In the realm of modern computing and network operations, understanding the underlying infrastructure that facilitates seamless data flow is crucial. One such component, often encountered but not always fully grasped, is the “proxy host.” For many users, especially those operating within specialized technological fields like advanced drone operations, remote sensing, or complex imaging systems, the concept of a proxy host might arise when troubleshooting connectivity issues, optimizing data transfer, or ensuring secure communication channels. This article delves into the fundamental nature of proxy hosts, their operational mechanics, and their specific relevance within technologically advanced domains.
Understanding the Proxy Host: A Gateway to Network Access
At its core, a proxy host acts as an intermediary. Instead of devices connecting directly to the internet or a specific server, they communicate with the proxy host first. This intermediary then forwards the request to the intended destination and subsequently relays the response back to the originating device. This intermediary role offers a range of benefits, from enhanced security and privacy to improved performance and access control.
The Fundamental Role of a Proxy Server
Imagine you’re trying to access a website. Without a proxy, your device sends a direct request to the website’s server. With a proxy, your device sends the request to the proxy server. The proxy server then initiates its own request to the website’s server, using its own IP address. When the website’s server responds, it sends the data back to the proxy server, which then forwards it to your device.
This “man-in-the-middle” (in a beneficial, controlled way) position allows the proxy to perform several critical functions:
- Masking IP Addresses: The proxy server uses its own IP address when communicating with the internet. This effectively hides the original IP address of your device, providing a layer of anonymity and privacy. This is particularly valuable in scenarios where direct exposure of an operational unit’s network identity could be a security risk.
- Caching: Proxy servers can store frequently accessed web pages or data. When another device requests the same information, the proxy can serve it directly from its cache, reducing latency and bandwidth consumption. This is a significant advantage in environments with limited or expensive data connectivity, such as remote drone operation bases or deployed sensing stations.
- Filtering and Security: Proxies can be configured to block access to certain websites or content, acting as a firewall. They can also scan incoming and outgoing data for malicious software, providing an additional layer of security. For critical applications, this ensures that only approved data streams are processed and that sensitive operational data is protected from unauthorized access or compromise.
- Access Control: In corporate or institutional networks, proxy hosts are often used to manage and monitor internet access. This allows administrators to control which resources employees or systems can access and to track usage.
Types of Proxy Hosts
While the fundamental principle remains the same, proxy hosts can be categorized based on their functionality and how they are deployed:
- Forward Proxies: These are the most common type and are typically used by clients (individual devices or networks) to access the internet. They act on behalf of the client, forwarding requests to various external servers.
- Reverse Proxies: In contrast to forward proxies, reverse proxies are used by servers. They sit in front of one or more web servers and intercept requests from clients. This allows them to distribute incoming traffic across multiple servers (load balancing), provide SSL encryption, and protect the backend servers from direct exposure. In sophisticated drone management systems, reverse proxies can be used to manage traffic to ground control stations or data processing hubs.
- Anonymous Proxies: These proxies are designed to hide the client’s IP address. They can range from transparent proxies (which don’t hide the IP) to highly anonymous proxies that go to great lengths to obscure the client’s origin.
- Transparent Proxies: These proxies intercept traffic without requiring any configuration on the client’s device. They are often used by ISPs or network administrators for content filtering or caching.
- Distorting Proxies: These proxies change their IP address with each request, making it harder to track the origin of the traffic.
- High-Anonymity Proxies: These proxies strive to be completely invisible, not revealing their proxy nature or the client’s IP address.
Proxy Hosts in Specialized Technological Fields
The concept of a proxy host is not confined to general internet browsing. In technologically advanced fields like those involving drones, advanced imaging, and cutting-edge flight technology, proxy hosts play a critical, albeit often unseen, role.
Data Transmission and Management in Drone Operations
In the context of drone operations, particularly for commercial or industrial applications such as aerial surveying, infrastructure inspection, or agricultural monitoring, the efficient and secure transmission of data is paramount. Drones, especially those equipped with high-resolution cameras or sophisticated sensors, generate vast amounts of data.
- Remote Data Offloading: During extended missions, drones may need to offload captured data before returning to base. A proxy host, strategically located at a forward operating base or even on a mobile platform, can act as an intermediary to receive this data. This proxy can then manage the transfer to a central storage facility, prioritizing bandwidth allocation and ensuring data integrity. This is crucial when dealing with large video files or sensor readings that would be impractical to store entirely on the drone.
- Command and Control Relay: For beyond-visual-line-of-sight (BVLOS) drone operations, maintaining a stable command and control link is essential. Proxy hosts can be used to relay commands from a ground control station to the drone, especially when direct communication links are unreliable or obstructed. This can involve a chain of proxy servers that optimize routing and ensure that critical commands reach the drone with minimal latency.
- Geospatial Data Aggregation: When multiple drones are deployed for large-scale mapping or surveillance, the generated geospatial data needs to be aggregated and processed. A proxy host can serve as a collection point for this data, performing initial validation, indexing, and then routing it to a central processing server. This offloads processing from the individual drones and streamlines the overall data workflow.
- Security and Access Control for Sensitive Data: Drones used for security or intelligence gathering often capture highly sensitive information. A proxy host can enforce strict access controls, ensuring that only authorized personnel or systems can access the retrieved data. It can also facilitate secure encryption and decryption of data in transit, safeguarding it from interception.
Enhancing Flight Technology Data Flow
Beyond the drone itself, the systems that support flight technology, such as navigation, stabilization, and sensor data processing, also benefit from proxy host architectures.
- Sensor Data Aggregation and Pre-processing: Advanced flight systems often incorporate numerous sensors – GPS, IMUs, barometers, lidar, radar. The raw data from these sensors can be overwhelming. A proxy host, perhaps integrated into the flight controller or a dedicated data acquisition unit, can aggregate this data, perform initial filtering, calibration, and even basic pre-processing before transmitting it to the main flight computer. This reduces the computational load on the primary processor and allows for faster decision-making.
- Real-time Navigation Data Streamlining: For autonomous flight and precision navigation, a constant stream of accurate positional and navigational data is required. A proxy host can manage this stream, ensuring that the most relevant and up-to-date data from GPS receivers, ground-based beacons, or other navigation aids is prioritized and delivered to the flight control system. It can also act as a buffer, smoothing out momentary glitches in data reception.
- Obstacle Avoidance System Integration: Obstacle avoidance systems rely on real-time data from sensors like lidar and cameras. A proxy host can facilitate the rapid exchange of this sensor data with the flight control algorithms responsible for path planning and avoidance maneuvers. By optimizing this data flow, it contributes to the responsiveness and effectiveness of the obstacle avoidance system, which is critical for preventing collisions and ensuring safe operation.
Optimizing Imaging and Camera Data Streams
The integration of cameras and advanced imaging systems with drones introduces unique challenges related to data volume and real-time processing.
- High-Resolution Video Stream Management: Drones equipped with 4K or higher resolution cameras generate massive video files. When this video needs to be streamed in real-time for FPV (First Person View) piloting or for remote monitoring, a proxy host can play a crucial role. It can compress the video stream, manage bandwidth allocation, and even perform preliminary processing like de-noising or color correction before transmitting it to the ground station. This ensures a smoother and more responsive viewing experience.
- Gimbal Camera Data Synchronization: For cinematic shots and stable aerial footage, the synchronized movement of the gimbal and camera is essential. A proxy host can act as a central point for receiving telemetry data from the gimbal and coordinating its movements with the camera’s operational parameters, ensuring that the desired framing and stability are maintained throughout the flight.
- Thermal and Optical Zoom Data Integration: In applications like search and rescue or industrial inspection, thermal imaging and optical zoom cameras are vital. A proxy host can manage the integration of data from these disparate imaging modalities. It can present a unified view to the operator, allowing them to seamlessly switch between thermal and optical feeds or overlay information from both, enhancing situational awareness and diagnostic capabilities.
- FPV System Communication Optimization: For FPV racing drones or professional aerial cinematography, low-latency video transmission is paramount. A proxy host, often integrated into the FPV system itself, can optimize the encoding and transmission of the video signal, minimizing lag and providing the pilot or operator with a near real-time view of what the drone’s camera sees.
Identifying Your Proxy Host
In many advanced technological environments, particularly those involving networked devices and specialized software, the concept of “what is my proxy host” often arises when troubleshooting connectivity issues or configuring specific applications.
Manual Configuration and Software Settings
In most cases, your proxy host is something that has been explicitly configured on your device or within the software you are using.
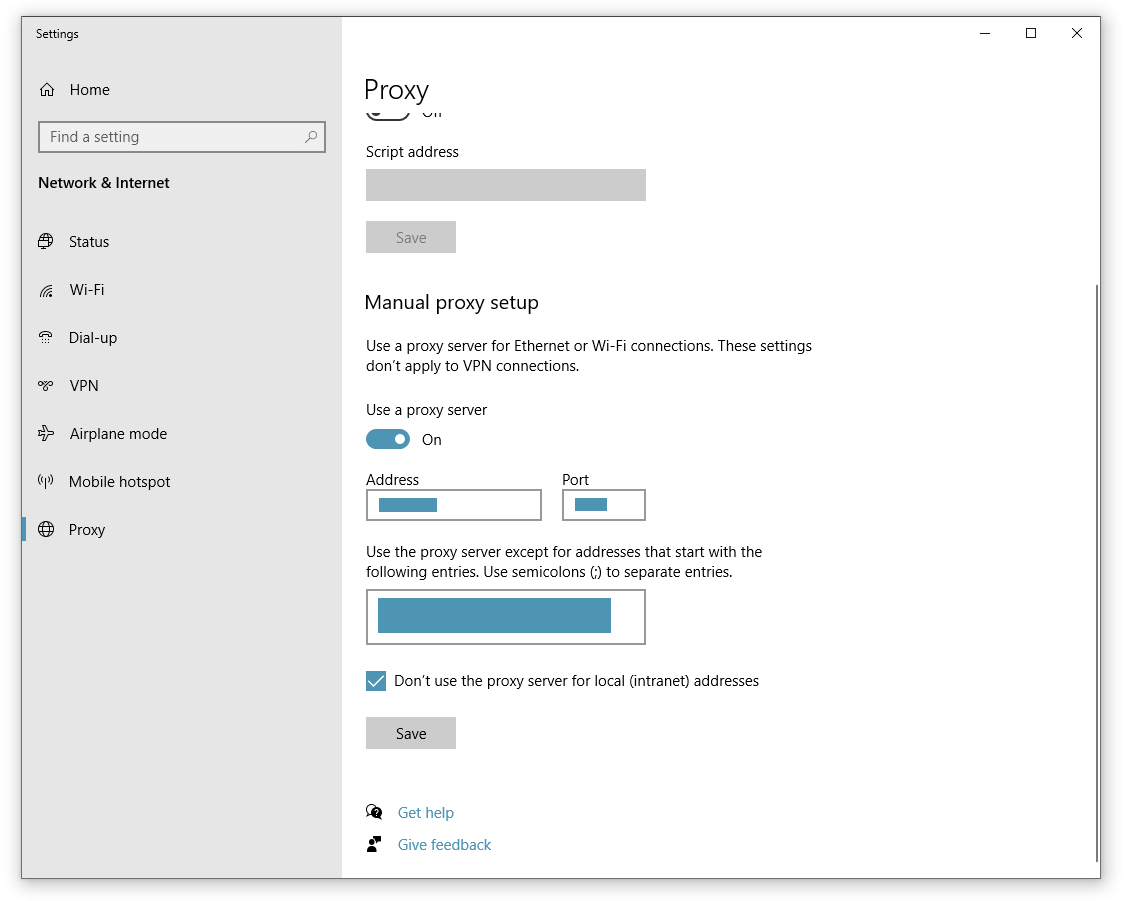
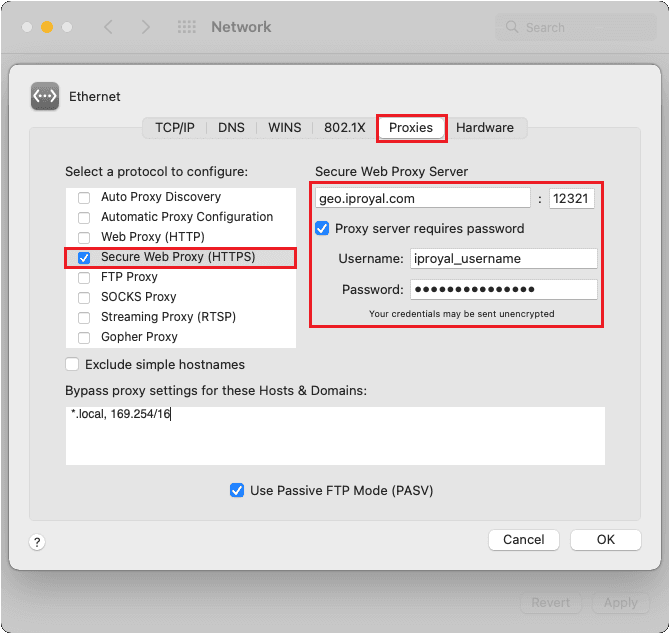
- Operating System Settings: On computers, proxy settings are typically found within the network or internet options of the operating system (e.g., Windows, macOS, Linux). Here, you can manually enter the IP address or hostname of the proxy server and the port number it uses.
- Browser Settings: Web browsers often have their own proxy settings, which can either use the system’s proxy settings or be configured independently. This allows for granular control over which applications are routed through a proxy.
- Application-Specific Settings: Many specialized applications, especially those used in drone control, data analysis, or remote sensing, will have their own dedicated proxy configuration sections. This is where you would specify the proxy host if the application requires it to connect to a specific server or service.

Network Administration and System Architecture
In larger or more complex network environments, your proxy host is usually determined by the network administrator or the overall system architecture.
- Corporate Networks: In a corporate setting, the IT department will typically configure a network-wide proxy server to manage internet access for all employees. Your device will automatically use this proxy without requiring manual configuration.
- Cloud-Based Services: When interacting with cloud-based platforms for drone data storage, processing, or flight planning, the service provider may dictate how you connect. While not always explicitly a “proxy host” in the traditional sense, the underlying infrastructure managing these connections can function analogously, ensuring secure and efficient data transfer.
- DevOps and IT Infrastructure: For individuals involved in managing the infrastructure that supports advanced drone operations or imaging pipelines, understanding the proxy hosts within their server architecture is crucial for network design, load balancing, and security. This might involve identifying the IP addresses of reverse proxies that front critical services or forward proxies that manage outbound traffic from server farms.
In conclusion, a proxy host is a fundamental network component that acts as an intermediary, facilitating communication between devices and external resources. While its general purpose is straightforward, its application in specialized technological fields such as drone operations, advanced flight technology, and sophisticated imaging systems highlights its critical role in ensuring efficiency, security, and seamless data flow. Understanding how to identify and leverage proxy hosts can significantly enhance the performance and reliability of these cutting-edge technologies.
