In an era increasingly defined by connectivity and intelligent systems, the security of digital communication has become paramount. This is especially true in the burgeoning field of drones and aerial technology, where innovation in autonomous flight, remote sensing, and data collection pushes the boundaries of what’s possible. As these advanced technologies become more integrated into critical infrastructure, commercial operations, and even everyday life, the need for robust, reliable, and secure communication protocols intensifies. Among the foundational technologies enabling this secure digital landscape, IKEv2—Internet Key Exchange version 2—stands out as a crucial component. While often discussed in the broader context of IT security, its principles and advantages are profoundly relevant to the “Tech & Innovation” category, particularly when considering the secure operation and data handling of modern drone systems.

IKEv2 is not a standalone security solution but rather a fundamental protocol that facilitates the establishment of secure connections, most notably within the IPsec (Internet Protocol Security) suite. It acts as the orchestrator for secure communication, ensuring that devices can safely authenticate each other and agree upon cryptographic keys before any sensitive data is exchanged. For the intricate and often mission-critical operations involving drones, understanding IKEv2’s role is key to appreciating the layers of security underpinning these sophisticated aerial platforms. It’s about more than just preventing unauthorized access; it’s about guaranteeing the integrity and confidentiality of the vast amounts of data—from telemetry to high-resolution imagery—that modern drones generate and transmit.
The Foundation of Secure Connectivity: Understanding IKEv2
To grasp IKEv2’s significance in drone-related tech and innovation, it’s essential to first understand its core function and design principles. At its heart, IKEv2 is about establishing a Security Association (SA), which is a crucial agreement between two communicating entities (like a drone and its ground control station, or a drone and a cloud server) on how they will use security protocols and algorithms to protect their communication.
IPsec’s Pillar: Where IKEv2 Fits In
IKEv2 is an integral part of the IPsec protocol suite, which provides security services at the IP layer of the Internet protocol stack. IPsec itself offers two primary security protocols: Authentication Header (AH) for data integrity and origin authentication, and Encapsulating Security Payload (ESP) for confidentiality, data origin authentication, integrity, and anti-replay protection. However, IPsec needs a mechanism to manage the cryptographic keys and establish the SAs that AH and ESP rely on. This is precisely where IKEv2 comes in.
Before any encrypted or authenticated data can flow via IPsec’s AH or ESP, IKEv2 performs the heavy lifting of setting up these secure channels. It negotiates the algorithms, keys, and parameters that both ends of the communication will use, effectively creating a secure tunnel. Without IKEv2, manually configuring and managing these cryptographic parameters for every connection would be an impossible task, especially in dynamic environments like drone operations where connections might be established and terminated frequently, and with varying endpoints.
Key Exchange: The Heart of Secure Communication
The primary function of IKEv2 is key exchange. It enables two parties to securely generate and agree upon shared secret keys over an insecure channel, such as the internet. This process involves sophisticated cryptographic techniques, including Diffie-Hellman key exchange, which ensures that even if an eavesdropper intercepts the negotiation, they cannot derive the secret keys.
IKEv2 operates in phases. In Phase 1, it establishes an IKE SA, which is a secure and authenticated channel for the negotiation of subsequent SAs. This initial phase authenticates the communicating peers using various methods, such as pre-shared keys, digital certificates, or EAP (Extensible Authentication Protocol). Once the IKE SA is established, Phase 2 then creates one or more child SAs (IPsec SAs) for the actual user data traffic, applying the specific security services (encryption, authentication) defined by AH or ESP. This two-tiered approach ensures that the negotiation process itself is secure, protecting the subsequent communication channels.
Robustness and Efficiency: Why IKEv2 Stands Out
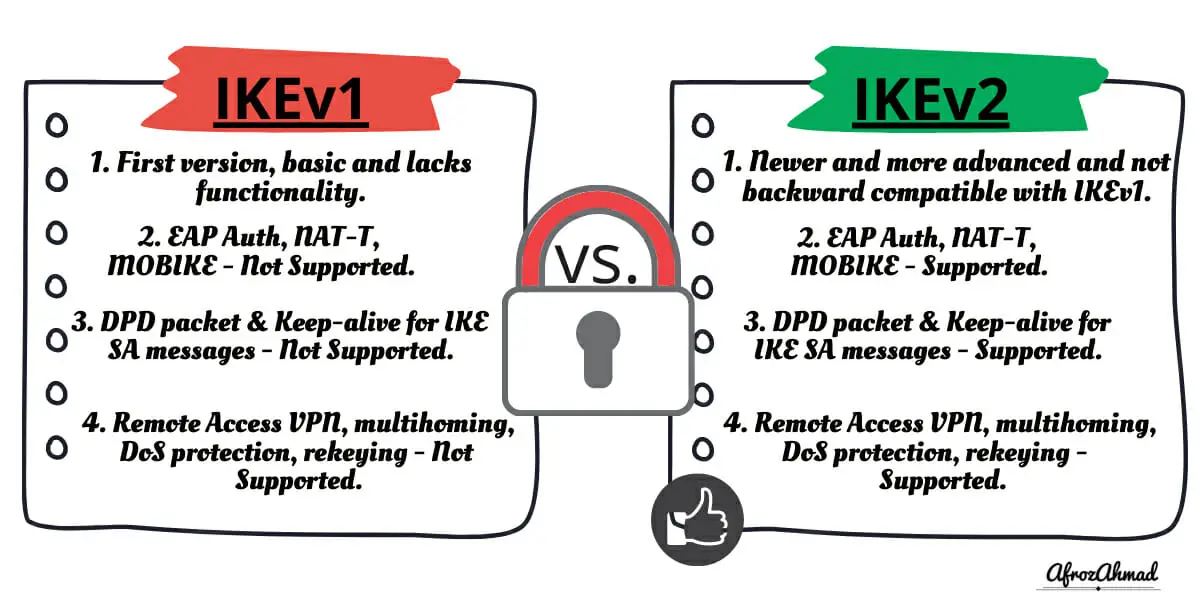
Compared to its predecessor, IKEv1, IKEv2 offers significant improvements in robustness, efficiency, and simplicity. It streamlines the negotiation process, reducing the number of messages required to establish a secure tunnel. This efficiency is critical for applications where quick connection setup and minimal overhead are desired, such as mobile VPNs or dynamic drone communications. IKEv2 also includes built-in support for mobility and multihoming (MOBKEY), allowing connections to persist even if a device changes its IP address or network interface, a highly valuable feature for drones operating across different cellular towers or Wi-Fi networks. Its resilience to network disruptions and its ability to quickly re-establish connections make it a superior choice for critical, real-time applications.
IKEv2 in the Drone Ecosystem: Enabling Secure Aerial Innovation
The advancements in drone technology, particularly in autonomous flight, remote sensing, and sophisticated data processing, necessitate a parallel evolution in their security frameworks. IKEv2 plays a pivotal role in enabling these innovations by providing a robust backbone for secure communications. Within the “Tech & Innovation” context of drones, IKEv2’s capabilities translate directly into enhanced operational integrity and data protection.
Securing Drone Telemetry and Command & Control
Drones rely on constant communication with their ground control stations (GCS) for telemetry data (e.g., altitude, speed, battery status) and critical command and control (C2) signals (e.g., flight path adjustments, payload activation). Unauthorized access to these channels could lead to severe consequences, from loss of control and crashes to malicious hijacking. By employing IKEv2-based VPNs, the entire communication link between the drone and the GCS can be encrypted and authenticated. This ensures that:
- Confidentiality: Telemetry data remains private, inaccessible to unauthorized third parties.
- Integrity: Command signals cannot be tampered with in transit, preventing malicious alterations to flight parameters.
- Authentication: Both the drone and the GCS verify each other’s identity, preventing spoofing and ensuring that only authorized entities can control the drone.
This level of security is crucial for commercial drone operations, military applications, and critical infrastructure inspections where the integrity of flight operations is non-negotiable.
Protecting Sensitive Data from Aerial Imaging and Remote Sensing
Modern drones are equipped with sophisticated cameras and sensors, capable of collecting high-resolution imagery, LiDAR data, thermal signatures, and more. This data often includes sensitive information—be it proprietary industrial surveys, confidential environmental data, or even personal privacy-related content. Transmitting this data from the drone to a processing center, often via cloud services or dedicated ground networks, presents a significant security challenge.
IKEv2-secured connections ensure that data collected during aerial imaging and remote sensing missions remains encrypted during transmission. This protects against eavesdropping and data breaches, guaranteeing that the valuable insights gathered by drones reach their intended recipients securely. For sectors like agriculture, construction, surveillance, and environmental monitoring, where data accuracy and confidentiality are paramount, IKEv2 provides a critical layer of protection for valuable aerial intelligence.
Ensuring Integrity in Autonomous Flight and AI-Driven Operations
Autonomous drones and those leveraging AI for tasks like object recognition, navigation, or anomaly detection represent the pinnacle of drone innovation. These systems often require real-time data processing, complex decision-making, and communication with cloud-based AI engines. The integrity of these communication channels is absolutely vital. If an AI model’s input or output is compromised, the drone’s autonomous behavior could be unpredictable, unsafe, or malicious.
IKEv2 helps secure the communication pathways between the drone’s onboard systems, external AI processing units, and cloud services. It ensures that the algorithms, sensor data feeds, and behavioral commands exchanged are protected from tampering and unauthorized access. This is fundamental for building trust in autonomous systems and facilitating their broader adoption in sensitive and critical applications.
Architectural Advantages of IKEv2 for Connected Drone Systems
Beyond its core security functions, IKEv2 offers specific architectural advantages that make it particularly well-suited for the dynamic and often challenging operational environments of drones. These benefits contribute directly to the reliability and scalability of drone technology.
Resilience Against Network Disruptions
Drones operate in varied environments, often encountering fluctuating network conditions, transitions between different network types (e.g., Wi-Fi to cellular), or temporary loss of signal. IKEv2’s built-in support for mobility (MOBKEY) is a significant advantage here. It allows an IPsec tunnel to survive changes in the underlying network parameters, such as the drone’s IP address. This means that if a drone temporarily loses its cellular connection and then regains it with a new IP, or switches to a different network interface, the secure VPN tunnel can often be seamlessly re-established or maintained without requiring a full reconnection process. This resilience is critical for maintaining continuous command and control, uninterrupted data streaming, and overall mission reliability.
Support for Mobile and Roaming Platforms
The very nature of drones defines them as mobile and roaming platforms. Traditional VPN protocols can struggle with devices that frequently change their network points of attachment. IKEv2 was designed with mobility in mind, making it an excellent choice for securing communications from moving vehicles and aerial platforms. This feature ensures that even as a drone travels long distances or operates in areas with inconsistent network coverage, its secure connection to its ground station or data repository remains robust and functional, facilitating efficient and secure long-range operations.
Streamlined Configuration and Management
While IKEv2 is powerful, its design also emphasizes efficiency in negotiation and streamlined configuration. This simplicity is a benefit for large-scale drone deployments or fleet management systems, where configuring and managing individual secure connections for numerous drones could become an administrative burden. IKEv2’s fewer message exchanges and clearer state transitions compared to its predecessors make it easier to implement and troubleshoot, contributing to operational efficiency and reducing the complexity associated with deploying secure drone networks.
Implementing IKEv2 for Advanced Drone Security
The practical application of IKEv2 within the drone ecosystem involves its integration into various communication pathways and system architectures. This encompasses everything from basic command links to complex cloud-based AI processing.
VPN Integration for Ground Control Stations and Cloud Services
The most common implementation of IKEv2 for drone security is through Virtual Private Networks (VPNs). A drone, or more commonly its ground control station, can establish an IKEv2/IPsec VPN tunnel to a central server, a cloud platform, or directly to other authorized endpoints. This creates an encrypted and authenticated communication channel for all data flowing between the drone system and its remote infrastructure.
- Ground Control Station to Data Center: Securely transmit collected data for processing and storage.
- Drone to Cloud Platform: For drones with onboard VPN clients (increasingly common in enterprise-grade UAVs), direct secure communication with cloud services for AI, mapping, or fleet management.
- Remote Pilot to GCS: Securing the connection if the pilot is operating from a remote location.
This integration ensures end-to-end security for crucial operational data and intellectual property.
End-to-End Encryption for Drone-to-Drone Communications (Future Implications)
As drone swarms and collaborative autonomous systems become more prevalent, the need for secure drone-to-drone communication will intensify. While currently more complex to implement at the individual drone level due to computational and power constraints, IKEv2’s principles offer a blueprint for future end-to-end encryption solutions between UAVs. Imagine a scenario where multiple drones share sensor data and coordinate actions without a central ground station—IKEv2 could provide the secure key exchange mechanism for establishing authenticated and encrypted links between individual drones, safeguarding cooperative missions from interception or manipulation. This represents a significant area for future “Tech & Innovation” in drone security.
Compliance and Regulatory Considerations in Secure Drone Operations
Many industries are subject to strict data protection regulations (e.g., GDPR, HIPAA, critical infrastructure standards). Drones collecting sensitive information must comply with these mandates. Implementing IKEv2-secured communications helps organizations demonstrate due diligence in protecting data in transit, contributing to compliance requirements. The robust encryption and authentication provided by IKEv2 can be a key component in a comprehensive security strategy that meets regulatory standards for data handling and operational security in drone applications.
The Future of Drone Security with IKEv2 and Beyond
As drone technology continues its rapid evolution, so too must the security measures designed to protect it. IKEv2, as a cornerstone of secure connectivity, is well-positioned to adapt to these changes, but it also faces new challenges.
Adapting to Quantum Threats
The emergence of quantum computing poses a long-term threat to current cryptographic algorithms, including those used by IKEv2. Research into post-quantum cryptography (PQC) is actively underway to develop algorithms that are resistant to quantum attacks. Future iterations or enhancements of IKEv2 will likely incorporate PQC standards to maintain its relevance and effectiveness in a quantum-enabled world, ensuring that drone communications remain secure against future computational power. This is a critical area for “Tech & Innovation” in the cryptographic space that directly impacts secure drone operations.
Integration with Zero-Trust Architectures
The “Zero-Trust” security model, which dictates that no user or device should be trusted by default, regardless of whether they are inside or outside the network perimeter, is gaining traction. IKEv2’s strong authentication and encryption capabilities align well with Zero-Trust principles. In a Zero-Trust drone ecosystem, every drone, GCS, and cloud service would need to explicitly verify its identity and establish a secure, authenticated session using protocols like IKEv2 before any communication is permitted, enhancing overall security posture against internal and external threats.
The Evolving Landscape of Cyber-Physical Security for UAVs
The future of drone security involves a complex interplay of physical security, network security, and operational security. IKEv2 addresses a critical piece of this puzzle by securing communication channels. As drones become more integrated into smart cities, logistics, and critical infrastructure, the scope of “Tech & Innovation” in cybersecurity for UAVs will expand to cover supply chain integrity, firmware authentication, intrusion detection systems tailored for aerial platforms, and robust incident response frameworks—all of which will implicitly or explicitly rely on foundational secure communication protocols like IKEv2.
In conclusion, “What is IKEv2?” reveals a protocol that is far more than just a technical specification; it is an enabler of secure “Tech & Innovation” in the drone world. By providing a resilient, efficient, and robust framework for establishing secure and authenticated communication channels, IKEv2 underpins the integrity of drone operations, safeguards sensitive aerial data, and facilitates the confident expansion of autonomous flight capabilities. As drones continue to redefine possibilities across industries, the role of foundational security technologies like IKEv2 will remain indispensable in ensuring their safe, reliable, and secure future.
