In the realm of cybersecurity, the terms “virus” and “worm” are often used interchangeably, leading to confusion for those trying to understand the nuances of malware. While both are malicious programs designed to cause harm, their fundamental difference lies in their propagation methods and dependence on host files. Understanding these distinctions is crucial for implementing effective security measures and safeguarding digital assets. This article will delve into the core characteristics of viruses and worms, highlighting their unique behaviors, infection vectors, and the impact they can have on individuals and organizations.
Understanding the Core Nature of Malware
Before dissecting the differences between viruses and worms, it’s essential to establish a baseline understanding of what constitutes malware and the broader categories it falls under. Malware, short for malicious software, is a general term encompassing any software designed to disrupt, damage, or gain unauthorized access to a computer system. This can range from data theft and system disruption to complete control of compromised devices. Viruses and worms are two prominent types of malware, each with its own modus operandi.
The Virus: A Parasitic Intruder
A computer virus, in its most fundamental definition, is a piece of malicious code that attaches itself to an existing, legitimate program or file. Think of it like a biological virus that needs a host cell to replicate and spread. Without a host, a virus cannot function or propagate. When the infected program or file is executed, the virus code is also executed, allowing it to replicate and spread to other programs or files on the same system or on connected networks.
- Replication Mechanism: Viruses typically replicate by inserting their code into other executable files. When an infected file is opened or run, the virus code executes, searches for other vulnerable files, and injects its own code into them. This process can happen rapidly, leading to widespread infection within a system.
- Payload and Damage: The “payload” of a virus refers to the malicious action it performs beyond replication. This can range from displaying annoying messages, deleting files, corrupting data, stealing sensitive information, to even rendering the entire system unusable. The damage caused by a virus is often directly tied to its payload.
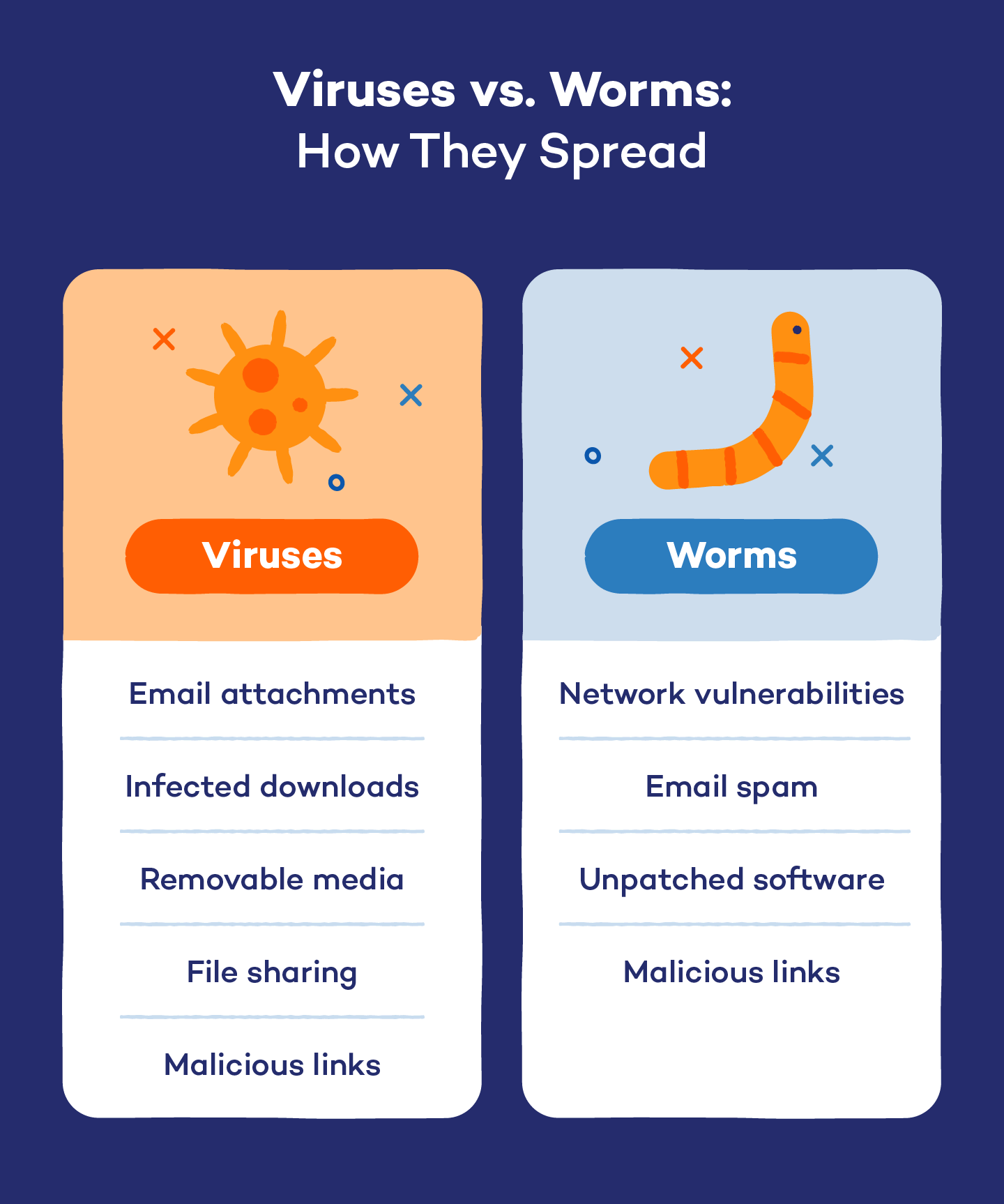
- Infection Vectors: Viruses commonly spread through infected email attachments, downloaded files from untrusted sources, infected USB drives, and compromised software installations. User interaction is almost always required for a virus to execute and spread, meaning a user must open an infected file or run an infected program.
- Example Scenarios: Imagine downloading a seemingly legitimate software update from an unofficial website. This update might contain a virus that attaches itself to the software’s executable file. When you run the software, the virus activates, potentially spreading to other programs on your computer or even to shared network drives.
The Worm: The Self-Sufficient Spreader
In contrast to viruses, computer worms are standalone malicious programs that do not require attachment to an existing host file to function or propagate. Their primary characteristic is their ability to self-replicate and spread across networks, often without any user interaction. Worms exploit vulnerabilities in operating systems or network protocols to gain access to other systems and replicate themselves.
- Autonomous Propagation: The defining feature of a worm is its ability to spread independently. Once a worm infects a system, it actively scans the network for other vulnerable machines and exploits those vulnerabilities to copy itself over. This self-propagation capability allows worms to spread at an alarming rate, often creating a significant strain on network resources.
- Exploiting Vulnerabilities: Worms are adept at identifying and exploiting security flaws in software and network configurations. These vulnerabilities can be in operating systems, web browsers, email clients, or network services. By exploiting these weaknesses, worms can bypass traditional security measures and gain access to systems.
- Network Impact: Due to their rapid propagation, worms can quickly overwhelm networks with traffic, leading to denial-of-service (DoS) conditions. This can disrupt business operations, slow down internet access, and make systems inaccessible.
- Payload Diversity: Like viruses, worms can also carry malicious payloads. These payloads can be similar to those of viruses, including data theft, system disruption, or the creation of backdoors for remote access. Some worms are designed solely for propagation, while others have destructive payloads.
- Example Scenarios: Consider a worm that exploits a known vulnerability in a web server’s software. Once it infects one server, it scans the internet for other servers with the same vulnerability and automatically infects them, creating a chain reaction that can affect thousands of systems within hours.
Key Differences in Propagation and Replication
The most significant divergence between viruses and worms lies in their methods of spreading and replicating. This difference dictates their potential impact and the strategies needed to combat them.
Dependence on Host Files: The Crucial Distinction
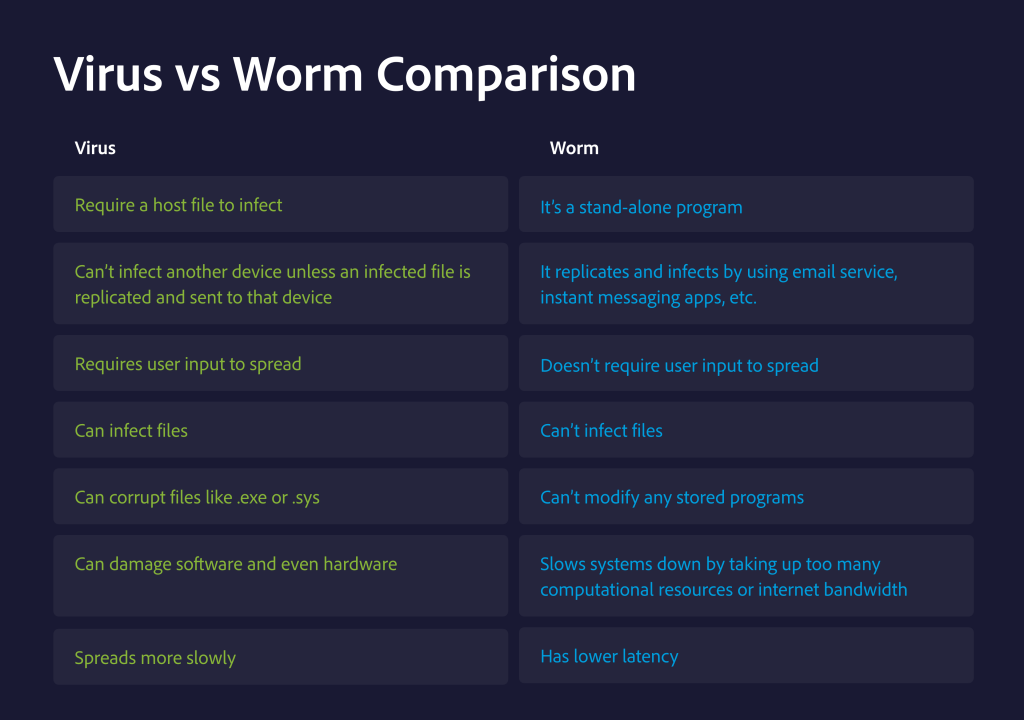
- Viruses: As mentioned, viruses are parasitic. They need to attach themselves to an existing file (often an executable file) to survive and replicate. If the host file is deleted or quarantined, the virus is effectively removed. The execution of the host file is the trigger for the virus to become active.
- Worms: Worms are independent entities. They are self-contained programs that can exist and run on their own. They don’t need to piggyback on other files. Their primary goal is to replicate and spread to new systems, utilizing network connections and exploiting vulnerabilities.
User Interaction vs. Autonomous Action
- Viruses: Typically require some form of user interaction to spread. This could be opening an infected email attachment, running a compromised application, or plugging in an infected USB drive. Without user action, the virus often remains dormant.
- Worms: Are designed for autonomous operation. They can scan networks, identify vulnerable systems, and exploit those vulnerabilities to spread without any human intervention. This makes them significantly more dangerous and difficult to contain once they are released into the wild.
Scope of Infection
- Viruses: Tend to spread more slowly, primarily within a single computer or on directly connected networks. Their spread is often limited by the sharing of infected files.
- Worms: Have the potential for rapid, widespread global infection due to their ability to traverse networks autonomously. They can spread across the internet at an exponential rate, affecting a vast number of systems in a short period.
Impact and Mitigation Strategies
The differing natures of viruses and worms necessitate tailored approaches to prevention, detection, and remediation. While some security practices overlap, understanding their distinct characteristics allows for more targeted and effective cybersecurity strategies.
The Threat Landscape: What to Watch Out For
- Virus Threats: Viruses can be particularly damaging to individual systems. Their payloads can range from minor annoyances to catastrophic data loss. The threat is often localized to the infected machine and its immediate network environment. However, a well-crafted virus can still have significant consequences for data integrity and system functionality.
- Worm Threats: The primary threat from worms is their ability to cause widespread network disruption and system compromise. They can consume bandwidth, clog networks, and serve as a delivery mechanism for other, more damaging malware. The scale of a worm outbreak can paralyze organizations and even impact critical infrastructure.
- Hybrid Threats: It’s important to note that modern malware often blurs these lines. Some sophisticated threats might exhibit characteristics of both viruses and worms, combining self-propagation with the ability to infect host files for persistence.
Effective Defense Mechanisms
- Antivirus and Anti-Malware Software: This is the first line of defense against both viruses and worms. Regularly updated antivirus software can detect, quarantine, and remove known malware signatures. It plays a crucial role in identifying infected files and blocking malicious executables.
- Firewalls: Firewalls act as a barrier between your network and the outside world, controlling incoming and outgoing network traffic. They can help prevent unauthorized access that worms might exploit to spread. Properly configured firewalls can block the network ports and protocols that worms commonly use for propagation.
- Regular Software Updates and Patching: This is paramount for preventing worm infections. Software developers release security patches to fix vulnerabilities that malware, including worms, exploits. Keeping your operating system, applications, and firmware up-to-date ensures that these known weaknesses are closed.
- User Education and Awareness: For viruses, educating users about safe computing practices is vital. This includes being cautious about opening email attachments from unknown senders, avoiding suspicious links, downloading software only from trusted sources, and being wary of unsolicited files.
- Network Segmentation: Dividing a network into smaller, isolated segments can limit the spread of malware. If one segment is infected by a worm, the segmentation can prevent it from easily spreading to other parts of the network.
- Intrusion Detection and Prevention Systems (IDPS): These systems monitor network traffic for suspicious activity and can alert administrators or automatically block malicious attempts to exploit vulnerabilities, which is particularly effective against worm propagation.
- Regular Backups: In the event of a severe infection, having regular, verified backups of critical data is essential for recovery. This ensures that even if a virus or worm corrupts or deletes files, the data can be restored.

Conclusion: A Continuous Battle for Digital Security
The distinction between viruses and worms, while seemingly technical, has profound implications for how we approach cybersecurity. Viruses, with their parasitic nature and reliance on user action, often require vigilant end-user behavior and robust anti-malware solutions. Worms, on the other hand, pose a more immediate network-wide threat due to their autonomous propagation capabilities, necessitating strong network security measures, timely patching, and proactive vulnerability management.
As the landscape of cyber threats continues to evolve, the lines between different types of malware may blur further. However, understanding the foundational differences between viruses and worms provides a critical framework for building resilient digital defenses. By staying informed about these threats and implementing comprehensive security strategies, individuals and organizations can significantly reduce their vulnerability and protect their valuable digital assets in an increasingly interconnected world. The ongoing battle against malware is a testament to the dynamic nature of technology and the unwavering need for vigilance and adaptation in cybersecurity.
