In an era defined by digital transformation and an ever-increasing reliance on interconnected systems, data has unequivocally become the new currency. From personal photographs to proprietary business strategies, the information stored on our devices is invaluable, and its protection paramount. It is within this critical context that disk encryption technologies, like Microsoft’s BitLocker, emerge as foundational components of modern cybersecurity. At the heart of BitLocker’s protective mechanism lies a seemingly simple yet profoundly vital component: the BitLocker key. Understanding what a BitLocker key is, how it functions, and why its secure management is non-negotiable, is fundamental for anyone navigating today’s digital landscape. This article will delve into the intricacies of this essential security element, framing its importance within the broader scope of tech innovation and responsible data stewardship.
Understanding BitLocker: A Foundation of Data Security
BitLocker Drive Encryption is a full-disk encryption feature included with Microsoft Windows versions starting with Vista. Its primary purpose is to protect data by encrypting entire volumes on your hard drive, thereby preventing unauthorized access to your files, even if your device is lost, stolen, or tampered with. It integrates seamlessly with the Windows operating system, offering a robust layer of defense against data breaches and ensuring confidentiality.
The Role of Encryption in Modern Computing
Encryption, at its core, is the process of converting information or data into a code to prevent unauthorized access. In the context of modern computing, where devices are frequently mobile and susceptible to physical compromise, encryption acts as a last line of defense. Should a laptop be stolen, for instance, a thief might gain access to the hardware, but without the appropriate decryption key, the data stored on the hard drive remains an unreadable jumble of encrypted characters. This renders the data useless to the perpetrator, effectively safeguarding privacy and sensitive information. BitLocker achieves this by encrypting all user files, system files, and the operating system itself, ensuring comprehensive protection from the moment the device is powered on. This proactive approach to data security is increasingly important as the volume and sensitivity of digital information continue to grow across all sectors of tech and innovation.
How BitLocker Works at a High Level
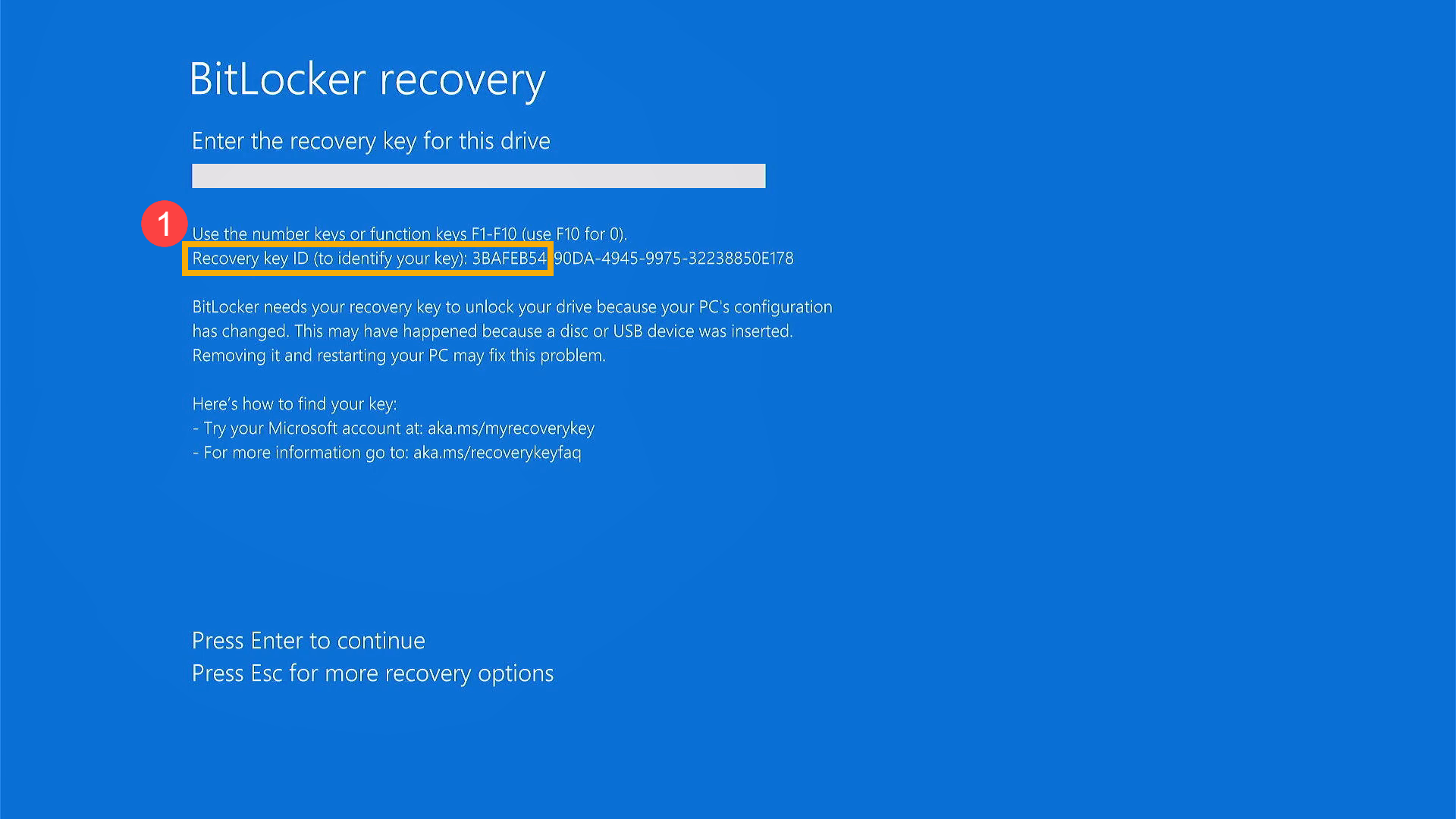
When BitLocker is enabled on a drive, it utilizes a strong encryption algorithm (AES, typically with 128-bit or 256-bit keys) to scramble all the data on that volume. The encryption process itself is often tied to a Trusted Platform Module (TPM) chip, a specialized microcontroller that secures hardware with integrated cryptographic keys. The TPM checks the integrity of the boot process, ensuring that no malicious software has tampered with the system before unlocking the drive. If the TPM detects any changes, it will not release the encryption key, requiring the user to provide a recovery key. This multi-layered approach ensures that the data remains locked unless the system is in its expected, secure state or an authorized user intervenes with the correct key. This sophisticated interaction between hardware and software underscores BitLocker’s role as a cornerstone in robust endpoint security.
The Core Purpose of a BitLocker Key
While the TPM handles much of the automated key management, there are specific scenarios where a direct interaction with a “BitLocker key” becomes necessary. This is where the concept of the recovery key primarily comes into play – a critical element designed to provide access when standard authentication methods fail or are unavailable.
The Master Key to Your Encrypted Drive
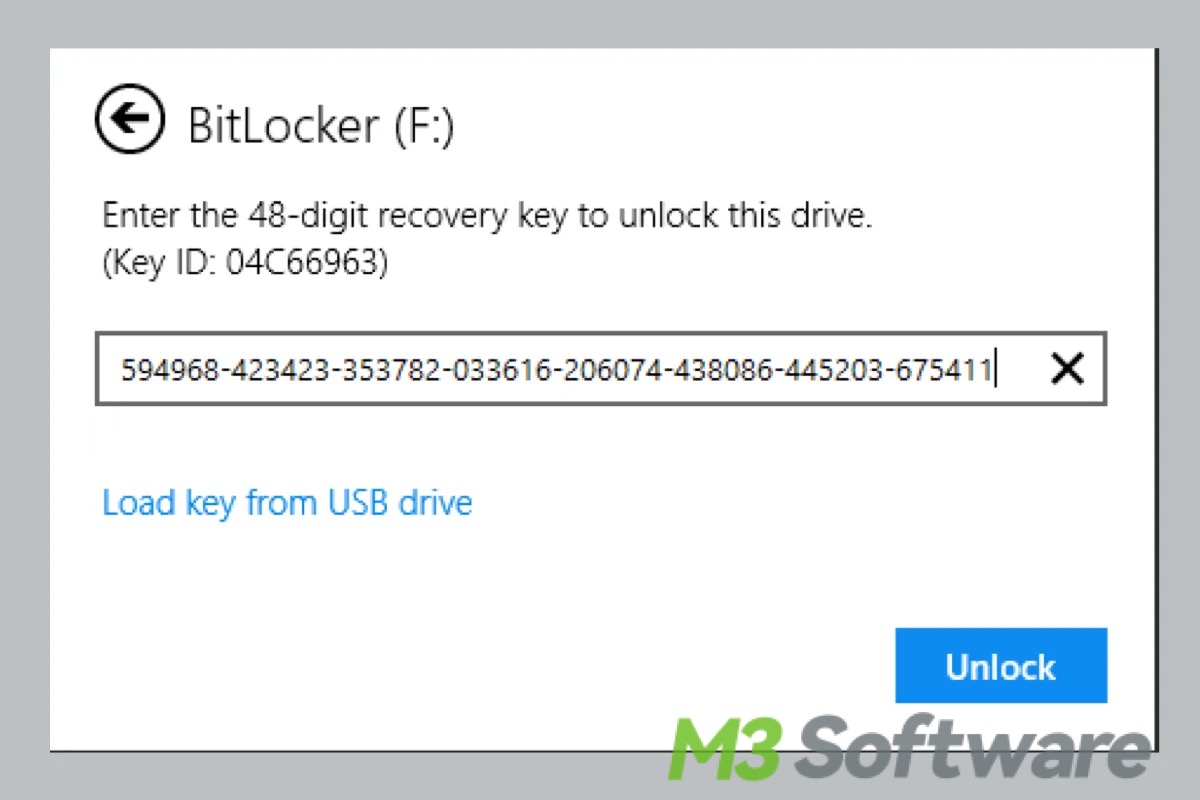
Fundamentally, a BitLocker key, often referred to as a BitLocker recovery key, is a unique, 48-digit numerical password. This key is generated during the BitLocker setup process and is absolutely essential for decrypting your drive if the normal startup process fails. It serves as the ultimate master key, capable of unlocking your encrypted data even if your computer’s configuration changes, the TPM detects a security threat, or you forget your PIN or password. Without this specific key, your encrypted data can become permanently inaccessible, effectively turning your stored information into an unbreakable digital vault with the key thrown away. Its existence highlights the careful balance between robust security and necessary recoverability, a common challenge in advanced tech solutions.
Why You Might Need Your Recovery Key
There are several common scenarios where you might be prompted to enter your BitLocker recovery key:
- Hardware Changes: Upgrading your motherboard, changing your BIOS/UEFI settings, or even specific firmware updates can trigger the TPM to consider the system configuration as altered, thus requesting the recovery key.
- Security Concerns: If the TPM detects an attempt to bypass security checks or if the boot order is unexpectedly changed, it will prompt for the key.
- Forgotten Passwords/PINs: If you use a password or PIN to unlock your BitLocker drive and you forget it, the recovery key is your fallback.
- Operating System Issues: In cases of OS corruption or significant boot problems, the system might revert to requesting the recovery key to ensure data integrity before granting access.
- System Restore/Reset: Performing certain system recovery operations might also necessitate the key.
In essence, the recovery key acts as an emergency bypass, a failsafe mechanism that ensures legitimate users can regain access to their data under challenging circumstances, without compromising the overall security model.
Types of BitLocker Keys and Where to Find Them
While the 48-digit recovery key is the most commonly discussed “BitLocker key,” it’s important to understand the broader ecosystem of key management within the BitLocker framework.
The Recovery Key: Your Lifeline
As discussed, the 48-digit recovery key is paramount. During the BitLocker setup, Windows provides several options for saving this key, acknowledging its critical importance:
- Save to a Microsoft Account: For personal devices, this is often the most convenient and recommended method. The key is securely stored in your Microsoft account online (account.microsoft.com/devices/recoverykey).
- Save to a USB Flash Drive: The key can be saved as a text file to a removable USB drive. This offers offline storage but requires careful physical security of the USB drive.
- Save to a File: You can save the key as a text file to a network drive or another non-encrypted location. This is often used in corporate environments for centralized management.
- Print the Recovery Key: A physical printout provides an offline, hardcopy backup. This should be stored in a secure, fireproof location, like a safe.
It is crucial to choose at least one, and preferably multiple, secure methods for storing this key. Losing it effectively means losing access to your data forever.
Other Key Management Options
Beyond the recovery key, BitLocker employs other methods for managing and unlocking access:
- Trusted Platform Module (TPM): As mentioned, the TPM is the default and most transparent method. It securely stores the primary encryption key and releases it automatically if the system’s integrity checks pass, requiring no user input.
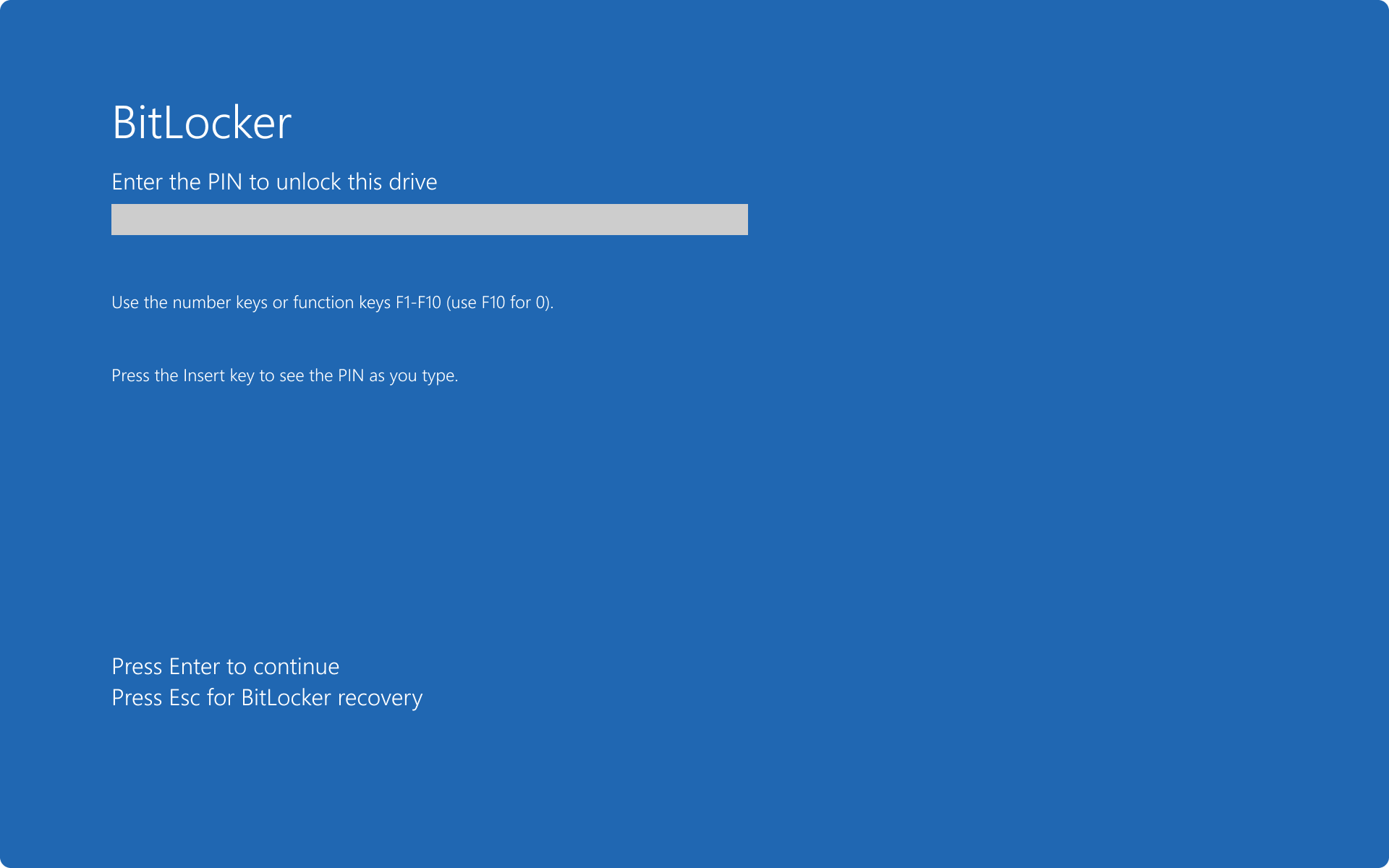
- PIN/Password: Users can configure a PIN or alphanumeric password to be entered at boot time, in addition to or instead of TPM-based unlocking. This adds an extra layer of authentication, especially important if the TPM itself is compromised.
- USB Startup Key: A USB flash drive can be used as a “startup key.” The encryption key is stored on this USB, and it must be inserted into the computer during startup for the drive to unlock.
- Network Unlock: In enterprise environments, BitLocker can be configured for Network Unlock, allowing encrypted systems to automatically unlock when connected to a trusted corporate network, using a server-based key.
These diverse methods cater to different security requirements and operational contexts, from individual users to large organizations, showcasing BitLocker’s flexibility as a robust technology solution.
Common Locations to Store Your Recovery Key
Effective key management is as crucial as the encryption itself. Here’s a summary of common and recommended places:
- Microsoft Account: This is generally the easiest and most reliable for personal use. Ensure your Microsoft account itself is secured with multi-factor authentication.
- Company/Organizational IT Department: For business devices, IT administrators often store BitLocker keys in Active Directory or specialized key management systems. Contact your IT department if you’re using a company-issued device.
- USB Flash Drive: A dedicated USB drive kept in a secure, separate location from the computer.
- Printed Copy: Stored in a physical safe, locked drawer, or secure filing cabinet.
- Cloud Storage (Encrypted): If using a third-party cloud storage solution, ensure the file containing the key is further encrypted before upload.
Never store the recovery key on the same encrypted drive, or an easily accessible, unencrypted location on the same machine. This defeats the purpose of the encryption.
Best Practices for Managing Your BitLocker Keys
The power of BitLocker lies in its robust encryption, but its usability hinges entirely on the proper management of its keys. Neglecting key management can lead to permanent data loss, a scenario that no amount of advanced technology can reverse.
Secure Storage Strategies
The cardinal rule of BitLocker key management is to keep the recovery key secure and separate from the device it encrypts. For home users, storing it in a Microsoft account is highly recommended, paired with a strong, unique password and two-factor authentication for that account. For a physical copy, consider a fireproof safe at home or a secure deposit box. In professional settings, IT departments often leverage Active Directory for automatic key escrow, centralizing recovery key storage for managed devices. This allows for quick recovery by authorized personnel while maintaining a high level of security. Regular audits of key storage locations and access controls are also vital to ensure ongoing compliance and prevent unauthorized access.
Regular Verification and Backup
It’s not enough to simply save your recovery key once. Technology evolves, and storage methods can degrade or be misplaced. Periodically verifying that your saved key is correct and accessible is a critical best practice. You can test a printed key by typing it into a temporary lockout prompt (if you can simulate one safely) or simply retrieving it from your Microsoft account to confirm it’s there. Additionally, if you re-encrypt a drive or significantly alter BitLocker settings, it’s wise to generate and save a new recovery key. Treating your recovery key like an important physical document (passport, deed, etc.) reinforces the necessary diligence.
The Dangers of Losing Your Key
The stark reality is that if you lose your BitLocker recovery key and are unable to access your device through other means (like a PIN or TPM), your data will be irrecoverable. BitLocker is designed to be extremely resilient against brute-force attacks and decryption without the key. This robust security, while desirable for data protection, becomes an insurmountable barrier if the legitimate owner loses the master key. This irreversible consequence underscores why BitLocker key management isn’t just a technical detail but a crucial aspect of personal and organizational data governance, often requiring clear policies and user education.
When and Why BitLocker is Essential for Tech & Innovation
BitLocker, while a mature technology, remains an indispensable tool, particularly as technology continues to innovate and proliferate into new domains. Its foundational role in data security underpins many aspects of modern tech.
Protecting Sensitive Data in a Connected World
In a world increasingly dominated by mobile devices, cloud computing, and the Internet of Things (IoT), data traverses vast networks and resides on numerous endpoints. BitLocker serves as a critical defense for the endpoints themselves – laptops, tablets, and even specialized devices running Windows. Whether it’s protecting intellectual property on an engineer’s workstation, patient data on a hospital’s mobile clinic device, or financial records on a remote employee’s laptop, BitLocker ensures that sensitive information is not exposed if the physical device falls into the wrong hands. This is particularly relevant as remote work becomes standard and devices move beyond the physical security of an office.
Compliance and Regulatory Requirements
Many industries are subject to stringent data protection regulations, such as GDPR, HIPAA, and various national cybersecurity frameworks. These regulations often mandate the encryption of sensitive data, especially on portable devices. Implementing BitLocker is a straightforward and effective way for organizations to meet these compliance requirements, demonstrating a commitment to data privacy and security. The ability to centrally manage BitLocker and its keys (e.g., through Active Directory and Microsoft Endpoint Manager) makes it a favored solution for enterprises striving for regulatory adherence and strong data governance.
Mitigating Risks in Autonomous Systems and IoT
While not directly operating on consumer IoT devices, the principles of BitLocker-like encryption are highly relevant to the broader ecosystem of autonomous systems and industrial IoT. These advanced systems often rely on embedded Windows machines or similar operating systems for control, data processing, and telemetry. Protecting the data and the integrity of the operating environment on these critical nodes is paramount. For example, in an autonomous vehicle, the onboard computer may store critical mapping data, sensor logs, and system configurations. Encrypting these drives with robust mechanisms similar to BitLocker can prevent malicious actors from extracting sensitive information or tampering with the system’s operational parameters, safeguarding both data and system functionality. As tech innovation pushes boundaries, so too must the sophistication and application of data security solutions like BitLocker.
In conclusion, the BitLocker key is far more than a simple password; it is the linchpin of an advanced data protection system. Its existence underscores the critical importance of robust encryption in safeguarding digital assets in an increasingly complex and interconnected world. For individuals and organizations alike, understanding and meticulously managing these keys is not just a best practice, but an absolute necessity for maintaining digital security and integrity in the face of ever-evolving technological landscapes.
