links.
Cloud-Based Fleet Management and Secure VPN Tunnels
For large-scale enterprise drone operations, cloud-based fleet management platforms are becoming indispensable. These platforms provide centralized control, mission planning, data storage, and analytics. Securely integrating drones into these cloud ecosystems often involves:
- Secure VPN Tunnels: Establishing encrypted virtual private network connections from the drone (or its ground station) directly to the cloud platform, ensuring all data and command traffic is protected over public networks.
- Device Certificates: Each drone possessing a unique digital certificate for authentication with the cloud platform, ensuring only authorized devices can connect.
- Zero-Trust Architectures: Implementing a security model where no device, user, or application is trusted by default, requiring verification at every access point.
The Future of Drone Connectivity: Mesh Networks and 5G Integration
The horizon for drone connectivity includes even more transformative technologies:
- Self-Healing Mesh Networks: Drones forming ad-hoc, self-organizing mesh networks where each drone can act as a repeater, extending range and enhancing resilience in complex environments or over vast areas. This creates a highly robust and decentralized communication fabric.
- 5G and Beyond: The advent of 5G offers unprecedented bandwidth, ultra-low latency, and massive connectivity, ideal for real-time BVLOS operations, high-volume data streaming, and enabling fully autonomous drone swarms. Future G (6G and beyond) technologies will further enhance these capabilities, supporting ubiquitous drone presence and hyper-connectivity. These cellular technologies offer inherent security advantages through operator-managed infrastructure, but robust end-to-end encryption from the drone to the application layer will remain paramount.
In conclusion, while “what is a WPS on a router” speaks to consumer-level networking, its conceptual framework of simplified, protected setup is a powerful analogy for the advanced challenges in drone Tech & Innovation. The future of drone operations hinges on developing connectivity solutions that offer the utmost in ease of use for rapid deployment, coupled with impenetrable security measures to safeguard against threats. By embracing lessons from the past and integrating cutting-edge technologies, the industry can ensure that drones continue to push the boundaries of what’s possible, securely and reliably.
