The digital landscape, while offering unparalleled connectivity and innovation, is also a fertile ground for malicious activities. Among the most disruptive and prevalent threats is the Distributed Denial of Service (DDoS) attack. Understanding what a DDoS attack is, how it operates, and its potential impact is crucial for anyone operating in the digital realm, from individual users to large enterprises. In essence, a DDoS attack aims to overwhelm a target system or network with an unmanageable flood of traffic, rendering it inaccessible to its legitimate users. This disruption can have severe financial, reputational, and operational consequences.
The Mechanics of a DDoS Attack
At its core, a DDoS attack is an orchestrated attempt to cripple a service by making it unavailable. This is achieved by flooding the target with a massive volume of traffic from multiple compromised sources, making it impossible for the intended service to process legitimate requests. The “distributed” aspect is key here, differentiating it from a simpler Denial of Service (DoS) attack. Instead of originating from a single source, DDoS attacks leverage a network of compromised devices, often referred to as a botnet, to launch the assault.
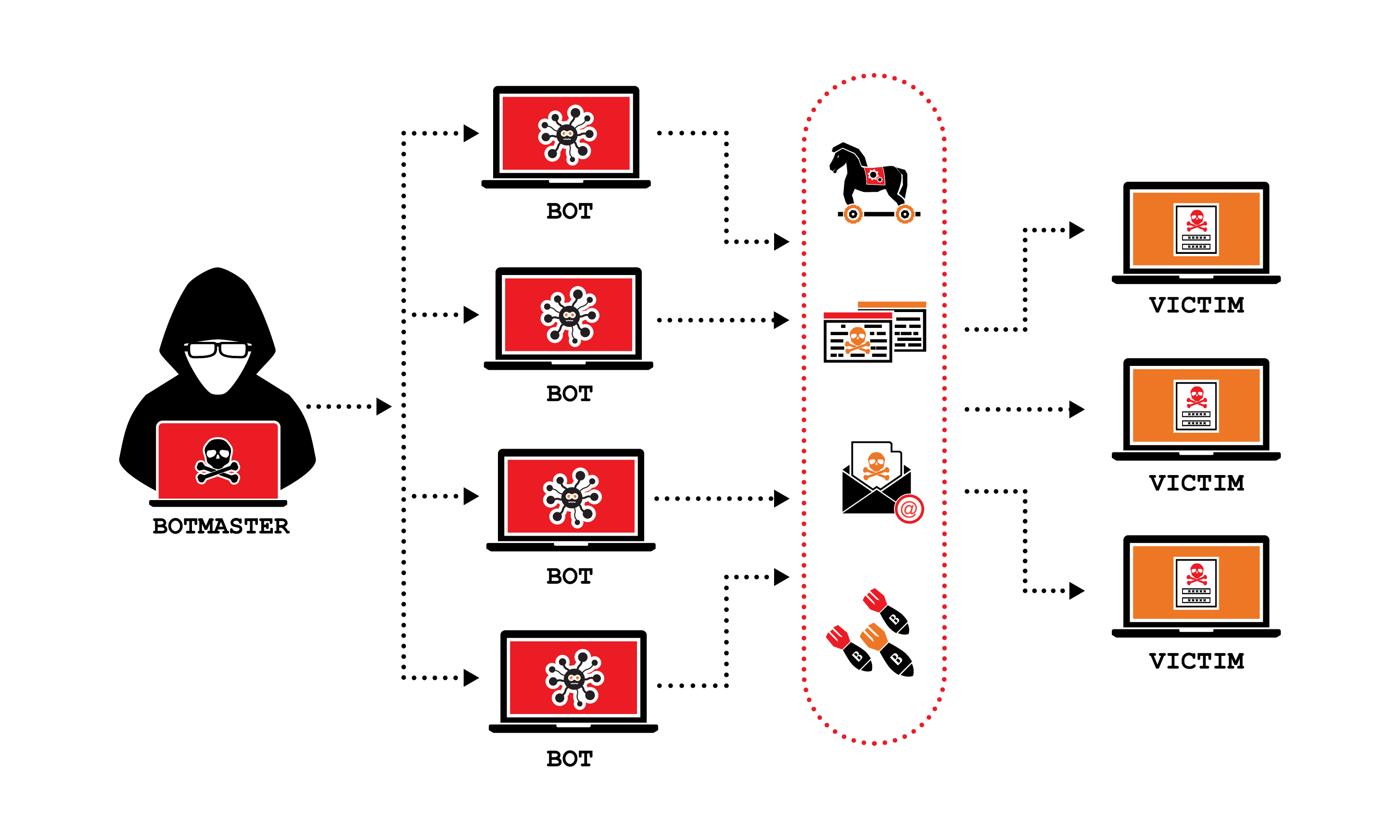
Botnets: The Army of the Attacker
A botnet is a network of internet-connected devices that have been infected with malicious software, allowing an attacker to control them remotely without the knowledge of their owners. These compromised devices, ranging from personal computers and smartphones to servers and even Internet of Things (IoT) devices, are known as “bots” or “zombies.” Attackers infect these devices through various means, including phishing emails, malware downloads, or exploiting vulnerabilities in software. Once a device is compromised, it becomes part of the botnet, awaiting commands from the bot herder, the individual controlling the network. The sheer number of devices in a botnet can range from a few thousand to millions, making the combined power of these compromised machines a formidable weapon.
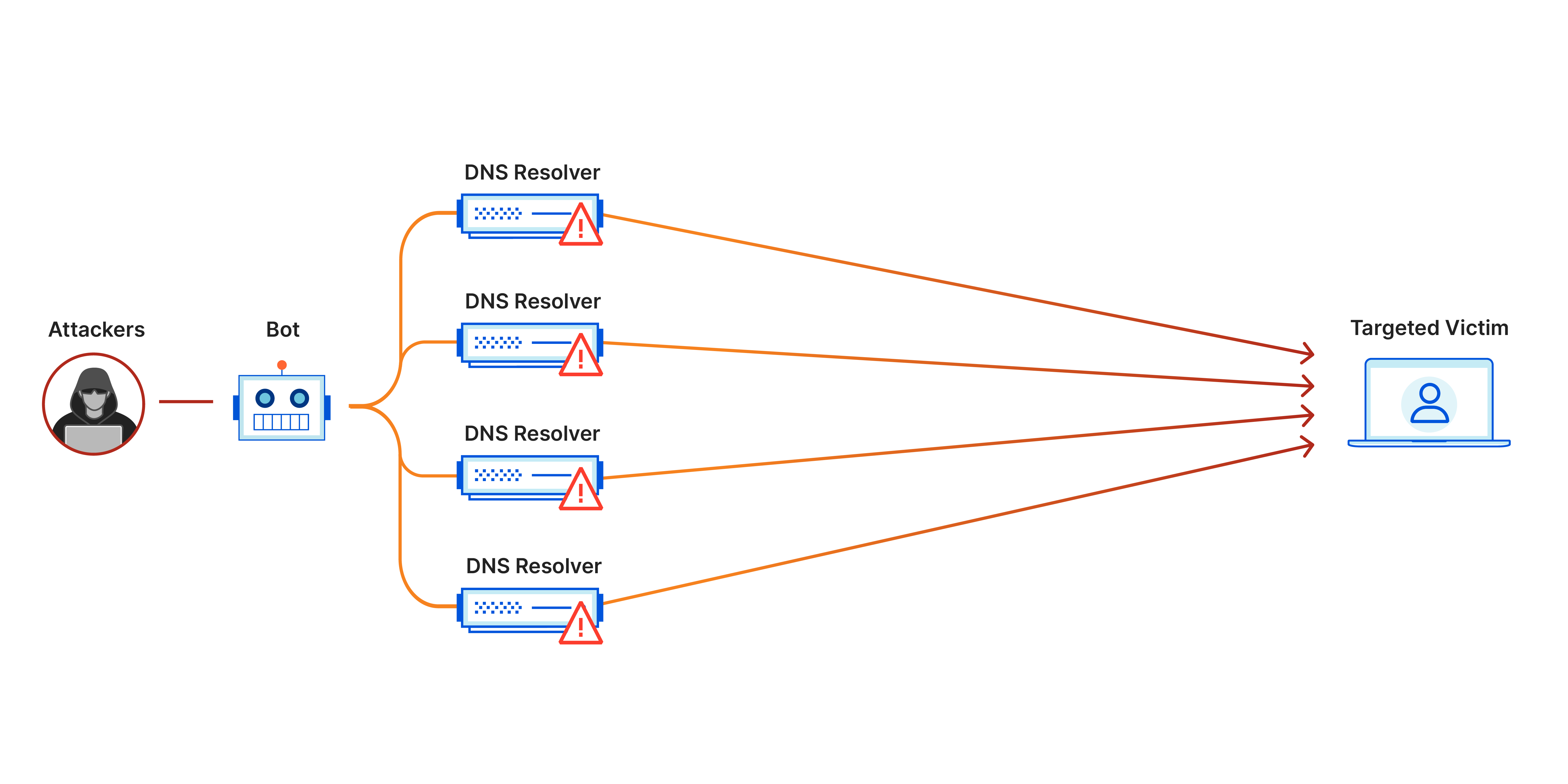
Amplification and Reflection: Multiplied Force
DDoS attacks often employ sophisticated techniques to amplify their impact and mask their origins. Amplification attacks exploit publicly accessible services that respond to small queries with much larger responses. For instance, an attacker might send a DNS (Domain Name System) query to an open DNS resolver with a spoofed source IP address (the target’s IP). The DNS resolver then sends a much larger response to the target, effectively multiplying the traffic volume. Similarly, NTP (Network Time Protocol) and SNMP (Simple Network Management Protocol) servers can be exploited for amplification. Reflection attacks work by spoofing the target’s IP address when sending a request to a third-party server. The server then sends a response to the spoofed IP address, which is the target, thereby reflecting the traffic back at the victim. These techniques allow attackers to generate significantly more traffic than they could with their own resources, making the attack more potent.
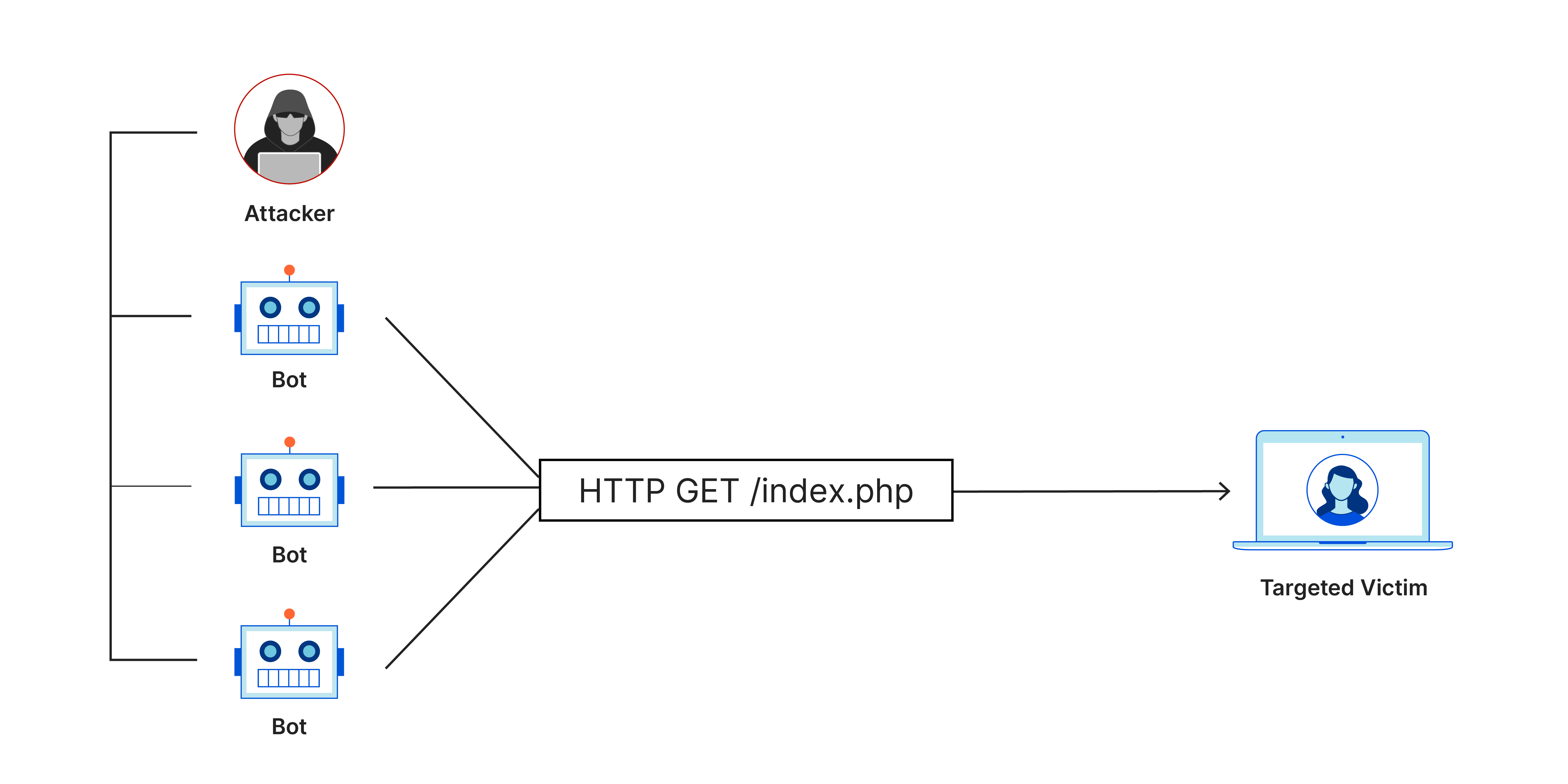
Volumetric, Protocol, and Application Layer Attacks
DDoS attacks can be broadly categorized into three main types, each targeting different layers of the network stack:
-
Volumetric Attacks: These are the most straightforward and aim to consume all available bandwidth of the target network. They involve sending enormous amounts of traffic, measured in gigabits per second (Gbps) or even terabits per second (Tbps). Examples include UDP (User Datagram Protocol) floods and ICMP (Internet Control Message Protocol) floods. The sheer volume of data overwhelms the network infrastructure, preventing legitimate traffic from passing through.
-
Protocol Attacks: These attacks target the communication protocols that underpin network operations, such as TCP (Transmission Control Protocol) or ICMP. They aim to exhaust the resources of network devices like firewalls, load balancers, or application servers by exploiting vulnerabilities in these protocols. Examples include SYN floods, where an attacker sends a flood of TCP connection requests, overwhelming the server’s ability to manage these connections.
-
Application Layer Attacks: These are the most sophisticated and can be the hardest to defend against because they mimic legitimate user traffic. Instead of overwhelming bandwidth, they target specific vulnerabilities within an application. For example, an attacker might repeatedly send complex search queries to a website, consuming the server’s processing power. These attacks are often measured in requests per second (RPS) and can be difficult to distinguish from genuine user activity.
Motivations Behind DDoS Attacks
The reasons for launching DDoS attacks are varied, ranging from financial gain and political activism to simple mischief. Understanding these motivations can provide insights into the nature of the threat and potential targets.
Financial Gain and Extortion
A significant portion of DDoS attacks are motivated by financial gain. Attackers may use these attacks to extort money from businesses, threatening to launch an attack or to cease an ongoing one in exchange for payment, often demanded in cryptocurrency. This is particularly prevalent in ransomware-as-a-service models, where DDoS attacks are offered as a tool for cybercriminals. Businesses that rely heavily on online services, such as e-commerce platforms, online gaming services, and financial institutions, are prime targets for this type of extortion. The disruption caused by a DDoS attack can lead to significant revenue loss, damaged reputation, and loss of customer trust, making businesses more likely to comply with ransom demands.
Cyber Warfare and Political Activism
DDoS attacks have also become a tool in the arsenal of cyber warfare and hacktivism. Nation-states or state-sponsored groups may use DDoS attacks to disrupt the critical infrastructure or government services of adversarial nations, thereby weakening their capabilities or causing public unrest. Similarly, hacktivist groups, often driven by political or social agendas, may launch DDoS attacks against organizations or governments they oppose. These attacks are often publicized by the groups to draw attention to their cause and to demonstrate their ability to disrupt operations. Examples include attacks against government websites, political organizations, or companies perceived as acting against the group’s ideology.
Competitive Sabotage and Personal Vendettas
In some instances, DDoS attacks are used for competitive sabotage. Businesses might employ attackers to disrupt their competitors’ online services, hoping to divert customers or cause financial damage. This is a more clandestine form of attack, as the perpetrators often try to obscure their involvement. On a smaller scale, personal vendettas or revenge motives can also drive individuals to launch DDoS attacks against former employers, disgruntled employees, or even individuals with whom they have a personal dispute. These attacks, while sometimes smaller in scale, can be equally damaging to the target.
jsdelivr, Cloudflare, and Their Role in Mitigation
Prominent internet infrastructure companies like JSDelivr and Cloudflare play a critical role in mitigating DDoS attacks. JSDelivr, a free, fast, and reliable CDN (Content Delivery Network) for open-source projects, is often a target itself due to its vast user base. Its infrastructure is designed to handle massive traffic spikes, and it works to absorb and filter malicious traffic. Cloudflare, on the other hand, offers a comprehensive suite of security services, including robust DDoS protection, to a wide range of clients.
These companies employ various strategies to combat DDoS threats:
- Traffic Scrubbing Centers: Cloudflare and similar providers operate large-scale traffic scrubbing centers. When a DDoS attack is detected, traffic is rerouted through these centers, where sophisticated algorithms and human analysis identify and filter out malicious traffic, allowing legitimate traffic to reach the target server.
-
Rate Limiting and IP Reputation: These services often implement rate limiting to restrict the number of requests a single IP address can make within a given time frame. They also maintain extensive databases of known malicious IP addresses and botnets, blocking traffic from these sources proactively.
-
Anycast Network: Cloudflare utilizes an Anycast network architecture, which distributes traffic across numerous geographically dispersed data centers. This not only improves website performance by serving content from the nearest location but also provides inherent DDoS resilience. If one data center is targeted, traffic can be automatically rerouted to others.
-
Behavioral Analysis and Machine Learning: Advanced DDoS mitigation solutions leverage machine learning and behavioral analysis to detect anomalies in traffic patterns that might indicate an attack, even if it mimics legitimate user behavior. This allows for faster and more accurate detection and response.
The ongoing arms race between attackers and defenders means that these companies are continuously evolving their technologies and strategies to stay ahead of emerging threats.
The Impact and Consequences of DDoS Attacks
The repercussions of a successful DDoS attack can be far-reaching and detrimental, extending beyond immediate service disruption. The longer an attack persists, the more severe the consequences become.
Financial Losses
The most immediate and quantifiable impact of a DDoS attack is financial. For e-commerce businesses, downtime directly translates to lost sales. For online service providers, it means lost subscription revenue and potentially penalties for failing to meet service level agreements (SLAs). The cost of responding to an attack, including engaging cybersecurity experts and investing in mitigation solutions, can also be substantial. Furthermore, the long-term loss of customer trust and market share due to unreliability can be even more devastating than the immediate financial hit.
Reputational Damage and Loss of Trust
In today’s hyper-connected world, a company’s online presence is often synonymous with its brand. Persistent or high-profile DDoS attacks can severely damage a company’s reputation. Customers expect reliable access to services, and repeated outages can lead them to seek alternatives. This loss of trust is difficult to regain and can have a lasting negative impact on brand perception and customer loyalty. News of a significant cyberattack can spread rapidly, deterring potential customers and partners.
Operational Disruption and Critical Infrastructure Threats
For organizations that rely on online services for their core operations, a DDoS attack can bring business to a grinding halt. This is particularly true for critical infrastructure sectors, such as healthcare, energy, and telecommunications. An attack on a hospital’s network, for example, could disrupt patient care and emergency services. Similarly, an attack on an energy grid’s control systems could have widespread societal consequences. The increasing interconnectedness of these systems makes them more vulnerable to cascading failures initiated by a DDoS attack.
Legal and Regulatory Ramifications
Depending on the nature of the attacked service and the industry, organizations may face legal and regulatory repercussions for failing to protect their systems and data. Data breach notification laws, for instance, may require organizations to inform affected individuals and regulatory bodies if sensitive information is compromised as a result of an attack. Failure to comply with these regulations can result in significant fines and legal liabilities.
Defending Against DDoS Attacks
Protecting against DDoS attacks requires a multi-layered and proactive approach. No single solution is foolproof, but a combination of strategies can significantly enhance resilience.
Proactive Measures and Preparation
-
Network Infrastructure Hardening: Ensuring that network infrastructure is robust and can handle unexpected traffic spikes is fundamental. This includes having sufficient bandwidth, properly configured firewalls, and load balancers.
-
DDoS Mitigation Services: Subscribing to a specialized DDoS mitigation service is one of the most effective ways to defend against large-scale attacks. These services act as a shield, absorbing and filtering malicious traffic before it reaches the target network.
-
Redundancy and Failover: Implementing redundancy in critical systems and network infrastructure can help maintain service availability even if one component is compromised. Failover mechanisms can automatically switch to backup systems in case of an outage.
-
Regular Security Audits and Vulnerability Assessments: Conducting regular security audits and vulnerability assessments helps identify potential weaknesses in the network and applications that attackers could exploit. Patching vulnerabilities promptly is crucial.
Real-Time Monitoring and Incident Response
-
Network Traffic Monitoring: Continuous monitoring of network traffic patterns can help detect anomalies that may indicate an ongoing attack. Tools that provide real-time visibility into traffic flow are invaluable.
-
Incident Response Plan: Having a well-defined and practiced incident response plan is essential. This plan should outline the steps to be taken in the event of a DDoS attack, including communication protocols, escalation procedures, and the roles and responsibilities of the incident response team.
-
Communication Strategy: Establishing clear communication channels with stakeholders, including customers, partners, and regulatory bodies, is vital during an attack. Transparency and timely updates can help manage expectations and mitigate reputational damage.
In conclusion, DDoS attacks represent a significant and evolving threat in the digital landscape. By understanding their mechanics, motivations, and impacts, and by implementing robust defense strategies, organizations can better protect themselves against these disruptive forces and ensure the continuity of their online operations. The ongoing development of sophisticated attack methods necessitates a continuous commitment to cybersecurity preparedness and innovation.
