The question of “what is a good software for storing private data?” is becoming increasingly relevant in our digital age. As we generate and collect more personal information, the need for secure and reliable storage solutions grows. Whether it’s sensitive financial documents, personal journals, family photos, or proprietary business information, the way we store this data directly impacts its privacy and accessibility. This article delves into the critical aspects of choosing software for storing private data, exploring the different types of solutions available, the key features to consider, and best practices for ensuring the utmost security.

Understanding Your Private Data Storage Needs
Before diving into specific software solutions, it’s crucial to understand the nature and volume of your private data, as well as your specific requirements for accessing and managing it. Different types of data necessitate different storage approaches.
Differentiating Data Types and Their Sensitivity
Personal Documents: This category includes anything from identification documents (passports, driver’s licenses), financial records (bank statements, tax returns), legal documents (wills, contracts), and health records. These are often highly sensitive and require robust encryption and access controls.
Creative Assets: For photographers, videographers, artists, and other creatives, private data might encompass unreleased projects, RAW image files, video footage, design drafts, and personal portfolios. The volume of this data can be substantial, requiring ample storage capacity and efficient organization.
Intellectual Property and Business Data: Entrepreneurs and businesses often need to store proprietary algorithms, trade secrets, client lists, confidential project plans, and internal communications. The security of this data is paramount for competitive advantage and legal compliance.
Personal Memories and Digital Legacies: This encompasses cherished family photos, videos, personal writings, and even digital journals. While not always strictly sensitive in a legal or financial sense, their sentimental value makes them incredibly private and worthy of secure storage.
Assessing Your Storage Requirements
Your needs extend beyond just security. Consider these factors when evaluating storage software:
Volume of Data: Are you storing a few gigabytes of documents or terabytes of high-resolution media? This will dictate the capacity you need and the most cost-effective solutions.
Accessibility: Do you need to access your data from multiple devices (desktop, laptop, tablet, smartphone)? Do you need offline access, or is cloud-based access sufficient?
Collaboration Needs: Will you need to share specific files or folders with trusted individuals? If so, the software should offer secure sharing capabilities.
Backup and Recovery: How critical is it to recover your data in case of hardware failure, accidental deletion, or cyberattack? Robust backup and recovery features are non-negotiable for truly private data.
Longevity: Are you storing data for the short term or for archival purposes that might span decades? This influences the choice of storage media and the stability of the software provider.
Exploring Software Solutions for Private Data Storage
The landscape of data storage software is diverse, offering a range of options from cloud-based services to local, self-hosted solutions. Each comes with its own set of advantages and disadvantages regarding security, cost, and accessibility.
Cloud-Based Storage Solutions: Convenience Meets Security
Cloud storage offers unparalleled convenience, allowing access to your data from anywhere with an internet connection. However, selecting a provider that prioritizes your privacy is essential.
Secure Cloud Storage Providers
End-to-End Encryption: This is the gold standard. It means that your data is encrypted on your device before it’s uploaded to the cloud and can only be decrypted by you or authorized recipients. Even the cloud provider cannot access your unencrypted data. Look for providers that offer zero-knowledge encryption, where they genuinely have no access to your encryption keys.
Reputable Providers: Companies like Sync.com, pCloud (with their optional premium encryption), and Tresorit are known for their strong privacy policies and robust encryption features. These services are often designed with privacy as a core tenet, offering features like end-to-end encryption by default or as a readily available add-on.
Features to Look For:
- Zero-Knowledge Encryption: As mentioned, this is paramount.
- Two-Factor Authentication (2FA): An essential layer of security that requires more than just a password to log in.
- Version History and File Recovery: The ability to restore previous versions of files or recover deleted items is crucial for data protection.
- Secure Sharing Options: If you need to share files, ensure the platform offers encrypted sharing links with expiration dates and password protection.
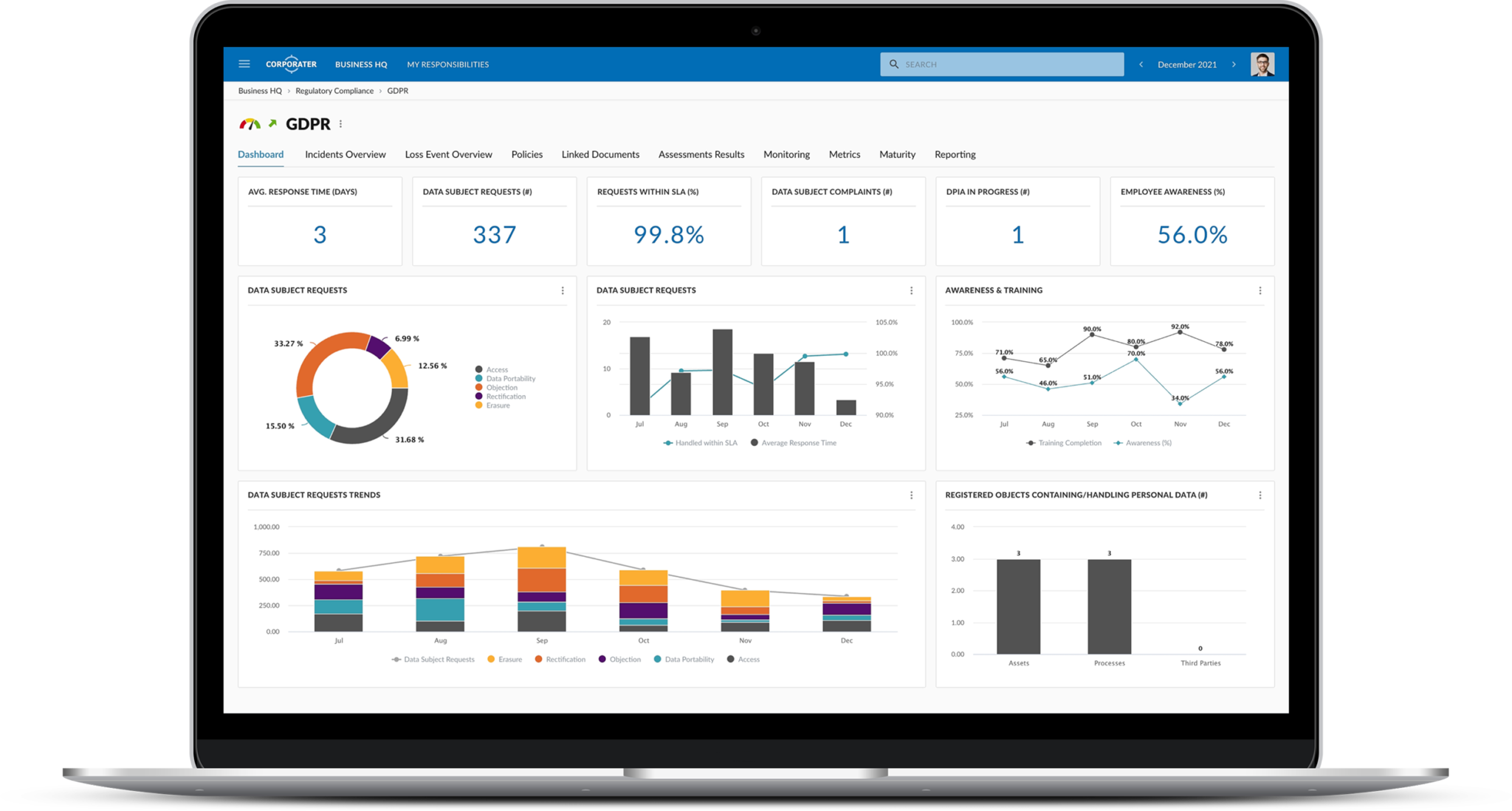
- Compliance Certifications: For businesses, look for providers that comply with relevant data protection regulations (e.g., GDPR, HIPAA).
Potential Pitfalls of Cloud Storage
While convenient, cloud storage is not without its risks. You are essentially entrusting your data to a third party.
- Data Breaches: Even the most secure cloud providers can be targets for sophisticated cyberattacks.
- Account Compromise: If your account credentials are stolen, your data can be accessed.
- Provider Policies: Always read the terms of service and privacy policy carefully. Understand how the provider handles your data and what their obligations are.
- Vendor Lock-in: Migrating large amounts of data from one cloud provider to another can be a tedious and time-consuming process.
Local Storage Solutions: Maximum Control, Maximum Responsibility
For those who prioritize ultimate control over their data, local storage solutions offer a compelling alternative. This typically involves storing data on your own hardware, giving you direct command over its security.
Network-Attached Storage (NAS) Devices
A NAS device is a dedicated file storage server that connects to your home or office network. It offers a centralized location for all your data and can be accessed from multiple devices on your network.
Key Advantages:
- Full Control: You own the hardware and have complete control over data access and security.
- Large Capacity: NAS devices can accommodate multiple hard drives, offering significant storage space.
- RAID Configurations: Redundant Array of Independent Disks (RAID) setups can protect your data from individual drive failures.
- Personal Cloud Functionality: Many NAS devices offer features to create your own private cloud, accessible remotely.
Software Considerations for NAS:
- Operating System: NAS devices run on specialized operating systems (e.g., Synology DSM, QNAP QTS). These operating systems often come with built-in encryption tools, user access management, and backup utilities.
- Encryption: Ensure the NAS OS supports full-disk encryption or folder-level encryption.
- User Management: Implement strong user passwords and restrict access to only authorized users.
- Remote Access Security: If enabling remote access, use strong passwords, enable 2FA, and consider using a VPN for an extra layer of security.
External Hard Drives and SSDs
External drives are the simplest form of local storage. For private data, however, simply storing it on an unencrypted drive is insufficient.
Encryption is Non-Negotiable:
- Hardware Encryption: Some external drives come with built-in hardware encryption. This is often more efficient than software encryption as it uses dedicated hardware for the encryption process.
- Software Encryption: You can use built-in operating system tools (like BitLocker on Windows or FileVault on macOS) or third-party encryption software to encrypt the entire drive or specific partitions.
- Password Protection: Always set a strong, unique password for your encrypted drives.
Best Practices for Local Storage:
- Regular Backups: Even with local storage, backups are critical. Consider a secondary external drive or a cloud backup service for your local data.
- Physical Security: Protect your local storage devices from theft, damage, and unauthorized physical access.
- Secure Disposal: When you no longer need a drive, ensure you securely wipe or destroy it to prevent data recovery.
Hybrid and Decentralized Storage: The Future of Privacy?

Hybrid approaches combine the benefits of both cloud and local storage, while decentralized solutions offer novel ways to distribute and secure data.
Hybrid Cloud Solutions
These solutions involve a combination of local and cloud storage. For example, you might use a NAS device as your primary storage and then use it to back up selected sensitive data to a secure cloud provider.
Benefits:
- Redundancy: Data is stored in multiple locations, increasing resilience.
- Balanced Approach: You retain local control over your most sensitive data while leveraging the convenience of the cloud for less critical files or backups.
Decentralized Storage Networks
These emerging solutions break data into pieces, encrypt them, and distribute them across a network of computers, often using blockchain technology. This eliminates single points of failure and makes data highly resistant to censorship and tampering.
Examples:
- Storj: A decentralized cloud storage platform that uses a network of nodes to store encrypted data fragments.
- Filecoin: A decentralized storage network that incentivizes users to rent out their hard drive space.
Considerations:
- Maturity: These technologies are still evolving, and user-friendliness can vary.
- Complexity: Setting up and managing decentralized storage can be more complex than traditional solutions.
- Performance: Data retrieval times can sometimes be slower depending on network conditions.
Key Features to Prioritize in Private Data Storage Software
Regardless of whether you choose cloud, local, or hybrid solutions, certain features are universally important for safeguarding your private data.
Encryption: The Cornerstone of Privacy
Types of Encryption:
- Symmetric Encryption: Uses a single key for both encryption and decryption. Faster and more efficient for large amounts of data.
- Asymmetric Encryption (Public-Key Cryptography): Uses a pair of keys: a public key for encryption and a private key for decryption. Crucial for secure communication and digital signatures.
Encryption Protocols:
- AES (Advanced Encryption Standard): Currently the most widely used and robust symmetric encryption algorithm. Look for AES-256.
- TLS/SSL: Protocols used to encrypt data in transit, essential for cloud storage and web-based access.
Access Control and User Management
Granular Permissions: The ability to define who can access what data and what actions they can perform (read, write, delete) is vital, especially in shared environments.
Strong Authentication:
- Multi-Factor Authentication (MFA/2FA): A must-have for any system handling sensitive data.
- Password Policies: Enforce strong, unique passwords and encourage regular changes.
Backup and Disaster Recovery
Automated Backups: Schedule regular, automated backups to ensure your data is consistently protected.
Offsite Backups: Store backups in a separate physical location from your primary data to protect against local disasters (fire, flood, theft).
Data Redundancy: For local storage, consider RAID configurations. For cloud, understand how the provider ensures data durability.
Restore Testing: Periodically test your restore process to ensure you can actually recover your data when needed.
Data Integrity and Audit Trails
Data Integrity Checks: Mechanisms that verify data hasn’t been altered or corrupted during storage or transit.
Audit Logs: Detailed records of all access and activity within the storage system. This is invaluable for security monitoring and forensic analysis if a breach occurs.
Implementing Best Practices for Storing Private Data
Choosing the right software is only half the battle. Implementing sound practices is equally crucial for maintaining the privacy and security of your data.
The Principle of Least Privilege
Grant users and applications only the minimum permissions necessary to perform their intended functions. Avoid giving everyone administrative access.
Regular Software Updates and Patching
Keep your operating systems, applications, and any storage software up-to-date. Updates often include critical security patches that protect against known vulnerabilities.
Secure Network Practices
If using local storage or accessing cloud services, ensure your network is secure. Use strong Wi-Fi passwords, consider a firewall, and be cautious about connecting to public Wi-Fi networks.
Physical Security for Local Storage
If you’re using external drives or NAS devices, ensure they are stored in a secure location where they are protected from theft, physical damage, and unauthorized access.
Secure Data Disposal
When discarding old hard drives or storage media, ensure that the data is irrecoverably erased or that the media is physically destroyed.
Education and Awareness
For individuals and teams, understanding the importance of data privacy and the security measures in place is fundamental. Regular training on best practices can significantly reduce the risk of human error leading to a data breach.
In conclusion, selecting “good software for storing private data” is a multifaceted decision that requires careful consideration of your unique needs, the sensitivity of your information, and the evolving landscape of technology. By understanding the different storage paradigms, prioritizing essential security features like robust encryption and access control, and diligently implementing best practices, you can significantly enhance the privacy and security of your most valuable digital assets. The key is to remain informed, proactive, and to never underestimate the importance of safeguarding your personal information.
