In the rapidly evolving landscape of technology, particularly within the drone industry, the concept of a “vulnerability management system” is paramount. While the term itself might sound technical and perhaps even intimidating, its essence is about proactive defense and ensuring the integrity and security of complex systems. For drone operators, manufacturers, and anyone involved in the deployment of Unmanned Aerial Vehicles (UAVs), understanding and implementing effective vulnerability management is not just a best practice; it’s a critical necessity.
The Evolving Threat Landscape for Drones
The proliferation of drones across various sectors – from consumer photography and entertainment to industrial inspection, agriculture, and public safety – has brought with it an expanding attack surface. As drones become more sophisticated, interconnected, and data-intensive, they also become more attractive targets for malicious actors. This ever-changing threat landscape necessitates a robust approach to identifying and mitigating potential weaknesses.

Understanding the Attack Surface
The attack surface of a drone system is multifaceted. It encompasses not just the physical aircraft itself but also its communication links, ground control stations, data storage, connected software, and the associated infrastructure. Each of these components represents a potential entry point for exploitation.
Aircraft Hardware and Firmware
The drone’s internal components, including flight controllers, sensors, communication modules, and embedded firmware, can harbor vulnerabilities. Flaws in the design or implementation of this hardware and software can be exploited to gain unauthorized control, steal data, or disrupt operations. For instance, a poorly secured communication module might allow an attacker to intercept commands or inject false ones. Similarly, outdated firmware with known exploits can leave the drone susceptible to takeover.
Communication Protocols and Links
The radio frequencies and protocols used for communication between the drone and its ground control station are critical. If these links are not adequately encrypted or authenticated, they can be vulnerable to jamming, spoofing, or man-in-the-middle attacks. Attackers could potentially intercept control signals, disrupt flight, or even take over the drone’s navigation. The increasing use of Wi-Fi and Bluetooth for drone connectivity, while convenient, also introduces familiar attack vectors that require careful management.
Ground Control Software and Applications
The software used to operate and manage drones, whether on a dedicated controller or a mobile device, is another significant area of concern. These applications often handle sensitive data, including flight plans, telemetry, and captured imagery. Bugs or design flaws in this software can lead to data breaches, denial-of-service attacks, or allow unauthorized access to drone functionality. Furthermore, the integration of third-party applications or services can introduce additional dependencies and potential vulnerabilities.
The Core Components of a Vulnerability Management System
A vulnerability management system (VMS) is a comprehensive, cyclical process designed to identify, assess, prioritize, remediate, and report on security weaknesses within an organization’s IT infrastructure and, by extension, its drone ecosystem. It’s not a one-time fix but an ongoing effort.
Identification: Proactive Scanning and Discovery
The first crucial step in vulnerability management is identifying potential weaknesses. This involves a combination of automated tools and manual assessments to uncover known and unknown vulnerabilities.
Automated Vulnerability Scanners
Specialized software tools are employed to scan networks, systems, and applications for known security flaws. These scanners maintain vast databases of vulnerabilities and can quickly identify common misconfigurations, outdated software versions, and exploitable bugs. For drones, this might involve scanning the network the ground control station is connected to, or specialized tools designed to probe drone communication protocols.
Penetration Testing and Ethical Hacking
Beyond automated scans, penetration testing involves simulating real-world cyberattacks to uncover deeper, more complex vulnerabilities that automated tools might miss. Ethical hackers, with permission, attempt to exploit weaknesses in the drone system, including its hardware, software, and operational procedures. This can reveal vulnerabilities related to physical access, social engineering, or advanced exploitation techniques.
Threat Intelligence and Information Gathering
Staying abreast of the latest threats and vulnerabilities reported by security researchers, government agencies, and industry bodies is essential. This threat intelligence informs the identification process, allowing organizations to proactively scan for and address newly discovered exploits before they are widely used by malicious actors.
Assessment and Prioritization: Understanding the Risk
Once vulnerabilities are identified, they must be assessed to understand their potential impact and likelihood of exploitation. This allows for effective prioritization of remediation efforts.
Risk Scoring and Impact Analysis
Each identified vulnerability is typically assigned a risk score based on factors such as its severity (e.g., CVSS scores), the asset’s criticality, and the potential business impact. For drone operations, this could mean a vulnerability that allows unauthorized access to a critical infrastructure inspection drone carries a much higher risk than one affecting a consumer photography drone. Analyzing the potential consequences – such as data loss, operational disruption, safety hazards, or reputational damage – is key.
Asset Inventory and Context
A thorough understanding of the drone assets being managed is fundamental. This includes knowing what drones are in use, their configurations, their operational purpose, and the data they handle. Without proper asset inventory, it’s difficult to accurately assess the risk posed by a vulnerability. A vulnerability in a drone used for sensitive government surveillance is far more critical than in one used for recreational flying.
Remediation: Fixing the Flaws
The goal of vulnerability management is to reduce the risk by fixing the identified weaknesses. This phase involves implementing appropriate solutions to mitigate or eliminate the vulnerabilities.
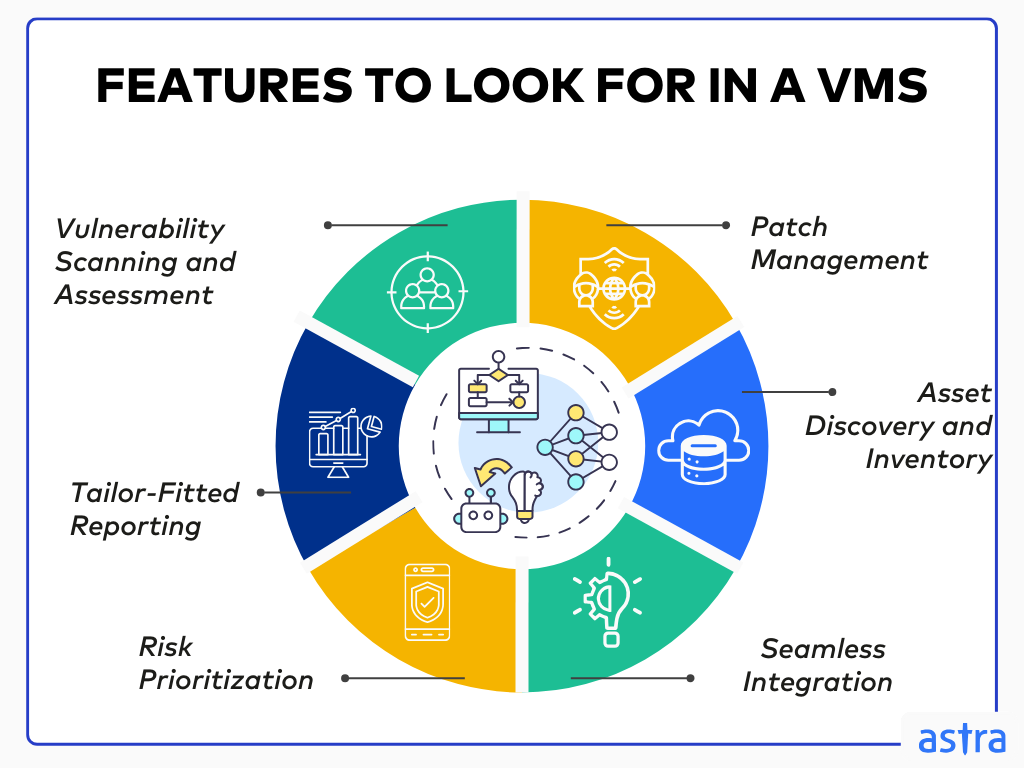
Patch Management and Software Updates
The most common remediation strategy is applying software patches and updates. Manufacturers regularly release these to address known security flaws in firmware, operating systems, and applications. For drone operators, maintaining a strict patch management policy for all connected devices and software is crucial. This includes ensuring the drone’s firmware, the ground control station’s operating system, and any associated mobile applications are kept up-to-date.
Configuration Hardening and Security Best Practices
Often, vulnerabilities arise from insecure configurations. Implementing security best practices, such as disabling unnecessary services, enforcing strong authentication, and segmenting networks, can significantly reduce the attack surface. For drone systems, this might involve securing the Wi-Fi network used for connectivity, implementing multi-factor authentication for access to ground control software, and physically securing the control station.
Workarounds and Compensating Controls
In some cases, immediate patching might not be feasible. In such situations, implementing workarounds or compensating controls can help mitigate the risk. This could involve temporarily disabling a vulnerable feature, implementing stricter access controls, or increasing monitoring of affected systems. For example, if a specific communication protocol on a drone has a known vulnerability that cannot be immediately patched, operators might choose to restrict its use or implement additional monitoring for suspicious activity on that channel.
Reporting and Continuous Improvement: The Cycle of Security
Vulnerability management is not a linear process; it’s a continuous cycle. Regular reporting and ongoing assessment are vital for maintaining a strong security posture.
Metrics and Reporting
Organizations need to track key metrics related to their vulnerability management program, such as the number of vulnerabilities identified, the time taken to remediate them, and the overall risk posture. Regular reports provide visibility into the effectiveness of the program and help justify continued investment. For drone operations, this could include reports on the security status of the fleet, the number of critical vulnerabilities addressed, and compliance with security policies.
Auditing and Review
Periodically auditing the vulnerability management process itself is essential to ensure its effectiveness and identify areas for improvement. This involves reviewing policies, procedures, and the performance of security tools and teams. As new technologies emerge and threat actors evolve, the vulnerability management system must adapt accordingly.
The Importance of a Dedicated Vulnerability Management System for Drones
For organizations operating drones, the need for a dedicated vulnerability management system is becoming increasingly pronounced. The consequences of a security breach can be severe, ranging from financial losses and reputational damage to the loss of sensitive data, physical damage to property, and even threats to public safety.
Protecting Sensitive Data and Intellectual Property
Drones are increasingly used to collect and transmit sensitive data, including aerial imagery, surveillance footage, inspection reports, and location information. A vulnerability could expose this data to unauthorized access, leading to data breaches, industrial espionage, or privacy violations. A robust VMS ensures that data remains confidential and protected throughout its lifecycle.
Ensuring Operational Continuity and Safety
The safe and reliable operation of drones is paramount, especially in critical applications like emergency response, infrastructure monitoring, and law enforcement. A successful cyberattack could disrupt flight operations, cause drones to crash, or lead to their misuse, posing significant safety risks. A VMS helps to prevent these disruptions by identifying and mitigating vulnerabilities before they can be exploited.
Compliance with Regulations and Industry Standards
As the drone industry matures, regulatory bodies and industry organizations are developing stricter guidelines and standards related to cybersecurity. Implementing a comprehensive vulnerability management system is often a requirement for compliance, helping organizations avoid penalties and maintain their operating licenses.
Building and Implementing an Effective Drone Vulnerability Management Program
Developing and deploying an effective vulnerability management system requires a structured approach and a commitment from all levels of an organization.
Establishing a Clear Policy and Framework
The first step is to establish a clear cybersecurity policy that specifically addresses drone operations. This policy should define responsibilities, outline procedures for vulnerability management, and set expectations for security awareness and training. A well-defined framework will guide all subsequent actions.
Investing in the Right Tools and Expertise
Effective vulnerability management relies on appropriate technology and skilled personnel. This includes investing in automated scanning tools, penetration testing services, and potentially specialized drone security solutions. Furthermore, organizations need to ensure they have access to cybersecurity professionals with expertise in IoT security and drone technologies, or they should invest in training for their existing IT teams.
Fostering a Culture of Security Awareness
Technology alone cannot solve all security challenges. A strong security culture, where all employees understand the importance of cybersecurity and their role in protecting drone systems, is essential. Regular training, awareness campaigns, and clear communication channels are vital to embedding security into the daily operations of drone users and operators.

Continuous Monitoring and Adaptation
The threat landscape is constantly changing, and so too must the vulnerability management system. Continuous monitoring of drone systems for anomalous activity, regular re-assessment of vulnerabilities, and a commitment to adapting the VMS to new threats and technologies are crucial for long-term security. This proactive and adaptive approach ensures that drone operations remain secure and resilient in the face of evolving cyber threats.
