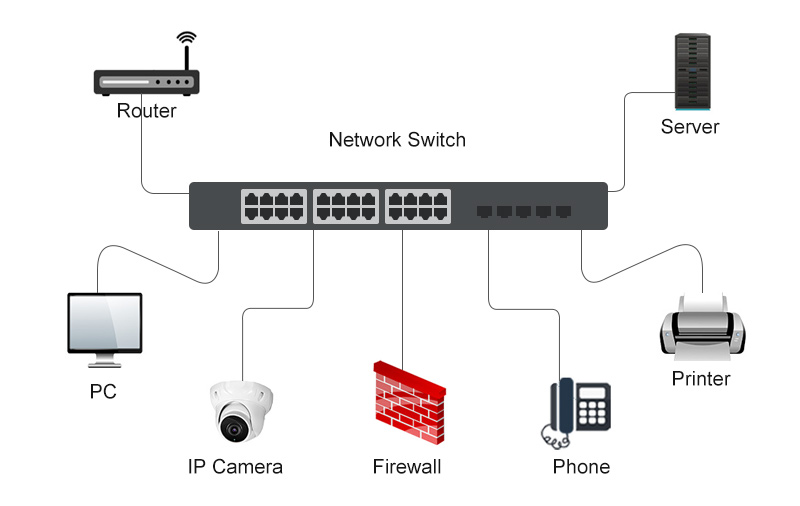
Network switches are fundamental components in modern networking, acting as the intelligent traffic directors that enable seamless communication between devices within a local area network (LAN). Unlike their simpler predecessors, hubs, switches possess the intelligence to learn and manage data flow efficiently, significantly enhancing network performance, security, and scalability. Understanding the role and functionality of network switches is crucial for anyone involved in setting up, managing, or troubleshooting wired networks, from small home offices to large enterprise environments.
The Core Functionality: Intelligent Data Forwarding
At its heart, a network switch’s primary job is to receive data packets from one connected device and intelligently forward them to their intended destination on the same network. This is a stark contrast to older hub technology, which simply broadcasted all incoming data to every connected device, leading to congestion and inefficiency. Switches, on the other hand, utilize a sophisticated process to ensure that data only travels where it needs to go.

Media Access Control (MAC) Addressing: The Switch’s “Address Book”
The intelligence of a network switch stems from its ability to learn and maintain a Media Access Control (MAC) address table. Every network interface card (NIC) in a connected device, such as a computer, printer, or server, has a unique, globally recognized MAC address. When a data packet arrives at a switch port, the switch examines the source MAC address of that packet and records it in its MAC address table, associating it with the specific port it arrived on.
When a data packet arrives with a destination MAC address, the switch consults its MAC address table.
- Known Destination: If the destination MAC address is found in the table, the switch forwards the packet only to the port associated with that MAC address. This direct, point-to-point communication dramatically reduces unnecessary network traffic and collisions.
- Unknown Destination: If the destination MAC address is not yet in the MAC address table, or if it’s a broadcast address (intended for all devices), the switch will broadcast the packet to all other ports, except the one it arrived on. The intended recipient will then respond, and the switch will learn its MAC address and port association for future transmissions.
This learning process is dynamic and continuous, allowing the switch to adapt to changes in the network topology as devices are added, removed, or moved.
Frame Processing and Forwarding Methods
Switches employ different methods to process and forward data frames, each with its own performance characteristics:
- Store-and-Forward: This is the most common and robust method. The switch receives the entire data frame into its buffer, checks it for errors (e.g., Cyclic Redundancy Check – CRC errors), and only then forwards it to the appropriate destination port. This ensures that only error-free data is propagated across the network, improving overall network reliability. However, it introduces a slight delay as the entire frame needs to be stored before forwarding.
- Cut-Through: In this method, the switch reads only the destination MAC address (or the first few bytes of the frame) and immediately begins forwarding the packet without waiting for the entire frame to arrive. This significantly reduces latency, making it ideal for high-performance applications like real-time voice and video streaming. The trade-off is that error checking is deferred or performed only after forwarding, potentially allowing corrupted frames to enter the network.
- Fragment-Free: A hybrid approach that attempts to balance the benefits of store-and-forward and cut-through. The switch reads the first 64 bytes of the frame, which includes the MAC addresses and any header information. It then forwards the frame. This allows for the detection of certain types of errors (like runt frames, which are too short) while still offering lower latency than pure store-and-forward.
The choice of forwarding method can impact network performance and is often a configurable option on managed switches.
Types of Network Switches: Catering to Diverse Needs
The world of network switches isn’t monolithic. A variety of switch types have emerged to address different network demands, ranging from basic connectivity to advanced management and security features.
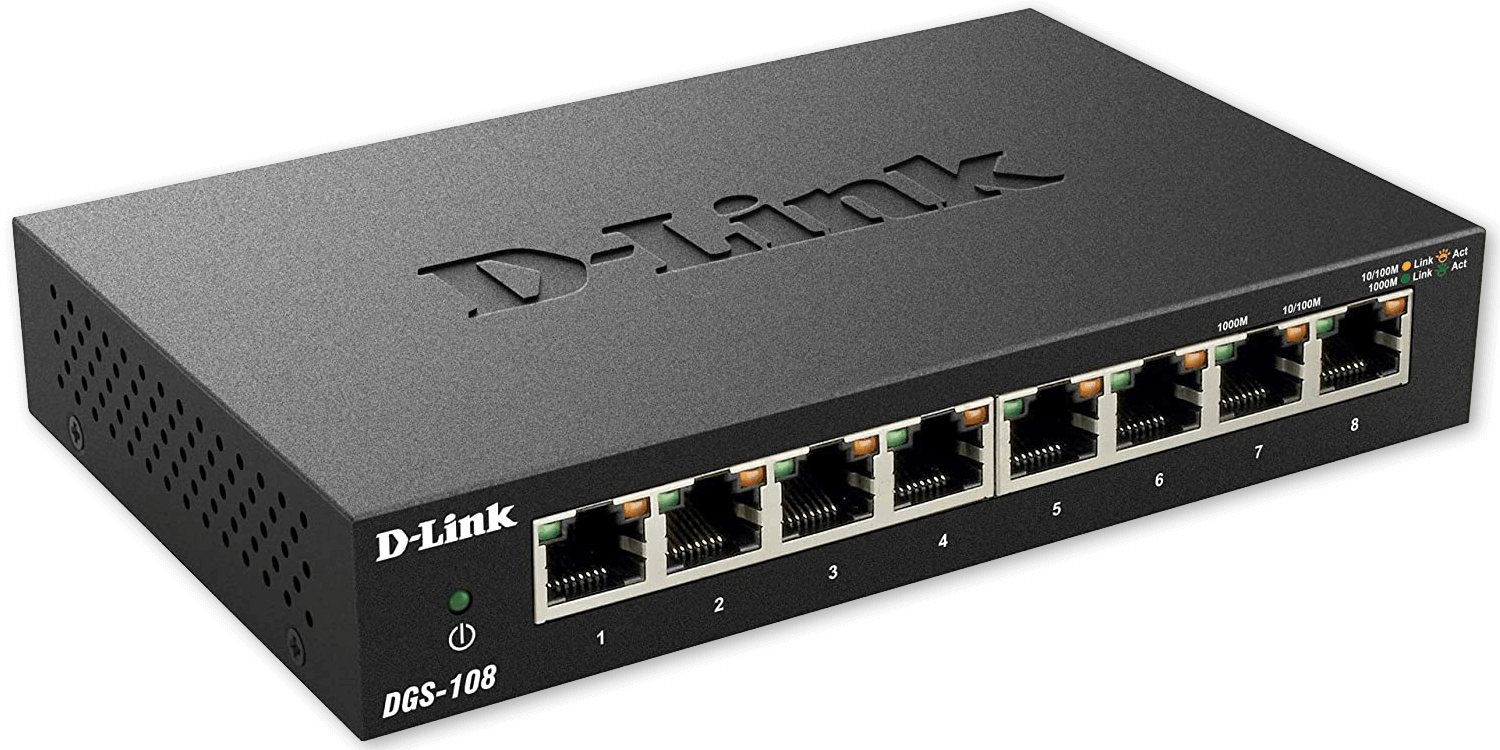
Unmanaged Switches: Plug-and-Play Simplicity
Unmanaged switches are the simplest and most affordable type of network switch. They are designed for basic plug-and-play functionality, requiring no configuration. Simply connect your devices, power on the switch, and it begins directing traffic.
- Key Characteristics:
- Fixed configuration; no user interface for management.
- Ideal for small home networks, small offices, or temporary network setups.
- Offer basic MAC address learning and forwarding.
- Typically available with 5, 8, 16, or 24 ports.
- Pros: Easy to set up and use, cost-effective.
- Cons: Limited features, no control over network traffic, no advanced security options.
Managed Switches: Power and Control
Managed switches offer a far greater degree of control and flexibility over network operations. They come with a management interface (web-based GUI, command-line interface – CLI, or SNMP) that allows administrators to configure, monitor, and manage network traffic, security, and performance.
- Key Features:
- VLANs (Virtual Local Area Networks): Allow administrators to segment a physical network into multiple logical networks. This improves security by isolating traffic and can simplify network management. For example, a company might create separate VLANs for the accounting department, the sales team, and guest Wi-Fi.
- QoS (Quality of Service): Enables administrators to prioritize certain types of network traffic over others. This is crucial for applications like voice calls (VoIP) or video conferencing, ensuring they receive sufficient bandwidth and low latency even when the network is congested.
- Port Mirroring: Allows administrators to copy traffic from one or more ports to a specific port for monitoring and analysis. This is invaluable for network troubleshooting and security forensics.
- Link Aggregation (LAG) / Port Trunking: Combines multiple physical network ports into a single logical link. This increases bandwidth and provides redundancy. If one link fails, traffic can automatically reroute through the remaining active links.
- SNMP (Simple Network Management Protocol): Allows network devices to be monitored and managed remotely.
- Pros: Enhanced control, advanced features, improved performance, better security, scalability.
- Cons: More expensive than unmanaged switches, require technical expertise to configure and manage.
Smart/Web-Managed Switches: A Hybrid Approach
Smart switches, also known as web-managed switches, offer a middle ground between unmanaged and fully managed switches. They provide some advanced features of managed switches but with a simpler web-based interface, making them more accessible to users who don’t require the full complexity of enterprise-grade managed switches.
- Key Characteristics:
- Typically offer features like VLANs, QoS, and port mirroring.
- Easier to configure than fully managed switches.
- A good choice for small to medium-sized businesses that need more control than unmanaged switches offer but without the steep learning curve of CLI-managed switches.
Advanced Switch Capabilities and Technologies
Beyond basic forwarding and management features, modern network switches incorporate a range of advanced capabilities designed to enhance performance, security, and efficiency.
Power over Ethernet (PoE): Simplifying Device Deployment
Power over Ethernet (PoE) technology allows network switches to deliver electrical power to connected devices over the same Ethernet cable that transmits data. This eliminates the need for separate power adapters for devices like IP phones, wireless access points (APs), and security cameras, simplifying installation and reducing clutter.
- PoE Standards: Different PoE standards exist (e.g., IEEE 802.3af, 802.3at PoE+, 802.3bt PoE++) which define the amount of power that can be delivered. Switches and the powered devices (PDs) must adhere to the same standard for compatibility.
- Benefits: Streamlined installation, reduced cabling, lower infrastructure costs, and improved flexibility in device placement.
Layer 2 vs. Layer 3 Switching: Expanding Functionality
Network switches primarily operate at Layer 2 (Data Link Layer) of the OSI model, using MAC addresses for forwarding. However, some advanced switches, known as Layer 3 switches, also incorporate routing capabilities, operating at Layer 3 (Network Layer) and using IP addresses for forwarding.
- Layer 2 Switches:
- Forward traffic based on MAC addresses.
- Operate within a single broadcast domain (LAN).
- Cannot route traffic between different IP subnets.
- Layer 3 Switches:
- Combine the functionality of a Layer 2 switch with a router.
- Forward traffic based on both MAC addresses (within a subnet) and IP addresses (between subnets).
- Can perform inter-VLAN routing, eliminating the need for a separate router for internal network segmentation.
- Offer higher performance for routing compared to traditional routers in many enterprise scenarios.
- Use Cases: Layer 3 switches are commonly found in larger enterprise networks where high-speed routing between VLANs or subnets is required.
Security Features: Protecting the Network
Network switches play a vital role in network security. Managed switches offer a suite of features to protect the network from unauthorized access and malicious activity.
- Port Security: Allows administrators to restrict access to specific ports based on MAC addresses. This prevents unauthorized devices from connecting to the network.
- DHCP Snooping: A security feature that monitors DHCP traffic on the network and prevents rogue DHCP servers from assigning IP addresses to clients.
- Access Control Lists (ACLs): Rules that can be configured on switches to permit or deny traffic based on various criteria, such as source/destination IP addresses, MAC addresses, and port numbers.
- 802.1X Network Access Control: A standard that provides authenticated access to the network. Devices must authenticate (e.g., with username/password or certificates) before being granted network access.
In conclusion, network switches are indispensable for building and maintaining efficient, reliable, and secure wired networks. From the simplicity of unmanaged switches to the advanced capabilities of managed and Layer 3 switches, understanding their functions and available features is key to optimizing network performance and ensuring seamless data flow for any connected environment.
