Cross-Site Scripting (XSS) is a prevalent and insidious type of web security vulnerability. It allows attackers to inject malicious scripts, typically JavaScript, into web pages viewed by other users. Unlike many other web attacks that target the server directly, XSS exploits vulnerabilities in the trust a user has for a website. When a user visits a compromised website, the malicious script executes within their browser, often with the same privileges as legitimate scripts from that website. This can lead to a range of harmful activities, from stealing sensitive information to hijacking user sessions. Understanding XSS is crucial for both developers building secure web applications and users who want to protect themselves online.

The Mechanics of Cross-Site Scripting Attacks
At its core, XSS occurs when an attacker can inject client-side code into web pages that are then delivered to other users. This injection typically happens through user-supplied input that the web application does not properly sanitize or validate before displaying it. The attacker doesn’t break into the website’s servers; instead, they exploit how the website handles and presents user-generated content.
How Injection Occurs
The primary mechanism for XSS attacks relies on improperly handled user input. Websites often allow users to submit data, such as comments, forum posts, search queries, or profile information. If the application doesn’t meticulously clean this input, it might interpret certain characters or sequences as executable code rather than plain text.
For instance, if a website displays user comments without proper sanitization, an attacker could post a comment containing a JavaScript snippet. When another user views this comment, their browser will execute the injected script.
- Example Scenario: Imagine a simple guestbook application where users can leave messages. If the application directly displays user input like this:
html¨K20K
An attacker could submit the following as their message:
html¨K19K
When this message is displayed, the browser will render the<script>tags and execute thealert()function, showing a pop-up message. While this is a benign example, it illustrates the fundamental principle of injecting executable code.
The Role of User Input and Lack of Sanitization
The vulnerability arises from the trust relationship between a user’s browser and a website. Browsers are designed to execute scripts from trusted sources. When a website fails to distinguish between legitimate content and potentially malicious user-supplied content, it opens the door for XSS.
Sanitization is the process of cleaning user input to remove or neutralize potentially harmful characters and code. This involves:
- Escaping special characters: Characters like
<,>,&,', and"have special meanings in HTML and JavaScript. If these characters are not properly escaped (e.g., by converting<to<), they can be interpreted as the start of code or tags. - Filtering malicious tags and attributes: Removing or neutralizing HTML tags like
<script>and JavaScript-specific attributes likeonerror. - Encoding output: Ensuring that data is displayed in a way that the browser treats it as data, not executable code.
When this sanitization process is weak or absent, user input can be crafted to include scripts that then execute in the context of the victim’s browser session.
Types of Cross-Site Scripting Attacks
XSS vulnerabilities are broadly categorized into three main types, distinguished by how the malicious script is delivered to the victim’s browser. Each type has its own characteristics and implications.
Stored XSS (Persistent XSS)
Stored XSS is considered the most dangerous type because the malicious script is permanently stored on the target server. This often occurs when an attacker injects script into a database, message forum, comment field, or any other data that the web application stores and later retrieves to display to other users.
- How it works: An attacker submits malicious script to a website, and the website stores this script as part of its data (e.g., in a database). When any user accesses the page that displays this stored data, their browser fetches the malicious script along with the legitimate content and executes it.
- Impact: Since the script is stored, every user who views the compromised page is potentially affected, without needing to be directly targeted or tricked into clicking a specific link. This can lead to widespread compromise.
- Example: An attacker posts a malicious script in a comment section of a blog. Every user who visits that blog post will have the script executed in their browser.
Reflected XSS (Non-Persistent XSS)
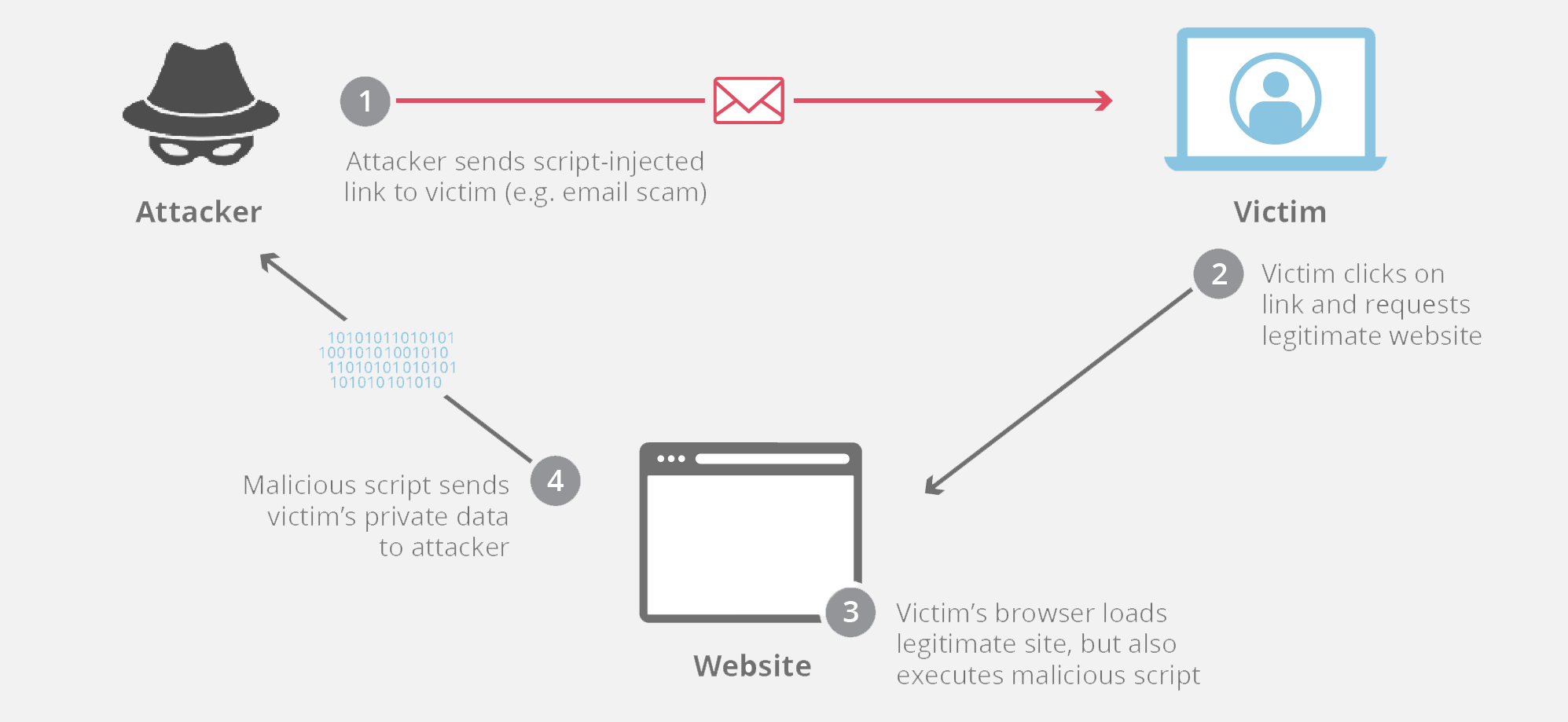
Reflected XSS attacks occur when a malicious script is embedded within a URL or other request parameter. The server then reflects this script back to the user in the response, causing it to execute in their browser. The script itself is not stored on the server.
- How it works: An attacker crafts a malicious URL containing a script. They then trick a victim into clicking this URL (e.g., via email, social media, or a malicious advertisement). When the victim clicks the link, their browser sends the request (including the script) to the web server. The server, without proper validation, includes the script in the response page sent back to the victim’s browser, and the script executes.
- Impact: This type of attack is less widespread than stored XSS as it requires the victim to actively click on a specially crafted link. However, it can still be very effective for targeted attacks or when combined with social engineering.
- Example: A website has a search function that displays the search query in the URL and on the results page. An attacker might create a URL like:
http://vulnerable-website.com/search?query=<script>alert('XSSed!');</script>
If a user clicks this link, and the website displays the search term directly without sanitization, the script will execute in their browser.
DOM-based XSS
DOM-based XSS is a more nuanced form of XSS where the vulnerability lies within the client-side code (the Document Object Model or DOM) of a web page, rather than the server-side code. The malicious script is executed as a result of modifying the DOM environment in the victim’s browser.
- How it works: In DOM-based XSS, the server’s response might be clean, but the client-side JavaScript code on the page processes user input in an insecure way. This allows an attacker to manipulate the DOM, leading to the execution of a script. The exploit often involves fragments of URLs (e.g., the part after the
#) which are not sent to the server but are processed by client-side JavaScript. - Impact: Similar to reflected XSS, this often requires user interaction. However, it can be harder to detect as the malicious payload might not appear in the server logs or the HTTP response viewed by a standard browser inspector.
- Example: A web page uses JavaScript to take a value from the URL fragment (
window.location.hash) and write it to the page’s HTML. If this value is not sanitized, an attacker could craft a URL like:
http://vulnerable-website.com/page#<script>alert('DOM XSS');</script>
The client-side JavaScript would then take this script and insert it into the DOM, causing it to execute.
The Impact and Risks of Cross-Site Scripting
The consequences of successful XSS attacks can range from mildly annoying to severely damaging, impacting both individual users and the reputation of the affected organizations. The primary goal of an XSS attack is to leverage the user’s browser as an execution environment for malicious code.
Session Hijacking and Credential Theft
One of the most common and damaging outcomes of XSS is session hijacking. Websites often use session cookies to keep users logged in. If an attacker can inject a script that steals these session cookies, they can then impersonate the victim and gain unauthorized access to their account on the vulnerable website.
- Cookie Theft: Scripts can be written to read the victim’s cookies and send them to an attacker-controlled server. For example, a JavaScript snippet could use
document.cookieto access cookies and then useXMLHttpRequestorfetchto send them to a remote server. - Bypassing Authentication: With a stolen session cookie, an attacker can bypass the need for a password and log in as the victim, gaining access to their personal data, financial information, or other sensitive content.
Data Manipulation and Defacement
XSS attacks can also be used to manipulate or deface the content of a website as viewed by the victim. The attacker’s script can modify the page’s HTML dynamically, changing text, images, or links to display misinformation or redirect users to malicious sites.
- Phishing: An attacker might inject a fake login form into a legitimate-looking page, tricking users into entering their credentials.
- Content Alteration: Websites can be defaced to display offensive material, spread propaganda, or spread misinformation, damaging the reputation of the website owner.
Malware Distribution and Phishing
Beyond stealing information directly from the compromised website, XSS can be a stepping stone to more elaborate attacks, including malware distribution and sophisticated phishing campaigns.
- Redirecting Users: Scripts can force the user’s browser to navigate to a different, malicious website without their consent. This malicious site might host malware for download or be part of a larger phishing operation.
- Exploiting Browser Vulnerabilities: In some advanced scenarios, the injected script could attempt to exploit known vulnerabilities in the victim’s browser or its plugins to install malware directly onto their system.
Preventing and Mitigating Cross-Site Scripting Vulnerabilities
Protecting against XSS requires a multi-layered approach, encompassing both secure coding practices for developers and user awareness for end-users. Given the ubiquity of web applications, robust prevention mechanisms are paramount.
Secure Coding Practices for Developers
The primary responsibility for preventing XSS lies with developers who build and maintain web applications. Implementing secure coding practices is essential to avoid introducing these vulnerabilities.
- Input Validation: Rigorously validate all user-supplied input on the server-side. This means checking if the input conforms to expected formats, lengths, and character sets. Reject any input that does not meet these criteria.
- Output Encoding: This is arguably the most critical defense. Always encode user-supplied data before rendering it in an HTML context. Use appropriate encoding functions based on where the data is being displayed. For example:
- HTML Encoding: Convert characters like
<to<,>to>, and&to&when displaying data within HTML tags. - JavaScript Encoding: Escape characters within JavaScript strings to prevent them from being interpreted as code.
- URL Encoding: Ensure data embedded in URLs is properly encoded.
- HTML Encoding: Convert characters like
- Content Security Policy (CSP): Implement CSP headers to define which resources (scripts, styles, images) the browser is allowed to load for a given page. This can significantly reduce the impact of XSS by preventing the execution of unauthorized scripts.
- Using Frameworks and Libraries: Modern web frameworks (e.g., React, Angular, Vue.js) often have built-in mechanisms for automatically sanitizing and encoding output, reducing the risk of XSS if used correctly.
- Regular Security Audits and Testing: Conduct regular security audits, penetration testing, and code reviews specifically looking for XSS vulnerabilities. Automated tools can help identify potential issues, but manual review is often necessary for complex scenarios.

User Awareness and Defensive Browsing
While developers have the primary role, users can also take steps to protect themselves.
- Be Wary of Suspicious Links: Do not click on links from unknown or untrusted sources, especially those that appear to be coming from your bank, social media, or other important services but have slightly altered URLs or unusual phrasing.
- Keep Browsers and Plugins Updated: Regularly update your web browser and any plugins (like Flash or Java) to the latest versions. Security updates often patch vulnerabilities that could be exploited by XSS attacks.
- Use Security Extensions: Consider using browser security extensions that can help detect and block malicious scripts or phishing attempts.
- Enable Browser Security Features: Most modern browsers have built-in security features designed to protect against malicious websites. Ensure these features are enabled.
- Understand Website Permissions: Pay attention to any requests for permissions that websites make, especially those related to running scripts or accessing your location.
By combining secure development practices with informed user behavior, the threat of Cross-Site Scripting can be significantly minimized, leading to a safer and more secure online experience for everyone.
