The dream of effortless aerial photography, breathtaking cinematic shots, or even just the simple joy of piloting a sophisticated machine can be shattered in an instant by the chilling realization that your drone has been compromised. In an increasingly connected world, the vulnerability of sophisticated technology to cyber threats is a stark reality. While drone technology offers unparalleled freedom and capability, it also presents new vectors for malicious actors. Understanding what to do if your drone has been hacked is no longer a niche concern; it’s an essential part of responsible drone ownership. This guide will equip you with the knowledge and steps to take to mitigate the damage, recover your asset, and enhance your future security.
Understanding Drone Hacking: The Threat Landscape
Before delving into remediation, it’s crucial to grasp the nature of drone hacking. This isn’t just about someone taking control of your drone mid-flight, though that is a terrifying possibility. Drone hacking encompasses a range of illicit activities, from data breaches to physical theft facilitated by digital intrusion. Understanding these threats will help you identify potential signs of compromise and implement preventative measures.
Common Hacking Methods and Vectors
Drone systems, whether consumer-grade or professional, rely on a complex interplay of hardware, software, and communication protocols. Each of these components can be a potential entry point for attackers.
- Radio Frequency (RF) Jamming and Spoofing: Many drones communicate with their controllers via radio frequencies. Attackers can use RF jamming to disrupt this communication, causing the drone to lose control or land unexpectedly. More sophisticated attacks involve RF spoofing, where an attacker mimics legitimate control signals, tricking the drone into following their commands instead of the pilot’s. This is particularly concerning for GPS-reliant drones, as spoofed GPS signals can lead them astray.
- Wi-Fi and Bluetooth Exploitation: Some drones, especially smaller or more basic models, utilize Wi-Fi or Bluetooth for connectivity. If these networks are not secured with strong passwords or if the drone’s firmware has known vulnerabilities, attackers can gain unauthorized access to the drone’s systems, including its camera feed and control interface. This can lead to data theft or direct control takeover.
- Firmware Vulnerabilities: Like any complex piece of technology, drone firmware can contain bugs or security flaws. Hackers actively scan for and exploit these vulnerabilities to gain elevated privileges or execute malicious code on the drone. This could allow them to disable safety features, access stored data, or even brick the device.
- Mobile Application Exploitation: The mobile apps used to control drones are also potential targets. If the app itself has vulnerabilities or if your mobile device is compromised, attackers could gain access to your drone through the app. This could involve stealing login credentials or exploiting weaknesses in the app’s communication with the drone.
- Physical Access and Tampering: While not strictly a digital hack, physical access to a drone can be a gateway to hacking. An attacker with physical access could potentially install malicious hardware or software, or even clone communication protocols.
Potential Consequences of a Drone Hack
The impact of a drone hack can range from minor inconvenience to severe financial loss and legal repercussions.
- Loss of Control and Crash: The most immediate and visible consequence is the loss of control, leading to a crash. This can result in damage to the drone itself, as well as potential damage to property or injury to people on the ground.
- Data Theft: Many drones record sensitive information, including flight logs, video footage, and even user credentials stored within the associated apps. If a drone is hacked, this data can be accessed and stolen, leading to privacy violations or the compromise of proprietary information. For commercial users, this could include mapping data, inspection footage, or sensitive client information.
- Theft of the Drone: A hacker could use their access to disable tracking features and fly the drone to a remote location, effectively stealing it. This is particularly a risk for more expensive or specialized drones.
- Reputational Damage: For businesses that use drones for commercial purposes, a hacking incident can lead to significant reputational damage, eroding trust with clients and stakeholders.
- Legal and Regulatory Issues: If a hacked drone is used for illegal activities, such as surveillance or property damage, the owner could face legal consequences, even if they were not directly responsible for the hacking.
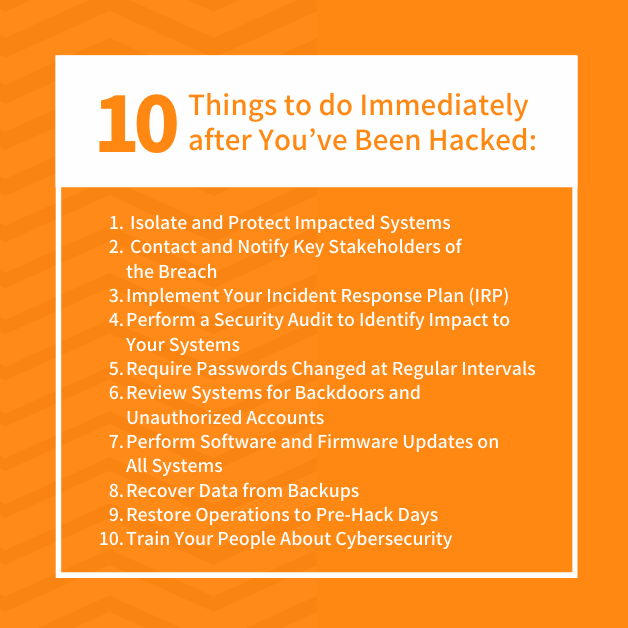
Immediate Steps to Take When You Suspect a Hack
The moment you suspect your drone has been compromised, swift and decisive action is critical. The goal is to contain the damage, prevent further unauthorized access, and begin the recovery process.
Assessing the Situation and Securing Your Assets
The first step is to calmly and methodically assess the situation. Don’t panic, but act with urgency.
- Is the Drone Currently Under Unauthorized Control? If the drone is in the air and behaving erratically, or if you’ve lost connection unexpectedly, prioritize regaining control or ensuring its safe landing if possible. This might involve attempting to re-establish a connection, activating return-to-home (RTH) features, or in extreme cases, initiating an emergency landing if your controller allows.
- Has the Drone Been Stolen or is it Missing? If you believe the drone has been stolen and is no longer in your possession, immediate steps to track and report it are crucial.
- Review Recent Flight Data and Logs: If you have access to your drone’s flight logs or the associated mobile app, review them for any anomalies, such as unexpected flight paths, unusual sensor readings, or unrecognized connection attempts.
- Check Associated Accounts: Log out of all drone-related applications and accounts on all your devices. Then, change your passwords for your drone manufacturer’s account, your Wi-Fi network, and any cloud storage services where drone data might be uploaded. Use strong, unique passwords and enable two-factor authentication wherever possible.
Disconnecting and Isolating the Drone
If the drone is physically accessible and you suspect it’s been compromised, the immediate priority is to prevent further damage or unauthorized use.

- Power Down the Drone: If the drone is powered on and you have physical access, turn it off immediately. Remove the battery if it’s easily detachable. This will sever any active connections.
- Disable Remote Controllers and Associated Devices: Turn off any remote controllers, smartphones, or tablets that were recently used to control the drone.
- Isolate from Networks: If your drone or associated devices connect to Wi-Fi or Bluetooth, disable these functions. If the drone has a cellular modem, consider removing the SIM card if feasible.
- Secure the Drone Physically: If you have the drone, store it in a secure location where it cannot be accessed by unauthorized individuals.
Recovery and Mitigation Strategies
Once the immediate threat is contained, the focus shifts to recovering your drone and its data, and implementing measures to prevent future incidents.
Contacting Authorities and Manufacturers
In cases of theft or significant compromise, involving the right parties is essential for recovery and investigation.
- Report to Law Enforcement: If your drone has been stolen, file a police report immediately. Provide them with all relevant details, including the drone’s serial number, model, and any identifying features.
- Contact the Drone Manufacturer: Reach out to the customer support of your drone’s manufacturer. Explain the situation in detail. They may have specific protocols for dealing with hacked devices, including remote disabling of the drone or assistance with firmware resets. They can also provide insights into known vulnerabilities and potential exploits for your specific model.
- Report to Aviation Authorities (if applicable): Depending on your location and the type of drone, you may need to report the incident to aviation authorities, especially if the drone was being used for commercial purposes or if the hacking incident posed a safety risk.
Data Recovery and Forensics
If data has been compromised or lost, pursuing recovery might be necessary, particularly for commercial operations.
- Check Cloud Backups: If you regularly back up your drone’s data to cloud services, check these backups for unaffected versions of your files.
- Professional Data Recovery Services: For critical data, consider engaging a professional data recovery service. They may be able to retrieve data from damaged storage devices or from the drone itself, if it’s recoverable.
- Digital Forensics: In cases of significant breach or suspected criminal activity, a digital forensics expert may be able to analyze the drone’s internal systems to identify how the hack occurred, what data was accessed, and potentially identify the perpetrator. This is typically a more involved and costly process, usually reserved for high-value incidents.
Enhancing Your Drone’s Security Against Future Attacks
Prevention is always better than cure. Implementing robust security measures will significantly reduce your drone’s vulnerability to hacking.
Fortifying Your Drone’s Connectivity
The wireless links between your drone, controller, and associated devices are prime targets for hackers.
- Secure Your Wi-Fi Network: Ensure your home and office Wi-Fi networks are secured with strong WPA2 or WPA3 encryption and a complex password.
- Update Firmware Regularly: Always keep your drone’s firmware, your controller’s firmware, and the companion mobile app updated to the latest versions. Manufacturers often release updates to patch security vulnerabilities. Set up automatic updates if available.
- Change Default Passwords: If your drone or its associated equipment has default passwords (e.g., for Wi-Fi access points on the drone itself), change them immediately to strong, unique passwords.
- Use Secure Communication Protocols: Familiarize yourself with the communication protocols your drone uses. If it offers options for encrypted communication, enable them.
- Be Cautious with Public Wi-Fi: Avoid connecting your drone’s controller or associated mobile devices to unsecured public Wi-Fi networks, as these are often hotbeds for malicious activity.

Strengthening Your Operational Security
Beyond technical measures, your operational practices play a crucial role in drone security.
- Enable Two-Factor Authentication (2FA): Whenever possible, enable 2FA on your drone manufacturer’s account and any associated cloud storage or app accounts. This adds an extra layer of security beyond just your password.
- Secure Your Mobile Device: Ensure the smartphone or tablet used to control your drone is password-protected, has up-to-date security software, and is not jailbroken or rooted, as these can make it more susceptible to malware.
- Physical Security: Treat your drone like any other valuable piece of equipment. Store it securely when not in use and be mindful of who has physical access to it.
- Be Wary of Unsolicited Software or Firmware: Only download and install software, firmware, or apps from official sources. Be suspicious of links or attachments sent via email, even if they appear to be from the manufacturer.
- Regular Security Audits: For professional users, consider periodic security audits of your drone operations and data management practices to identify and address any emerging risks.
The threat of drone hacking is real and evolving. By understanding the risks, taking immediate action when a compromise occurs, and proactively implementing robust security measures, you can significantly protect your valuable aerial asset and enjoy the benefits of drone technology with greater peace of mind. Stay informed, stay vigilant, and fly safely.
