The realm of network communication is a complex tapestry woven with intricate protocols, each serving a specific purpose in ensuring the smooth and reliable flow of data. While many users are familiar with common protocols like HTTP for web browsing or SMTP for email, there are other, less visible but equally vital, protocols that underpin the very foundation of network diagnostics and troubleshooting. One such protocol is the Internet Control Message Protocol, or ICMP. The question “What port is ICMP?” often arises in discussions about network security, performance, and management. However, to understand ICMP’s role, it’s crucial to grasp that it doesn’t operate on a traditional port in the same way that TCP or UDP protocols do.
This article will delve into the fundamental nature of ICMP, explaining why it deviates from the typical port-based model and how it contributes to the broader landscape of network technology. We will explore its primary functions, the types of messages it generates, and its significance in diagnosing and understanding network behavior.
Understanding Network Protocols: The Port Paradigm
To appreciate why ICMP is unique, we must first establish the concept of network ports and their role in the communication model. In networking, the Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are the primary transport layer protocols. They operate on top of the Internet Protocol (IP), which is responsible for addressing and routing packets across networks.
The Role of TCP and UDP Ports
TCP and UDP use port numbers to differentiate between multiple applications or services running on the same host. Imagine a computer as a building with many apartments. The IP address is like the building’s street address, identifying the specific computer. Port numbers are like the apartment numbers within that building, allowing data to be directed to the correct application or service (e.g., a web server, an email client, a game).
When a client application wants to communicate with a server application, it sends a request to the server’s IP address and a specific port number. The server, listening on that port, receives the request and sends a response back to the client’s IP address and its designated port. This port-based system is fundamental to multiplexing, enabling a single host to handle numerous concurrent network connections for various applications.
For example:
- Port 80 is commonly used for HTTP (Hypertext Transfer Protocol), the backbone of World Wide Web communication.
- Port 443 is used for HTTPS (HTTP Secure), providing encrypted web communication.
- Port 25 is typically associated with SMTP (Simple Mail Transfer Protocol), used for sending emails.
- Port 53 is designated for DNS (Domain Name System), which translates human-readable domain names into IP addresses.
These well-defined port assignments allow network devices and software to quickly identify the intended recipient of data.
The Internet Protocol (IP) Layer
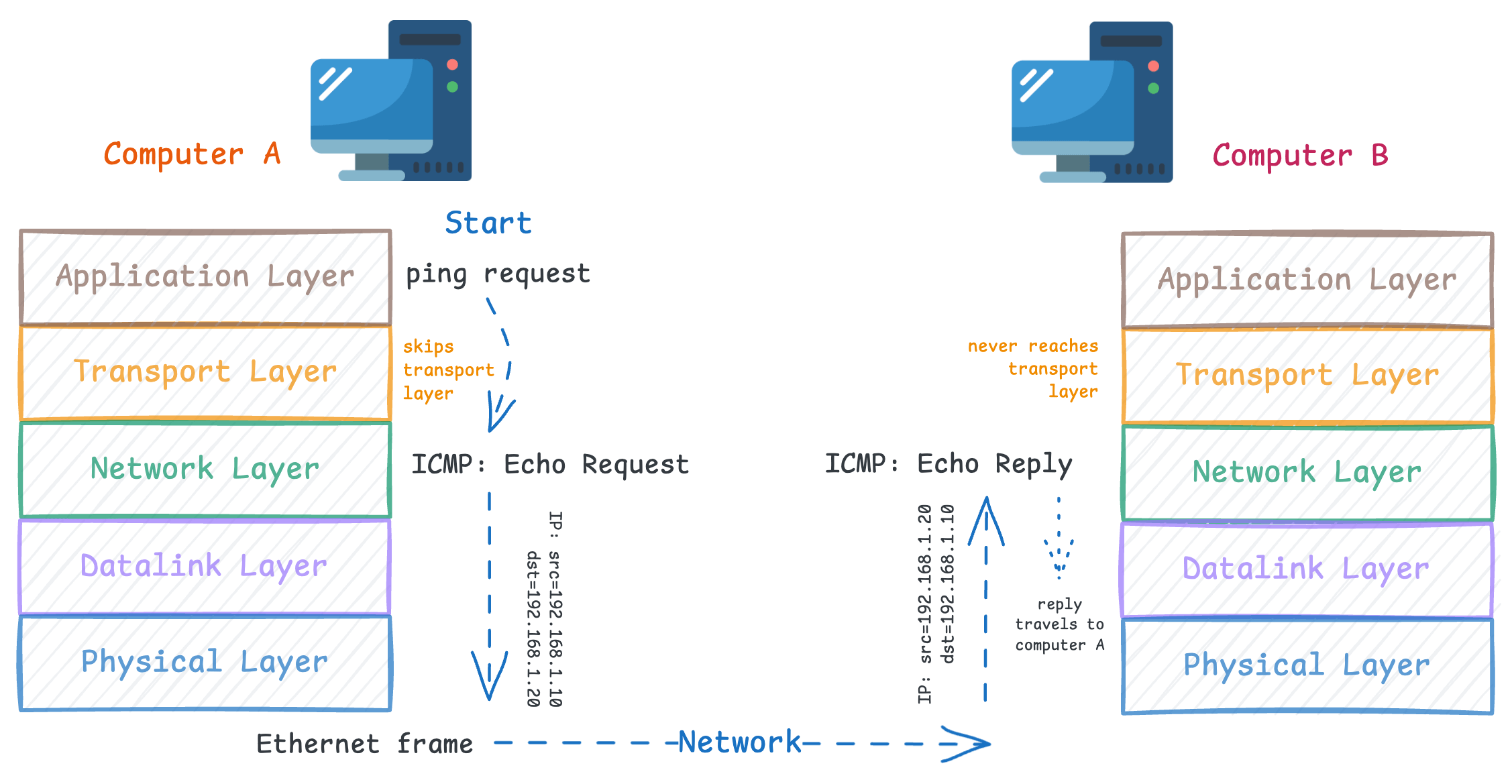
Above the data link layer (which handles physical network interfaces) and below the transport layer (TCP/UDP), sits the Internet Protocol (IP). IP’s primary responsibility is to packetize data and route these packets across diverse networks to their destination. It operates on a connectionless model, meaning it doesn’t establish a persistent connection before sending data. Each IP packet is treated independently.
IP packets contain source and destination IP addresses, along with other header information. When an IP packet arrives at a host, the host’s network stack examines the protocol field in the IP header to determine what to do with the payload. This field indicates whether the packet contains TCP data, UDP data, or data from another protocol.
ICMP: A Protocol of Control and Diagnostics
Now, let’s turn our attention to ICMP. Unlike TCP and UDP, ICMP does not have a concept of “ports” in the conventional sense. ICMP is designed to carry control and error messages related to IP operations. It is closely tied to the IP layer itself and operates directly within it.
ICMP’s Relationship with IP
ICMP messages are encapsulated directly within IP packets. When an ICMP message is sent, it’s placed as the payload of an IP packet. The IP header’s protocol field will be set to a specific value (value 1) that signifies ICMP. This tells the receiving host that the packet’s payload is an ICMP message and not data from a TCP or UDP application.
Because ICMP is fundamentally about the operation of the IP layer, it doesn’t need to interact with specific applications running on ports. Its purpose is to provide feedback to the originating IP entity (usually a host or router) about network conditions, the reachability of hosts, or the status of IP packet delivery.
ICMP Message Types
ICMP defines a variety of message types, each serving a distinct diagnostic or control function. These messages are identified by a “Type” field and often a “Code” field within the ICMP header, providing finer granularity for specific error conditions. Some of the most common and important ICMP message types include:
Echo Request and Echo Reply (Type 8 and Type 0)

These are arguably the most well-known ICMP messages, forming the basis of the ping utility.
- Echo Request (Type 8): A host sends an Echo Request message to a destination host, essentially asking, “Are you there?”
- Echo Reply (Type 0): If the destination host is reachable and operational, it responds with an Echo Reply message, confirming its presence and reachability.
The round-trip time for these requests and replies is a crucial metric for assessing network latency and connectivity.
Destination Unreachable (Type 3)
This message is generated by a router or host when it cannot deliver an IP packet to its final destination. It provides valuable information about why delivery failed. The “Code” field further specifies the reason for the unreachability. Common codes include:
- Code 0 (Net Unreachable): The router does not have a route to the destination network.
- Code 1 (Host Unreachable): The router knows how to reach the network, but the specific host on that network is not responding or is down.
- Code 3 (Port Unreachable): While ICMP itself doesn’t use ports, this message is generated by the destination host when it receives a packet for an IP address but the transport layer protocol (TCP or UDP) on that host indicates that no application is listening on the specified destination port. This is a common source of confusion, as it’s an ICMP message related to transport layer port issues.
- Code 4 (Protocol Unreachable): The destination host received the packet but doesn’t support the protocol specified in the IP header.
- Code 5 (Source Route Failed): A router encountered an error while trying to route the packet based on source routing options.
Time Exceeded (Type 11)
This message is generated by a router when the Time To Live (TTL) field in an IP packet reaches zero before the packet reaches its destination, or by the destination host if it receives a fragment of a datagram with a fragment reassembly time limit exceeded.
- Code 0 (TTL equals 0 during transit): This is the most common scenario, indicating that a packet has traversed too many routers or that a routing loop exists, causing it to be discarded. The
traceroute(ortracerton Windows) utility relies heavily on this ICMP message to map out the path packets take across the internet. It sends packets with incrementally increasing TTL values, and each router that discards a packet due to TTL expiration sends back a “Time Exceeded” message, revealing its identity and position in the path. - Code 1 (Fragment reassembly time exceeded): The destination host could not reassemble all fragments of a datagram within the allowed time.
Redirect (Type 5)
This message is sent by a router to inform a host about a more efficient route to a particular destination. It suggests that the host should send future packets for that destination directly to another, more optimal router. This is a form of dynamic route optimization.
Echo Control Messages (Type 30 and 31 – Deprecated)
While less common and largely deprecated, earlier versions of ICMP included Echo Control messages, which served similar purposes to Echo Request/Reply but were part of a different set of specifications.
ICMP’s Significance in Network Management and Security
The absence of ports for ICMP is not a limitation but a reflection of its role as a foundational network management and diagnostic tool. Its messages are essential for understanding network performance, troubleshooting connectivity issues, and identifying potential network problems.
Network Diagnostics and Troubleshooting
Tools like ping and traceroute, which are indispensable for network administrators and even everyday users, are built upon ICMP.
ping: By sending Echo Requests and analyzing Echo Replies, users can quickly determine if a host is reachable and gauge the latency of the connection. Persistent packet loss or high latency indicated bypingcan point to network congestion, faulty hardware, or routing problems.traceroute: As mentioned,tracerouteuses ICMP Time Exceeded messages to map the path a packet takes from source to destination. This allows administrators to pinpoint where in the network a problem might be occurring, whether it’s a specific router that’s down or experiencing high load, or a link that’s saturated.
Network Monitoring and Performance Analysis
ICMP messages, particularly Echo Requests and Replies, are fundamental to network monitoring systems. These systems continuously send ICMP probes to critical network devices and servers to ensure they are online and responding. The collected data on response times and packet loss provides valuable insights into the overall health and performance of the network.
Security Implications
While ICMP is a vital diagnostic tool, it can also be exploited by malicious actors. This has led to various security considerations:
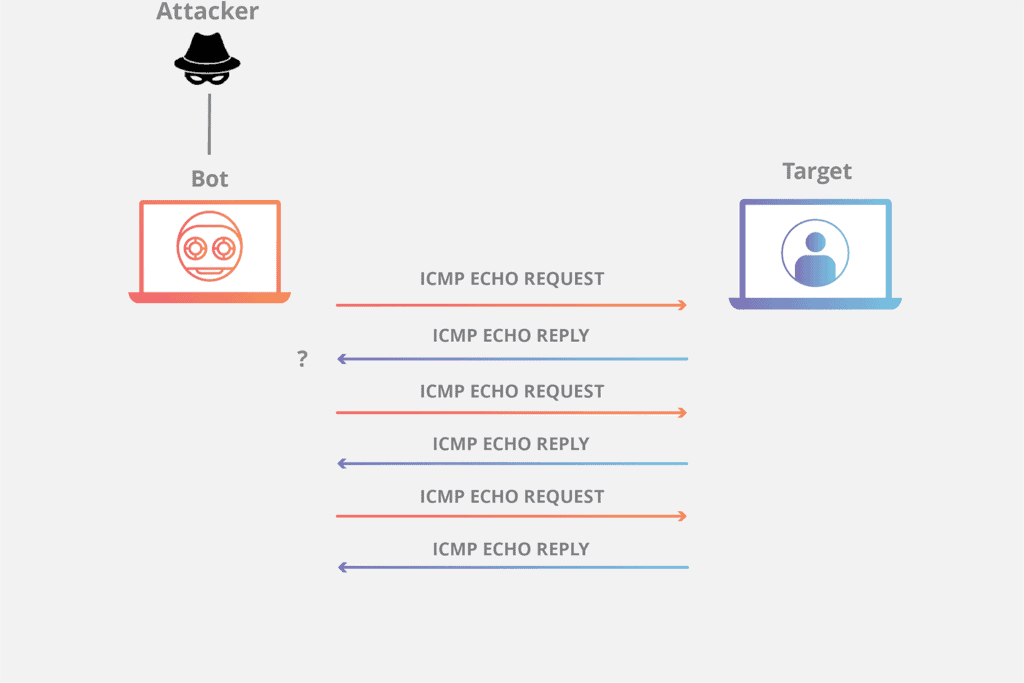
- Denial-of-Service (DoS) Attacks: Certain ICMP-based attacks, like “Smurf” attacks, leverage ICMP Echo Requests to overwhelm target systems with traffic.
- Information Gathering: Attackers can use ICMP to map out networks and identify active hosts.
- Firewall Rules: Because ICMP is so fundamental, firewalls are often configured to allow essential ICMP messages (like Echo Requests/Replies) while blocking others to mitigate security risks. However, an overly restrictive firewall policy that blocks all ICMP can hinder legitimate network diagnostics.
Therefore, understanding which ICMP messages are necessary and which can be safely filtered is crucial for maintaining a secure yet functional network. The decision to block certain ICMP types is a balancing act between security and diagnostic capabilities. For example, blocking all “Destination Unreachable” messages might prevent some attack vectors, but it also makes it harder to diagnose why a legitimate connection is failing.
Conclusion
In essence, the question “What port is ICMP?” is a bit of a misnomer. ICMP does not operate on a port number like TCP or UDP. Instead, it is a protocol that runs directly within the IP layer, using specific message types and codes to facilitate network control, diagnostics, and error reporting. Its messages are encapsulated within IP packets, and the IP header’s protocol field identifies them as ICMP. This unique position allows ICMP to be a powerful tool for understanding network behavior, troubleshooting connectivity, and monitoring performance. While its utility is undeniable, its security implications necessitate careful consideration and intelligent firewall policies. Recognizing ICMP’s distinct role, separate from the port-based paradigm of application-level protocols, is fundamental to comprehending the intricate workings of modern networks.
