Vulnerability testing is a critical security practice employed to identify weaknesses within a system that could be exploited by malicious actors. In the rapidly evolving landscape of technology, particularly concerning sophisticated systems like drones, advanced cameras, and cutting-edge flight technology, understanding and mitigating these vulnerabilities is paramount. This article will delve into the core principles of vulnerability testing, its methodologies, and its crucial importance across various technological domains, with a specific focus on how it safeguards the integrity and functionality of drone systems, their integrated flight technology, and the captured imagery.
Understanding the Landscape of Vulnerabilities
Before diving into the testing methodologies, it’s essential to grasp the diverse nature of vulnerabilities that can plague modern technological systems. These weaknesses can manifest in software, hardware, firmware, or even in the operational procedures surrounding the technology.
Software and Firmware Vulnerabilities
Software and firmware form the digital backbone of many advanced systems. Bugs, coding errors, outdated libraries, and insecure programming practices can create exploitable openings.
Common Software Vulnerabilities
- Buffer Overflows: Occur when a program attempts to write more data into a buffer than it can hold, potentially overwriting adjacent memory and allowing attackers to inject malicious code.
- SQL Injection: A type of attack where malicious SQL statements are inserted into an entry field for execution, potentially allowing attackers to access, modify, or delete data.
- Cross-Site Scripting (XSS): Involves injecting malicious scripts into web pages viewed by other users, which can be used to steal cookies, session tokens, or redirect users to malicious sites.
- Insecure Deserialization: A vulnerability where untrusted data is deserialized by an application, potentially leading to code execution.
- Outdated Libraries and Frameworks: Using components with known vulnerabilities that have not been patched can expose the entire system.
Firmware Flaws
Firmware, the low-level software that controls hardware, is also a prime target. Flaws in firmware can grant attackers deep control over a device.
- Hardcoded Credentials: Passwords or keys embedded directly into the firmware, making them easily discoverable.
- Unencrypted Communication Protocols: Transmitting sensitive data, such as control commands or telemetry, without encryption makes it susceptible to interception and manipulation.
- Insecure Update Mechanisms: If firmware updates are not properly authenticated or encrypted, attackers could push malicious firmware onto the device.
Hardware and Network Vulnerabilities
Beyond software, the physical components and the way devices communicate also present potential risks.
Hardware Weaknesses
- Physical Tampering: Unauthorized physical access can lead to the compromise of components, extraction of sensitive data, or implantation of malicious hardware.
- Side-Channel Attacks: These attacks exploit information leaked from the physical implementation of a computing system, such as power consumption, electromagnetic radiation, or timing, to infer secret information like cryptographic keys.
- Component Backdoors: The possibility of compromised components being manufactured with hidden functionalities or vulnerabilities.
Network and Communication Vulnerabilities
The interconnectedness of modern devices means network security is crucial.
- Weak Encryption Protocols: Using outdated or compromised encryption algorithms for wireless communication (e.g., Wi-Fi, Bluetooth, proprietary drone control links).
- Man-in-the-Middle (MITM) Attacks: An attacker intercepts communication between two parties, potentially eavesdropping or altering the messages.
- Denial-of-Service (DoS) Attacks: Overwhelming a system with traffic or requests, rendering it inoperable. This can be particularly disruptive for real-time drone operations.
- Unauthorized Access: Exploiting weak authentication mechanisms to gain access to control networks or device interfaces.
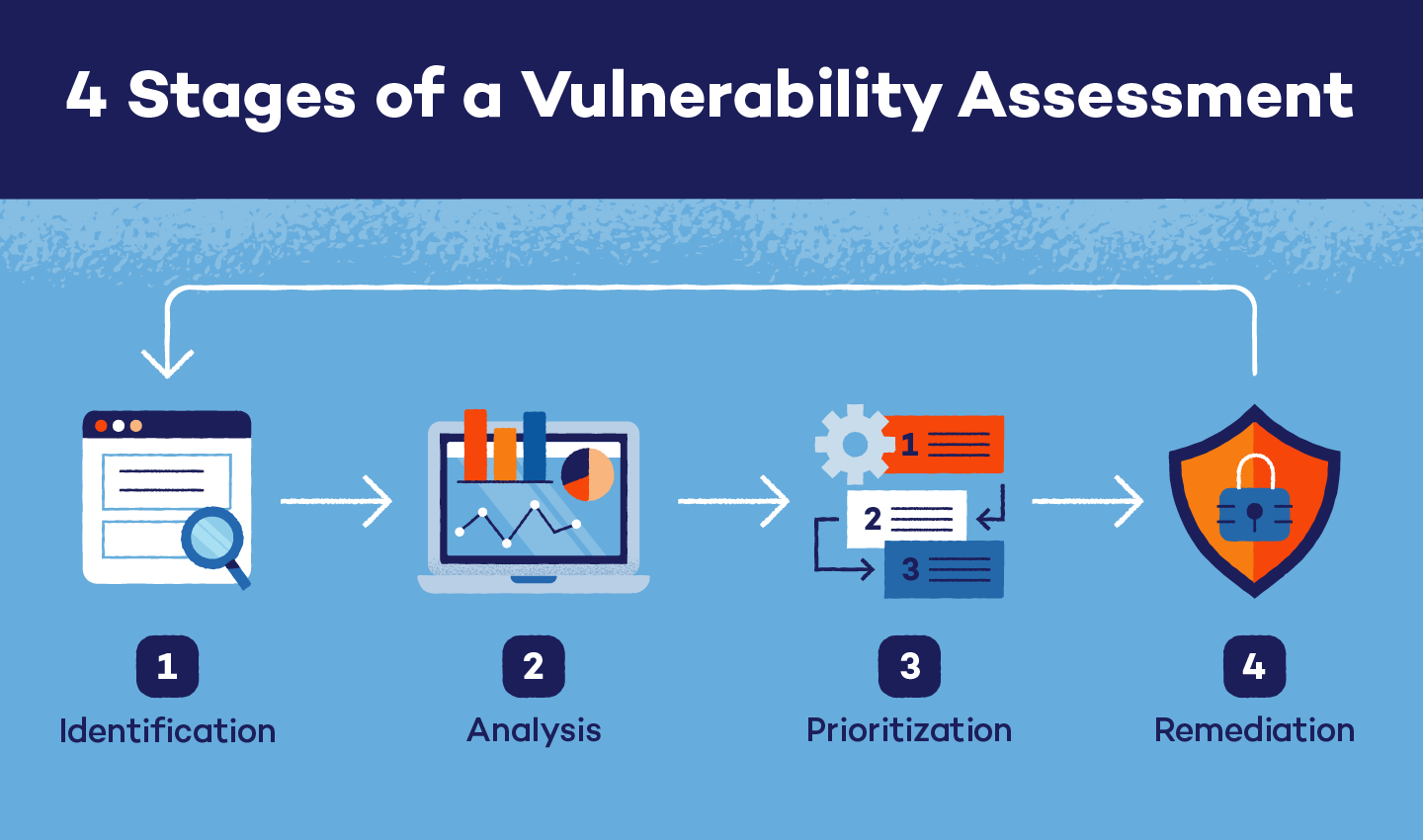
Methodologies for Vulnerability Testing
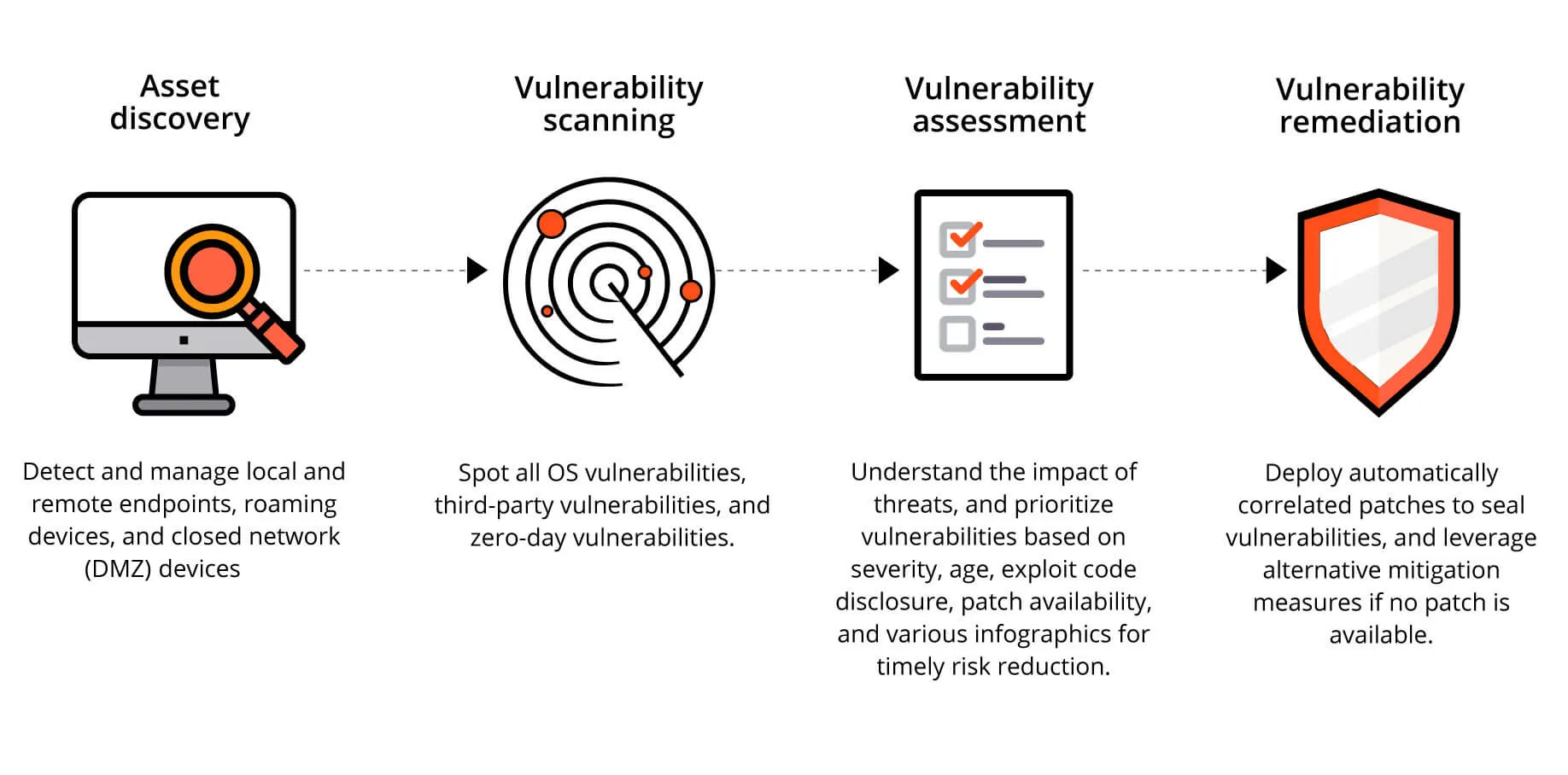
Vulnerability testing employs a range of techniques to systematically uncover these weaknesses. These methodologies can be broadly categorized into automated and manual approaches, often used in conjunction for comprehensive coverage.
Automated Vulnerability Scanning
Automated tools are highly efficient for identifying known vulnerabilities based on extensive databases.
Network Scanners
Tools like Nessus, OpenVAS, and Qualys scan networks and devices for open ports, running services, and known vulnerabilities associated with those services. They can identify unpatched software, weak configurations, and common security misconfigurations.
Web Application Scanners
For systems with web-based interfaces (common in drone management platforms or camera control apps), tools such as Burp Suite, OWASP ZAP, and Acunetix can detect vulnerabilities like SQL injection, XSS, and insecure direct object references.
Static Application Security Testing (SAST)
SAST tools analyze source code, byte code, or binary code without executing the application. They can identify potential vulnerabilities early in the development lifecycle by looking for insecure coding patterns. Examples include SonarQube and Checkmarx.
Dynamic Application Security Testing (DAST)
DAST tools test applications by interacting with them as an end-user would, sending various inputs and observing outputs to identify runtime vulnerabilities. This approach is effective for identifying vulnerabilities that only manifest when the application is running.
Manual Vulnerability Assessment and Penetration Testing
While automated tools are powerful, manual testing is essential for discovering complex, logic-based, or zero-day vulnerabilities that automated tools might miss.

Vulnerability Assessment
This process involves a more in-depth analysis than automated scanning. It often includes manual review of configurations, architecture, and code, combined with targeted automated scans. The goal is to identify potential vulnerabilities and assess their risk.
Penetration Testing (Ethical Hacking)
Penetration testing goes a step further by actively attempting to exploit identified vulnerabilities to determine the extent of potential damage. Ethical hackers simulate real-world attacks to test an organization’s security posture. This can involve:
- Reconnaissance: Gathering information about the target system.
- Scanning: Identifying active hosts and open ports.
- Gaining Access: Exploiting vulnerabilities to gain unauthorized entry.
- Maintaining Access: Establishing persistent control.
- Covering Tracks: Removing evidence of the intrusion (though in ethical hacking, this is often simulated for awareness).
Firmware Analysis
For devices like drones, specialized firmware analysis is crucial. This can involve reverse engineering firmware to understand its functionality, identify embedded secrets, and detect potential vulnerabilities in the code.
The Importance of Vulnerability Testing
The implications of unaddressed vulnerabilities are far-reaching, impacting data security, operational integrity, and even physical safety, especially in the context of drones and their associated technologies.
Protecting Data and Privacy
Modern drones and imaging systems capture vast amounts of data, ranging from sensitive aerial imagery to operational telemetry.
Sensitive Data Exposure
Unsecured systems can lead to the exposure of proprietary information, personal identifiable information (PII) of individuals captured in imagery, or strategic flight data. Vulnerability testing helps ensure that data is protected through encryption, access controls, and secure storage.
Privacy Concerns
With increasing deployment of drones for surveillance, delivery, and personal use, privacy is a major concern. Vulnerability testing can help prevent unauthorized access to camera feeds or location data, thus safeguarding individual privacy.
Ensuring Operational Integrity and Reliability
The functionality and reliability of drone systems, including their flight control and navigation, are paramount.
Preventing Operational Disruptions
Vulnerabilities can be exploited to disrupt drone operations, leading to mission failures, lost assets, or even crashes. This is particularly critical for commercial, industrial, or public safety applications where reliability is non-negotiable.
Maintaining Control System Security
The flight control system is the brain of a drone. Exploiting vulnerabilities here could allow an attacker to take control of the drone, steer it off course, or cause it to land or crash intentionally. Robust vulnerability testing ensures these control systems are resilient.
Enhancing Trust and Compliance
In regulated industries or when dealing with sensitive operations, trust and compliance are essential.
Regulatory Compliance
Many industries are subject to data protection regulations (e.g., GDPR, CCPA) and security standards. Regular vulnerability testing demonstrates a commitment to security and helps organizations meet these compliance requirements.
Building User Confidence
For consumers and businesses adopting drone technology or advanced camera systems, assurance of security and reliability is key. Proactive vulnerability testing builds trust and confidence in the technology’s safety and integrity.
Safeguarding Against Emerging Threats
The threat landscape is constantly evolving, with new attack vectors and exploits discovered regularly.
Proactive Defense
Vulnerability testing is not a one-time activity but an ongoing process. Regular testing allows organizations to stay ahead of emerging threats, identify new vulnerabilities as they are discovered, and patch them before they can be exploited.
Zero-Day Exploits
While difficult to predict, vulnerability testing, especially with advanced manual techniques and threat intelligence, can sometimes uncover previously unknown vulnerabilities (zero-days) before they are widely exploited. This allows for early mitigation.
In conclusion, vulnerability testing is an indispensable practice for any organization leveraging advanced technology. For drone enthusiasts, commercial operators, or manufacturers of cutting-edge aerial equipment, understanding and actively testing for vulnerabilities in their software, firmware, hardware, and network configurations is not just a technical necessity but a fundamental requirement for ensuring security, reliability, and trust in an increasingly connected world.
