In an increasingly interconnected world, where digital footprints are vast and ever-expanding, the concept of privacy has become a complex and often debated topic. For enthusiasts and professionals operating within the rapidly advancing field of drone technology, understanding cyber threats like “doxxing” is not just an academic exercise but a critical component of responsible innovation. Doxxing, a portmanteau of “dropping documents,” refers to the act of publicly revealing private or identifying information about an individual or organization, typically without their consent, with malicious intent. While traditionally associated with internet forums and hacking, the proliferation of sophisticated drone technology – particularly in areas like mapping, remote sensing, and autonomous flight – introduces new dimensions to how personal information can be gathered, processed, and potentially misused. This article delves into the meaning of doxxing, exploring its implications within the context of drone tech and emphasizing the importance of safeguarding privacy in an era defined by advanced aerial capabilities.
The Evolving Landscape of Privacy and Drones
The evolution of drone technology from hobbyist toys to indispensable tools for various industries has brought with it unprecedented capabilities for data collection and analysis. This technological leap, while offering immense benefits, simultaneously raises significant questions about individual privacy and the potential for misuse of collected data. Understanding these dynamics is crucial for fostering a responsible and secure drone ecosystem.
Data Collection Capabilities of Modern Drones
Modern drones, especially those categorized under “Tech & Innovation,” are equipped with an array of sophisticated sensors and imaging systems far beyond simple visual cameras. These include high-resolution optical cameras capable of 4K and even 8K video, thermal imaging sensors, LiDAR (Light Detection and Ranging) systems, multispectral and hyperspectral cameras, and advanced GPS/GNSS modules. When coupled with powerful onboard processing capabilities and AI algorithms, these drones can perform detailed mapping, create intricate 3D models of environments, conduct precise remote sensing for agriculture or infrastructure inspection, and even identify individuals or objects from significant altitudes.
For instance, drones engaged in mapping projects can capture aerial imagery so detailed that individual features, vehicles, and even people can be identified. Remote sensing missions might collect data that, when combined with other publicly available information, could reveal patterns of life or personal habits. The sheer volume and granularity of data that can be amassed pose a direct challenge to traditional notions of privacy, moving beyond mere observation to comprehensive digital profiling.
The Digital Footprint of Drone Operations
Beyond the data collected by drones, the operations of drones themselves generate a substantial digital footprint. This includes flight logs, registration information for pilots and aircraft, flight plans, geofencing data, and communications protocols. Many commercial and even advanced recreational drones require registration with aviation authorities, and their flights are often logged, sometimes publicly or semi-publicly through tracking apps and flight management systems.
Furthermore, drone operators themselves often create online profiles, participate in forums, and share their work on social media platforms. This digital presence, combined with technical data about their drone activities, can inadvertently create a trove of information. In the wrong hands, this scattered information – from where a drone frequently flies to the identity of its operator – could be pieced together to form a comprehensive profile, making drone operators themselves potential targets for doxxing. The intersection of powerful data collection tools and readily available personal information highlights a growing vulnerability in the drone community.
Understanding Doxxing: A Cyber Threat
To fully appreciate the risks within the drone context, it’s essential to grasp the core mechanics and impact of doxxing. It is more than just an invasion of privacy; it is a weaponization of information.
Definition and Mechanisms of Doxxing
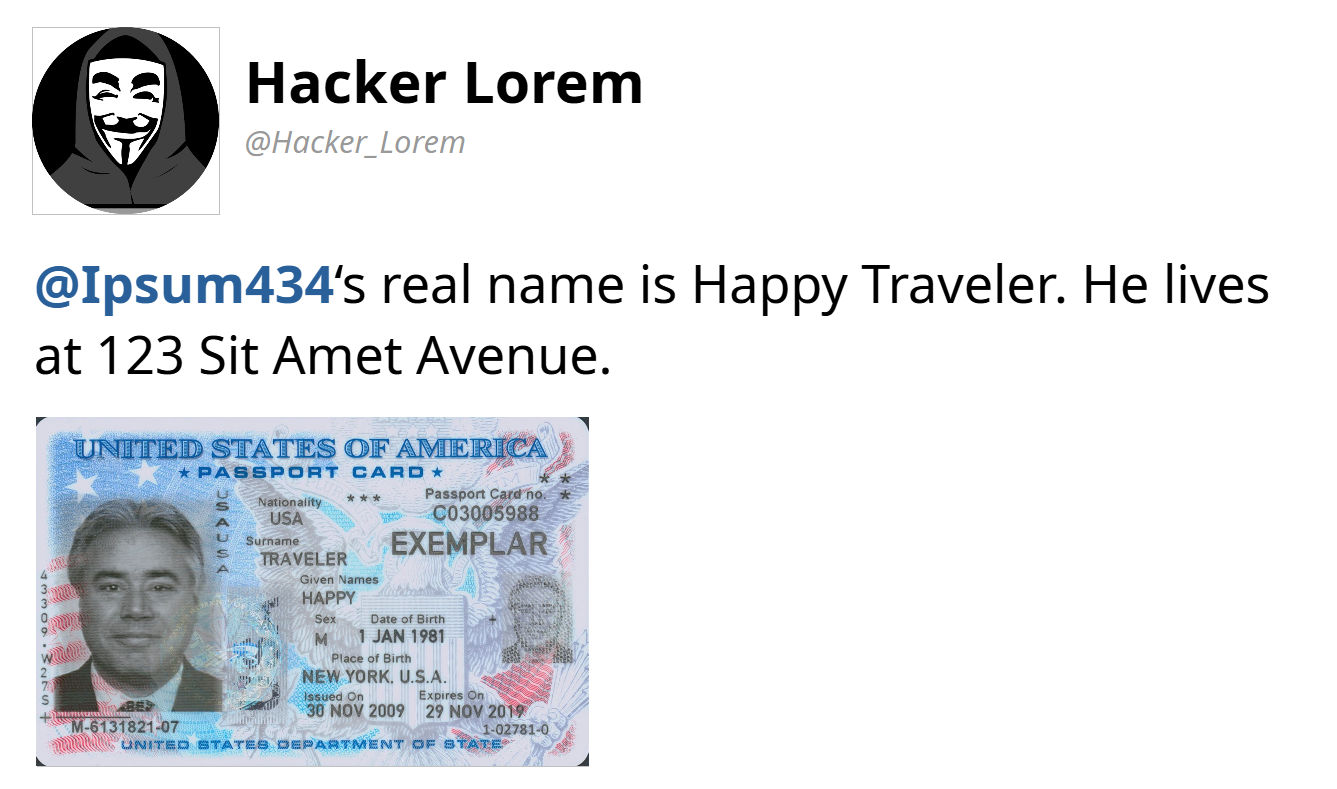
At its core, doxxing is the act of discovering and publishing the real personal information of an individual (or organization) online, typically without their consent, and with malicious intent. This information often includes a person’s real name, home address, workplace, phone number, financial details, and other private data. The intent behind doxxing can vary, from harassment and intimidation to revenge, extortion, or even inciting real-world violence.
The mechanisms of doxxing leverage both passive and active information gathering techniques. Passive methods involve scouring publicly available records – social media profiles, public databases (e.g., property records, voter registrations), news articles, forum posts, and old websites. Active methods might involve social engineering (tricking someone into revealing information), exploiting data breaches, or even more illicit means of accessing private databases. The internet’s vastness and the difficulty of completely erasing one’s online history make individuals particularly susceptible. Once published, “doxed” information can spread rapidly, making it nearly impossible to retract fully.
The Impact on Individuals and Organizations
The consequences of being doxxed can be severe and far-reaching. For individuals, it can lead to intense online harassment, stalking, identity theft, financial fraud, and even physical threats or attacks. The psychological toll can be immense, causing anxiety, fear, and a profound sense of vulnerability. Victims may feel compelled to change their names, move homes, or drastically alter their online and real-world lives to regain a sense of safety and anonymity.
For organizations, doxxing can lead to significant reputational damage, loss of customer trust, legal liabilities, and operational disruptions. If an employee, particularly one in a sensitive role related to drone operations or data handling, is doxxed, it could expose the organization to security breaches or targeted attacks. The financial cost of mitigating the effects of doxxing, from legal fees to cybersecurity enhancements and public relations efforts, can be substantial. In the context of drone tech, where companies might handle sensitive client data or government contracts, the stakes are even higher.
Drone Technology and the Doxxing Conundrum
The sophisticated capabilities of modern drones, while beneficial, introduce unique vectors through which doxxing can occur or be exacerbated. The focus on Tech & Innovation means examining how AI, autonomous flight, mapping, and remote sensing can inadvertently contribute to or become entangled with doxxing risks.
Identifying Vulnerabilities in Drone Ecosystems
The drone ecosystem presents several unique vulnerabilities. Firstly, the data collected through mapping and remote sensing applications can be highly granular. A drone surveying a neighborhood for urban planning or property assessment might capture high-resolution imagery that inadvertently reveals personal details – specific cars, routines of residents, modifications to homes, or even faces. While often aggregated and anonymized for public use, the raw data can be incredibly revealing. If this raw data were to fall into the wrong hands through a hack or insider threat, it could be used to doxx individuals living in the surveyed areas.
Secondly, the increasing autonomy of drones, driven by AI follow mode and advanced navigation systems, means that drones can operate with less direct human supervision, potentially collecting data over wider areas or for longer durations without immediate oversight. This raises concerns about who owns the data, who has access to it, and how it is secured throughout its lifecycle. A lapse in data governance or cybersecurity protocols for an autonomous drone fleet could lead to massive data breaches, containing personally identifiable information (PII) that could then be used for doxxing.

Misuse of Aerial Data for Personal Identification
The risk of aerial data being misused for personal identification is a primary concern. Imagine a scenario where a malicious actor gains access to a mapping project database. This database could contain high-resolution images, precise GPS coordinates, and even 3D models of residential areas. By correlating this data with publicly available information – such as property records (often public), social media posts geotagged to specific locations, or even license plate information visible in images – an individual’s full identity, including their exact living patterns, could be exposed.
Furthermore, facial recognition technology, while not commonly integrated into civilian drones due to privacy concerns, is technologically feasible. If such capabilities were to become more widespread or fall into the wrong hands, the potential for mass identification and subsequent doxxing from aerial platforms would be staggering. Even without explicit facial recognition, the unique characteristics of a property, a vehicle, or even a pet, when combined with other data points, can be enough to identify an individual. This highlights the ethical imperative for developers and operators in Tech & Innovation to prioritize privacy-by-design principles.
Safeguarding Against Doxxing in Drone Operations
Mitigating the risk of doxxing within the drone industry requires a multi-faceted approach, combining robust technological safeguards with stringent ethical guidelines and legal frameworks.
Best Practices for Data Handling and Anonymity
For drone operators and companies utilizing advanced mapping and remote sensing technologies, implementing best practices for data handling is paramount. This includes:
- Data Minimization: Only collect the data absolutely necessary for the mission. Avoid incidental collection of PII.
- Anonymization and Pseudonymization: Immediately anonymize or pseudonymize any potentially identifying data. This means removing direct identifiers or replacing them with artificial identifiers.
- Robust Encryption: Ensure all collected data, both in transit and at rest, is encrypted using strong, industry-standard protocols.
- Access Control: Implement strict access controls for data, limiting who can view, process, or download sensitive information.
- Secure Storage: Use secure, vetted cloud storage solutions or on-premise servers with robust cybersecurity measures.
- Data Retention Policies: Establish clear policies for how long data is stored and ensure timely deletion of unnecessary or expired data.
- Regular Audits: Conduct regular security audits and penetration testing to identify and address vulnerabilities in data handling systems.
- Training: Continuously train personnel on data privacy best practices and the risks associated with doxxing.
Beyond these, promoting a culture of “privacy first” within drone operations is essential. This means thinking about the privacy implications at every stage of a drone project, from planning to data dissemination.
Legal and Ethical Considerations in Drone Use
The rapid pace of technological advancement in drones often outstrips the development of legal frameworks. However, existing privacy laws, such as GDPR in Europe or various state-level privacy laws in the US, often apply to data collected by drones. Drone operators and companies must be acutely aware of and compliant with these regulations, especially when dealing with data that could identify individuals.
Ethically, drone operators have a responsibility to use their technology respectfully and considerately. This includes:
- Transparency: Be transparent with the public about drone operations, especially when operating in populated areas.
- Consent: Where feasible and legally required, seek consent from individuals before collecting data that might identify them.
- Minimizing Intrusion: Operate drones in a manner that minimizes intrusion into private spaces and avoids unnecessary surveillance.
- Responsible Disclosure: If a data breach occurs, follow ethical and legal guidelines for prompt and transparent disclosure.
The drone community, particularly those pushing the boundaries of Tech & Innovation, must actively engage in shaping ethical guidelines and advocating for thoughtful legislation that balances innovation with individual privacy rights.
The Future of Privacy in an Autonomous World
As drone technology continues its march towards greater autonomy and sophistication, the challenges and opportunities for privacy will only grow.
AI, Autonomous Flight, and Enhanced Surveillance
The ongoing development of AI follow mode, completely autonomous flight, and advanced object recognition capabilities heralds a new era of drone operations. While these innovations promise efficiency, safety, and new applications, they also enhance the potential for pervasive surveillance. Drones operating autonomously could collect data continuously over vast areas, identifying patterns, tracking movements, and potentially linking individuals to their activities with unprecedented accuracy.
The challenge lies in ensuring that these advanced capabilities are designed with privacy as a foundational principle, not an afterthought. This means developing AI algorithms that can anonymize data at the edge, building autonomous systems that adhere to geofenced privacy zones, and ensuring that the data collected by these highly intelligent machines is not easily exploitable for doxxing or other malicious purposes.

Building Resilient Systems and User Awareness
Ultimately, combating doxxing in the drone age requires a two-pronged approach: building resilient technological systems and fostering heightened user awareness. Technologically, this means investing in cybersecurity research specific to drone ecosystems, developing secure-by-design hardware and software, and creating robust, decentralized data management solutions. It also means exploring privacy-enhancing technologies that can process data without revealing PII.
From the user perspective, educating drone pilots, developers, and the public about the risks of doxxing and the privacy implications of drone technology is crucial. Understanding what constitutes sensitive data, how to protect it, and the potential consequences of its misuse empowers individuals to operate more responsibly and demand higher privacy standards from technology providers and policymakers.
In conclusion, “doxxing” represents a potent threat in the digital age, and its meaning expands to encompass the sophisticated data collection capabilities of modern drone technology. For the field of Tech & Innovation in drones, understanding and mitigating this threat is not just a regulatory compliance issue, but an ethical imperative to ensure that these powerful tools serve humanity’s progress without compromising fundamental rights to privacy and security.
