In the rapidly evolving landscape of data security, the methods employed to safeguard information are as diverse as the data itself. Among the fundamental building blocks of modern cryptography, stream ciphers stand out for their unique approach to encryption. Unlike their block cipher counterparts, which encrypt data in fixed-size chunks, stream ciphers operate on individual bits or bytes, transforming them into a pseudorandom keystream that is then combined with the plaintext. This fundamental difference dictates their characteristics, performance, and suitability for various applications. Understanding the intricacies of stream ciphers is crucial for anyone involved in secure communications, data protection, and the design of cryptographic systems.
The Core Principles of Stream Ciphers
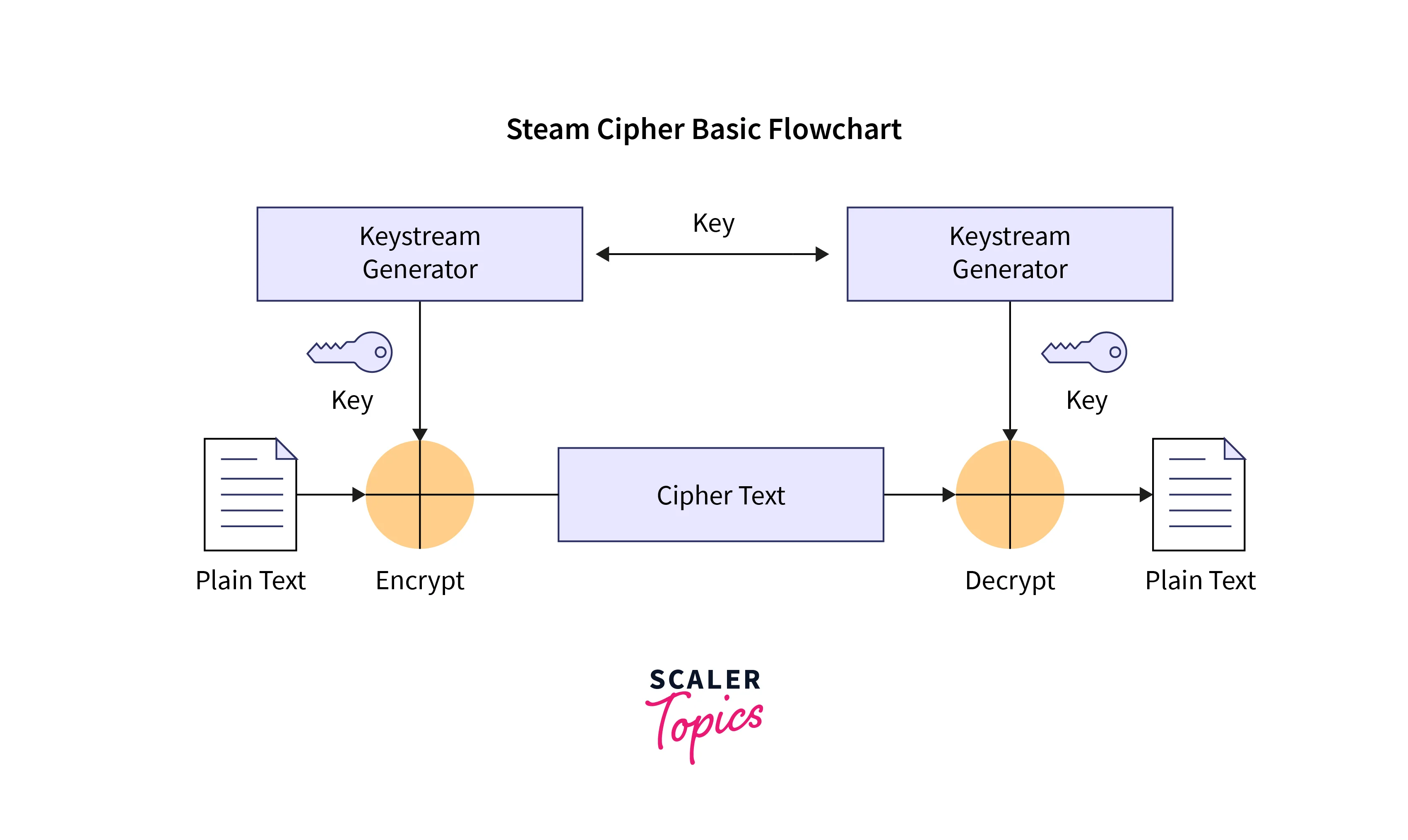
At its heart, a stream cipher is an encryption algorithm that encrypts individual plaintext digits (bits or bytes) one at a time. The encryption process involves generating a pseudorandom stream of bits, known as the keystream, which is then combined with the plaintext using a simple bitwise operation, typically the exclusive-OR (XOR) function. The decryption process mirrors this, using the same keystream to XOR with the ciphertext and recover the original plaintext. This fundamental mechanism, while seemingly simple, relies heavily on the quality and unpredictability of the generated keystream.
The Keystream Generation Process
The generation of the keystream is the most critical component of a stream cipher. This is typically achieved through a pseudorandom number generator (PRNG). A PRNG is an algorithm that produces a sequence of numbers that approximates the properties of random numbers, but is entirely determined by a secret initial value called the “seed” or “key.” The seed is crucial; it must be kept secret and unique for each message or communication session to ensure strong security.
There are two primary architectures for keystream generators:
- Linear Feedback Shift Registers (LFSRs): These are a class of digital circuits that produce a pseudorandom sequence of bits. They consist of a shift register and a linear function of the register’s contents. The output of the LFSR is fed back into the register, creating a new state. LFSRs are relatively simple and efficient but can be vulnerable to certain types of cryptanalysis if not designed carefully. Modern stream ciphers often use multiple interconnected LFSRs to enhance their security.
- Non-linear Generators: To overcome the potential weaknesses of purely linear generators, many stream ciphers employ non-linear feedback functions or combine linear components with non-linear elements. These non-linear operations make the keystream much harder to predict and analyze, significantly strengthening the cipher against attacks. Examples include the use of Boolean functions with complex structures or state machines that exhibit chaotic behavior.
The Role of the Key and Initialization Vector (IV)
The security of a stream cipher hinges on two primary inputs: the secret key and, often, an Initialization Vector (IV).
- The Secret Key: This is the fundamental secret that must be shared between the sender and receiver. It is used to seed the PRNG, thereby determining the specific keystream generated for a given message. The longer and more random the key, the more secure the encryption. A compromised key renders the entire encrypted communication useless.
- The Initialization Vector (IV): While the key determines the overall pseudorandomness, the IV plays a crucial role in ensuring that identical plaintexts encrypt to different ciphertexts, even when encrypted with the same key. This is vital for security, as repeating ciphertext patterns can reveal information about the underlying plaintext. The IV does not need to be secret but must be unique for each message encrypted with the same key. It is typically transmitted alongside the ciphertext.
The XOR Operation: Combining Plaintext and Keystream
The actual encryption and decryption process in a stream cipher is remarkably straightforward, leveraging the properties of the bitwise XOR operation.
- Encryption:
Ciphertext = Plaintext XOR Keystream - Decryption:
Plaintext = Ciphertext XOR Keystream
The XOR operation has the desirable property that applying it twice with the same value returns the original value: (A XOR B) XOR B = A. This means that if the receiver can generate the identical keystream as the sender, they can XOR it with the received ciphertext to recover the original plaintext. The security of the stream cipher therefore lies entirely in the unpredictability and secrecy of the keystream, which is derived from the secret key and IV.
Types and Architectures of Stream Ciphers
Stream ciphers can be broadly categorized based on their underlying keystream generation mechanism and how they are implemented. This categorization helps in understanding their strengths, weaknesses, and typical use cases.
Synchronous Stream Ciphers
In synchronous stream ciphers, the keystream is generated independently of the ciphertext and plaintext. Both the sender and receiver initialize their keystream generators with the same key and IV. As long as the generators remain synchronized, they will produce identical keystreams. Synchronization is crucial; if the sender and receiver fall out of sync (e.g., due to lost packets), subsequent bits will be decrypted incorrectly.
- Characteristics: High speed, suitable for real-time applications like voice or video transmission where minor desynchronization can be tolerated or corrected.
- Security Considerations: Vulnerable to replay attacks if the IV is not handled properly. Also susceptible to bit-flipping attacks if an attacker can modify the ciphertext without detection, as they can independently flip bits in the plaintext by flipping corresponding bits in the ciphertext.
Self-Synchronizing Stream Ciphers
Unlike synchronous stream ciphers, self-synchronizing stream ciphers allow the keystream generator to resynchronize automatically after a certain number of bits, even if some ciphertext bits are lost or corrupted. This is achieved by making the keystream generation dependent on a certain number of previously transmitted ciphertext bits.
- Characteristics: More robust against transmission errors and packet loss. The synchronization mechanism adds some latency and complexity compared to synchronous ciphers.
- Security Considerations: While more resilient to desynchronization, they can be more susceptible to certain cryptanalytic attacks if the dependency on ciphertext bits is exploited. The initial synchronization phase can also be a point of vulnerability.
Examples of Stream Ciphers
Historically and in modern cryptography, several stream ciphers have gained prominence:
- RC4: A widely used (though now considered insecure for many applications) synchronous stream cipher known for its simplicity and speed. It has been shown to have significant vulnerabilities, particularly in its initial bytes and in scenarios where the same keystream is reused.
- ChaCha20: A modern, highly regarded stream cipher developed by Daniel J. Bernstein. It is a synchronous stream cipher that uses a quarter-round function based on addition, rotation, and XOR operations. ChaCha20 is known for its speed and strong security guarantees, making it a popular choice in protocols like TLS 1.3.
- Salsa20: The predecessor to ChaCha20, also developed by Bernstein, it shares many of its design principles. Salsa20 is also a strong and efficient stream cipher.
- AES in CTR Mode: While AES is a block cipher, it can be used in Counter Mode (CTR) to function as a stream cipher. In CTR mode, AES encrypts a sequence of counters, and the resulting output is XORed with the plaintext. This mode offers high performance and parallelizability, making it a strong contender for stream cipher applications.
Applications and Use Cases
The inherent characteristics of stream ciphers – their speed, efficiency, and suitability for continuous data streams – make them ideal for a variety of security-critical applications.
Real-Time Communications and Streaming
The ability of stream ciphers to encrypt data on a bit-by-bit basis makes them particularly well-suited for applications that require low latency and continuous data flow. This includes:
- Voice over IP (VoIP): Encrypting voice calls to ensure privacy and prevent eavesdropping.
- Video Conferencing: Securing sensitive conversations and visual data during online meetings.
- Online Gaming: Protecting game data and preventing cheating or unauthorized access.
- Secure Socket Layer/Transport Layer Security (SSL/TLS): While TLS can utilize both block and stream ciphers, stream ciphers are often employed for their efficiency in handling the continuous data streams of web traffic.
Wireless Communication and Mobile Devices
In environments where bandwidth and processing power may be limited, stream ciphers offer an attractive solution for securing wireless communications.
- Wi-Fi Security (WPA2/WPA3): Stream ciphers like RC4 (in older versions, now replaced by more secure algorithms) and modern alternatives are fundamental to securing wireless networks against unauthorized access.
- Mobile Device Encryption: Protecting sensitive data stored and transmitted by smartphones and tablets.
Encryption of Large Data Files
While block ciphers are often the go-to for encrypting large files, stream ciphers, particularly when used in efficient modes like CTR, can also be highly effective.
- Disk Encryption: Protecting the entire contents of a hard drive or storage device.
- File Archiving and Compression: Securing sensitive files before transmission or long-term storage.
Cryptographic Protocols
Stream ciphers are integral components of many higher-level cryptographic protocols, contributing to their overall security.
- Secure VPNs (Virtual Private Networks): Establishing encrypted tunnels to protect internet traffic.
- Secure Messaging Applications: End-to-end encryption for private communications.
Security Considerations and Best Practices
Despite their efficiency and widespread use, stream ciphers are not without their security considerations. Proper implementation and adherence to best practices are paramount to ensuring their effectiveness.
Keystream Reuse: The Cardinal Sin
The most critical vulnerability associated with stream ciphers is the reuse of the keystream. If the same keystream is used to encrypt two different plaintexts, an attacker can easily recover both plaintexts by XORing the corresponding ciphertexts. This is because (P1 XOR K) XOR (P2 XOR K) = P1 XOR P2. The attacker, knowing P1 XOR P2, can then use known-plaintext attacks or other cryptanalytic techniques to deduce P1 and P2. Therefore, it is absolutely essential to ensure that the keystream is unique for every message. This is typically achieved by using a unique IV for each message encrypted with the same key.
Initialization Vector (IV) Management
The IV, as mentioned, does not need to be secret but must be unique. A predictable or repeating IV can significantly weaken the security of a stream cipher, even if the key remains secret. Common practices for IV management include:
- Counter-based IVs: Incrementing a counter for each message.
- Randomly generated IVs: Generating a sufficiently long random IV for each message.
Choosing Modern and Verified Ciphers
The cryptographic landscape is constantly evolving, with older ciphers like RC4 being found to have exploitable weaknesses over time. It is crucial to:
- Use well-established and modern stream ciphers: Algorithms like ChaCha20 and AES in CTR mode are currently considered secure and have undergone extensive cryptanalysis.
- Avoid outdated or proprietary ciphers: Unless they have been rigorously vetted by cryptographic experts, proprietary or obscure ciphers should be treated with suspicion.
Key Management
As with any form of encryption, secure key management is paramount. This includes:
- Key Generation: Using strong, random key generation methods.
- Key Storage: Storing keys securely, using hardware security modules (HSMs) or other robust methods.
- Key Distribution: Securely distributing keys to authorized parties.
- Key Rotation: Regularly changing keys to limit the impact of a potential compromise.
Implementation Flaws
Even the strongest cryptographic algorithm can be rendered insecure by implementation flaws. Common pitfalls include:
- Timing attacks: Exploiting variations in execution time to infer information about the key or plaintext.
- Side-channel attacks: Exploiting physical characteristics of the device, such as power consumption or electromagnetic radiation.
- Buffer overflows and other software vulnerabilities: Allowing attackers to manipulate the encryption process.
In conclusion, stream ciphers are a vital and versatile tool in the arsenal of data security. Their efficiency and suitability for continuous data streams make them indispensable in numerous modern applications. However, their security is heavily dependent on the correct generation of a unique and unpredictable keystream, the diligent management of keys and IVs, and adherence to secure implementation practices. By understanding these principles and best practices, we can leverage the power of stream ciphers to effectively protect our digital information.
