In the vast and ever-evolving landscape of technology and innovation, software stands as the pulsating heart, driving everything from the simplest applications to the most complex autonomous systems. At the very core of how this software comes to life on a Windows operating system lies a fundamental, yet often misunderstood, file type: the .exe file. Short for “executable,” these files are the digital commands that instruct your computer to perform a specific task, launch a program, or install a new piece of software. They are the initial spark that ignites the intricate processes within your machine, making them an indispensable element in the realm of modern computing and the engine behind countless technological advancements and innovations.
Understanding what an .exe file is, how it functions, and its role in the broader tech ecosystem is crucial for anyone engaging with technology, from end-users to software developers. It’s a concept that underpins the deployment of operating systems, the functionality of sophisticated AI algorithms, the processing power for remote sensing data, and the intricate control systems for advanced robotics and autonomous vehicles. This exploration will delve into the technical essence of .exe files, their pervasive impact on innovation, the critical security considerations they present, and their evolving place in the future of software deployment.
The Core of Software Execution: Understanding .exe Files
At its most basic, an .exe file is a program that a computer can directly run. It contains a sequence of instructions or commands that the computer’s processor can understand and execute. While seemingly simple, the journey from a programmer’s idea to a functional .exe file is a complex process that highlights foundational principles of computer science.
Defining the Executable
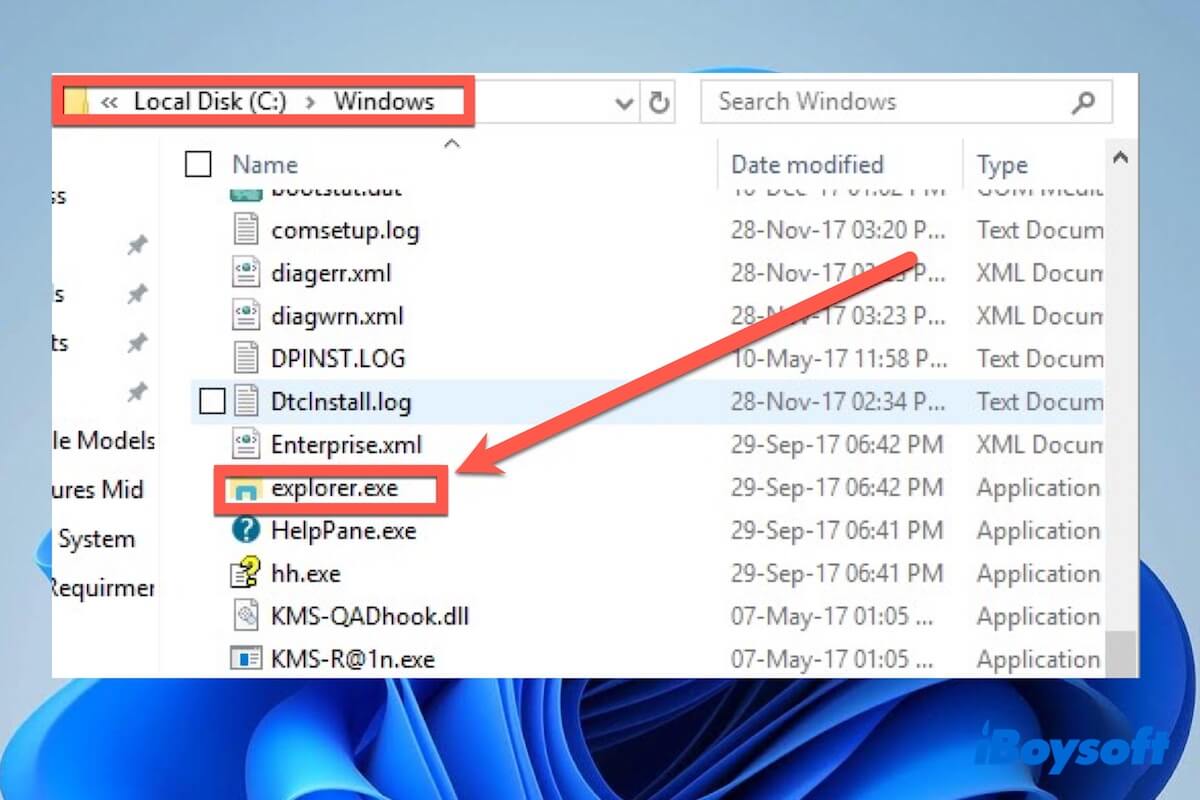
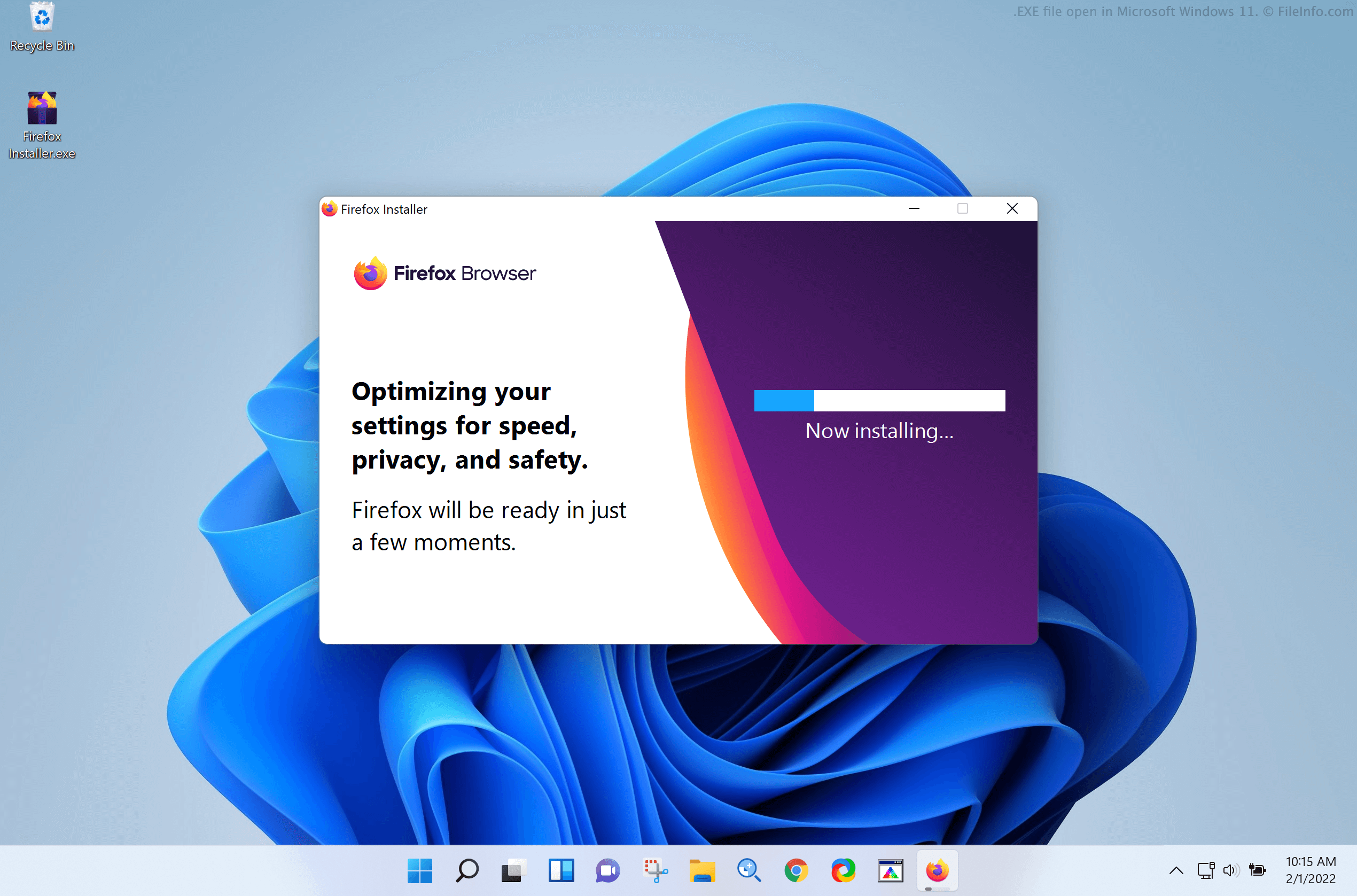
The .exe extension specifically denotes an executable file format used in Microsoft Windows, DOS, and OS/2 operating systems. Its primary function is to serve as the entry point for an application or process. When a user double-clicks an .exe file, or when a system process calls one, the operating system’s loader takes charge. It allocates memory, loads the file’s contents into that memory, and then directs the CPU to begin executing the instructions from a predefined starting point. This seemingly instantaneous action is the culmination of a sophisticated process that transforms human-readable code into machine-executable commands. Without this fundamental mechanism, the rich interactive experiences we associate with modern software would be impossible.
How an .exe File Works
The creation of an .exe file begins long before it ever lands on a user’s machine. Programmers write source code in high-level languages like C++, C#, Python, or Java. This human-readable code, however, cannot be directly understood by a computer’s processor. That’s where a crucial step called compilation comes in. A compiler is a specialized software tool that translates the source code into low-level machine code – binary instructions that the processor can directly interpret.
During compilation, the compiler also links various external libraries and resources that the program might need, such as functions for displaying graphics, managing network connections, or interacting with hardware. The result of this compilation and linking process is the .exe file. When the user initiates the .exe, the operating system’s program loader steps in. It parses the .exe file’s header to understand its structure, reserves the necessary memory, loads the machine code and data into that memory, and then prepares the execution environment. Finally, it passes control to the CPU, which begins fetching and executing the instructions embedded within the .exe file, bringing the software to life.
Components Within an Executable
An .exe file is not just a monolithic block of code; it’s a meticulously structured package containing several distinct components crucial for its operation.
- Code Segment (.text): This section contains the actual machine instructions that the CPU will execute. It’s the compiled version of the programmer’s algorithms and logic.
- Data Segment (.data, .rdata, .bss): This segment holds the program’s static data, such as global variables, constants, and string literals. It’s further divided into initialized data (e.g., pre-set values) and uninitialized data (e.g., variables that will receive values during runtime).
- Resource Segment (.rsrc): Many applications include non-code resources like icons, images, sound files, menus, dialog box definitions, and localized strings. These are stored in the resource segment, allowing the program to present a rich user interface and experience.
- Import/Export Tables: Programs often rely on functions provided by dynamically linked libraries (DLLs) – separate
.dllfiles that contain reusable code. The import table lists the functions that the.exeexpects to import from various DLLs, while the export table lists functions that the.exeitself makes available for other programs or DLLs to use. - Header: At the very beginning of the
.exefile is a header that provides critical metadata to the operating system’s loader. This includes information such as the size of the file, the starting address of the program, the required memory, and the location of different segments within the file. This header is the first thing the OS reads to understand how to prepare and launch the program.
These components work in concert to ensure that when an .exe file is launched, the operating system can correctly load, configure, and execute the program, providing the user with the intended functionality.
The Ubiquity and Versatility of .exe in Tech & Innovation
The .exe file format, despite its age, remains a cornerstone of how software is delivered and run on Windows-based systems, which continue to dominate various professional and personal computing environments. Its versatility has allowed it to underpin vast swathes of technological innovation.
Driving Operating Systems and Applications
From the moment a Windows PC boots up, .exe files are at work. The operating system itself is a collection of countless executables that manage hardware, provide user interfaces, and run essential background services. Every application, from word processors and web browsers to complex design software and video editing suites, is ultimately launched via an .exe file. This direct execution model has been foundational to the desktop computing paradigm, enabling a rich ecosystem of software that caters to virtually every need. Innovators have leveraged this direct access to system resources and processing power to create groundbreaking applications that push the boundaries of what computers can do, leading to advancements in everything from scientific simulation to interactive entertainment.
Beyond the Desktop: .exe in Specialized Tech
While primarily associated with desktop applications, the principles behind .exe files—packaging compiled code for direct execution—extend into specialized areas that drive significant tech innovation. In fields like autonomous systems, remote sensing, and advanced robotics, .exe files play a crucial role, often behind the scenes.
For instance, developers of autonomous flight systems or AI follow modes often create custom ground control station software or simulation tools that run on a Windows machine. These applications, packaged as .exe files, provide interfaces for mission planning, real-time monitoring, telemetry analysis, and post-flight data processing. Similarly, mapping and remote sensing applications heavily rely on .exe files for processing vast datasets from satellites or aerial platforms. These could be sophisticated algorithms for image stitching, terrain mapping, object recognition, or environmental analysis, all encapsulated within executables designed for high performance on local systems.
Even in scenarios where the primary processing might occur on embedded hardware, an .exe file on a host PC might be responsible for tasks like firmware updates, configuring parameters, or flashing new software onto the specialized device. The reliability and direct control offered by .exe files make them indispensable for deploying and managing complex, high-performance software tools critical to cutting-edge research and development in these advanced technological domains.
The Evolution of Executables
The .exe format itself has evolved significantly since its inception, moving from simple command-line tools to supporting sophisticated graphical user interfaces (GUIs) with rich multimedia capabilities. Early .exe files for DOS were simple 16-bit programs, but with the advent of Windows, the Portable Executable (PE) format emerged, supporting 32-bit and later 64-bit architectures, and incorporating features like resource sections and dynamic linking.
While .exe remains specific to Windows, the concept of an executable file is universal across operating systems. Linux uses ELF (Executable and Linkable Format), and macOS uses Mach-O. Each format serves the same fundamental purpose: to package compiled code and data in a way that the operating system can load and run. This continuous evolution and adaptation have allowed executable files to remain relevant, powering the software that enables increasingly complex and intelligent systems, from AI-driven analytics to real-time control applications that demand immediate, localized processing power.
Security, Integrity, and Management of .exe Files
The power and directness of .exe files, while enabling profound innovation, also present significant security challenges. Because they are designed to execute arbitrary instructions, they have long been a primary vector for malicious software, making their secure management and integrity verification paramount in any tech environment.
The Double-Edged Sword: Security Risks
The very nature of an .exe file—its ability to execute code directly on your system—makes it a prime target for cyber attackers. Malware, viruses, ransomware, and trojan horses are frequently disguised as legitimate .exe files. A malicious executable, once launched, can perform a wide range of harmful actions: steal personal data, encrypt files for ransom, install backdoors, hijack system resources, or even completely compromise the operating system. This inherent risk means that users and organizations must exercise extreme caution when dealing with .exe files from unknown or untrusted sources. In critical infrastructure, autonomous systems, or data-sensitive environments, a compromised .exe file can lead to catastrophic failures, data breaches, or loss of control, underscoring the severe implications for innovation and security alike.
Best Practices for Safe Execution
Mitigating the risks associated with .exe files requires a multi-layered approach involving technical safeguards and user vigilance.
- Digital Signatures: Legitimate software developers digitally sign their
.exefiles. This signature, cryptographically verified, confirms the publisher’s identity and ensures that the file hasn’t been tampered with since it was signed. Always check for valid digital signatures, especially for software downloaded from the internet. - Antivirus and Anti-Malware Software: Robust, up-to-date antivirus software is essential. It scans
.exefiles for known malicious patterns and behaviors, providing a critical first line of defense against threats. - User Account Control (UAC): Windows’ UAC prompts users for permission before an
.exefile makes significant changes to the system. While sometimes perceived as an annoyance, UAC is a vital security feature that prevents unauthorized executables from gaining administrative privileges. - Sandboxing and Virtualization: For highly suspicious or untested
.exefiles, executing them in a sandboxed environment or a virtual machine can contain any potential damage, preventing it from affecting the host system. This is a common practice for security researchers and developers testing potentially dangerous software. - Source Verification: Only download
.exefiles from official, trusted sources (e.g., the software developer’s official website, reputable app stores). Avoid downloads from suspicious links, unsolicited emails, or pirated software sites.
Managing Executables in a Modern Environment
Effective management of .exe files extends beyond initial execution to their lifecycle within an organization or system.
- Software Updates and Patching: Keeping software updated is critical. Developers frequently release updates to fix bugs, improve performance, and, most importantly, patch security vulnerabilities that attackers could exploit through outdated
.exefiles. Automated update mechanisms are key to maintaining a secure and stable environment. - Version Control: For development teams, strict version control of
.exefiles and their source code is vital. This ensures that correct, tested versions are deployed and allows for rollbacks if issues arise. - Deployment Strategies: In larger organizations or for critical systems, thoughtful deployment strategies are necessary. This includes staggered rollouts, testing in isolated environments before production, and using centralized software distribution tools to manage
.exeinstallations across multiple machines, particularly for specialized tech like ground control stations for autonomous systems or data processing clusters. - Application Whitelisting: In highly secure environments, application whitelisting can be implemented. This strategy allows only pre-approved
.exefiles to run, effectively blocking all other unknown or potentially malicious executables. This is particularly relevant for systems handling sensitive data or operating critical infrastructure.
By adhering to these practices, the risks associated with .exe files can be significantly mitigated, allowing innovators to leverage their power for advancement while safeguarding against potential threats.
The Future of Executables and Software Deployment
The digital landscape is in constant flux, with new paradigms for software development and deployment emerging regularly. While .exe files remain entrenched in the Windows ecosystem, the broader concept of executable software is evolving, influenced by cloud computing, cross-platform compatibility, and the increasing demand for specialized, secure execution environments.
Cloud-Native and Containerized Applications
The rise of cloud computing and cloud-native architectures has shifted much of the software execution from local machines to remote servers. Technologies like Docker and Kubernetes facilitate containerization, where applications and their dependencies are packaged into lightweight, portable units called containers. While these containers might still involve compiled binaries (like Linux ELF or even Windows PE for Windows-based containers), the user often interacts with a service running in the cloud rather than directly launching a local .exe. This trend moves the “execution” to a managed, scalable cloud environment, reducing the direct local interaction with .exe files for many mainstream applications. However, local .exe files continue to be crucial for development tools, administrative clients, and specialized applications that require direct hardware interaction or cannot tolerate network latency.
Web Assembly and Cross-Platform Executables
The drive for universal compatibility has also given rise to technologies like Web Assembly (Wasm). Wasm allows code written in various languages (C++, Rust, etc.) to be compiled into a binary format that can run efficiently within web browsers, offering near-native performance for complex applications without requiring local .exe downloads. This represents a significant shift towards “executables” that are platform-agnostic and delivered via the web. Similarly, frameworks like Electron allow web technologies to be packaged into standalone desktop applications, creating what appears to be a local .exe but is essentially a browser instance running web code. These innovations aim to abstract away the underlying operating system and hardware, making software more universally accessible.
The Enduring Role in Specialized Hardware and Embedded Systems
Despite the allure of cloud-native and web-based solutions, the .exe file (or its equivalent binary executable) retains an enduring and critical role in specific, highly innovative domains. For embedded systems, such as those found in advanced robotics, IoT devices, or the onboard computers of autonomous vehicles, direct execution of compiled code on local hardware is not just preferable but often mandatory. These systems demand low latency, high determinism, and direct access to hardware for real-time control, sensor data processing, and immediate decision-making – tasks where offloading to the cloud is often impractical or unsafe.
Similarly, in edge computing, where processing occurs close to the data source (e.g., on a drone performing real-time image analysis or a remote sensing station gathering environmental data), locally executed binaries are essential. The efficiency, speed, and reliability offered by a well-optimized, locally executed program are paramount for performance-critical applications. Thus, even as deployment methods evolve, the fundamental concept of a directly executable, compiled program remains central to the continued advancement of specialized hardware, AI, autonomous flight, and other cutting-edge technological innovations where performance and local control are non-negotiable.
Conclusion
The .exe file, a seemingly simple file extension, represents a foundational pillar of modern computing. It is the compiled embodiment of software, the direct command to a machine, and the primary vehicle through which countless innovations are brought to life on Windows platforms. From launching the operating system itself to powering sophisticated AI applications, processing vast datasets for remote sensing, and enabling the intricate control systems for advanced autonomous technologies, .exe files are indispensable.
While the tech landscape is continuously reshaped by cloud computing, containerization, and cross-platform solutions, the core principle of an executable file—a program designed for direct, efficient execution on a specific architecture—remains critically relevant. Its inherent power, however, comes with a responsibility for diligent security practices, given its potential as a vector for malicious activity.
As we look to the future, the .exe file, or its evolved counterparts across different operating systems and deployment models, will continue to be instrumental. It will power the local intelligence of edge devices, enable the precise control of autonomous systems, and provide the robust platforms for specialized software development. Understanding the .exe file is therefore not just about grasping a technical detail; it’s about appreciating a fundamental component that underpins the vast and exciting world of technology and innovation, driving progress one executed instruction at a time.
