The concept of an “identity function” might initially sound abstract, but within the realm of technology, particularly in areas like computer science, data processing, and even the underlying logic of some drone operations, it plays a surprisingly fundamental and impactful role. While not a tangible piece of hardware or a specific drone component, understanding the identity function is crucial for appreciating how systems process information, maintain consistency, and enable seamless data flow. In essence, it’s a function that returns its input unchanged. Imagine it as a perfect mirror, reflecting exactly what it receives. This simplicity, however, is its power, forming the bedrock for more complex operations and ensuring the integrity of data as it moves through various stages of processing.
The Foundational Principle of Identity
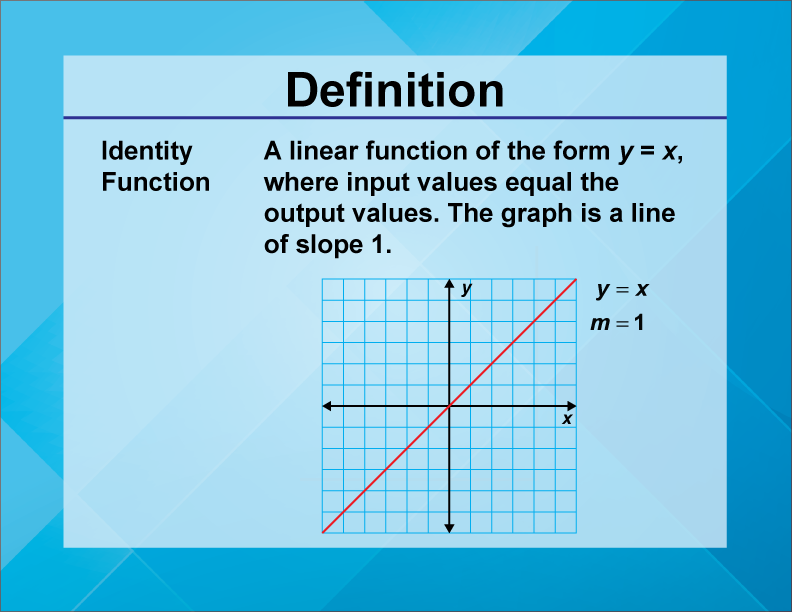
At its core, the identity function embodies the principle of “no change.” In mathematical terms, it’s represented as (f(x) = x), where (f) is the function, and (x) is the input. Whatever you put into the identity function, you get back exactly the same thing. This might seem trivial at first glance, but its implications in computational systems are far-reaching. It serves as a baseline, a reference point against which other functions can be compared or used to ensure that data has not been inadvertently altered.
Input, Process, and Output: The Unchanging Core
The fundamental interaction within any computational process involves taking an input, performing a process on it, and generating an output. The identity function is the simplest form of this interaction. The “process” is effectively doing nothing. It’s a placeholder, a function that exists to accept data and pass it along without modification. This is particularly important in complex workflows where data might pass through numerous stages. Having an identity function at certain points ensures that a particular stage has indeed performed its intended, albeit minimal, task without introducing any unintended transformations.
Mathematical Representation and Abstract Application
In mathematics, the identity function is a cornerstone of abstract algebra and set theory. It’s a mapping from a set to itself where every element is mapped to itself. This abstract concept translates directly into the computational world. When we discuss functions in programming, the identity function is often used as a building block. It’s not about performing a complex calculation, but about ensuring that a specific operation or data path maintains the original form of the data. This is crucial for maintaining data integrity and for understanding the flow of information in intricate algorithms.
Identity Functions in Data Processing and Software Engineering
The practical applications of the identity function are widespread in software development and data processing. It acts as a neutral element in functional programming, a way to pass data through a pipeline without alteration, and a tool for debugging and testing. Its seemingly passive nature makes it an active participant in ensuring the reliability and predictability of software systems.
As a Neutral Element in Functional Programming
Functional programming paradigms heavily rely on the concept of functions as first-class citizens. In this context, the identity function serves as a neutral element. Imagine a chain of operations, where each operation takes the output of the previous one as its input. If you need to insert a step in this chain that doesn’t modify the data, the identity function is the perfect choice. It allows you to compose functions in a modular way, ensuring that the overall flow remains predictable even when intermediary, non-modifying steps are introduced. This is akin to having a clear junction in a data pipeline that simply allows the data to pass through without any branching or alteration.

Ensuring Data Integrity and Consistency
In large-scale data processing pipelines, data often undergoes numerous transformations. At various points, it’s essential to verify that the data has not been corrupted or unintentionally altered. An identity function can be strategically placed within these pipelines to act as a check. If the output of an identity function differs from its input, it signals an issue within the system, pointing to a problem in the preceding or succeeding stages. This helps in maintaining data integrity and ensuring that the final processed data accurately reflects the original input, minus any intended transformations.
Debugging and Testing Utility
During the development and testing of software, the identity function can be an invaluable tool. When debugging, developers might want to isolate a specific part of a program and see how data flows without interference from other modules. By replacing a complex function with an identity function, they can observe the raw input and output, helping to pinpoint where issues might be occurring. Similarly, in unit testing, an identity function can be used to ensure that a particular module correctly passes data through, even if the module itself is supposed to be a simple pass-through.
Identity Functions in System Design and Logic
Beyond direct data manipulation, the identity function has a subtler but equally important role in the architectural design of complex systems, including those that might power advanced drone functionalities. It informs how control signals are managed and how different components interact without introducing unwanted side effects.
Control Flow and Decision Making
In systems that involve complex control flows, the identity function can represent a decision point where no action is taken, and the process continues with the existing state. For example, in a drone’s autonomous navigation system, there might be scenarios where no specific correction is needed, and the system simply continues on its current trajectory. This can be conceptually modeled using an identity function within the decision-making logic. The system “receives” the current state and “returns” the same state, indicating no deviation from the planned course.
Data Validation and Preprocessing
Before data is fed into a more complex algorithm or system, it might undergo a series of validation and preprocessing steps. An identity function can be used as a placeholder for steps that don’t require any modification but are essential for maintaining the order of operations or for ensuring that the data conforms to certain structural requirements. For instance, in a system that collects telemetry data from a drone, there might be stages that simply confirm the presence and format of certain data packets before they are processed further. These stages, conceptually, act as identity functions, ensuring data passes through without alteration while fulfilling their role in the overall sequence.

Bridging Software and Hardware Interactions
In systems that bridge software and hardware, the identity function can be useful for understanding how signals are passed. For example, a command sent from a ground control station to a drone might pass through several layers of software before being translated into a physical action by a motor controller. At certain points in this communication chain, the signal might be passed through without modification, serving as an identity function in the data transmission process. This ensures that the original command is preserved as it navigates the complex system architecture, allowing for precise execution by the hardware.
In conclusion, the identity function, despite its apparent simplicity, is a powerful concept that underpins much of modern computing and system design. Its ability to reflect input without alteration is not merely a mathematical curiosity but a fundamental tool for ensuring data integrity, enabling modularity in software, and facilitating the logical flow of information in complex technological systems. Whether it’s in the intricacies of data processing, the elegance of functional programming, or the underlying logic of advanced autonomous systems, the identity function plays a silent but crucial role in making our technology work reliably and predictably.
