In the realm of advanced technology, particularly within sectors that handle sensitive data, critical infrastructure, or national security concerns, the concept of “security clearance” takes on paramount importance. While often associated with government roles and military personnel, the implications of security clearance extend significantly into the world of cutting-edge technology, influencing who can develop, operate, and access certain sophisticated systems. For professionals and enthusiasts within the Tech & Innovation sphere, understanding security clearance is not just a matter of career progression; it’s a foundational element for engaging with groundbreaking advancements.
This article delves into the meaning and significance of security clearance within the context of technological innovation. We will explore what it entails, why it is crucial for certain technological fields, the different levels involved, and the rigorous processes that underpin its attainment. Ultimately, we aim to illuminate how this concept shapes the landscape of technological development and deployment, ensuring that sensitive innovations are handled responsibly and with the utmost security.
The Core Meaning and Purpose of Security Clearance
At its heart, a security clearance is an official determination that an individual is eligible for access to classified national security information or sensitive government systems. This determination is made by authorized government agencies following an investigation into the individual’s background, loyalty, character, and reliability. The primary purpose is to protect national security by preventing individuals who pose a risk of espionage, sabotage, or unauthorized disclosure of sensitive information from gaining access to it.
Beyond Government: The Tech Industry Nexus
While the most visible instances of security clearances are within government and defense sectors, their influence permeates the broader technology industry. Companies that develop or integrate technologies for government clients, particularly in defense, intelligence, aerospace, and critical infrastructure, often require their employees to hold security clearances. This is because these companies are privy to classified projects, proprietary technologies, and sensitive data that are vital to national security.
For instance, in the development of advanced AI Follow Mode technologies for defense applications, or autonomous flight systems used for reconnaissance, the underlying algorithms, sensor data, and operational parameters are often classified. Engineers, software developers, data scientists, and project managers working on such innovations must possess the necessary clearances to legally access and contribute to these projects. Without them, participation is simply not possible, acting as a gatekeeper for who can innovate in these critical areas.
Different Levels of Access and Trust
Security clearances are not monolithic; they exist in various levels, each denoting a different degree of access and sensitivity. Understanding these levels is crucial for navigating career paths in technology that intersect with national security.
Confidential
This is the lowest level of clearance. Individuals granted Confidential clearance are eligible to access information that, if disclosed without authorization, could cause “damage” to national security. This might include certain technical blueprints for non-critical systems or operational procedures for less sensitive equipment. In the tech industry, this could apply to personnel working on less sensitive aspects of projects that have a national security component, such as administrative roles or those involved in developing commercially viable technologies with potential dual-use applications.
Secret
The Secret clearance grants access to information that, if disclosed without authorization, could cause “serious damage” to national security. This level is common for individuals working on more advanced projects, including those involving sophisticated sensor data analysis, early-stage development of navigation systems, or initial research into novel stabilization techniques. For companies developing advanced Mapping and Remote Sensing technologies for governmental use, Secret clearance is often a prerequisite for engineers and researchers involved in the core development of these systems.
Top Secret
This is the highest level of clearance and grants access to information that, if disclosed without authorization, could cause “exceptionally grave damage” to national security. This includes highly sensitive intelligence, advanced weapon system designs, and strategic plans. In the tech sector, Top Secret clearance is typically required for individuals working on the most sensitive aspects of national security technology, such as cutting-edge advancements in AI for autonomous systems, highly classified aspects of drone technology, or proprietary encryption methods. Personnel involved in the direct development of Autonomous Flight capabilities for critical missions would likely require this level of clearance.
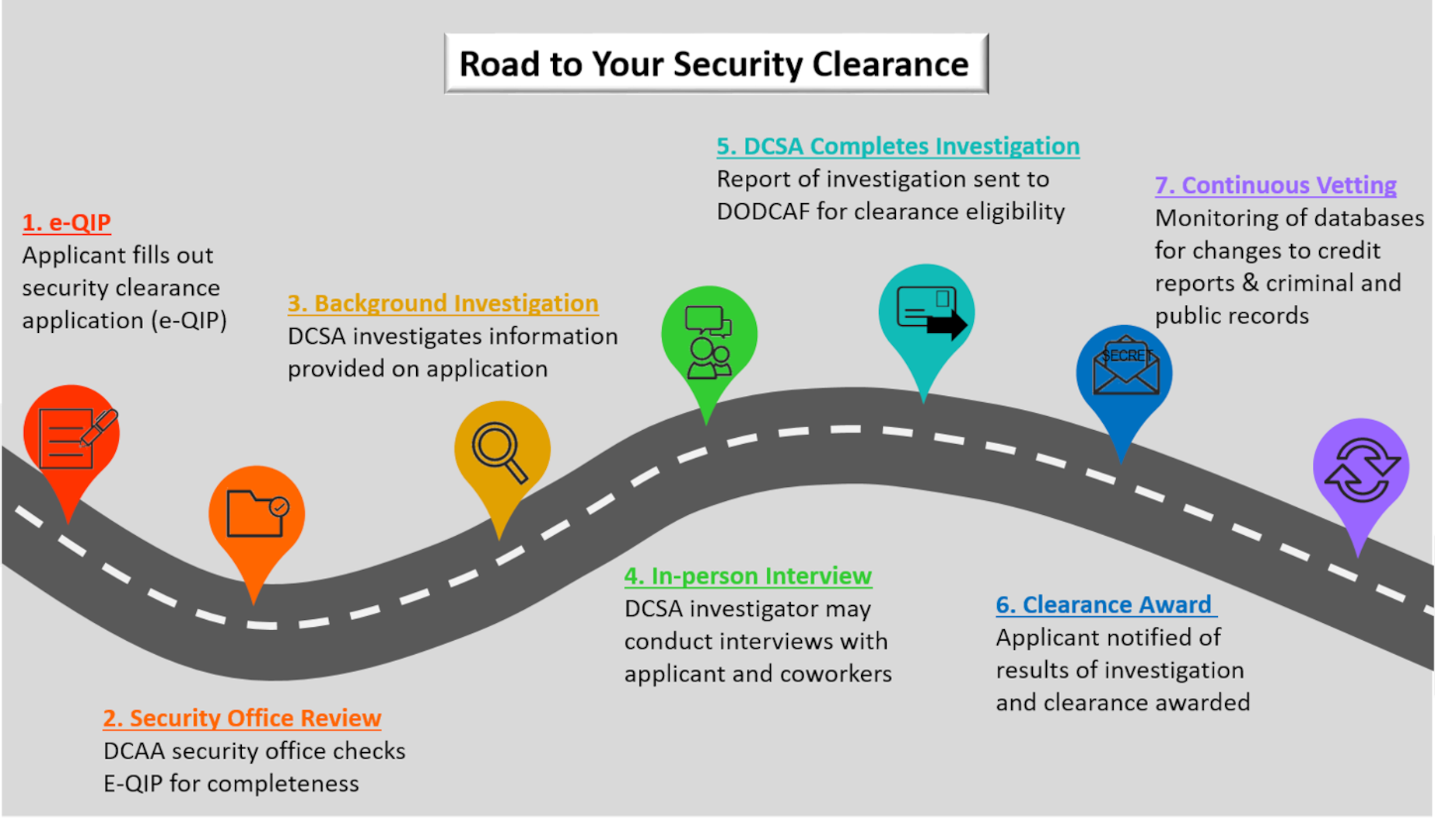
The Rigorous Process of Obtaining a Security Clearance
The process of obtaining a security clearance is designed to be thorough and exhaustive. It aims to identify any potential vulnerabilities or risks associated with an individual’s background that could compromise national security. This process can be lengthy and demanding, requiring honesty, patience, and cooperation from the applicant.
The Standard Investigation Process
The investigation typically involves several key components, each designed to scrutinize different facets of an applicant’s life.
Personal History Questionnaire (SF-86)
The journey begins with the completion of a detailed questionnaire, often the Standard Form 86 (SF-86), Questionnaire for National Security Positions. This document requires applicants to provide comprehensive information about their personal history, including:
- Employment History: Details of all jobs held over a significant period (often 7-10 years or more).
- Education History: Records of all educational institutions attended.
- Residence History: Where the applicant has lived over a significant period.
- Foreign Travel and Relationships: Details of international travel, foreign contacts, and any foreign influence.
- Financial History: Information on debts, assets, and financial stability, as potential financial difficulties can be exploited.
- Criminal Record: Any arrests, charges, or convictions.
- Drug and Alcohol Use: A candid account of past usage.
- Mental and Emotional Health: Information about any conditions that might affect reliability.
- Military Service: Details of any past military duty.
- References: Contact information for individuals who can attest to the applicant’s character and reliability.
The sheer volume of detail required in the SF-86 necessitates meticulous attention to accuracy and completeness. Any discrepancies or omissions can lead to significant delays or even disqualification.
Interview with an Investigator
Following the submission of the SF-86, a trained background investigator will conduct an in-person interview with the applicant. This interview is an opportunity for the investigator to clarify information provided in the questionnaire, delve deeper into specific areas, and assess the applicant’s demeanor and truthfulness. The investigator will ask probing questions to gain a comprehensive understanding of the applicant’s character and suitability.
Interviews with Associates and References
A crucial part of the investigation involves interviewing individuals who know the applicant. These typically include:
- Supervisors and Coworkers: To assess professional conduct, reliability, and teamwork.
- Neighbors: To gauge community integration and general behavior.
- Friends and Acquaintances: To provide a broader perspective on the applicant’s character and past actions.
- Family Members: To understand personal relationships and any potential influences.
The investigator will ask these individuals about the applicant’s integrity, honesty, judgment, discretion, and any concerns they may have regarding the applicant’s suitability for access to sensitive information.
Record Checks
Beyond personal interviews, the investigation includes comprehensive record checks, such as:
- Credit Bureaus: To assess financial responsibility.
- Criminal Justice Records: Local, state, and federal databases for any legal issues.
- Civil Records: To identify any significant civil litigation.
- Educational Institutions: To verify academic credentials.
- Previous Employers: To confirm employment history and reasons for departure.
The thoroughness of these checks ensures that all aspects of an applicant’s life are scrutinized for any potential security risks.
Why Security Clearance Matters in Tech Innovation
In the fast-paced world of technology, security clearance is not merely a bureaucratic hurdle; it is an enabler and a safeguard, particularly for innovations that have national security implications.
Enabling Access to High-Impact Projects
For technology companies and their employees, holding a security clearance can unlock access to some of the most challenging and impactful projects. This is especially true for sectors developing advanced solutions in areas like:
- Advanced Sensor Technologies: For surveillance, reconnaissance, and intelligence gathering.
- Cybersecurity Solutions: Protecting critical government and military networks.
- Artificial Intelligence and Machine Learning: For autonomous systems, predictive analysis, and threat detection.
- Next-Generation Communication Systems: Ensuring secure and resilient communication for national security operations.
Without the appropriate clearance, highly skilled engineers and researchers might be excluded from contributing to these vital advancements, limiting both their professional growth and the potential for innovation.
Ensuring Responsible Development and Deployment
The stringent vetting process associated with security clearances ensures that individuals entrusted with sensitive technologies are of sound character and possess a strong sense of loyalty and discretion. This is vital for preventing:
- Espionage and Sabotage: Malicious actors seeking to steal or disrupt sensitive technological developments.
- Unauthorized Disclosure: Accidental or intentional leaks of classified information that could compromise national security.
- Misuse of Technology: The diversion of advanced technologies for illicit purposes.
By restricting access to cleared personnel, organizations can maintain tighter control over the development lifecycle, from initial research and prototyping to final deployment, thereby upholding national security interests.

Fostering Trust and Confidence
For government agencies and defense organizations, partnering with technology firms requires a high degree of trust. The requirement for security clearances among key personnel in these firms builds confidence that the sensitive projects entrusted to them will be handled with the utmost professionalism and security. This trust is fundamental for fostering long-term collaborations and driving innovation that meets the stringent demands of national security.
In conclusion, security clearance, while seemingly a governmental formality, plays a critical role in shaping the landscape of technological innovation. It serves as a robust mechanism for protecting national security by ensuring that only vetted and trustworthy individuals have access to sensitive technologies and information. For those operating within the tech industry, especially in fields intersecting with defense and intelligence, understanding the implications and processes of security clearance is essential for career advancement and for contributing to the development of technologies that safeguard national interests. It is a testament to the fact that in the pursuit of groundbreaking innovation, responsibility and security are paramount.