In the ever-evolving landscape of cloud computing, managing and provisioning infrastructure efficiently and consistently is paramount. For organizations leveraging Amazon Web Services (AWS), this challenge is met head-on by AWS CloudFormation. This powerful service acts as a fundamental building block for automating the deployment and management of AWS resources, enabling developers and IT professionals to model their entire infrastructure in a declarative manner. Instead of manually configuring individual services through the AWS Management Console or scripting complex sequences of API calls, CloudFormation allows you to define your infrastructure as code (IaC), fostering repeatability, scalability, and reliability.
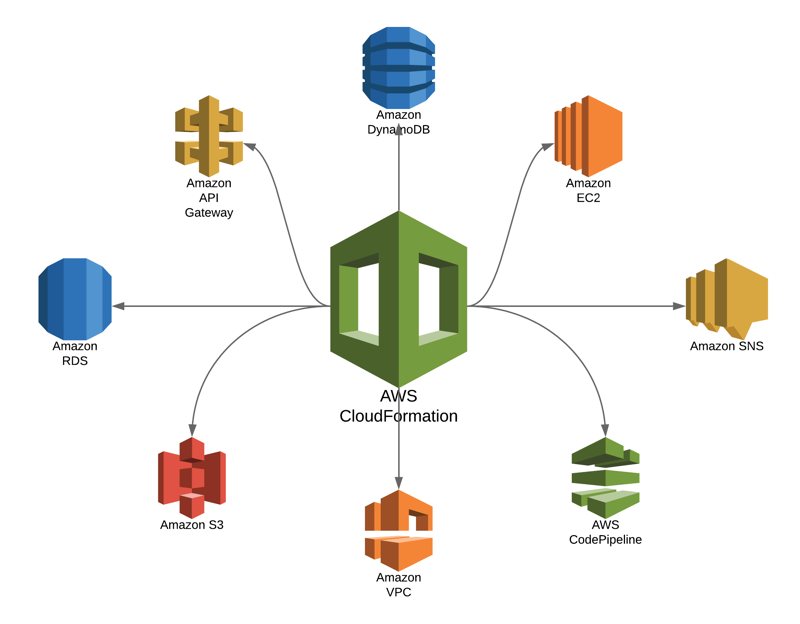
At its core, CloudFormation is a service that helps you model and set up your Amazon Web Services resources so that you can spend less time managing those resources and more time launching applications that rely on them. You can use CloudFormation to create, update, and delete your AWS resources in a predictable, repeatable, and automated fashion. It works by allowing you to define infrastructure in a template, which is a text file written in JSON or YAML format. This template acts as a blueprint for your entire cloud environment. When you submit this template to CloudFormation, it provisions the specified resources in the correct order and with the correct dependencies. This paradigm shift from imperative (telling the system how to do something step-by-step) to declarative (telling the system what you want) is a cornerstone of modern infrastructure management.
The Power of Infrastructure as Code with CloudFormation
The adoption of Infrastructure as Code (IaC) has revolutionized how we build, deploy, and manage applications in the cloud. CloudFormation is a prime example of IaC in action, bringing a host of benefits that address common pain points in traditional infrastructure management. By treating your infrastructure definitions as code, you unlock capabilities that were previously difficult or impossible to achieve. This section delves into the fundamental advantages that CloudFormation brings to the table, empowering organizations to operate with greater agility and confidence.
Declarative Syntax for Predictable Outcomes
The declarative nature of CloudFormation templates is a significant departure from imperative scripting. Instead of writing a sequence of commands that tell AWS what to do, you define the desired state of your infrastructure. You specify what resources you need (e.g., EC2 instances, RDS databases, S3 buckets), their configurations, and how they should relate to each other. CloudFormation then takes this blueprint and orchestrates the provisioning process, ensuring that the end state matches your declared intent. This declarative approach significantly reduces the cognitive load on engineers and minimizes the potential for human error. When you deploy a CloudFormation stack, you are not executing a series of commands; you are instructing AWS to create a specific configuration. If a resource fails to provision, CloudFormation can roll back the changes, ensuring that your infrastructure remains in a consistent and known state. This predictability is crucial for maintaining stable and reliable applications.
Resource Abstraction and Dependency Management
CloudFormation abstracts away much of the complexity of interacting directly with individual AWS services. You don’t need to worry about the specific API calls or the order in which certain resources must be created. CloudFormation intelligently infers dependencies between resources. For instance, if you define an EC2 instance that needs to be associated with a particular security group, CloudFormation understands that the security group must be created before the EC2 instance. This automatic dependency management is a game-changer, especially in complex environments with interdependencies. It simplifies the template creation process and reduces the likelihood of errors caused by incorrect resource ordering. Furthermore, CloudFormation supports a wide range of AWS services, allowing you to define and manage a comprehensive infrastructure stack from a single template. This unification simplifies management and reduces the need for context-switching between different tools and services.
Version Control and Collaboration
Since CloudFormation templates are text files, they can be easily integrated into version control systems like Git. This allows teams to track changes to their infrastructure definitions over time, revert to previous versions if needed, and collaborate effectively on infrastructure projects. Version control provides an audit trail of all infrastructure modifications, which is invaluable for troubleshooting, compliance, and security reviews. Developers and operations engineers can work together, reviewing each other’s infrastructure code, merging changes, and deploying updates with confidence. This fosters a culture of collaboration and shared responsibility, breaking down traditional silos between development and operations teams. The ability to treat infrastructure as code, just like application code, aligns perfectly with DevOps principles.
Understanding CloudFormation Stacks and Templates
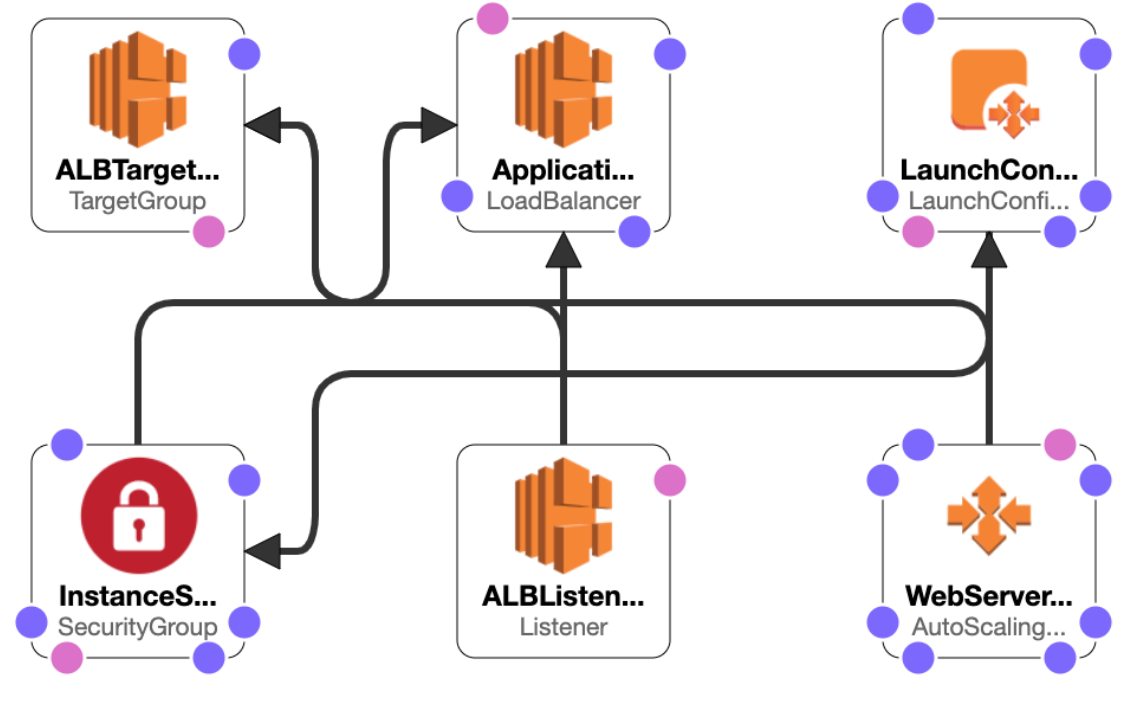
The core components of AWS CloudFormation are templates and stacks. A template defines the resources you want to provision, while a stack is a collection of these resources managed as a single unit. Understanding the relationship between these two elements is crucial for effectively using CloudFormation. This section breaks down these fundamental concepts, providing clarity on how CloudFormation organizes and deploys your infrastructure.
CloudFormation Templates: The Blueprint of Your Infrastructure
A CloudFormation template is a JSON or YAML file that describes the AWS resources you want to provision and configure. These templates consist of several sections, each serving a specific purpose in defining your infrastructure. The Resources section is the most critical, where you declare the AWS resources you wish to create, such as AWS::EC2::Instance, AWS::RDS::DBInstance, or AWS::S3::Bucket. Each resource declaration includes properties that configure its specific attributes. For example, when defining an EC2 instance, you would specify the AMI ID, instance type, and security groups.
Beyond the Resources section, templates can also include:
- Parameters: These allow you to provide input values when you create or update a stack, making your templates reusable and flexible. For instance, you can parameterize the instance type or the desired number of EC2 instances.
- Mappings: These enable you to specify conditional values. For example, you could use a mapping to select different AMIs based on the AWS region.
- Outputs: These allow you to specify values that you want to retrieve from your stack after it has been created, such as the public IP address of an EC2 instance or the endpoint of an RDS database.
- Conditions: These enable you to conditionally create or update resources based on parameter values or other conditions.
- Metadata: This section allows you to provide descriptive information about your template or specific resources.

The choice between JSON and YAML is largely a matter of preference. YAML is often considered more human-readable due to its less verbose syntax, while JSON is a more universally parsed format. Regardless of the format, the structure and functionality remain the same.
CloudFormation Stacks: Managing Resources as a Unit
A stack is the collection of AWS resources that you create and manage as a single unit when you execute a CloudFormation template. When you submit a template to CloudFormation, it creates a stack. You can then update or delete the stack, and CloudFormation will orchestrate the changes to your resources accordingly. CloudFormation tracks the status of your stack and the resources within it, providing visibility into the provisioning process.
Key operations you perform with stacks include:
- Creating a stack: This involves uploading your template and providing any necessary parameter values. CloudFormation then initiates the creation of all defined resources.
- Updating a stack: This allows you to modify the resources within an existing stack. You can change resource configurations, add new resources, or delete existing ones by providing an updated template. CloudFormation performs a comparison between the current and new template and applies the necessary changes, often with rollback capabilities.
- Deleting a stack: This removes all resources that were created as part of the stack, ensuring a clean teardown of your infrastructure.
Stacks provide a logical grouping for your infrastructure components, making it easier to manage, monitor, and troubleshoot your cloud environment.
Advanced Features and Best Practices for CloudFormation
As you become more comfortable with CloudFormation, you can leverage its advanced features to build more robust, secure, and efficient infrastructure. Implementing best practices ensures that your CloudFormation deployments are reliable and maintainable in the long run. This section explores some of these advanced capabilities and offers guidance on how to use CloudFormation effectively.
Change Sets for Safe Updates
One of the most critical aspects of managing live infrastructure is ensuring that updates are applied safely and predictably. CloudFormation’s Change Sets feature plays a vital role in this regard. Before applying changes to a stack, you can generate a change set, which provides a preview of the modifications CloudFormation intends to make. This includes seeing which resources will be created, modified, or deleted, along with the specific property changes. By reviewing the change set, you can identify potential unintended consequences and mitigate risks before they impact your production environment. This “dry run” capability significantly enhances the safety and confidence in your deployment processes.
StackSets for Multi-Account and Multi-Region Deployments
For organizations operating across multiple AWS accounts and regions, managing infrastructure consistently can be a complex undertaking. AWS CloudFormation StackSets addresses this challenge by allowing you to deploy and manage your stacks across multiple AWS accounts and AWS Regions from a single AWS Region. This is particularly useful for establishing a baseline of core infrastructure components, such as networking, security groups, or logging configurations, across your entire organization. StackSets automates the deployment and lifecycle management of these common resources, ensuring uniformity and reducing operational overhead. This capability is instrumental in achieving a well-governed and standardized cloud environment.
Nested Stacks for Modularity and Reusability
As your infrastructure definitions grow in complexity, managing a single, monolithic template can become cumbersome. Nested Stacks offer a solution by allowing you to modularize your CloudFormation templates. You can create reusable templates for common infrastructure components (e.g., a VPC template, a database template) and then reference these nested stacks within a parent template. This promotes code reusability, makes templates easier to understand and maintain, and allows for better organization of your infrastructure. By breaking down your infrastructure into smaller, manageable modules, you can accelerate development and reduce the likelihood of errors.
Best Practices for CloudFormation
- Use Version Control: Always store your CloudFormation templates in a version control system like Git.
- Parameterize Wisely: Utilize parameters to make your templates flexible and reusable across different environments or configurations.
- Implement Conditions: Use conditions to control the creation of resources based on specific criteria, allowing for more dynamic deployments.
- Leverage Outputs: Define outputs to easily retrieve important information about your deployed resources.
- Employ Change Sets: Always use change sets for stack updates to preview changes before they are applied.
- Structure with Nested Stacks: For complex infrastructures, break down templates into smaller, reusable nested stacks.
- Secure Your Templates: Be mindful of sensitive information within your templates and consider using AWS Secrets Manager or AWS Systems Manager Parameter Store for sensitive parameters.
- Implement Drift Detection: Regularly use CloudFormation’s drift detection feature to identify any manual changes made outside of CloudFormation.
By embracing CloudFormation and adhering to these best practices, organizations can unlock the full potential of infrastructure as code, driving efficiency, consistency, and innovation in their AWS cloud deployments.
