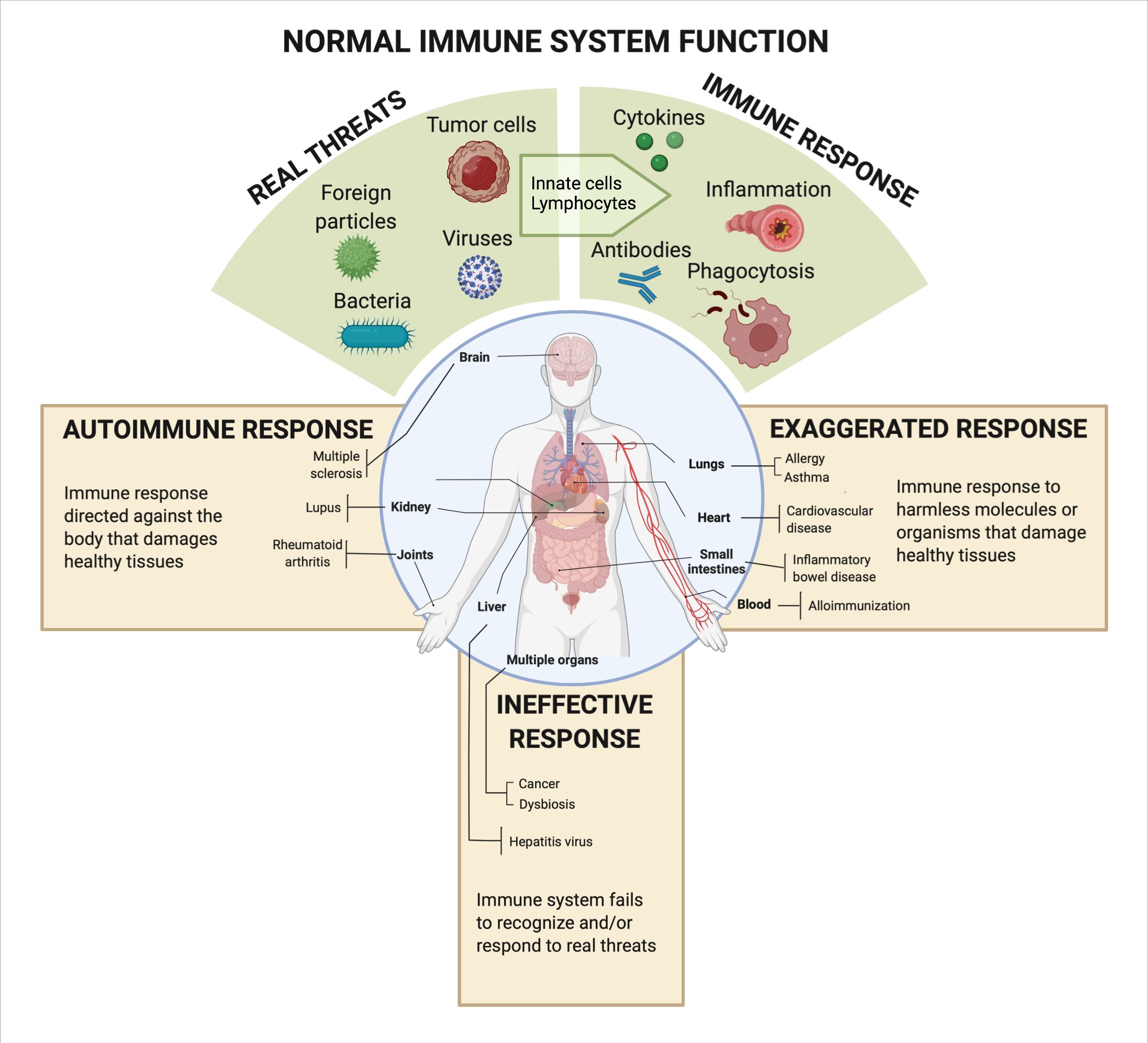
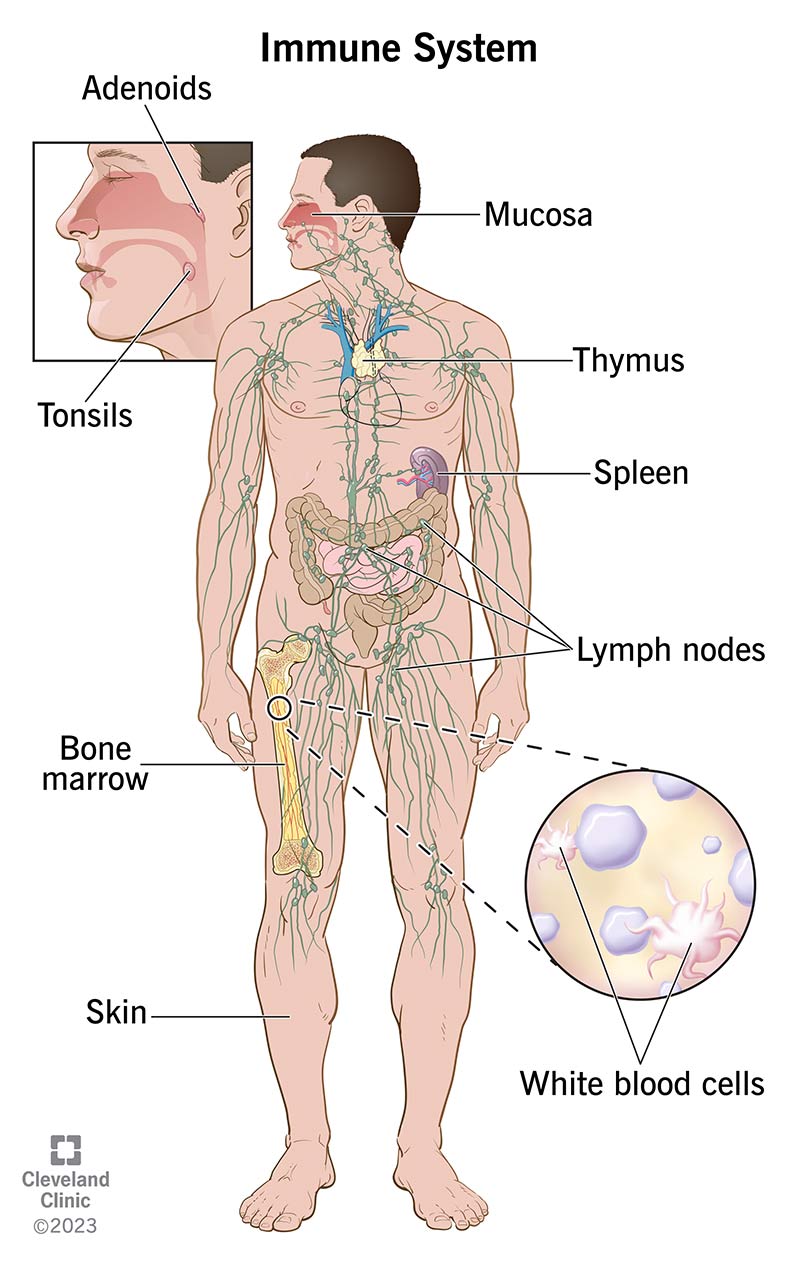
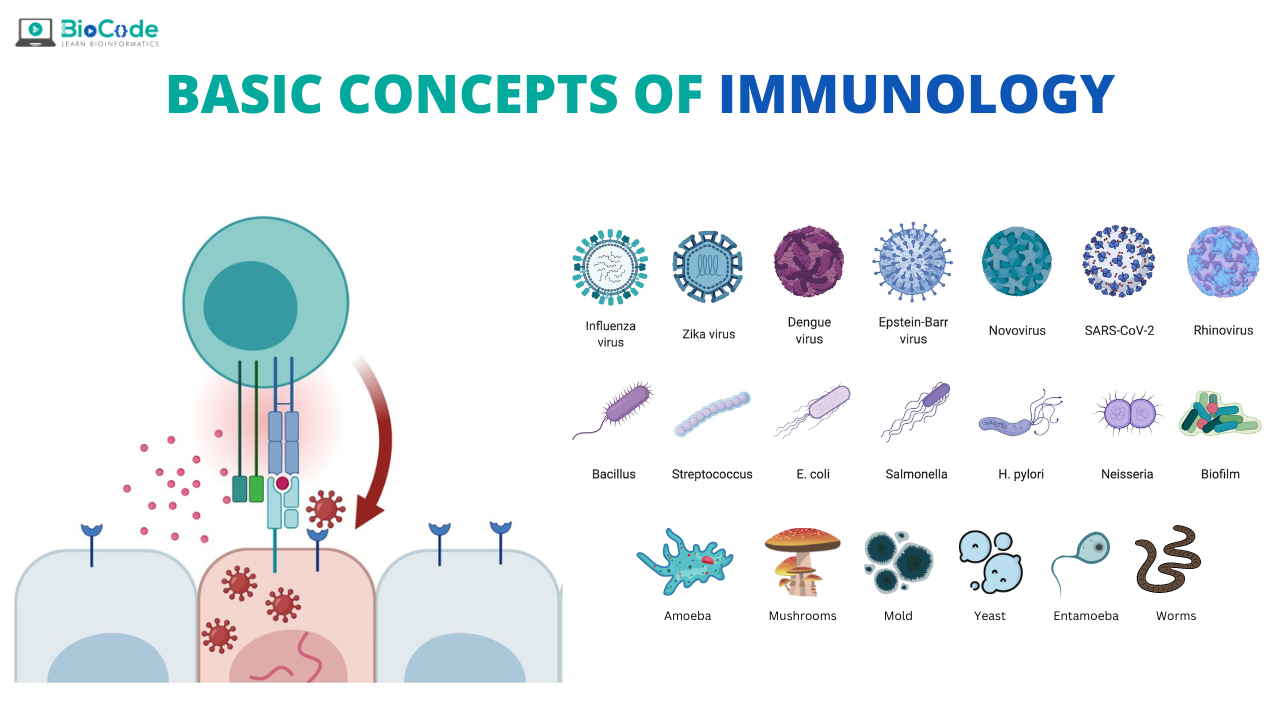
Immunology, in its original biological context, is the study of the immune system—a complex network of cells, tissues, and organs that work together to protect an organism from disease. It’s about distinguishing “self” from “non-self,” remembering past threats, and mounting targeted responses to maintain health and integrity. In the rapidly evolving landscape of modern technology, particularly with the proliferation of autonomous systems, robotics, and advanced AI, the principles underpinning biological immunity offer a powerful metaphor and a crucial design philosophy. This article explores “immunology” not as a biological science, but as a paradigm for building resilient, self-protecting technological systems—a concept we term “System Immunology.”
In an era where interconnectedness is pervasive, and systems operate with increasing autonomy, vulnerabilities multiply. From cyberattacks and software glitches to hardware failures and environmental disruptions, the integrity and operational continuity of critical technologies are under constant threat. Just as a biological organism requires an immune system to survive and thrive in a hostile microbial world, sophisticated technological systems need their own mechanisms for detection, defense, and recovery. This exploration delves into how the core tenets of immunology can inspire and inform the development of technologies that are not merely robust, but truly intelligent in their ability to preserve their own functionality and mission.
The Concept of “Immunity” in Technology
At its heart, “System Immunology” is the engineering discipline focused on designing and implementing technologies that can autonomously detect anomalies, identify threats, protect their operational integrity, and recover from disruptions. It’s about creating systems that are not only capable of performing their primary functions but are also inherently resilient, adaptive, and self-healing. This metaphorical leap from biology to technology recognizes the increasingly complex and dynamic environments in which modern tech operates.
Distinguishing Self from Non-Self
One of the most fundamental principles of biological immunology is the ability to differentiate between the body’s own cells and foreign invaders. In technological systems, this translates to differentiating between normal operational parameters, expected data patterns, and legitimate commands versus anomalous behavior, corrupted data, or malicious intrusions. For an autonomous drone, for instance, “self” includes its programmed flight path, expected sensor readings, and legitimate control signals. “Non-self” could be GPS spoofing attempts, unexpected turbulence readings not matching environmental data, or attempts to hijack its control link.
Memory and Learning
A key feature of adaptive immunity is immunological memory, where the immune system “remembers” pathogens it has encountered before, enabling a faster and more effective response upon subsequent exposure. In technological terms, this corresponds to systems that learn from past incidents. AI and machine learning play a pivotal role here, allowing systems to build a historical database of normal operations and deviations. When a new anomaly or attack pattern emerges, the system can leverage its “memory” of similar past events to identify, classify, and respond more efficiently, continuously refining its defensive strategies.
Proactive and Reactive Defenses
Biological immunity involves both innate (always active) and adaptive (learned) responses. Technologically, this means designing systems with both proactive and reactive defense mechanisms. Proactive measures might include robust encryption, secure boot processes, redundant hardware, and fault-tolerant software architectures that are always active. Reactive defenses, on the other hand, are triggered by detected threats, such as isolating compromised modules, initiating fail-safes, or altering operational modes to mitigate damage—much like antibodies targeting specific antigens.
Architecting Robustness: Principles of System Immunology
Building systems with an “immune system” requires a deliberate architectural approach that embeds resilience at every layer, from hardware to software and network infrastructure. It’s not an afterthought but a core design tenet.
Layered Defenses (Immune Barriers)
Just as the body has multiple layers of defense (skin, mucous membranes, cellular immunity), technological systems benefit from layered security and resilience. This includes physical security, robust network segmentation, strong access controls, data encryption, and application-level integrity checks. Each layer acts as a barrier, increasing the difficulty for threats to penetrate and compromise the system’s core functions. For a drone, this might mean secure hardware enclaves, encrypted communication links, and software that verifies the integrity of sensor data before execution.
Redundancy and Diversity (Distributed Immunity)
Biological systems often have redundant organs and diverse immune cell populations to ensure that even if one part fails or is overwhelmed, others can compensate. In technology, this translates to hardware redundancy (e.g., multiple flight controllers, backup power systems), software diversity (e.g., different algorithms for the same task), and geographical distribution for critical infrastructure. If one sensor or processing unit fails, a redundant component can seamlessly take over, preventing catastrophic system failure. This is particularly crucial for autonomous vehicles and critical infrastructure where downtime is unacceptable.
Autonomous Monitoring and Anomaly Detection (Immune Surveillance)
Continuous monitoring is the “surveillance” arm of system immunology. This involves real-time analysis of system performance metrics, network traffic, sensor data, and user activity to detect deviations from established baselines. Advanced analytics, machine learning algorithms, and behavioral profiling are employed to identify anomalies that could signify a fault, an intrusion, or an impending failure. For an autonomous drone, this could mean monitoring motor RPMs, battery drain rates, GPS signal quality, and control input consistency, flagging any parameter that falls outside predefined safe operating ranges or learned normal patterns.
Detecting and Responding to Threats: The Technological Immune Response
Once an anomaly or threat is detected, an effective immune system must be capable of mounting a timely and appropriate response. This often involves a multi-stage process, from initial containment to full recovery and learning from the event.
Containment and Isolation (Quarantine)
Upon detection of a threat, the immediate priority is to contain it and prevent its spread throughout the system. This can involve isolating compromised modules, segments, or processes, much like quarantining an infected individual. For network systems, this might mean dynamically reconfiguring firewalls to block suspicious traffic. In a modular robotic system, it could mean shutting down power to a faulty actuator or isolating a corrupted software component to prevent it from affecting critical flight controls.
Remediation and Self-Healing (Repair Mechanisms)
After containment, the system needs mechanisms to remediate the issue and restore normal functionality. This could range from rolling back to a previous stable configuration, patching vulnerabilities, or autonomously reconfiguring system parameters to bypass a damaged component. The concept of “self-healing” software, where errors are detected and corrected without human intervention, is a prime example of this. For a drone, if a sensor malfunctions, an immune-inspired system might automatically switch to a redundant sensor or use data fusion from other sensors to compensate, ensuring mission continuity.
Alerting and Reporting (Pathogen Identification)
While autonomous response is ideal, human oversight and intervention are often necessary for complex or novel threats. System immunology includes robust alerting mechanisms that inform human operators about critical incidents, providing detailed telemetry and diagnostic information. This is analogous to a doctor receiving a detailed report from a lab analysis identifying a specific pathogen. These reports are crucial for understanding the attack vectors, vulnerabilities exploited, and improving future system defenses.
Real-World Applications: Immune Systems for Drones and Robotics
The principles of System Immunology are particularly pertinent to autonomous systems like drones, which operate in dynamic and often unpredictable environments with minimal human intervention. Their missions frequently involve critical tasks, making resilience paramount.
Drone Cybersecurity
Drones are vulnerable to a myriad of cyber threats, including GPS spoofing, signal jamming, malware injection, and unauthorized access to control systems. An immunological approach to drone cybersecurity would involve:
- Secure Hardware Enclaves: Protecting critical firmware and cryptographic keys.
- Encrypted Communications: End-to-end encryption for command-and-control links and data telemetry.
- Anomaly Detection in Flight Data: AI algorithms monitoring flight paths, sensor readings, and control inputs for suspicious deviations that could indicate spoofing or hijacking.
- Autonomous Countermeasures: Systems capable of initiating emergency landings, returning to base, or activating jamming countermeasures upon detecting a confirmed threat.
Fault Tolerance in Autonomous Flight
Hardware failures (e.g., motor malfunction, battery degradation) and software bugs can have catastrophic consequences for drones. Immune-inspired fault tolerance includes:
- Redundant Flight Controllers: Multiple independent control units that can take over if one fails.
- Sensor Fusion with Anomaly Rejection: Using data from multiple, diverse sensors (e.g., GPS, inertial measurement units, vision cameras) and algorithms to detect and discard erroneous readings from a faulty sensor.
- Adaptive Flight Control: Algorithms that can reconfigure flight parameters to compensate for a damaged propeller or motor, maintaining stability and control.
- Self-Diagnosis and Predictive Maintenance: AI models analyzing operational data to predict component failures before they occur, scheduling proactive maintenance.
Ethical AI and Anomaly Resolution
As AI takes on more decision-making roles in autonomous systems, its integrity and ethical operation become critical. System immunology can help ensure that AI models do not operate outside their intended parameters or make biased decisions. This involves:
- Continuous AI Model Monitoring: Detecting drift in model performance or unusual outputs that could indicate data poisoning or adversarial attacks.
- Explainable AI (XAI): Providing insights into AI decision-making processes, allowing operators to understand why a system took a particular action, especially in critical situations.
- “Guardrail” AI: Implementing secondary AI systems or rule-based engines that act as watchdogs, ensuring the primary AI operates within predefined ethical and safety boundaries.
The Future of Self-Protecting Tech: Continuous Evolution
The field of System Immunology is not static; it is an evolving discipline that promises increasingly sophisticated self-protection capabilities for technological systems. As threats become more advanced and systems grow more complex, the need for inherent resilience will only intensify.
Collective Immunity (Swarm Intelligence)
Drawing another parallel from biology, where a population can develop “herd immunity,” future technological systems might leverage collective intelligence to enhance security. A swarm of drones, for example, could share threat intelligence and defensive strategies in real-time. If one drone detects a jamming signal or a GPS spoofing attempt, it could alert the entire fleet, allowing all units to adapt their navigation and communication protocols simultaneously, increasing the overall “immune response” of the collective.
Proactive Threat Anticipation (Anticipatory Immunity)
Beyond reacting to known threats, the next frontier involves systems that can anticipate potential vulnerabilities and threats. This requires sophisticated predictive analytics, threat intelligence fusion, and potentially even simulations of future attack scenarios to fortify defenses before attacks materialize. This anticipatory immunity would be crucial for protecting critical infrastructure, national security assets, and increasingly, our personal data and digital lives.
Human-Machine Collaboration (Immunological Partnership)
Ultimately, a truly robust technological immune system will involve seamless collaboration between autonomous capabilities and human intelligence. While AI can handle rapid detection and initial responses, human operators bring nuanced judgment, ethical considerations, and the ability to strategize against novel, complex threats. The “immunology” of technology is not about replacing human intervention entirely, but about creating intelligent systems that amplify human capabilities and safeguard the integrity of our digital and physical world.
In conclusion, reinterpreting “what is an immunology” within the domain of Tech & Innovation reveals a powerful framework for building the next generation of resilient, self-protecting technologies. By applying the biological principles of self-recognition, memory, adaptation, and coordinated response, we can design autonomous systems, robotics, and complex software infrastructures that are not only efficient and effective but also inherently capable of safeguarding their own existence and mission in an increasingly challenging operational environment. This “System Immunology” is poised to become a cornerstone of future innovation, ensuring our technological advancements are as robust as they are revolutionary.
