In the vast and intricate landscape of digital technology, where data traverses networks at lightning speed and information integrity is paramount, foundational concepts often underpin the most complex systems. Among these, the Message-Digest Algorithm 5, universally known as MD5, stands as a crucial, albeit now historically nuanced, pillar. Far from being a mere technical acronym, understanding MD5 is essential for anyone delving into data integrity, cybersecurity’s evolution, and the core mechanics of digital verification. It represents a specific type of cryptographic hash function, an algorithm designed to take an input (or ‘message’) of any length and produce a fixed-size output, known as a ‘hash value’ or ‘message digest’. This “digital fingerprint” concept, central to MD5, has profoundly influenced how we verify data, secure communications, and understand the vulnerabilities inherent in digital information.
At its core, MD5 was engineered to ensure that data remains unchanged during transmission or storage. Imagine sending a critical document over the internet; how can the recipient be absolutely certain that the file they receive is precisely the same one you sent, unaltered by accidental corruption or malicious tampering? MD5 offered a robust mechanism for this verification. By generating a unique, fixed-length string of characters for the original data and then comparing it to a hash generated from the received data, any discrepancy immediately signals a problem. While its security implications have significantly evolved, rendering it unsuitable for many modern cryptographic applications, MD5 remains an important subject for understanding the trajectory of information security and the principles that govern data integrity in our increasingly digital world. This article delves into the mechanics of MD5, its historical role, its current limitations, and its enduring relevance within the broader sphere of tech and innovation.
The Foundational Concept: Hashing and Digital Fingerprints
To truly grasp what an MD5 is, one must first understand the fundamental concept of a hash function. In computer science and cryptography, a hash function is an algorithm that maps data of arbitrary size to a fixed-size bit array. This process, known as “hashing,” produces a hash value, hash code, digest, or simply a hash. It’s akin to creating a unique, compact summary or a digital fingerprint for a larger piece of data.
Digital Fingerprints for Data
The analogy of a fingerprint is particularly apt. Just as every human has a unique set of ridges on their fingers that can identify them, a well-designed hash function aims to produce a unique output for every unique input. Even a minuscule change in the input data – a single altered character, a swapped byte, or an added space – should ideally result in a drastically different hash value. This property is known as the “avalanche effect,” and it’s critical for the integrity-checking capabilities of hash functions. If the hash values for two seemingly identical files differ, you can be certain that the files are not identical. This forms the basis for file integrity checks, ensuring that downloaded software hasn’t been corrupted or maliciously altered, or that a stored document hasn’t suffered data degradation.
The One-Way Street of Hashing
Another crucial characteristic of cryptographic hash functions, like MD5, is their one-way nature. This means it’s computationally infeasible to reverse the process – to reconstruct the original input data from its hash value alone. While generating a hash from data is quick and straightforward, working backward from the hash to the original data is designed to be practically impossible within a reasonable timeframe, even with immense computing power. This “preimage resistance” is fundamental for applications like password storage, where storing hashes instead of plain-text passwords enhances security. If a database is compromised, attackers only get the hashes, making it extremely difficult for them to recover the actual passwords. While MD5’s one-way property has been compromised in specific ways (collision attacks, which we’ll discuss later), the principle of one-way hashing remains a cornerstone of modern cybersecurity.
Deconstructing MD5: How the Algorithm Works
MD5 was developed by Ronald Rivest in 1991, succeeding earlier algorithms like MD4. It was designed to be faster and more secure than its predecessors, and for a time, it served its purpose admirably. The algorithm takes an input message of any length and processes it in 512-bit blocks. The output is a 128-bit (16-byte) hash value, typically represented as a 32-character hexadecimal number.
Input, Processing, and Fixed-Length Output
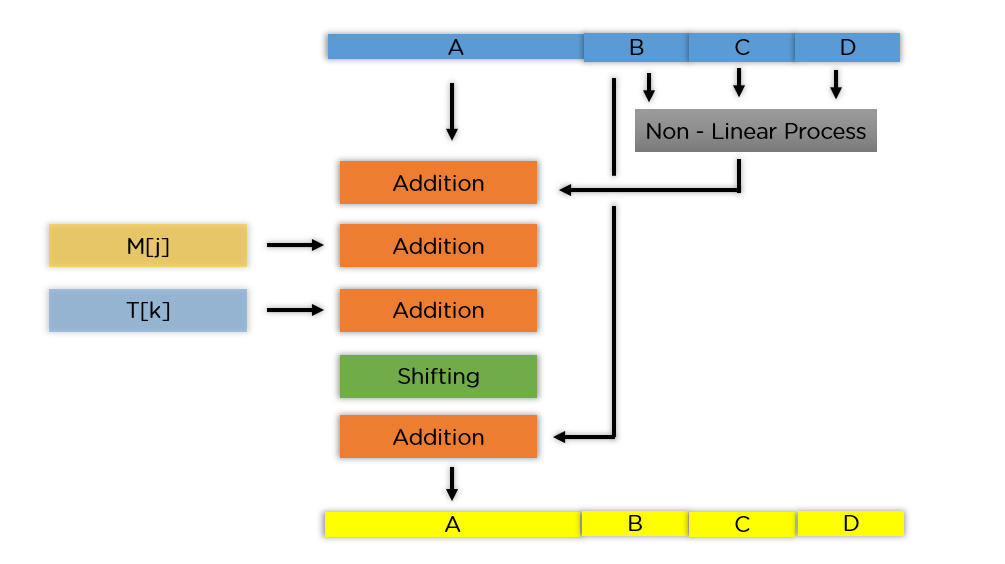
The process begins by padding the input message so that its length (in bits) is congruent to 448 modulo 512. This ensures that the message, plus an additional 64-bit field representing the original length, fills a complete 512-bit block. Once padded, the message is processed in these 512-bit chunks. Each block undergoes a series of complex logical operations, bitwise manipulations, and additions with a set of initialization vectors (IVs) and round constants. These operations are structured into four main rounds, each performing 16 operations, for a total of 64 distinct steps.
The Steps of the MD5 Algorithm
Within each round, the algorithm uses a different non-linear function (F, G, H, I), which helps mix the bits and ensure the avalanche effect. These functions, combined with left bitwise rotations and additions of specific constants and parts of the previous round’s output, contribute to the complexity and apparent randomness of the final hash. The output of one block’s processing feeds into the next, iteratively updating four 32-bit registers. After all message blocks have been processed, the concatenation of the final values in these four registers forms the 128-bit MD5 hash.
The sheer complexity of these operations, while seemingly arbitrary, is what makes the MD5 hash difficult to reverse engineer and ensures that even a tiny change in the input cascades through the calculations to produce a dramatically different output. For its time, this algorithmic design was a significant achievement in ensuring data integrity and providing a reliable digital fingerprint.
Practical Applications and Historical Significance
For many years, MD5 served as a workhorse in various digital applications, becoming an integral part of how we handled data verification and security in the early days of the internet. Its widespread adoption solidified its place in the history of tech and innovation.
Ensuring File Integrity and Downloads
Perhaps the most common and enduring application of MD5 has been in verifying file integrity. When you download a software package, an operating system image, or any critical file, the provider often publishes its MD5 checksum alongside the download link. After downloading, users can run an MD5 hash calculation on their local copy of the file and compare it to the published hash. If the hashes match, it confirms that the file was downloaded completely and without any corruption or unauthorized modification during transit. This simple yet effective mechanism has prevented countless issues arising from incomplete downloads or compromised distribution channels, playing a vital role in the reliability of software and data distribution.
Password Storage (and its Pitfalls)
Historically, MD5 was also widely used for storing user passwords. Instead of storing passwords in plain text, which would be a severe security vulnerability if a database were breached, systems would store the MD5 hash of each password. When a user attempted to log in, the system would hash their entered password and compare it to the stored hash. If they matched, access was granted. This method leveraged the one-way property of MD5, preventing attackers who gained access to the database from immediately knowing the users’ passwords. However, this application proved to be one of MD5’s most significant weaknesses over time. Due to its speed and relatively short hash output, techniques like “rainbow tables” (precomputed tables of hashes for common passwords) and brute-force attacks became increasingly effective at reversing MD5 hashes for weak passwords, leading to compromises. This highlighted the critical need for stronger hashing algorithms and proper “salting” techniques (adding a random string to a password before hashing) to enhance security.
Early Digital Signatures and Authentication
In its early years, MD5 also played a role in digital signature schemes, where a hash of a document would be encrypted with a private key to create a signature. The recipient could then decrypt the signature with the public key and compare the resulting hash to one they independently generated from the document, thus verifying both the authenticity and integrity of the sender and the document. While MD5’s vulnerabilities eventually led to its deprecation for this purpose, its use in these early systems laid the groundwork for the more robust digital signature mechanisms we rely on today, illustrating its importance in the foundational development of secure digital communication.
The Evolution of Security and MD5’s Vulnerabilities
Despite its historical utility, the landscape of cryptography and cybersecurity is one of constant evolution. As computing power advanced and cryptographic analysis matured, vulnerabilities in MD5 began to emerge, ultimately leading to its deprecation for security-sensitive applications.
Understanding Collision Attacks
The most significant vulnerability of MD5 is its susceptibility to “collision attacks.” A collision occurs when two different inputs produce the exact same hash output. While, in theory, finding a collision for any hash function is possible (due to the pigeonhole principle – more possible inputs than fixed-size outputs), a strong cryptographic hash function should make finding such collisions computationally infeasible. For MD5, however, researchers demonstrated practical methods to find collisions. In 2004, a significant breakthrough showed how to find MD5 collisions relatively easily. This was a critical blow to MD5’s cryptographic integrity. If two different documents or pieces of code could generate the same MD5 hash, then a malicious actor could create a fraudulent document with the same hash as a legitimate one. This could lead to a severe security breach, for instance, by replacing a legitimate software update with a malicious one that shares the same MD5 checksum, making it appear authentic to verification tools.
Why MD5 is Deprecated for Security
The ease of generating MD5 collisions means that it can no longer be trusted for applications where data authenticity or integrity against malicious tampering is paramount. This includes:
- Digital Signatures: If an attacker can create two documents with the same hash, they can trick someone into digitally signing a legitimate document, then replace it with a malicious one that has the same signature.
- Password Hashing: While MD5 hashes are still one-way, the existence of collisions, combined with the effectiveness of rainbow tables and brute-force attacks, means that MD5 is no longer considered secure for password storage, especially without robust salting.
- Code Integrity Checks: For verifying the integrity of software or firmware, MD5 is risky because a malicious entity could inject malware while preserving the original hash.
Organizations and security standards bodies universally recommend against using MD5 for any new security-related applications and advocate for replacing it in existing systems where possible. Its deprecation marks a crucial lesson in the dynamic nature of cybersecurity, where algorithms once deemed robust can become vulnerable with advancements in cryptanalysis and computational power.
Modern Alternatives: SHA-256 and Beyond
The vulnerabilities of MD5 paved the way for the adoption of stronger hash functions. The Secure Hash Algorithm (SHA) family, particularly SHA-256 and SHA-512, are now the industry standard for cryptographic hashing. These algorithms produce longer hash outputs (256 bits and 512 bits, respectively), making collision attacks significantly more difficult to achieve. They are also designed with more complex internal structures that resist known attack techniques. For password storage, specifically, specialized hashing algorithms like bcrypt, scrypt, and Argon2 are recommended because they are “slow by design” – intentionally computationally intensive – to deter brute-force and rainbow table attacks, even with powerful hardware. The transition from MD5 to these more robust alternatives highlights an ongoing commitment within tech and innovation to continually strengthen our digital defenses against emerging threats.
MD5’s Enduring Niche and Future Relevance
Despite its cryptographic weaknesses, MD5 is not entirely obsolete. It continues to hold specific niches where its speed and historical presence still offer utility, primarily in non-security-critical contexts. Furthermore, its story serves as an invaluable educational tool within the realm of cybersecurity and computer science.
Non-Cryptographic Uses
For applications where the primary concern is accidental data corruption rather than malicious tampering, MD5 can still be a viable option. For instance:
- Data Deduplication: In large storage systems or backup solutions, MD5 can be used to quickly identify identical files or blocks of data, preventing redundant storage. If two files have the same MD5 hash, there’s a very high probability they are identical, allowing for efficient deduplication. While a collision could theoretically lead to misidentification, the risk is often acceptable for non-critical data.
- Checksums for Non-Sensitive Data: For checking the integrity of non-sensitive datasets in internal systems, where an attacker has no motivation to craft a collision, MD5 remains a fast and efficient option.
- Identifying Unique Data Records: In database management or large data processing tasks, MD5 can be employed to generate unique identifiers for records, making it easier to track and manage data, provided the uniqueness guarantee is not for security-critical functions.
In these scenarios, the objective is typically to catch random errors or simple duplicates, where the computational overhead of stronger algorithms might be unnecessary, and the likelihood of a practical collision attack being relevant is negligible.
A Foundational Concept in Cybersecurity Education
Perhaps MD5’s most significant enduring relevance is its role as an educational case study. It perfectly illustrates several critical principles in cybersecurity:
- The Importance of Algorithmic Strength: MD5’s journey from robust to vulnerable highlights that cryptographic algorithms are not static solutions but require continuous evaluation and eventual replacement.
- The Nature of Cryptographic Attacks: Understanding collision attacks on MD5 provides a concrete example of how cryptographic primitives can be broken and the implications for real-world security.
- The Evolution of Security Best Practices: MD5’s deprecation underscores the importance of staying current with recommended security protocols and migrating to stronger alternatives as they become available.
- The Balance of Performance and Security: It demonstrates the trade-offs involved in designing cryptographic systems, where factors like speed and computational cost must be weighed against the level of security required.
For students and professionals in tech and innovation, studying MD5 is not just about learning a defunct algorithm; it’s about gaining profound insights into the foundational principles of data integrity, the constant arms race in cybersecurity, and the critical thinking required to design and implement secure digital systems. MD5, therefore, remains a vital part of the curriculum, serving as a powerful reminder of how technology evolves and the perpetual need for vigilance in protecting our digital world.
