In the rapidly evolving landscape of drone technology, understanding the underlying network infrastructure is becoming increasingly crucial for pilots, developers, and enthusiasts alike. While the focus often lands on camera quality, flight stability, or cinematic capabilities, the fundamental networking principles that enable seamless communication are just as vital. Among these principles, the concept of an IP subnet is a cornerstone for managing and segmenting networks, particularly as drones become more interconnected and sophisticated. This article delves into the intricacies of IP subnets, explaining their purpose, how they function, and their relevance within the broader context of drone operations and development.
The Foundation: Understanding IP Addresses
Before dissecting the subnet, it’s essential to grasp the concept of an IP (Internet Protocol) address. An IP address is a unique numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. It serves two primary functions: host or network interface identification and location addressing. Think of it as a digital mailing address for your drone when it’s communicating with other devices, whether that’s a ground control station, a server in the cloud, or even other drones in a swarm.
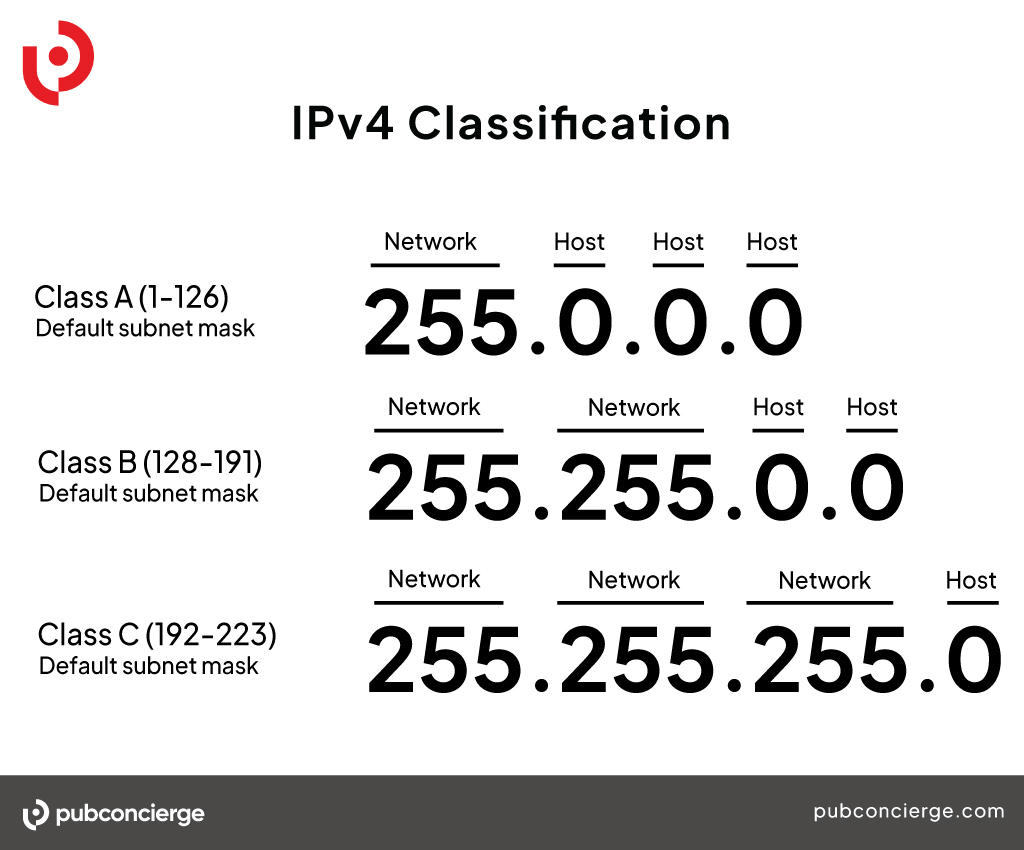
IP addresses come in two main versions: IPv4 and IPv6. IPv4, the older and more prevalent version, consists of 32 bits, typically represented as four decimal numbers (0-255) separated by dots (e.g., 192.168.1.10). This format provides a vast number of unique addresses, but with the explosion of connected devices, the pool of available IPv4 addresses is dwindling. IPv6, on the other hand, uses 128 bits and is represented by eight groups of four hexadecimal digits separated by colons (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334). IPv6 offers a virtually inexhaustible supply of addresses, designed to accommodate the future of connected devices, including the ever-increasing number of drones.
The Need for Network Segmentation
In any network, especially a complex one involving multiple devices, simply assigning unique IP addresses isn’t always the most efficient or secure approach. Imagine a large drone fleet operating simultaneously. If all drones were on the same vast network, managing communication, troubleshooting issues, and ensuring data security would become incredibly challenging. This is where the concept of network segmentation comes into play, and this is precisely where IP subnets shine.
Network segmentation involves dividing a larger network into smaller, more manageable sub-networks, or subnets. This division offers several significant advantages, including improved performance, enhanced security, and simplified administration. By breaking down a network into smaller segments, traffic within each segment is localized, reducing congestion on the overall network. This is particularly beneficial in drone operations where real-time data transmission, such as video feeds or telemetry, is critical.
Subnetting: The Art of Division
Subnetting is the process of taking a single, larger IP network and dividing it into multiple smaller networks. This is achieved by using a subnet mask. A subnet mask is a 32-bit number (for IPv4) that works in conjunction with an IP address to determine which part of the IP address represents the network and which part represents the host.
The Role of the Subnet Mask
The subnet mask essentially “masks” out the network portion of an IP address, leaving the host portion. In its binary form, a subnet mask consists of a series of consecutive ‘1’s followed by a series of consecutive ‘0’s. The ‘1’s indicate the network portion, and the ‘0’s indicate the host portion. For example, a common IPv4 subnet mask is 255.255.255.0. In binary, this is:
11111111.11111111.11111111.00000000
When a subnet mask is applied to an IP address, a logical “AND” operation is performed. This operation identifies the network address. Any bits that are ‘1’ in both the IP address and the subnet mask will result in a ‘1’ in the network address. Any bits that are ‘0’ in either the IP address or the subnet mask will result in a ‘0’ in the network address.
Consider an IP address 192.168.1.10 with a subnet mask of 255.255.255.0.
IP Address (Binary): 11000000.10101000.00000001.00001010
Subnet Mask (Binary): 11111111.11111111.11111111.00000000
Network Address (Binary): 11000000.10101000.00000001.00000000
Network Address (Decimal): 192.168.1.0
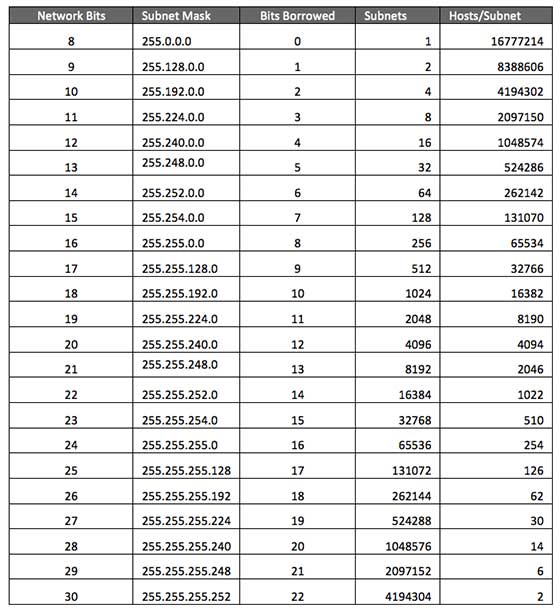
This means that all devices with IP addresses starting with 192.168.1. are on the same subnet. The “0” part of the subnet mask indicates that the last 8 bits are available for host addresses within this subnet. This subnet can accommodate 2^8 – 2 = 254 usable host addresses (excluding the network address and the broadcast address).
How Subnetting Creates Smaller Networks
By changing the subnet mask, we can effectively “borrow” bits from the host portion of an IP address and use them to define smaller networks. This process is known as Variable Length Subnet Masking (VLSM). For instance, if we have the IP network 192.168.1.0 and want to create two subnets, we can use a subnet mask like 255.255.255.128.
Original Network: 192.168.1.0/24 (Subnet mask 255.255.255.0)
New Subnet Mask: 255.255.255.128 (Binary: 11111111.11111111.11111111.10000000)
With this new mask, we have borrowed one bit from the host portion. This allows us to create two subnets:
- Subnet 1: Network Address 192.168.1.0. Host addresses will range from 192.168.1.1 to 192.168.1.126.
- Subnet 2: Network Address 192.168.1.128. Host addresses will range from 192.168.1.129 to 192.168.1.254.
Each of these subnets now has 2^(8-1) – 2 = 126 usable host addresses. This granular control allows network administrators to allocate IP address space more efficiently and to create networks tailored to specific needs.
Practical Applications in Drone Technology
The principles of IP subnetting, while abstract, have tangible and significant implications for how drones operate and interact within networks. As drones move beyond simple remote-controlled aircraft to become integral components of complex systems, understanding subnetting becomes less of a technical niche and more of a necessity.
Enhancing Drone Communication and Control
In scenarios involving multiple drones, such as large-scale aerial surveying, drone swarms for entertainment, or coordinated emergency response operations, a robust communication infrastructure is paramount. IP subnets play a crucial role in segmenting these networks. For example, a fleet of drones might be divided into subnets based on their operational zone, function, or even their physical proximity.
Ground Control Station (GCS) Networks
A common use case is the network managed by a Ground Control Station (GCS). A GCS might be responsible for managing dozens or even hundreds of drones. Instead of putting all drones and the GCS on a single flat network, subnetting allows for the creation of a dedicated subnet for drone communication. This subnet can be configured with specific security policies, bandwidth allocations, and routing rules. This isolation ensures that commands sent from the GCS to a specific drone or group of drones are not interfered with by unrelated network traffic, and it prevents a security breach on one drone from compromising the entire fleet.
Inter-Drone Communication
As drones become more autonomous and capable of collaborating, direct communication between drones is increasingly important. In a swarm scenario, drones might need to share real-time positional data, environmental readings, or task progress. By placing these drones on a dedicated subnet, their inter-communication can be optimized. This reduces latency, as data doesn’t have to traverse multiple routers and network segments. Furthermore, specific security protocols can be applied to this subnet, ensuring that only authorized drones can communicate with each other, preventing malicious actors from injecting false data or disrupting swarm behavior.
Security and Isolation
Security is a paramount concern in drone operations, especially when dealing with sensitive data, critical infrastructure inspections, or military applications. IP subnetting is a fundamental tool for implementing network security.
Network Segmentation for Security
By dividing a network into smaller subnets, organizations can enforce stricter access controls. For instance, drones used for public safety surveillance might be placed on a highly secure subnet, separate from less critical networks. This segregation means that if a drone on a less secure subnet is compromised, the attacker’s access is limited to that specific subnet, preventing them from reaching the more sensitive drone data or control systems. Firewalls can then be configured to control traffic flow between these subnets, allowing only necessary communication while blocking unauthorized access.
Protecting Sensitive Data Transmission
When drones transmit sensitive data, such as high-resolution imagery, thermal scans, or proprietary sensor readings, ensuring the integrity and confidentiality of this data is vital. Subnetting, combined with encryption and authentication protocols, creates a more secure communication channel. By isolating the data transmission on a dedicated subnet, the potential attack surface is reduced, and administrators can implement specific security measures tailored to the sensitivity of the data being transmitted. This is particularly relevant for enterprise-level drone solutions where data privacy and compliance are critical.
Advanced Concepts and Future Trends
The application of IP subnetting in drone technology is not static. As drone capabilities expand and network technologies advance, so too will the ways in which we leverage subnetting for more sophisticated operations.
IPv6 and Drone Networks
With the limitations of IPv4 becoming increasingly apparent, the adoption of IPv6 is inevitable. IPv6’s massive address space will simplify network management for large fleets of drones. Instead of complex subnetting schemes to conserve IPv4 addresses, administrators can assign unique, globally routable IPv6 addresses to each drone, and potentially even to individual sensors or components on a drone.
Simplified Address Management
The sheer number of available IPv6 addresses means that complex subnetting to fit devices into smaller blocks becomes less of a necessity for address conservation. Each drone, each GCS, and each associated ground infrastructure component can be assigned an IP address from a vast pool. This simplification can streamline deployment and reduce the chances of misconfiguration. However, it’s important to note that even with abundant addresses, the principles of subnetting for network segmentation and security remain critically important. VLSM will still be used to logically divide networks for organizational and security purposes, not just for address scarcity.
Enhanced Connectivity and Mobility
IPv6 also offers features like stateless autoconfiguration, which can simplify the process of bringing new drones online. Furthermore, IPv6’s mobility features can improve how drones maintain network connectivity as they move across different networks or geographic locations, which is a common scenario for drones operating over extended areas. This can lead to more seamless transitions and reduced communication interruptions.
Software-Defined Networking (SDN) and Network Function Virtualization (NFV)
The integration of drones with emerging networking paradigms like Software-Defined Networking (SDN) and Network Function Virtualization (NFV) will further amplify the importance of well-defined subnets. SDN separates the control plane from the data plane, allowing for centralized network management and dynamic configuration. NFV enables network functions, such as firewalls or routing, to be run as software on general-purpose hardware.
Dynamic Network Configuration for Drones
In an SDN environment, subnets can be dynamically created, modified, and torn down based on the operational needs of the drones. For instance, as a drone transitions from a flight mission to a maintenance check, its network profile and subnet assignment could be automatically adjusted. This agility is crucial for complex, multi-mission drone operations. NFV, when applied to drone networks, could allow for virtualized network security functions or routing capabilities to be deployed closer to the drone, potentially even on the drone itself or a local gateway, further enhancing performance and security through optimized subnet configurations.
The Future of Drone Network Architectures
The convergence of these technologies will pave the way for highly intelligent, adaptive, and secure drone networks. Understanding IP subnetting is the foundational knowledge that allows professionals to design, implement, and manage these advanced network architectures. As drones become more integrated into our daily lives, from delivery services and infrastructure inspection to personal aerial photography, the silent, efficient, and secure operation of their underlying networks, powered by the principles of IP subnetting, will be the invisible force that makes it all possible.

