In an increasingly interconnected world, where devices communicate seamlessly and data flows instantaneously, the concept of a “network name” might seem like a trivial detail, often overlooked or taken for granted. However, beneath its seemingly simple definition lies a fundamental identifier that underpins the vast majority of our digital interactions. From connecting a smartphone to a home Wi-Fi network to enabling complex autonomous drone operations, understanding what a network name is and how it functions is crucial for anyone engaging with modern technology and, specifically, with the innovative landscape of drone technology. This article delves into the essence of network names, exploring their multifaceted roles within the broader context of tech and innovation, emphasizing their critical importance in the burgeoning field of unmanned aerial systems (UAS).

The Fundamental Role of Network Names in Modern Technology
At its heart, a network name serves as a label, a signpost that distinguishes one digital network from another. It’s the primary way users and devices identify and connect to a specific network within a sea of available options. Without these unique identifiers, navigating the wireless spectrum or establishing secure data paths would be an impossible task, leading to chaos and connectivity failures.
Defining the Service Set Identifier (SSID): Your Wi-Fi’s Digital Fingerprint
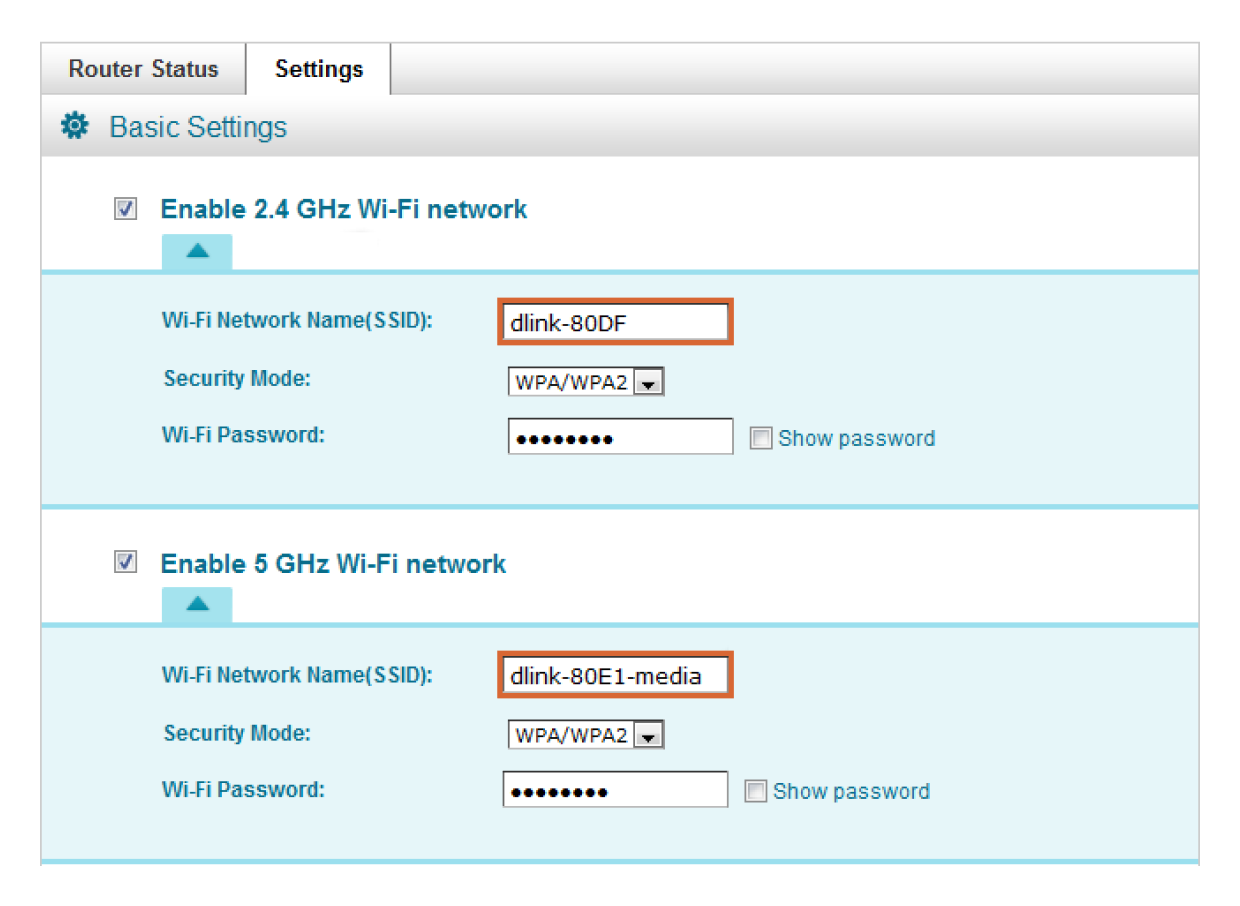
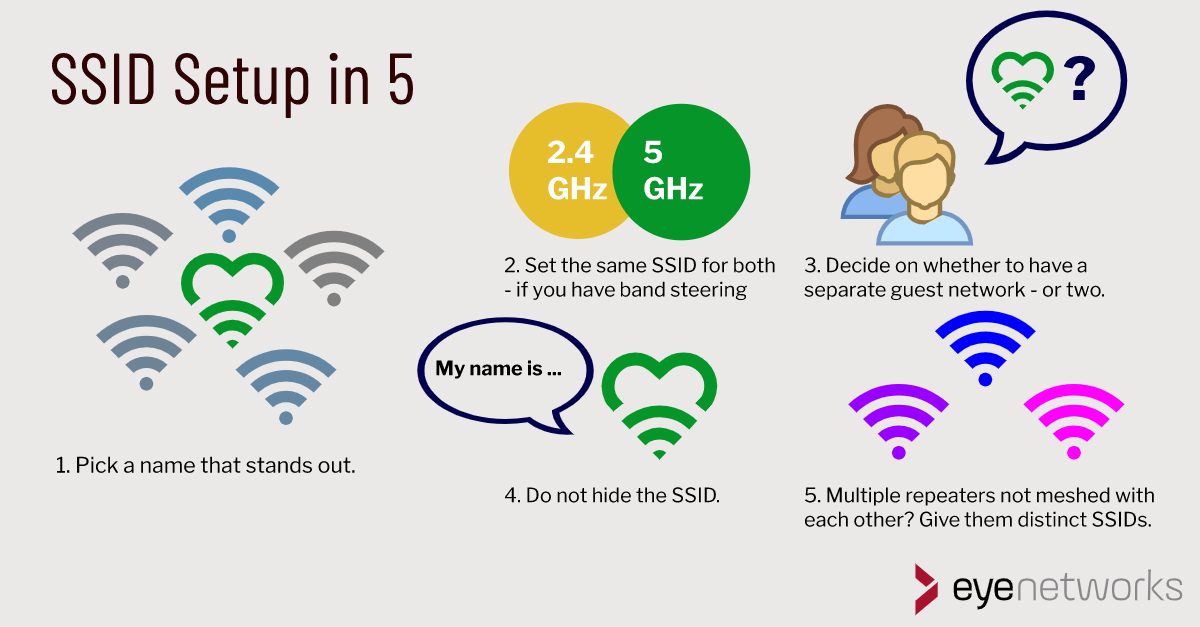
The most common manifestation of a network name encountered by the average user is the Service Set Identifier, or SSID. This is the human-readable name you see when scanning for Wi-Fi networks on your laptop, phone, or smart device. Whether it’s “MyHomeNetwork,” “CoffeeShopGuest,” or the default name provided by an internet service provider, the SSID is how a wireless access point (like a router) broadcasts its presence.
An SSID functions much like a neighborhood name in a city. It tells you which group of houses (devices) belongs to a particular area (network). When a device attempts to connect, it scans for SSIDs, presents a list to the user, and upon selection, attempts to authenticate using credentials (usually a password or passphrase). This seemingly simple process is the gateway to the internet for billions of devices globally. In the realm of smart homes, IoT devices, and even smart drone controllers, the SSID is the first step in establishing a link that allows for configuration, data transfer, and remote operation. The security of this initial connection, often protected by WPA2 or WPA3 encryption protocols, is paramount to safeguarding personal data and device integrity.
Beyond Wi-Fi: Hostnames, Device IDs, and Their Importance
While SSID predominantly refers to Wi-Fi networks, the concept of a “network name” extends to other forms of digital identification. In wired networks or more complex system architectures, identifiers such as hostnames or unique device IDs play a similar role. A hostname, for instance, is a label assigned to a device connected to a computer network that helps identify it on that network. This could be “MyLaptop,” “Server-01,” or “DroneControlStation.” These names simplify administration and communication within local area networks (LANs) and even across the internet via DNS (Domain Name System) resolution.
Furthermore, many smart devices, including drones and their components, possess unique hardware identifiers (like MAC addresses or serial numbers) that, while not “network names” in the user-facing sense, are critical at lower levels of the network stack. These identifiers ensure that data packets reach their intended recipient and facilitate device recognition within a network, even when an SSID isn’t directly involved in the peer-to-peer connection, such as a drone establishing a direct ad-hoc Wi-Fi link with its controller or an FPV system. Understanding these various forms of network identification is vital for developing robust, secure, and interoperable technological solutions, especially in dynamic environments like drone operations.
Network Names as the Backbone of Drone Communication and Innovation
The intricate dance of drones in the sky, performing complex maneuvers, capturing stunning visuals, or collecting critical data, relies heavily on a robust and identifiable communication framework. Network names are an indispensable part of this framework, enabling everything from basic control to advanced autonomous functions.
Connecting Controllers and FPV Systems: The Wireless Link
For most consumer and prosumer drones, the primary control link between the drone and its remote controller is established wirelessly. Often, this connection utilizes a modified Wi-Fi protocol or a proprietary radio frequency link that still, at its core, relies on a unique network identifier. When a drone is powered on, it essentially broadcasts its “presence” through a dedicated network, much like a Wi-Fi router broadcasts an SSID. The controller then scans for this specific drone’s identifier—its network name, in essence—to establish a direct, peer-to-peer connection.
Similarly, First-Person View (FPV) systems, which transmit real-time video feeds from the drone’s camera to goggles or a display, also depend on identifiable wireless links. These FPV systems, whether digital or analog, operate on specific frequencies and often create their own dedicated networks, each with an implicit or explicit “name” that distinguishes it from other signals. For example, a digital FPV system might create a Wi-Fi-like ad-hoc network that the FPV goggles connect to, requiring the goggles to recognize the drone’s unique network identifier to receive the video stream. This reliable and unique identification is critical for preventing interference and ensuring a stable, low-latency connection during flight.
Enabling Smart Features: From Firmware Updates to Cloud Services
Modern drones are not just flying cameras; they are sophisticated flying computers. Many advanced features and operational efficiencies are unlocked when a drone, or more commonly its smart controller, connects to the internet. This is where traditional Wi-Fi network names (SSIDs) come into play. A smart controller, for example, connects to a home or public Wi-Fi network using its SSID and password. This connection then enables a plethora of “Tech & Innovation” features:
- Firmware Updates: Ensuring the drone and controller always have the latest software for performance improvements, new features, and critical security patches.
- Flight Log Synchronization: Uploading flight data to cloud platforms for analysis, troubleshooting, and compliance.
- Geo-referencing and Mapping Data Uploads: For photogrammetry and 3D mapping missions, captured images and associated metadata can be uploaded directly from the field via a Wi-Fi hotspot or later through a home network.
- AI Processing Offload: In some advanced scenarios, particularly for AI-powered “follow-me” modes or object recognition, preliminary data might be transmitted to a cloud service for intensive processing, with commands then sent back to the drone.
- Livestreaming: Broadcasting aerial footage directly from the drone (via its smart controller’s internet connection) to social media or professional streaming platforms.
These capabilities underscore how seamlessly integrating drones into existing network infrastructures, identified by their network names, enhances their utility far beyond basic flight.
Data Transmission for Mapping, Sensing, and AI-Powered Flight
Beyond basic control and internet access, network names are foundational to advanced drone applications in mapping, remote sensing, and autonomous flight. High-resolution imagery, LiDAR data, multispectral readings, and real-time telemetry from complex sensors must be reliably transmitted from the drone to a ground station or cloud service. These data streams often require high-bandwidth, stable network connections.
For large-scale mapping projects or precision agriculture, drones might be equipped with specialized payloads that generate massive datasets. The network layer, identified by its unique name, provides the conduit for this information. Whether it’s a dedicated high-frequency radio link with its own identification protocol or a robust enterprise Wi-Fi network set up for industrial operations, the ability to specifically target and connect to the correct data path is non-negotiable. For AI-powered autonomous flight, where the drone might make real-time decisions based on streamed sensor data and pre-programmed parameters, the underlying network, specified by its name, ensures the integrity and timeliness of critical information exchanges, directly impacting the drone’s ability to navigate, avoid obstacles, and execute its mission autonomously.
Securing Your Network Name: A Critical Layer in Tech and Drone Operations
In an age rife with cyber threats, understanding and implementing network security best practices is no longer optional; it’s imperative. This holds true for general technology use and is particularly critical for drones, where unauthorized access can have severe consequences, ranging from privacy breaches to potential safety hazards.
The Perils of Unsecured Networks: Data Breaches and Unauthorized Access
An unsecured network, easily identifiable by its network name (SSID), presents an open invitation to malicious actors. For a typical home network, this could lead to data theft, compromised personal information, or unauthorized use of bandwidth. For businesses, the risks escalate to corporate espionage, intellectual property theft, and operational disruption. The principle extends directly to drone technology. If a drone’s control or data link is unsecure or uses easily guessed network names and passwords, it becomes vulnerable. An attacker could potentially intercept video feeds, disrupt flight, gain access to sensitive collected data (e.g., mapping data of private property), or even commandeer the drone, turning it into a tool for illicit activities. The network name, while an identifier, must always be paired with strong authentication mechanisms.
Best Practices for Protecting Your Drone’s Network
Protecting a drone’s network involves a multi-layered approach, starting with the very concept of its network name:
- Strong Passwords and Encryption: The most fundamental step is to protect any Wi-Fi network (whether for a smart controller or a direct drone link if applicable) with a strong, complex password using WPA2 or, ideally, WPA3 encryption. Never use default passwords.
- Unique and Obscure SSIDs (for general Wi-Fi): While hiding an SSID isn’t a security panacea (it can still be discovered), using a unique, non-obvious SSID for home or operational Wi-Fi networks can deter casual snoopers. Avoid using personal information in the network name.
- Understanding Network Types: Drones often operate in various network modes:
- Infrastructure Mode: Connecting to an existing router (e.g., a smart controller connecting to home Wi-Fi). Here, the router’s security is key.
- Ad-Hoc/Direct Mode: The drone or controller creates its own peer-to-peer network (e.g., drone-to-controller link). These typically rely on proprietary security or pre-shared keys. Ensure these are robust.
- Public Wi-Fi Avoidance: For sensitive drone operations or data transfer, avoid connecting drone controllers to public, unsecured Wi-Fi networks, as these are common targets for eavesdropping.
- Regular Firmware Updates: Keep drone, controller, and smart device firmware up to date. Manufacturers frequently release updates that patch security vulnerabilities in network protocols and communication layers.
- VPN Usage for Sensitive Data: When a drone controller connects to the internet for uploading sensitive data, utilizing a Virtual Private Network (VPN) can encrypt the data traffic, adding an extra layer of security beyond the local network’s protection.
By adhering to these practices, users can significantly mitigate the risks associated with drone connectivity, ensuring both operational integrity and data privacy.
The Evolution of Network Identification in Advanced Drone Systems
As drone technology continues its rapid advancement, moving towards greater autonomy, swarm intelligence, and integration into national airspace, the role of network identification is also evolving. Future drone systems will rely on increasingly sophisticated networking paradigms, each with its own approach to naming and identifying connections.
From Local Wi-Fi to Global Connectivity: Cellular and Satellite Integration
While current consumer drones largely rely on direct Wi-Fi or proprietary radio links, and smart controllers utilize standard Wi-Fi, the future of drone operations, particularly for commercial and industrial applications, is shifting towards broader network integration. Long-range Beyond Visual Line of Sight (BVLOS) operations, delivery services, and vast-area inspections necessitate persistent, global connectivity.
This is where cellular (4G, and increasingly 5G) and satellite communication enter the picture. With cellular integration, a drone becomes another node on the mobile network, identified by an IMSI (International Mobile Subscriber Identity) tied to its SIM card, and communicates through specific APNs (Access Point Names) defined by the carrier. These identifiers replace or augment traditional Wi-Fi SSIDs, offering vastly increased range and bandwidth. Similarly, satellite communication provides truly global reach, identifying drones through dedicated satellite modems and network access credentials. These advanced connectivity options open doors for unprecedented autonomous operations, remote monitoring, and real-time decision-making across vast distances, fundamentally altering how we perceive “network names” in a drone context from a localized SSID to a global mobile identity.
Mesh Networks and Swarm Intelligence: Decentralized Identification
The concept of drone swarms, where multiple UAS coordinate their actions autonomously, represents a significant leap in drone innovation. These swarms often communicate via mesh networks, a decentralized architecture where each drone acts as a relay, extending the network’s range and robustness. In such systems, the idea of a single “network name” becomes more complex. Instead, each drone within the swarm maintains its own unique identifier and understands the identities of its peers. The “network” is defined by the collective, self-forming connections, rather than a single access point broadcasting an SSID.
This decentralized identification is critical for enabling swarm intelligence, allowing drones to share sensor data, synchronize flight paths, and collaboratively accomplish missions, even if individual drones momentarily lose connection to a central ground station. The underlying technology might involve specialized radio protocols where network names are dynamically assigned or discovered, ensuring seamless communication and resilience in dynamic, multi-drone environments. This push towards distributed intelligence is a core area of “Tech & Innovation,” challenging traditional notions of network naming.
The Future of Drone Connectivity: Standardizing Identities for UTM and BVLOS
As drone traffic proliferates, the need for safe and efficient integration into national airspace becomes paramount. This has led to the development of Unmanned Aircraft System Traffic Management (UTM) systems, which aim to manage and coordinate drone flights, similar to air traffic control for manned aircraft. A crucial component of UTM is the ability to uniquely identify and track every drone in the sky.
Here, the concept of a “network name” evolves into standardized digital identification broadcast by the drone itself. Initiatives like Remote ID (Remote Identification) mandate that drones continuously broadcast their identity (serial number, operator ID), location, and other telemetry data over publicly available spectrum or through networked services. This broadcast identity acts as a universally recognizable “network name” for regulatory bodies, air traffic controllers, and other airspace users. For BVLOS operations, these broadcast identities are integral for collision avoidance systems and compliance with airspace regulations. The future of drone connectivity will rely heavily on these standardized, universally identifiable network “names” to ensure safety, foster innovation, and enable the full potential of drones for commerce, public safety, and beyond.
In conclusion, “what is a network name?” is far from a simple query. It’s a question that unlocks layers of understanding about digital connectivity, from the fundamental principles of Wi-Fi to the cutting-edge innovations driving autonomous drones. As technology advances, the forms and functions of network names will continue to evolve, but their core purpose—to uniquely identify and facilitate communication—will remain an indispensable pillar of our interconnected world, especially in the exciting and rapidly expanding domain of drone technology and innovation.
