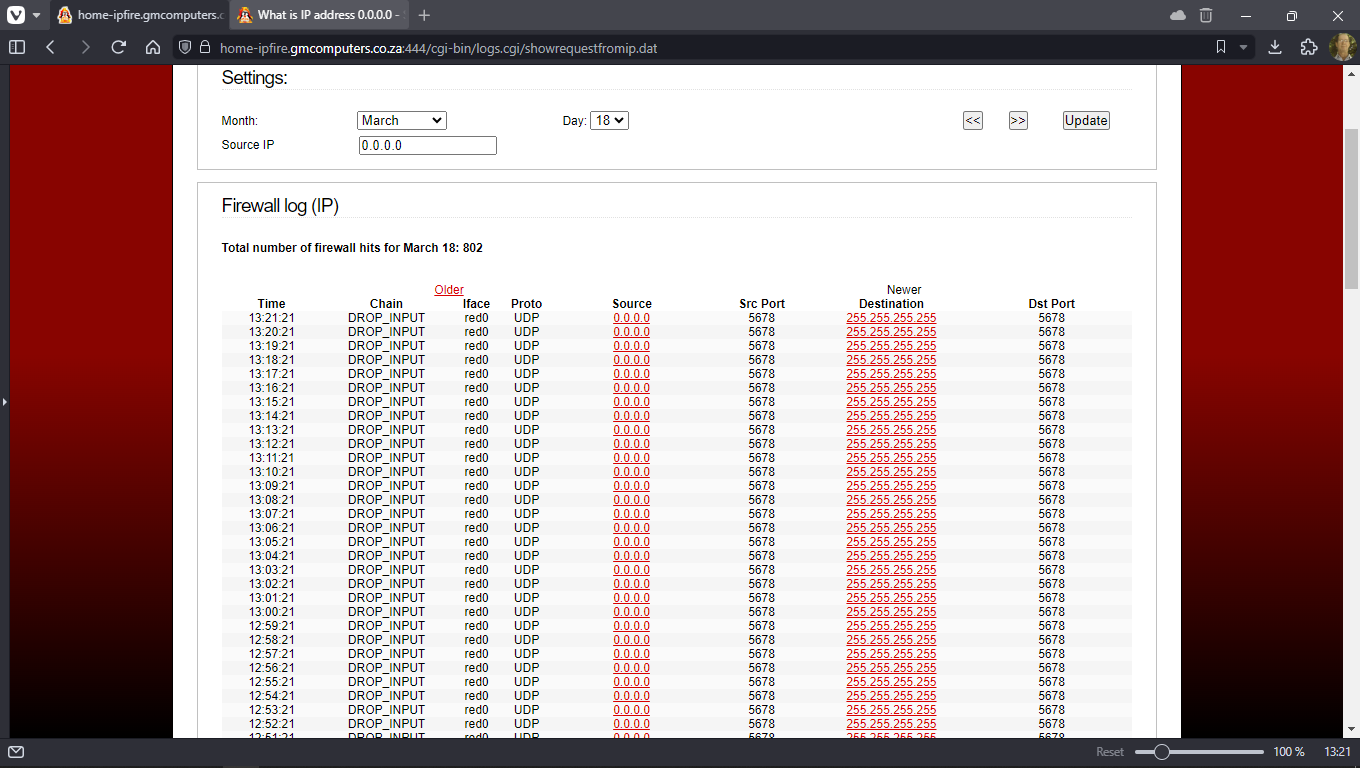
In the intricate tapestry of modern technology, where distributed systems, artificial intelligence, autonomous vehicles, and remote sensing define the cutting edge, foundational concepts often operate silently, yet profoundly. Among these, the seemingly enigmatic IP address “0.0.0.0” stands as a cornerstone. Far from being a specific, identifiable machine, 0.0.0.0 is a non-routable meta-address, a ubiquitous placeholder that plays a crucial, albeit often misunderstood, role in how networked systems initialize, communicate, and operate. Understanding 0.0.0.0 is not merely an exercise in network trivia; it’s an essential insight into the mechanisms that underpin the connectivity and scalability of contemporary tech innovations.

This address serves multiple critical functions, primarily indicating an unspecified or invalid target, or, more commonly, signifying “all available network interfaces” on a given host. Its abstraction allows for tremendous flexibility and simplifies configuration in dynamic environments, from local development setups to sprawling cloud infrastructures. For developers and architects building the next generation of intelligent systems, grasping the nuances of 0.0.0.0 is key to designing robust, scalable, and secure applications.
The Foundational Role of 0.0.0.0 in Network Architecture
At its core, 0.0.0.0 is a conceptual anchor in the vast and complex world of IP networking. It’s not an address you would assign to a device to receive traffic directly, nor does it typically exist on the public internet. Instead, its power lies in its symbolic meaning and its internal utility within a network device’s configuration.
A Conceptual Anchor in IP Addressing
The Internet Protocol (IP) address system provides a unique identifier for every device on a network, enabling data to be routed correctly. However, 0.0.0.0 deviates from this norm. It represents an unspecified or unknown address. When a device’s network interface controller (NIC) is configured with 0.0.0.0, it typically signifies that the device has not yet obtained a valid IP address, often during the boot-up sequence before a Dynamic Host Configuration Protocol (DHCP) server assigns one. More profoundly, in server configurations, 0.0.0.0 acts as a wildcard, instructing an application to listen for connections on all available network interfaces—whether they are Wi-Fi, Ethernet, or virtual interfaces. This capability is fundamental for flexibility, especially in systems designed for high availability and dynamic networking.
Default Routes and Gateway Initialization
Beyond server binding, 0.0.0.0 also plays a critical role in defining network routes, specifically as the “default route.” In a router’s or host’s routing table, a destination of 0.0.0.0/0 signifies the default gateway. This tells the operating system: “If you don’t have a more specific route for a particular destination IP address, send the traffic to this gateway.” This mechanism is universally employed and is indispensable for any networked device to communicate beyond its immediate local network segment. From a server in a data center to an embedded system in an autonomous drone attempting to send telemetry data, the 0.0.0.0/0 default route is the initial instruction for outbound traffic to reach its intended destination, facilitating everything from basic internet access to complex distributed system communications.
The “Any” Address: Listening Across Interfaces
The most frequent and impactful use of 0.0.0.0 in the context of modern applications is its function as the “any” address. When a server-side application—be it a web server, an API endpoint, or a data streaming service—is configured to bind to 0.0.0.0 on a specific port, it signals its readiness to accept incoming connections on that port regardless of which of the host machine’s IP addresses the client uses to connect. For instance, if a machine has two network interfaces with IP addresses 192.168.1.10 and 10.0.0.5, a service binding to 0.0.0.0:80 will accept connections originating from clients targeting either 192.168.1.10:80 or 10.0.0.5:80. This simplifies network configuration immensely, as the application doesn’t need to be explicitly aware of the specific network topology or changing IP addresses of its host.
Enabling Service Accessibility in Dynamic Computing Environments
The utility of 0.0.0.0 truly shines in the dynamic and often ephemeral landscapes of modern computing, where flexibility and ease of deployment are paramount. From cloud infrastructure to containerized applications, this meta-address helps abstract away networking complexities, allowing developers to focus on application logic.
Server Binding and API Exposure
In the world of microservices and cloud-native architectures, applications are frequently deployed on virtual machines or containers with dynamic IP addresses. When building APIs for services that handle remote sensing data, manage AI model inference requests, or coordinate autonomous agents, developers often configure these services to listen on 0.0.0.0. This ensures that regardless of the specific IP address assigned to the host or container, the service will be accessible. This flexibility is invaluable for continuous deployment and elastic scaling, as services can be moved, replicated, or scaled up and down without requiring manual network reconfigurations, greatly accelerating the development and deployment cycles for innovative tech solutions.
Containerization and Virtualized Networks
Containerization technologies like Docker and orchestration platforms such as Kubernetes heavily leverage the concept of 0.0.0.0. Inside a Docker container, applications almost invariably bind to 0.0.0.0. This internal binding signifies that the service is available within the container’s isolated network environment. Kubernetes and Docker then handle the complex task of network address translation (NAT) and port mapping, exposing these services to external networks or other containers. This abstraction is fundamental to the agility of containerized applications, allowing AI workloads, data processing pipelines, and sophisticated backends for autonomous systems to be packaged, deployed, and scaled across diverse infrastructure with unprecedented ease, decoupling the application from its underlying network specifics.
Facilitating Inter-Service Communication
Complex distributed systems are characterized by multiple services collaborating to achieve a larger goal. Whether it’s a data ingestion service feeding a machine learning pipeline, or a control service communicating with a fleet management system, these inter-service communications are critical. By having services listen on 0.0.0.0, they can be readily discovered and accessed by other components within the same network segment or cluster. This approach simplifies the configuration of service meshes, message brokers, and other communication middleware that glue distributed applications together, ensuring seamless data flow and command execution across various modules of advanced tech solutions.
0.0.0.0’s Impact on AI, Autonomous Systems, and Remote Sensing
The implications of 0.0.0.0 extend directly into the cutting-edge domains of artificial intelligence, autonomous systems, and remote sensing, enabling robust communication and flexible deployments for these highly networked and data-intensive technologies.
Networked Robotics and Autonomous Vehicle Communication
Autonomous systems, including advanced drones for environmental monitoring, industrial inspection, or logistical operations, are fundamentally networked entities. They constantly exchange data: telemetry, sensor readings, command and control signals, and navigation updates. Within an autonomous vehicle’s internal network, various sub-systems—such as perception modules, planning engines, and actuation controllers—often need to communicate. By configuring internal services or APIs to listen on 0.0.0.0, these components can reliably establish connections regardless of which internal network interface becomes active or is used for communication. This flexibility is crucial for systems that might operate in varied environments, ensuring continuous data flow for situational awareness and decision-making, even as network interfaces or conditions change. It underpins the robustness required for mission-critical autonomous functions.
Distributed AI Training and Inference
The scale of modern AI demands distributed computing. Training large language models or complex neural networks often involves hundreds or thousands of GPUs collaborating across a cluster. In such scenarios, worker nodes need to communicate parameters, gradients, and synchronization signals. When an AI training framework’s communication layer (e.g., using frameworks like TensorFlow Distributed or PyTorch Distributed) configures its message passing interfaces to listen on 0.0.0.0, it ensures that any node within the cluster can connect to it, regardless of the specific network interface IP address. This simplifies cluster setup and management, making distributed AI training more accessible and efficient. Similarly, for AI inference at the edge or in the cloud, models exposed via APIs often listen on 0.0.0.0 to accept requests from a diverse range of clients or other services, enabling real-time decision-making for applications like predictive maintenance or object detection in remote sensing imagery.
Remote Sensing Data Ingestion and Processing
Remote sensing applications, whether from satellite constellations, high-altitude aircraft, or drone-mounted sensors, generate colossal volumes of data—imagery, LiDAR scans, spectral data, and more. Robust data ingestion and processing pipelines are essential to handle this influx. Data collection services, often deployed in cloud environments or specialized data centers, are typically configured to listen on 0.0.0.0. This allows them to accept data streams from any connected remote sensor or data relay point, simplifying the architecture for dynamic sensor deployments. Such flexibility ensures that as new sensors come online, or as data paths are reconfigured, the central ingestion system remains operational and accessible, ready to process critical environmental, agricultural, or infrastructural insights derived from remote observations.
Security Considerations and Best Practices in Modern Tech
While 0.0.0.0 offers undeniable advantages in flexibility and ease of configuration, its “listen on all interfaces” nature introduces significant security considerations that demand careful attention, especially in critical tech applications.
The Double-Edged Sword of Accessibility
The convenience of having a service listen on all interfaces is also its greatest vulnerability if not managed correctly. By binding to 0.0.0.0, an application becomes accessible not just from intended internal networks but potentially from any network segment the host is connected to, including the wider internet, if appropriate firewall rules are not in place. For sensitive services—such as internal APIs controlling autonomous drone movements, databases holding proprietary remote sensing data, or AI models handling confidential information—this broad accessibility can be a severe security risk. Unintended exposure can lead to unauthorized access, data breaches, or malicious control, completely undermining the security posture of an advanced tech system.
Secure Configuration in Production Environments
In production environments, especially for mission-critical systems or those handling sensitive data, the default of binding to 0.0.0.0 should be critically re-evaluated. Best practice dictates that services should ideally bind to specific, necessary IP addresses (e.g., an internal network IP) rather than all available interfaces. When 0.0.0.0 is used, it must be coupled with robust network segmentation, stringent firewall rules, and access control lists (ACLs) to strictly limit which IP addresses or networks are permitted to connect to the service. For example, an API serving AI inference requests should only be accessible from authorized front-end services or clients, never directly from the public internet without proper authentication and authorization layers. For internal-only services in autonomous vehicles, firewalling off external access is paramount.
Adhering to Zero-Trust Principles
The discussion around 0.0.0.0 naturally aligns with modern cybersecurity paradigms like Zero Trust. A Zero Trust architecture operates on the principle of “never trust, always verify,” meaning no user or device is inherently trusted, regardless of their location inside or outside the network perimeter. While 0.0.0.0 provides broad accessibility, a Zero Trust approach would demand explicit authorization and authentication for every connection attempt, even if the service is configured to listen broadly. This means that while 0.0.0.0 facilitates initial connectivity, the subsequent security layers—including strong authentication, granular access controls, and continuous monitoring—are indispensable to protect the integrity and confidentiality of data and control systems in any advanced technological deployment.
Conclusion: The Unseen Pillar of Digital Connectivity
The simple string “0.0.0.0” belies its profound and multifaceted role in the architecture of modern technology. Far from being an inert or irrelevant IP address, it functions as an essential placeholder and a powerful configurative tool, enabling the flexibility and scalability that characterize today’s most innovative systems. From facilitating basic network operations and routing decisions to simplifying the deployment of complex AI models, autonomous vehicle communication protocols, and vast remote sensing data pipelines, 0.0.0.0 is an unseen, yet indispensable, pillar of digital connectivity.
Its paradoxical nature—representing both an absence and an omnipresence—underscores a fundamental principle in technology: abstraction is power. However, with this power comes responsibility. As the frontiers of AI, robotics, and advanced data analytics continue to expand, an informed understanding of foundational networking concepts like 0.0.0.0, coupled with rigorous security practices, remains paramount. It ensures that the boundless innovation we strive for is built upon a foundation that is not only flexible and efficient but also robust and secure, safeguarding the future of our interconnected world.
