In an increasingly interconnected digital world, the security of online communications is paramount. From personal banking to e-commerce, every interaction we have with websites relies on the underlying protocols that govern data exchange. For years, Hypertext Transfer Protocol (HTTP) served as the backbone of the web, but its inherent lack of security paved the way for various vulnerabilities. The introduction of Transport Layer Security (TLS), commonly known as SSL, marked a significant leap forward, encrypting data in transit and protecting against eavesdropping. However, even with TLS in place, a subtle but critical flaw persisted: the initial connection. This is where HTTP Strict Transport Security (HSTS) enters the picture, acting as a crucial directive that forces web browsers to interact with a website exclusively over secure HTTPS connections, fundamentally enhancing web security and user privacy.

HSTS, defined in RFC 6797, is a web security policy mechanism that helps protect websites from downgrade attacks and cookie hijacking. It works by instructing browsers that a website should only be accessed using HTTPS, eliminating the risk of unencrypted HTTP connections even if the user explicitly types http:// or clicks on an outdated http:// link. This proactive enforcement of secure connections closes a critical loophole, making the web a safer place for both users and service providers. Understanding HSTS is not just about comprehending another technical acronym; it’s about grasping a fundamental pillar of modern web security architecture that safeguards our digital interactions daily.
The Imperative for Secure Web Communication
The journey of web security began with a stark realization: unencrypted data is vulnerable data. While the internet was initially designed for information sharing, the proliferation of sensitive transactions and personal data online necessitated robust protection mechanisms.
The Vulnerabilities of Standard HTTP
HTTP, by its very design, transmits data in plain text. This means that any information exchanged between a user’s browser and a web server—from login credentials and credit card details to private messages—is readable by anyone who can intercept the traffic. This vulnerability opens the door to several types of attacks:
- Eavesdropping: Malicious actors can “listen in” on network traffic, easily capturing sensitive data as it travels across the internet.
- Tampering: Without encryption, an attacker could not only read but also modify data in transit, potentially altering transactions or injecting malicious code.
- Session Hijacking: Attackers can steal session cookies transmitted over HTTP, gaining unauthorized access to a user’s logged-in accounts.
- Man-in-the-Middle (MITM) Attacks: In an MITM attack, an adversary secretly relays and alters the communication between two parties who believe they are directly communicating with each other. For example, an attacker could intercept an HTTP connection, serving a fake website or redirecting the user to a malicious site without their knowledge.
These inherent weaknesses of HTTP made it clear that a more secure alternative was essential for the commercial and personal growth of the internet.
The Role of TLS/SSL in Securing Data
The answer arrived in the form of Transport Layer Security (TLS), the successor to Secure Sockets Layer (SSL). TLS/SSL certificates provide two primary functions: encryption and authentication.
- Encryption: When a website uses HTTPS (HTTP Secure), the communication channel between the browser and the server is encrypted. This scrambling of data ensures that even if an attacker intercepts the traffic, they cannot read its content without the decryption key.
- Authentication: TLS/SSL certificates also serve to authenticate the server. When a user connects to an HTTPS website, their browser verifies the certificate’s authenticity, ensuring they are connecting to the legitimate website and not an imposter. This helps prevent phishing and MITM attacks where an attacker tries to impersonate a legitimate site.
Despite the critical protection offered by TLS/SSL, a gap remained. Users could still initially connect to a website over HTTP, even if the site supported HTTPS. This initial unencrypted connection, often before a server-side redirect to HTTPS, was a prime target for downgrade attacks, where an attacker could force a browser to remain on the insecure HTTP connection. This “window of vulnerability” is precisely what HSTS was designed to close.
HSTS Explained: A Deep Dive
HTTP Strict Transport Security is a powerful mechanism designed to eliminate the reliance on client-side redirects from HTTP to HTTPS, ensuring that browsers always connect securely to a specified domain.
How HSTS Works: The Strict-Transport-Security Header
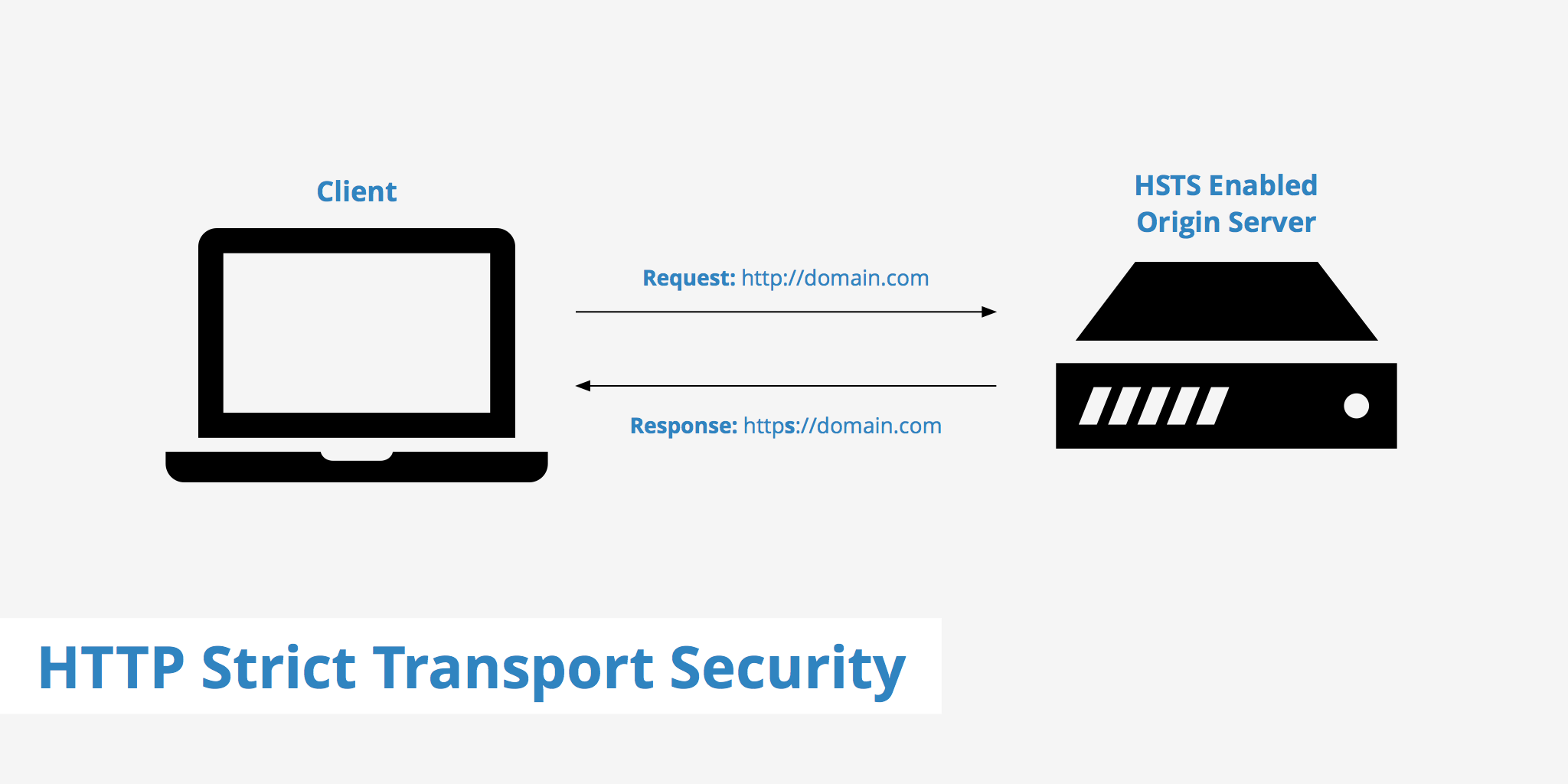
At its core, HSTS operates through a specific HTTP response header: Strict-Transport-Security. When a web server sends this header to a browser, it essentially gives the browser a strict instruction: “For a specified period, only communicate with this domain and its subdomains using HTTPS.”
Here’s a step-by-step breakdown:
- First Secure Connection: A user accesses a website, let’s say
https://example.com, for the first time. The connection must be HTTPS for HSTS to take effect. - HSTS Header Received: The server responds with the HSTS header, for instance:
Strict-Transport-Security: max-age=31536000; includeSubDomains. - Browser Stores Policy: The browser receives this header and stores the HSTS policy for
example.com(and its subdomains, if specified) for the duration indicated bymax-age. - Future Requests Enforced: For all subsequent attempts to access
example.com(or its subdomains) within themax-ageperiod, the browser will automatically convert anyhttp://request into anhttps://request internally before sending it over the network. It will also block any attempt to connect over HTTP or if the SSL certificate is invalid, preventing users from bypassing security warnings.
This means that even if a user types http://example.com or clicks a link pointing to http://example.com, the browser will automatically upgrade the connection to HTTPS without ever sending an insecure request to the server. This completely bypasses the initial HTTP-to-HTTPS redirect, eliminating the opportunity for downgrade attacks during that crucial first interaction.
Preloading HSTS for Enhanced Protection
While the HSTS header provides significant protection after the first secure visit, the “first visit problem” still exists. A user’s very first interaction with a site might still be vulnerable if they initially try an HTTP connection. To address this, the HSTS preload list was created.
The HSTS preload list is a hardcoded list of domains directly embedded into major web browsers (like Chrome, Firefox, Edge, Safari, and Opera). If a domain is on this list, browsers will always connect to it via HTTPS, even on the very first visit, effectively eliminating the initial vulnerability.
For a website to be included in the HSTS preload list, it must meet specific criteria, including:
- Serving a valid TLS certificate.
- Redirecting all HTTP traffic to HTTPS.
- Serving the HSTS header with a sufficiently long
max-age(typically one year or more). - Including the
includeSubDomainsdirective. - Including the
preloaddirective.
Being on the preload list offers the strongest form of HSTS protection, as it ensures that browsers are aware of the secure-only policy even before ever communicating with the website.
Directives and Configuration: max-age, includeSubDomains, preload
The Strict-Transport-Security header contains specific directives that define its behavior:
max-age=<seconds>: This is a mandatory directive that specifies the duration (in seconds) for which the browser should remember that the site is HTTPS-only. A longermax-ageprovides longer-lasting protection. For the HSTS preload list, amax-ageof at least 31536000 seconds (one year) is typically required.includeSubDomains: This optional directive tells the browser that the HSTS policy applies to all subdomains of the current domain as well. For example, ifexample.comsends this directive, thenblog.example.comandshop.example.comwill also be forced to use HTTPS. This is crucial for comprehensive protection across an entire web presence.preload: This optional directive, if present, signals to browsers that the site owner consents to having their domain included in the HSTS preload list. This directive itself doesn’t cause preloading; it’s an attestation for the preload list submission process.
Proper configuration of these directives is critical for effective HSTS implementation, ensuring the desired level of security and coverage.
Benefits and Impact of Implementing HSTS
Implementing HSTS goes beyond merely redirecting traffic to HTTPS; it fundamentally shifts the security posture of a website, offering a multitude of benefits for both service providers and end-users.
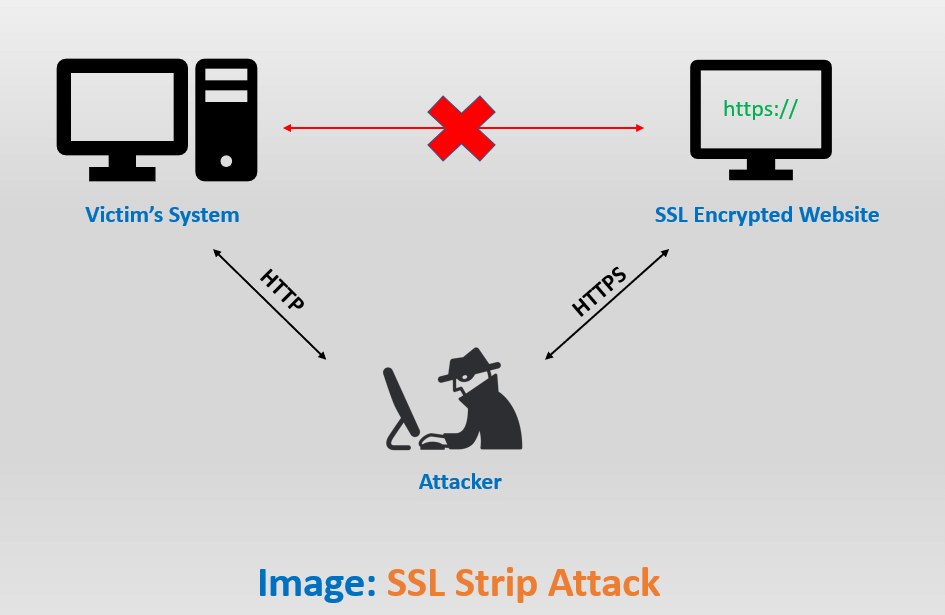
Preventing Man-in-the-Middle (MITM) Attacks
One of the most significant advantages of HSTS is its robust defense against certain types of Man-in-the-Middle (MITM) attacks. Without HSTS, an attacker positioned between a user and a server could intercept an initial HTTP request, even if the site supports HTTPS. The attacker could then potentially downgrade the connection to an insecure HTTP session, or present a forged SSL certificate, thereby capturing sensitive data.
HSTS thwarts these attacks by forcing the browser to always initiate an HTTPS connection to the specified domain. If an attacker tries to intercept the connection and downgrade it to HTTP, or if they attempt to present an invalid or untrusted certificate, the HSTS-aware browser will simply refuse to connect, displaying a severe error message and preventing the user from proceeding. This proactive enforcement ensures that an MITM attacker cannot trick the browser into communicating insecurely.
Enhancing User Trust and Data Privacy
In an era of increasing data breaches and privacy concerns, demonstrating a commitment to security builds user trust. By implementing HSTS, website owners signal to their users that they prioritize secure communication and the protection of their data. Users benefit from knowing that their sensitive information, such as login credentials, financial details, and personal data, is consistently encrypted and protected from interception.
This enhanced data privacy contributes to a safer online experience. Users don’t have to worry about accidentally navigating to an unencrypted version of a site or falling victim to attacks that exploit the initial insecure connection. HSTS makes secure browsing a default, seamless experience, reducing user anxiety and fostering confidence in online services.
Improving Performance through Secure-by-Default Connections
While often overlooked, HSTS can also contribute to a subtle improvement in website performance. Without HSTS, a user who attempts to access a site via HTTP is first sent to the HTTP server, which then issues a 301 or 302 redirect to the HTTPS version of the site. This process involves an additional round-trip between the browser and the server.
With HSTS, particularly when a site is on the preload list, the browser never initiates an insecure HTTP request. It internally converts the request to HTTPS from the outset. This eliminates the need for the HTTP-to-HTTPS redirect, saving a round-trip network request. Although this might seem like a minor optimization, for high-traffic sites or users on high-latency networks, these saved milliseconds can contribute to a slightly faster and more responsive browsing experience. Moreover, it reduces the server load associated with handling and redirecting HTTP requests.
Implementation Considerations and Best Practices
While HSTS offers substantial security benefits, its implementation requires careful planning and adherence to best practices to avoid potential issues and ensure seamless operation.
Gradual Rollout and Monitoring
Implementing HSTS, especially with a long max-age, is a significant commitment. A misconfigured HSTS policy can render a website inaccessible if not properly handled. Therefore, a gradual rollout strategy is highly recommended:
- Start with a short
max-age: Begin with a very shortmax-age(e.g., 5 minutes or 300 seconds). This allows administrators to test the policy and quickly revert if any issues arise, as the browser will forget the policy after a short period. - Monitor diligently: Closely monitor website traffic, error logs, and user feedback during the initial rollout phase. Look for any reported access issues or unexpected behavior.
- Increase
max-ageprogressively: Once confidence is established with a shortmax-ageand no issues are detected, gradually increase it over time (e.g., to 1 day, then 1 week, then 1 month, and finally to a year or more for preload eligibility). - Consider
includeSubDomainslast: Only add theincludeSubDomainsdirective after confirming that all subdomains also support HTTPS and have valid certificates. This is crucial as a broad HSTS policy can make an insecure subdomain completely inaccessible.
This phased approach minimizes risk and provides ample opportunity to identify and resolve problems before committing to a long-term HSTS policy.
Managing HSTS Across Subdomains and Different Services
Managing HSTS effectively becomes more complex for organizations with numerous subdomains, separate applications, or services hosted on different servers.
- Comprehensive HTTPS Coverage: Before implementing
includeSubDomains, ensure that every single subdomain, including legacy systems or forgotten micro-sites, is fully accessible over HTTPS with a valid, non-expired certificate. An insecure subdomain caught under anincludeSubDomainsHSTS policy will become completely unreachable for users with a cached HSTS policy, leading to a “This site can’t be reached” error. - Certificate Management: A robust certificate management process is essential. All certificates for all domains and subdomains must be kept up-to-date and valid. If a certificate expires or becomes invalid, users with an HSTS policy will be locked out of the site until the issue is resolved and the policy’s
max-ageexpires (or is explicitly cleared by the user). - Third-party Services: Be mindful of third-party services (e.g., CDNs, analytics, ad networks) that might be loaded from different domains or subdomains. Ensure they also use HTTPS. While HSTS primarily protects the main domain, mixed content warnings can still arise if third-party resources are loaded over HTTP.
Careful auditing of the entire web presence is a prerequisite for a successful and robust HSTS implementation.
Potential Pitfalls and Troubleshooting
Despite its benefits, HSTS can introduce challenges if not handled correctly:
- “Bricking” a website: The most significant pitfall is inadvertently applying a long
max-ageHSTS policy without all subdomains being HTTPS-ready. This can “brick” access for users, as their browsers will refuse to connect to any HTTP resources for the duration of the policy. - Certificate Errors: Expired or invalid TLS certificates on an HSTS-enabled site will prevent access, as browsers are forced to reject insecure connections. Ensure robust monitoring and auto-renewal for certificates.
- Development Environments: Be cautious when developing or testing on domains that are part of an HSTS policy (especially with
includeSubDomains). Browsers might enforce HTTPS, complicating local testing with self-signed certificates or HTTP-only environments. Clearing HSTS cache in the browser (often via browser developer tools or flags) can be necessary for testing. - Legacy Browser Support: While widely supported by modern browsers, very old browsers might not recognize the HSTS header, leaving those users vulnerable. This is becoming less of an issue as older browsers are phased out.
Effective troubleshooting involves checking server configurations, reviewing certificate validity, analyzing browser console errors, and potentially using HSTS testing tools to verify proper header delivery and configuration.
The Future of Web Security and HSTS’s Evolving Role
HTTP Strict Transport Security has profoundly impacted web security, transitioning from an optional enhancement to a de facto standard for secure websites. Its continued relevance is assured as the internet evolves towards a more private and secure paradigm.
Integration with Modern Security Protocols
HSTS works in concert with a suite of other modern security protocols to form a multi-layered defense. It complements TLS 1.3, the latest and most secure version of the encryption protocol, by ensuring that connections are always initiated using the strongest available encryption. It also pairs well with Content Security Policy (CSP), which helps mitigate cross-site scripting (XSS) and other content injection attacks by defining which dynamic resources are allowed to load.
Looking ahead, HSTS will likely remain a foundational component. As new HTTP versions like HTTP/3 (which uses QUIC, built on UDP) become prevalent, the principle of strict transport security will continue to be crucial. While the underlying transport mechanisms may change, the need to enforce encrypted communication from the very first byte will persist. HSTS provides an abstraction layer that allows browsers to maintain this enforcement regardless of the specific network protocol beneath.
The Push Towards a Fully Encrypted Web
The ultimate goal for many internet advocates and major technology companies is a fully encrypted web—a scenario where all web traffic is HTTPS by default. HSTS is a powerful driver towards this vision. By making HTTPS the mandatory norm for participating websites, it reduces the attack surface across the internet significantly. Initiatives like “HTTPS Everywhere” and the efforts by browser vendors to flag HTTP sites as “not secure” reinforce this push.
The widespread adoption of HSTS, especially with more domains joining the preload list, means that a larger portion of user interactions with the web are inherently secure from the outset. This not only protects individual users but also raises the bar for security across the entire ecosystem, making the internet a more trustworthy environment for commerce, communication, and information exchange. As privacy concerns escalate and cyber threats grow more sophisticated, the simple yet effective mechanism of HSTS will continue to play a vital, unwavering role in building and maintaining a truly secure web.
