In the digital age, cybersecurity is not just a matter of personal privacy; it is a matter of national security and corporate integrity. At the heart of federal cybercrime prosecution in the United States is the Computer Fraud and Abuse Act (CFAA).
Whether you are a business owner, an IT professional, or a curious internet user, understanding this law is essential for navigating the legal landscape of the internet.
What is the Computer Fraud and Abuse Act (CFAA)?
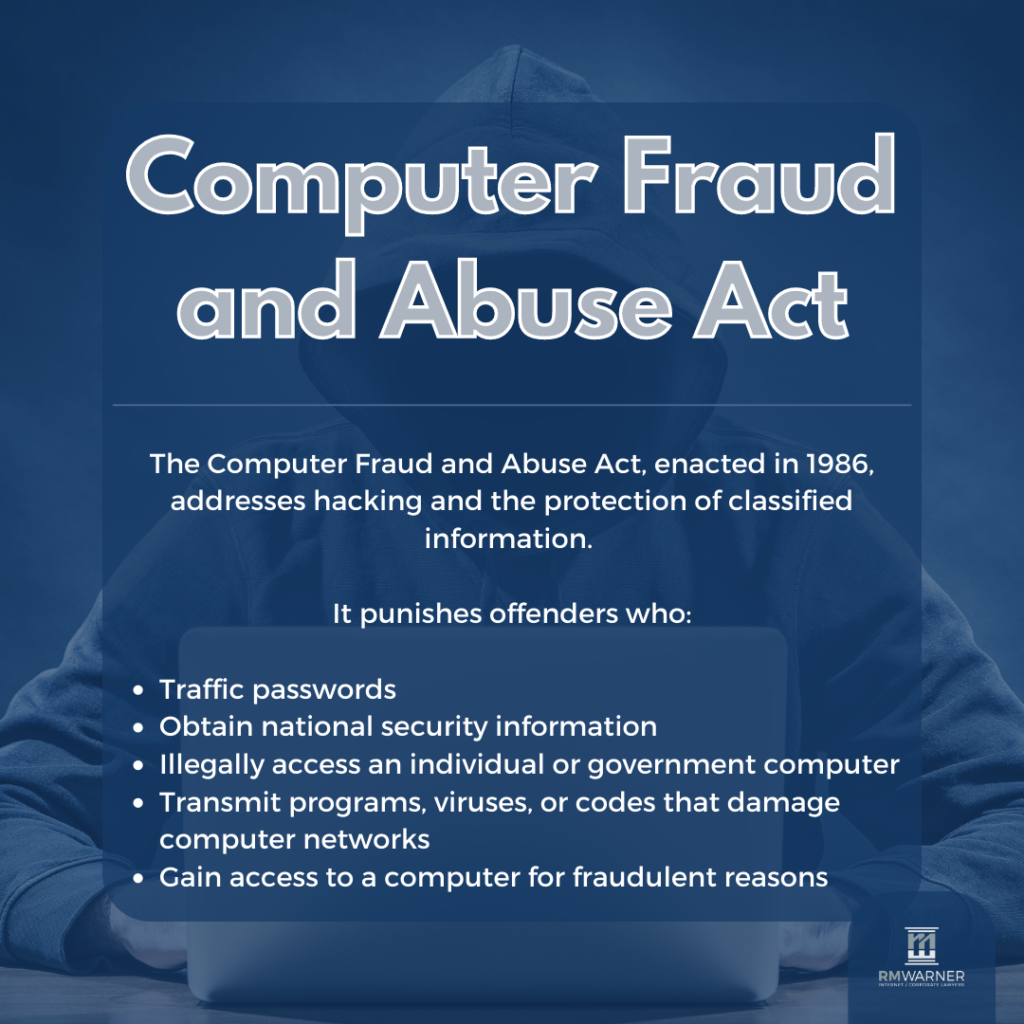
The Computer Fraud and Abuse Act, codified as 18 U.S.C. § 1030, is the primary federal statute used to prosecute hacking and unauthorized access to computers. Enacted in 1986, it was designed as an amendment to existing mail and wire fraud laws to address the growing concern of “computer crimes.”
Initially, the law was intended to protect federal government computers and financial institution systems. However, through several amendments, its scope has expanded to cover almost any computer connected to the internet.

The History: From Hollywood to Legislation
Interestingly, the CFAA was prompted in part by pop culture. Following the release of the 1983 film WarGames, in which a young hacker nearly triggers a nuclear war, Congress became concerned about the vulnerability of government systems. This led to the creation of the CFAA to provide a legal framework for punishing digital intruders.
Key Provisions: What Does the CFAA Prohibit?
The CFAA outlines several distinct types of prohibited conduct. The most common violations involve:
- Unauthorized Access: Accessing a computer without any permission at all (classic “hacking”).
- Exceeding Authorized Access: Having permission to access a computer but using that access to obtain or alter information that the user is not entitled to see or use.
- Computer Espionage: Accessing a computer to obtain restricted government information.
- Transmitting Threats/Extortion: Using a computer to transmit threats to damage a system or to extort money (often seen in ransomware cases).
- Trafficking in Passwords: Selling or sharing login credentials that allow unauthorized access to computers.
What is a “Protected Computer”?
In the early days, a “protected computer” meant one used by the government or a bank. Today, the definition is much broader. Under the CFAA, a protected computer includes any computer used in or affecting interstate or foreign commerce. Effectively, this includes every smartphone, tablet, laptop, and server connected to the internet.
The “Van Buren” Case: A Major Legal Shift
For years, the CFAA was criticized for being overly broad. Some prosecutors used it to charge people for simply violating a website’s “Terms of Service” or an employer’s computer use policy.
However, in 2021, the U.S. Supreme Court ruled in Van Buren v. United States. The Court narrowed the definition of “exceeding authorized access.” It ruled that if you have permission to access a specific folder or database, you cannot be charged under the CFAA for having an “improper motive” for taking that data. You are only in violation if you access areas of the computer that you were never allowed to enter.
Penalties for Violating the CFAA
The CFAA is both a criminal and a civil statute. This means:
- Criminal Penalties: Individuals can face fines and prison sentences ranging from one year (for first-time misdemeanors) to 20 years (for serious or repeat offenses involving national security).
- Civil Liability: Private companies or individuals can sue hackers for damages if the unauthorized access caused at least $5,000 in loss during a one-year period.
Why the CFAA Matters Today
As data breaches and ransomware attacks become more frequent, the CFAA remains the government’s “big stick” for punishing cybercriminals. For businesses, it provides a legal avenue to recover losses after a breach. For researchers and employees, it serves as a boundary for what constitutes legal versus illegal digital behavior.
Conclusion
The Computer Fraud and Abuse Act is a powerful, albeit complex, piece of legislation. While it started as a reaction to 1980s technophobia, it has evolved into the cornerstone of American cyber law. Understanding the distinction between authorized and unauthorized access is critical for anyone operating in the modern digital economy.

Keywords for SEO:
- Computer Fraud and Abuse Act
- CFAA explained
- Unauthorized access laws
- 18 U.S.C. 1030
- Cybercrime legislation US
- Van Buren v. United States
