In the ever-evolving landscape of digital interaction, the concept of privacy has become paramount. As we navigate the vast expanse of the internet, concerns about our online footprint, the data collected about our browsing habits, and the potential for its misuse are increasingly at the forefront of public consciousness. Among the array of tools and features designed to address these concerns, the “incognito tab” has emerged as a widely recognized, yet often misunderstood, mechanism for enhancing online privacy. But what exactly is an incognito tab, and how does this seemingly simple browser function represent a significant stride in personal data management and the broader innovation of user-centric digital experiences?
This exploration delves into the core functionalities of incognito tabs, the technological underpinnings that enable their operation, and their implications within the wider context of tech and innovation. We will dissect the common misconceptions surrounding incognito mode, clarify its limitations, and highlight its role as a fundamental building block for more sophisticated privacy-enhancing technologies.
The Core Functionality: A Veil of Ephemerality
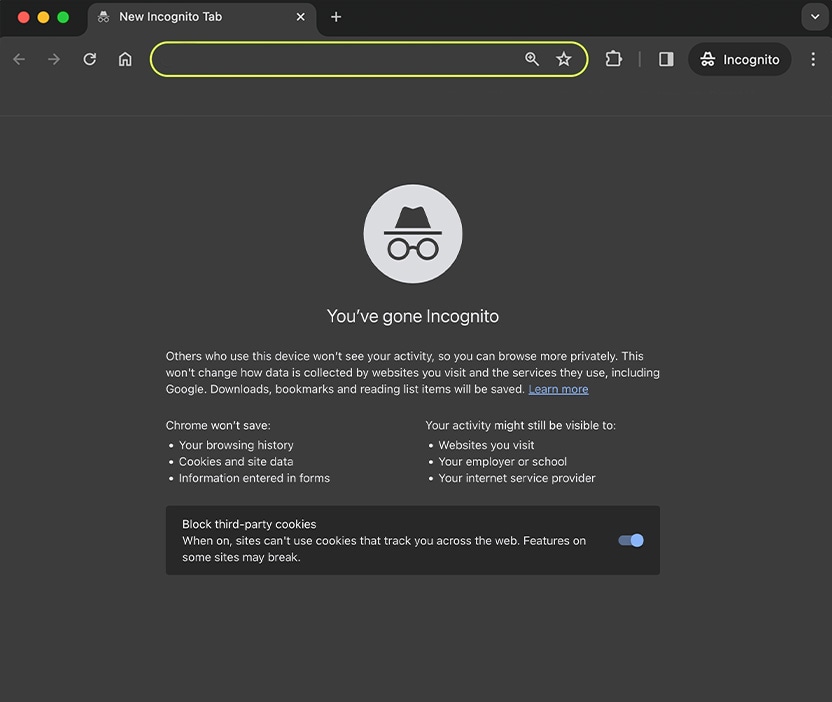
At its heart, an incognito tab, often referred to by various names such as “Private Browsing,” “Incognito Mode,” or “InPrivate,” is a specialized browsing session designed to leave minimal traces on the local device. This is not a magic invisibility cloak for the internet; rather, it’s a carefully engineered feature that alters how the web browser handles and stores information during that specific session. The primary goal is to prevent the browser from saving data that could be easily accessed by others who use the same device.
Minimizing Local Data Storage
The most immediate and apparent effect of using an incognito tab is the cessation of local data logging. When you browse the web in a standard browser window, the software diligently records a wealth of information to enhance your future browsing experience and for various operational purposes. This includes:
- Browsing History: Every website you visit is cataloged, allowing you to quickly revisit pages through the history menu or by typing in the address bar. In incognito mode, this history is not saved. Once the incognito window is closed, all record of the sites visited within that session is purged from the browser’s history.
- Cookies: These are small text files websites place on your computer to remember your preferences, login status, and other session-specific information. While essential for seamless online experiences, cookies can also be used for tracking. Incognito tabs typically treat cookies as session-specific. Any cookies generated during an incognito session are deleted when the window is closed, preventing them from persisting and being used for tracking across multiple browsing sessions on that device.
- Site Data and Permissions: This encompasses information like cached images and files, downloaded files (though the downloaded files themselves remain on your computer, the record of their download is cleared), form data entered into web pages, and any permissions granted to websites (e.g., access to your microphone or camera). Incognito mode prevents this data from being saved locally, ensuring a cleaner slate upon session termination.
- Temporary Files: Browsers often store temporary files, such as images and scripts, to speed up page loading times. Incognito mode aims to discard these temporary files as well, further reducing the digital residue left on the device.
The Illusion of Anonymity vs. Actual Privacy
It is crucial to understand that incognito mode offers a specific type of privacy: local privacy. It shields your browsing activities from other users of the same device. If you share your computer with family members or colleagues, they will not be able to see your incognito browsing history or the websites you visited within that session through your browser’s history or cookies. This local segregation is a significant, albeit limited, step in managing personal digital information.
However, incognito mode does not render you anonymous on the internet. This is a common misconception that leads to a false sense of security. Your online activities can still be monitored and recorded by various entities outside of your local device:
- Internet Service Providers (ISPs): Your ISP can see all the internet traffic that passes through their network, regardless of whether you are using an incognito tab. They can log the websites you visit, the duration of your visits, and the amount of data you consume.
- Websites You Visit: Websites themselves can still track your activity when you visit them, even in incognito mode. They can use IP addresses, unique browser fingerprints (combinations of settings and configurations that can identify your browser), and other methods to monitor your engagement, purchase history, and behavior on their site. If you log into an account on a website (e.g., your social media or email), the website will know it’s you, regardless of the browsing mode.
- Employers or Network Administrators: If you are using a computer or network provided by your employer or school, the network administrators may have the ability to monitor your internet activity, even when you are in incognito mode. They often have robust logging systems in place for security and policy enforcement.
- Search Engines: While incognito mode prevents your search history from being saved locally, the search queries you enter can still be used by search engines to personalize your search results and serve targeted advertisements in future standard browsing sessions.
Technological Underpinnings: A Shift in Browser Architecture
The implementation of incognito mode represents a thoughtful innovation in browser architecture, prioritizing user control over data persistence. It’s not a simple on/off switch for internet tracking but a sophisticated re-routing and temporary storage mechanism within the browser’s software.
Session-Based Data Management
The core technological principle behind incognito mode is session-based data management. When an incognito tab is opened, the browser initiates a temporary, isolated session. All data generated during this session is earmarked for immediate deletion upon the closure of the incognito window. This is achieved through a combination of:
- Ephemeral Storage: Instead of writing data to persistent storage (like your hard drive), the browser utilizes temporary memory allocations that are cleared when the session ends. This is analogous to using a notepad that gets shredded after you’re done with it, rather than filing it away.
- Modified Data Handling Protocols: The browser’s internal protocols for handling cookies, cache, and history are temporarily altered. They are instructed to operate in a write-once-delete-immediately fashion, or not to write at all for certain types of data.
- Isolated Processes: Modern browsers often employ process isolation for tabs, meaning each tab runs in its own process. Incognito mode can leverage this by ensuring that the processes associated with incognito tabs have stricter data deletion policies applied to them upon termination.
Evolution and Refinement of Privacy Features
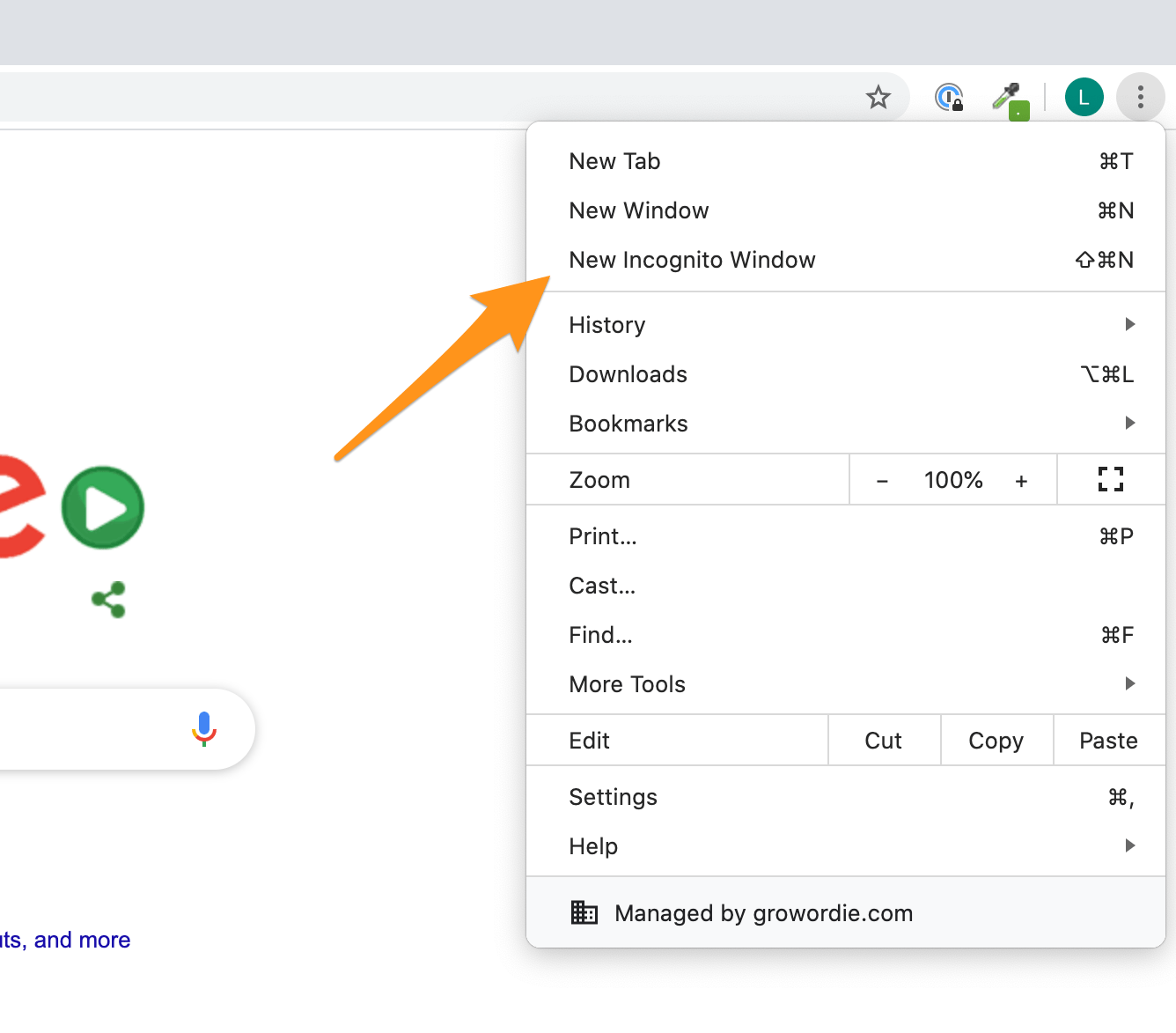
The concept of private browsing has evolved significantly since its inception. Early iterations might have been simpler, with less granular control over data. Today, incognito mode is a more robust feature, integrated into the core functionality of major browsers like Google Chrome, Mozilla Firefox, Microsoft Edge, and Apple Safari.
- Chrome’s Incognito Mode: Pioneered the term “Incognito” and is characterized by its distinct dark interface. It focuses on not saving browsing history, cookies, site data, or information entered into forms.
- Firefox’s Private Browsing: Offers enhanced tracking protection by default, even in private windows, blocking a wider range of trackers than some other browsers.
- Microsoft’s InPrivate Browsing: Similar to incognito mode, it prevents the browser from saving browsing history, temporary internet files, cookies, and form data.
- Safari’s Private Browsing: Emphasizes intelligent tracking prevention, aiming to block websites from tracking users across the web by analyzing and limiting site data and cross-site tracking cookies.
The continuous refinement of these features reflects a growing understanding of user privacy needs and the ongoing innovation in browser development to balance functionality with data protection.
Beyond Incognito: The Broader Context of Online Privacy Innovation
While incognito tabs are a valuable tool for local privacy, they represent just one facet of a much larger and more complex ecosystem of online privacy technologies and innovations. The demand for greater control over personal data has spurred the development of more comprehensive solutions, moving beyond simple local data deletion to address network-level privacy and anonymity.
Tools for Enhanced Anonymity and Security
The limitations of incognito mode have paved the way for more advanced privacy tools that aim to obfuscate online activity at a network level:
- Virtual Private Networks (VPNs): VPNs encrypt your internet traffic and route it through a remote server, masking your IP address and making it appear as though you are browsing from the VPN server’s location. This provides a significant layer of privacy by hiding your online activities from your ISP and making it harder for websites to track your real location.
- Tor Browser: The Onion Router (Tor) is a free and open-source software that enables anonymous communication. It works by routing internet traffic through a worldwide, volunteer overlay network consisting of thousands of relays to conceal a user’s location and usage from anyone conducting network surveillance or traffic analysis. While slow, it offers a high degree of anonymity.
- Privacy-Focused Search Engines: Search engines like DuckDuckGo and Startpage do not track your search queries, store your personal information, or create user profiles. They provide search results without the personalization that often comes with data collection by mainstream search engines.
- Browser Extensions: A plethora of browser extensions are available that enhance privacy by blocking ads, trackers, and scripts. These can be used in conjunction with incognito mode for an additional layer of protection. Examples include uBlock Origin, Privacy Badger, and Ghostery.

The Future of Digital Privacy: A Continual Innovation Cycle
The ongoing development in digital privacy is a testament to the relentless pursuit of user empowerment in the digital age. Incognito tabs, while a foundational innovation, serve as a gateway to understanding the deeper complexities of online data management. The future promises even more sophisticated solutions, driven by:
- Decentralized Identity and Data Management: Technologies that allow individuals to control their digital identity and personal data, rather than having it stored and managed by third parties.
- Zero-Knowledge Proofs and Homomorphic Encryption: Advanced cryptographic techniques that enable data processing and verification without revealing the underlying data itself, offering unprecedented levels of privacy for sensitive information.
- AI-Powered Privacy Assistants: Intelligent agents that can proactively manage privacy settings, alert users to potential data breaches, and optimize online privacy based on user preferences.
In conclusion, an incognito tab is a vital, albeit basic, innovation in user privacy, designed to prevent the local logging of browsing data. It empowers users with a greater sense of control over their digital footprint on shared devices. However, its effectiveness is confined to the local environment. Understanding its functionalities, its technological underpinnings, and its limitations is crucial for navigating the modern digital landscape. As technology continues to advance, the pursuit of online privacy will undoubtedly lead to even more innovative solutions, building upon the foundational principles that incognito mode represents.
